Practice Free AZ-400 Exam Online Questions
2You have a GitHub repository.
You need to ensure that all changes to code are validated by your company’s security department before the main branch is deployed.
Which two actions can you perform? Each correct answer presents a complete solution. NOTE: Each correct selection is worth one point.
- A . Create a branch protection rule for the feature branches.
- B . Create a branch protection rule for the main branch.
- C . Create a LICENSE file.
- D . Require signed commits.
- E . Create a CODEOWNERS file.
SIMULATION
You need to create a notification if the peak average response time of an Azure web app named az400-9940427-main is more than five seconds when evaluated during a five-minute period. The notification must trigger the “https://contoso.com/notify” webhook. To complete this task, sign in to the Microsoft Azure portal.
You plan to create an image that will contain a .NET Core application.
You have a Docker file file that contains the following code. (Line numbers are included for reference only.)
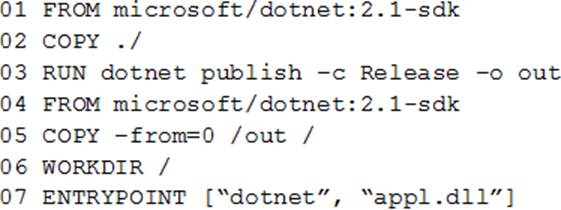
You need to ensure that the image is as small as possible when the image is built.
Which line should you modify in the file?
- A . 1
- B . 3
- C . 4
- D . 7
C
Explanation:
https://github.com/dotnet/dotnet-docker/blob/master/samples/dotnetapp/README.md
You plan to create an image that will contain a .NET Core application.
You have a Docker file file that contains the following code. (Line numbers are included for reference only.)
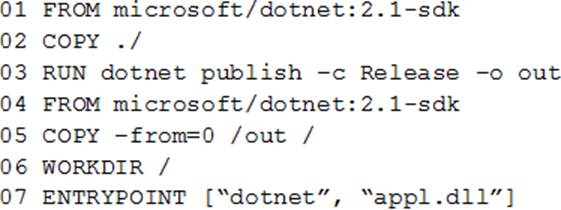
You need to ensure that the image is as small as possible when the image is built.
Which line should you modify in the file?
- A . 1
- B . 3
- C . 4
- D . 7
C
Explanation:
https://github.com/dotnet/dotnet-docker/blob/master/samples/dotnetapp/README.md
You are developing an Azure Pipelines pipeline.
You need to configure a check in the pipeline that will query Azure Boards to ensure that there are no active work item issues before the pipeline deploys a build to production.
Which type of check should you implement?
- A . post-deployment approvals
- B . manual validations
- C . pre-deployment gates
- D . pre-deployment approvals
You are designing a strategy to monitor the baseline metrics of Azure virtual machines that run Windows Server. You need to collect detailed data about the processes running in the guest operating system.
Which two agents should you deploy? Each correct answer presents part of the solution. NOTE: Each correct selection is worth one point.
- A . the Dependency agent
- B . the Azure Network Watcher Agent for Windows
- C . the Telegraf agent
- D . the Azure Log Analytics agent
A,D
Explanation:
The following table provide a quick comparison of the Azure Monitor agents for Windows.
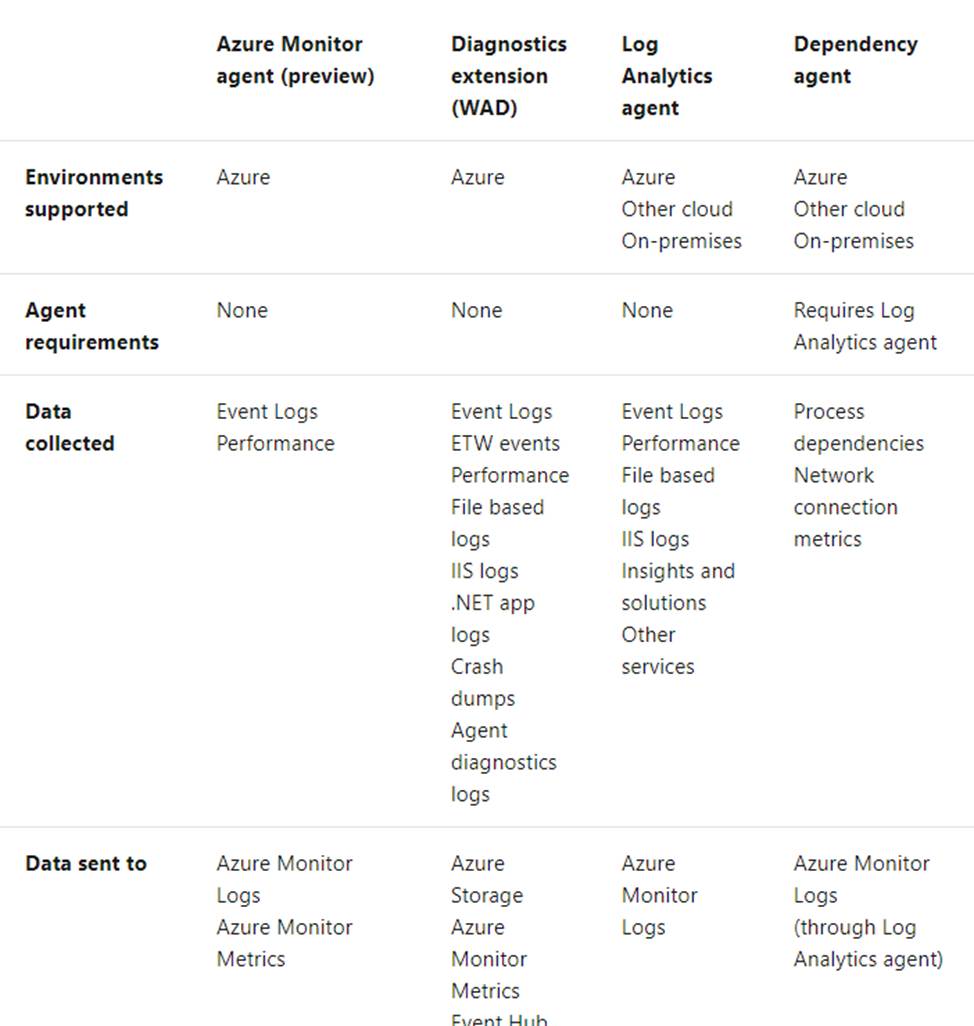
Reference: https://docs.microsoft.com/en-us/azure/azure-monitor/platform/agents-overview
You are designing a strategy to monitor the baseline metrics of Azure virtual machines that run Windows Server. You need to collect detailed data about the processes running in the guest operating system.
Which two agents should you deploy? Each correct answer presents part of the solution. NOTE: Each correct selection is worth one point.
- A . the Dependency agent
- B . the Azure Network Watcher Agent for Windows
- C . the Telegraf agent
- D . the Azure Log Analytics agent
A,D
Explanation:
The following table provide a quick comparison of the Azure Monitor agents for Windows.
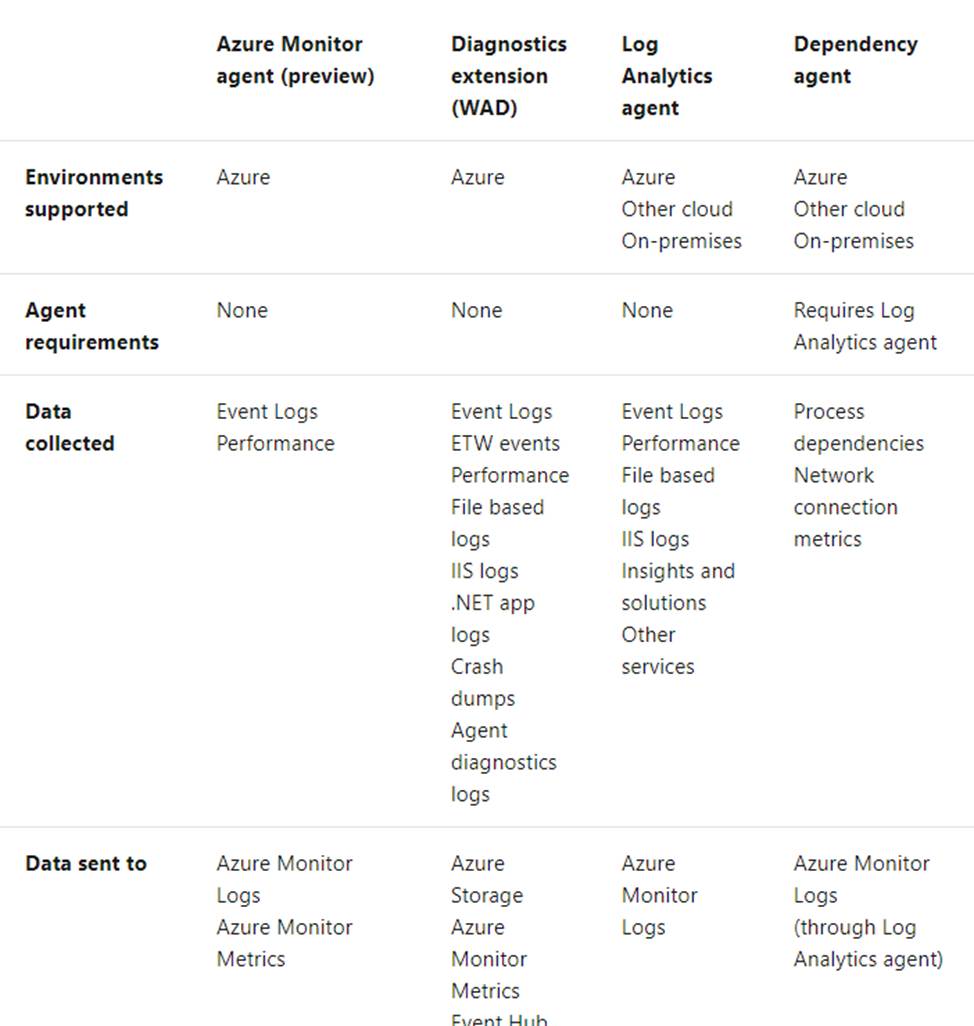
Reference: https://docs.microsoft.com/en-us/azure/azure-monitor/platform/agents-overview
HOTSPOT
You have an Azure subscription that contains the resources shown in the following table.
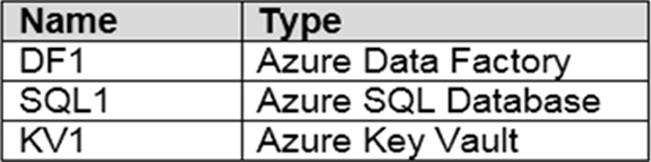
You plan to create a linked service in DF1. The linked service will connect to SQL1 by using Microsoft SQL Server authentication. The password for the SQL Server login will be stored in KV1.
You need to configure DF1 to retrieve the password when the data factory connects to SQL1. The solution must use the principle of least privilege.
How should you configure DF1? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
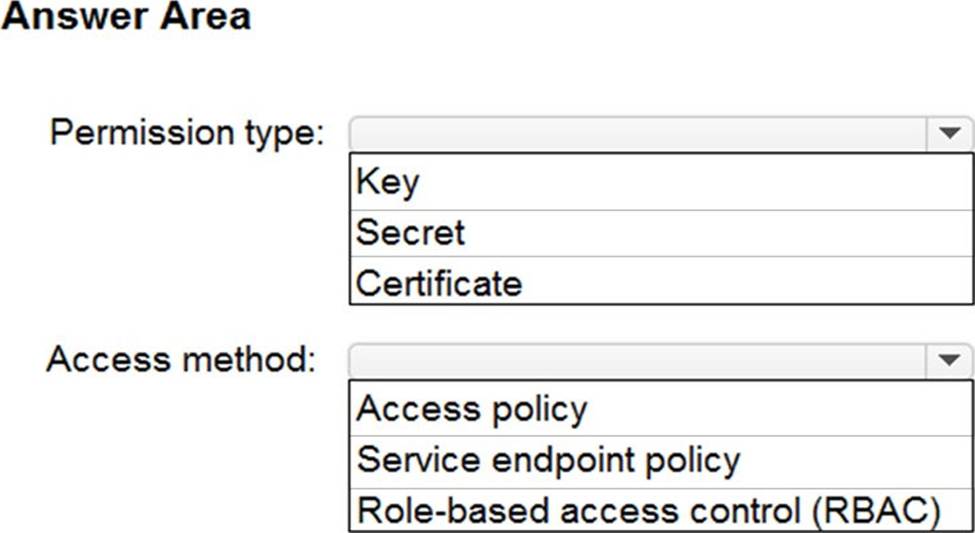
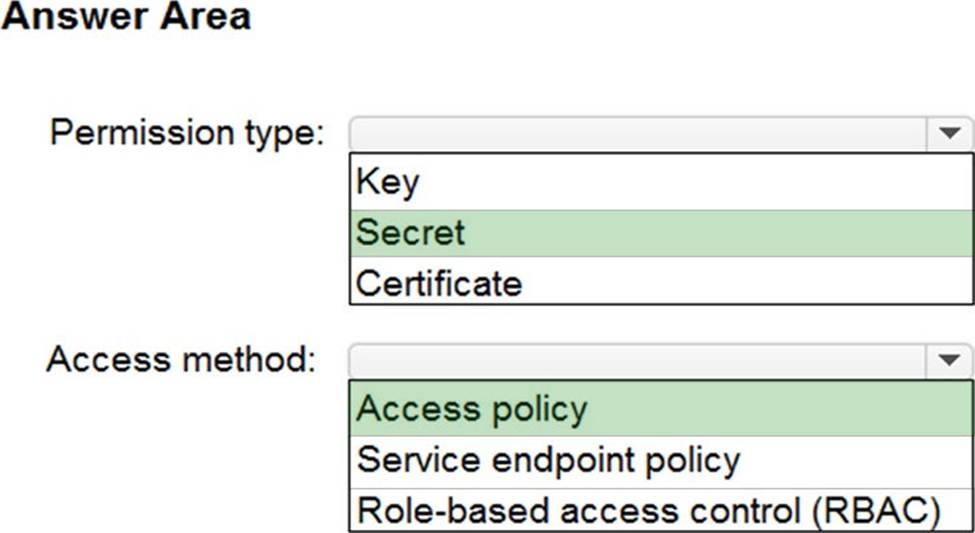
Explanation:
Box 1: Secret
Store credential in Azure Key Vault by reference secret stored in key vault.
To reference a credential stored in Azure Key Vault, you need to:
Retrieve data factory managed identity
Grant the managed identity access to your Azure Key Vault. In your key vault-> Access policies -> Add Access Policy, search this managed identity to grant Get permission in Secret permissions dropdown.
It allows this designated factory to access secret in key vault.
Create a linked service pointing to your Azure Key Vault.
Create data store linked service, inside which reference the corresponding secret stored in key vault.
Box 2: Access policy
Reference: https://docs.microsoft.com/en-us/azure/data-factory/store-credentials-in-key-vault
You have a GitHub repository.
You need to create a tag named v3.0.5 and ensure that the tag is available in the remote repository.
Which two commands should you run? Each correct answer presents part of the solution. NOTE: Each correct selection is worth one point.
- A . git coamit -m ‘tag v3.6.5’
- B . git push origin v3.0.5
- C . git tag V3.9.5
- D . git push -force
- E . git add ‘tag v3.6.5’
You have a GitHub repository.
You need to create a tag named v3.0.5 and ensure that the tag is available in the remote repository.
Which two commands should you run? Each correct answer presents part of the solution. NOTE: Each correct selection is worth one point.
- A . git coamit -m ‘tag v3.6.5’
- B . git push origin v3.0.5
- C . git tag V3.9.5
- D . git push -force
- E . git add ‘tag v3.6.5’
