Practice Free N10-009 Exam Online Questions
A company is purchasing a 40Gbps broadband connection service from an ISP.
Which of the following should most likely be configured on the 10G switch to take advantage of the new service?
- A . 802.1Q tagging
- B . Jumbo frames
- C . Half duplex
- D . Link aggregation
D
Explanation:
Since the switch supports only 10Gbps per port, achieving 40Gbps throughput requires link aggregation (LACP), which combines multiple 10Gbps links into one logical interface for higher bandwidth.
Breakdown of Options:
While troubleshooting a VoIP handset connection, a technician’s laptop is able to successfully connect to network resources using the same port. The technician needs to identify the port on the switch.
Which of the following should the technician use to determine the switch and port?
- A . LLDP
- B . IKE
- C . VLAN
- D . netstat
A
Explanation:
Link Layer Discovery Protocol (LLDP) is a network protocol used for discovering devices and their capabilities on a local area network, primarily at the data link layer (Layer 2). It helps in identifying the connected switch and the specific port to which a device is connected. When troubleshooting a VoIP handset connection, the technician can use LLDP to determine the exact switch and port where the handset is connected. This protocol is widely used in network management to facilitate the discovery of network topology and simplify troubleshooting.
Other options such as IKE (Internet Key Exchange), VLAN (Virtual LAN), and netstat (network statistics) are not suitable for identifying the switch and port information. IKE is used in setting up secure IPsec connections, VLAN is used for segmenting networks, and netstat provides information about active connections and listening ports on a host but not for discovering switch port details.
Reference: CompTIA Network+ Certification Exam Objectives – Network Troubleshooting and Tools section.
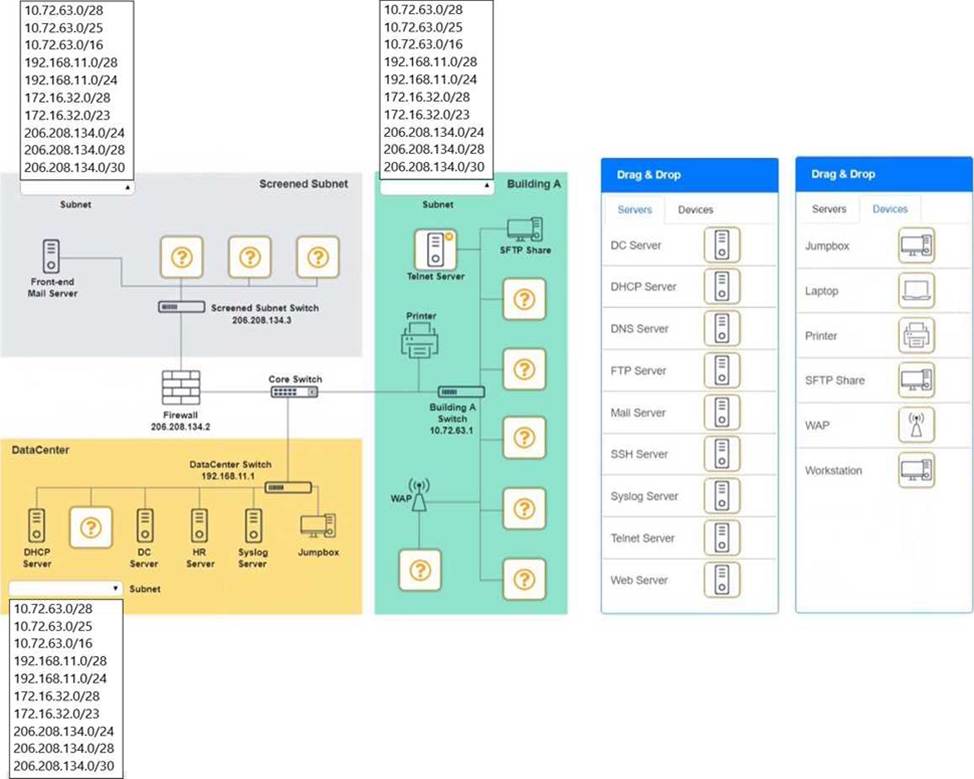
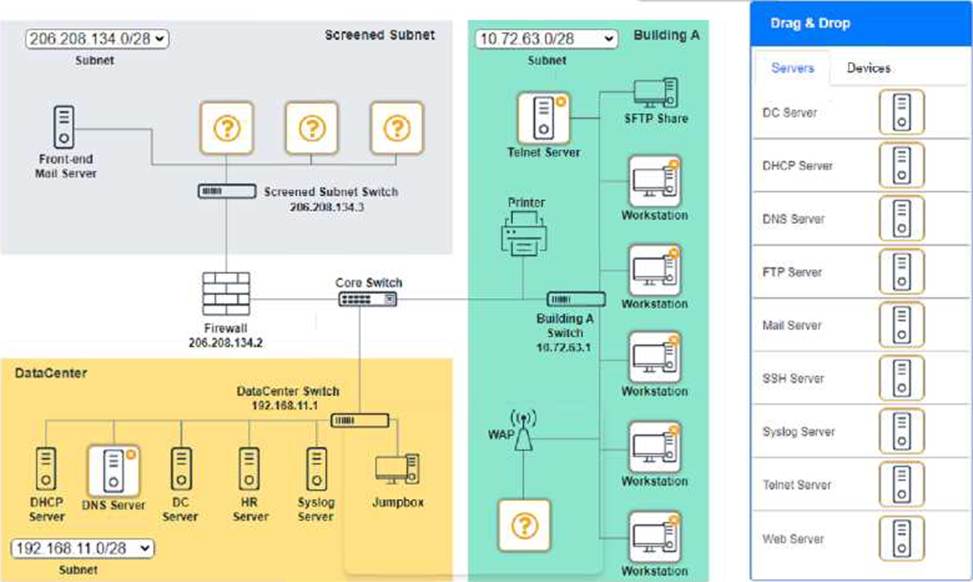
SIMULATION
You are tasked with verifying the following requirements are met in order to ensure network security.
Requirements:
Datacenter
Ensure network is subnetted to allow all devices to communicate properly while minimizing address space usage
Provide a dedicated server to resolve IP addresses and hostnames correctly and handle port 53 traffic Building A
Ensure network is subnetted to allow all devices to communicate properly while minimizing address space usage
Provide devices to support 5 additional different office users
Add an additional mobile user
Replace the Telnet server with a more secure solution
Screened subnet
Ensure network is subnetted to allow all devices to communicate properly while minimizing address space usage
Provide a server to handle external 80/443 traffic
Provide a server to handle port 20/21 traffic
INSTRUCTIONS
Drag and drop objects onto the appropriate locations. Objects can be used multiple times and not all placeholders need to be filled.
Available objects are located in both the Servers and Devices tabs of the Drag & Drop menu.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
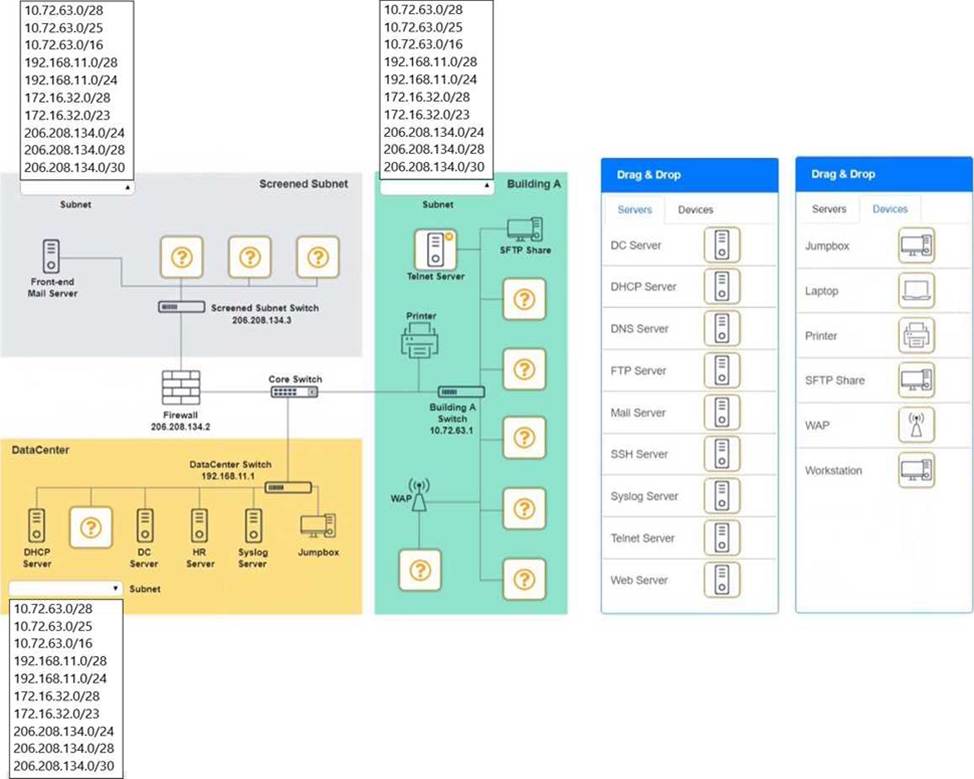
Building A devices C SSH server top left, workstations on all 5 on the right, laptop on bottom left DataCenter devices C DNS server.
A screenshot of a computer AI-generated content may be incorrect.
A screenshot of a computer AI-generated content may be incorrect. A screenshot of a computer AI-generated content may be incorrect.
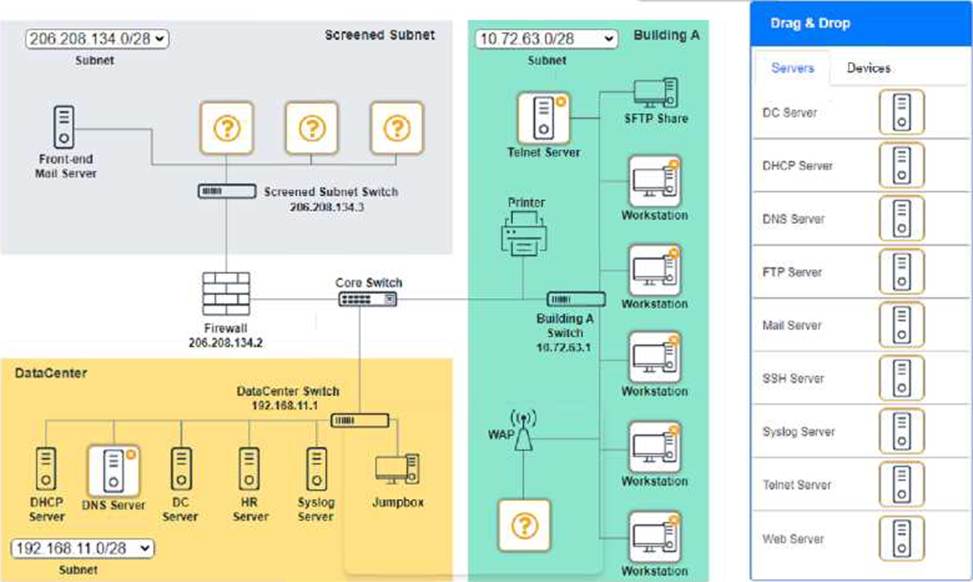
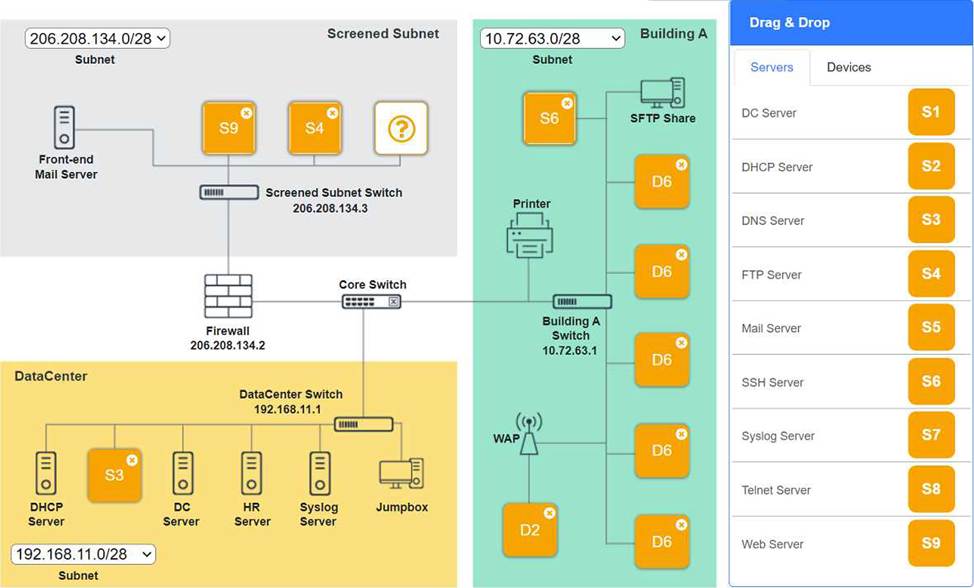
SIMULATION
You are tasked with verifying the following requirements are met in order to ensure network security.
Requirements:
Datacenter
Ensure network is subnetted to allow all devices to communicate properly while minimizing address space usage
Provide a dedicated server to resolve IP addresses and hostnames correctly and handle port 53 traffic Building A
Ensure network is subnetted to allow all devices to communicate properly while minimizing address space usage
Provide devices to support 5 additional different office users
Add an additional mobile user
Replace the Telnet server with a more secure solution
Screened subnet
Ensure network is subnetted to allow all devices to communicate properly while minimizing address space usage
Provide a server to handle external 80/443 traffic
Provide a server to handle port 20/21 traffic
INSTRUCTIONS
Drag and drop objects onto the appropriate locations. Objects can be used multiple times and not all placeholders need to be filled.
Available objects are located in both the Servers and Devices tabs of the Drag & Drop menu.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
Building A devices C SSH server top left, workstations on all 5 on the right, laptop on bottom left DataCenter devices C DNS server.
A screenshot of a computer AI-generated content may be incorrect.
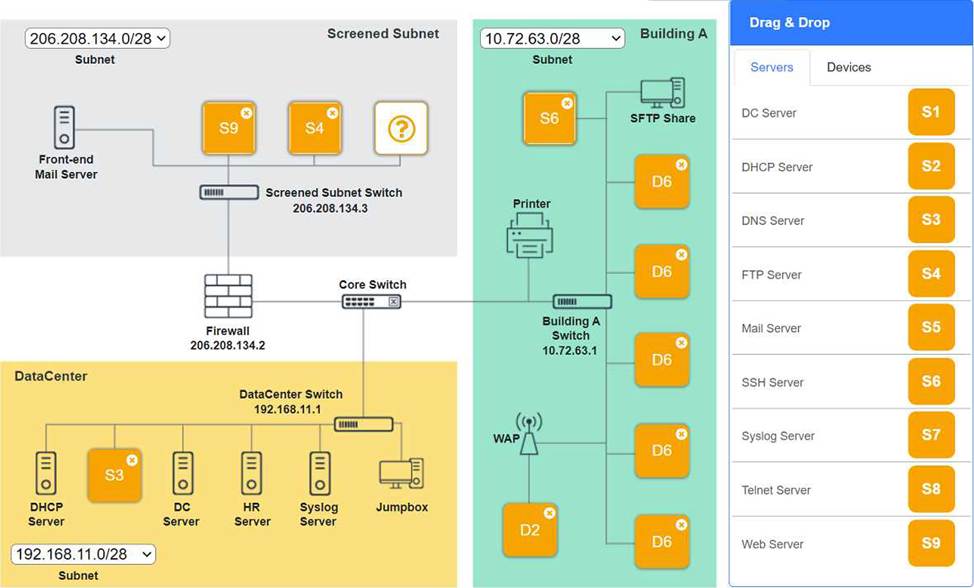
A screenshot of a computer AI-generated content may be incorrect. A screenshot of a computer AI-generated content may be incorrect.
Which of the following best describes the purpose of a UPS and PDU in a network installation?
- A . To support voltage requirements for devices in an IDF
- B . To manage power consumption in the MDF
- C . To connect multiple devices to a single network connection
- D . To regulate temperature in the MDF and IDF
A
Explanation:
A UPS (Uninterruptible Power Supply) and PDU (Power Distribution Unit) are installed to provide reliable, properly distributed electrical power to network equipment―especially in wiring closets such as an IDF and in main equipment rooms. In Network+ (N10-009) infrastructure objectives, a UPS protects against power loss and instability by supplying battery-backed power during outages and often providing conditioning to reduce the impact of sags, spikes, and brief interruptions. A PDU then distributes that power to multiple devices in a rack (switches, routers, firewalls, AP controllers), often offering organized outlets and, in managed models, monitoring/control features.
Option A is the best match because it reflects the practical purpose: ensuring network devices receive appropriate and continuous power in distribution frames/closets.
Option B is partially related, but “managing power consumption in the MDF” is too narrow and not as accurate as the broader function of providing backup and distribution power.
Option C describes a network switch, not power equipment.
Option D refers to HVAC/environmental controls, not UPS/PDU functionality.
Hence, A is correct.
Which of the following would describe a data recovery goal?
- A . MTBF
- B . RPO
- C . BCP
- D . MTTR
B
Explanation:
RPO (Recovery Point Objective) describes a data recovery goal by defining the maximum acceptable amount of data loss measured in time. For example, an RPO of 4 hours means the organization must be able to restore data to a point no more than four hours before the outage―so backups, replication, or snapshots must occur frequently enough to meet that target. In Network+ (N10-009) operations objectives, disaster recovery and business continuity concepts include understanding recovery metrics and how they influence backup strategies, replication design, and service resilience planning. RPO specifically answers: “How much data can we afford to lose?”
By contrast, MTBF (Mean Time Between Failures) is a reliability metric describing how often failures occur. MTTR (Mean Time To Repair/Recover) measures how long it takes to restore a system after failure, which is more aligned with service restoration time rather than data loss. BCP (Business Continuity Plan) is the overall plan/process for keeping critical business functions running during disruptions; it is not a single data recovery metric. Therefore, RPO is the correct term for a data recovery goal.
A user reports having intermittent connectivity issues to the company network.
The network configuration for the user reveals the following:
IP address: 192.168.1.10
Subnet mask: 255.255.255.0
Default gateway: 192.168.1.254
The network switch shows the following ARP table:
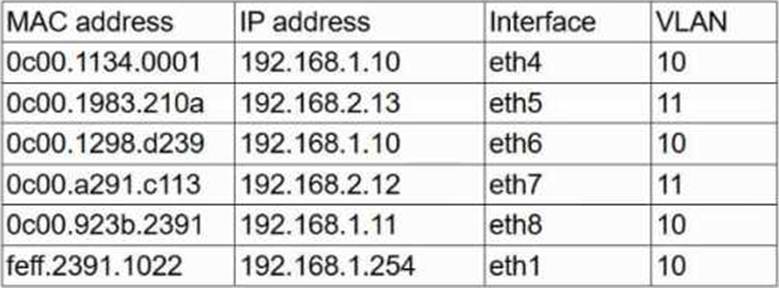
Which of the following is the most likely cause of the user’s connection issues?
- A . A port with incorrect VLAN assigned
- B . A switch with spanning tree conflict
- C . Another PC with manually configured IP
- D . A router with overlapping route tables
C
Explanation:
This scenario describes a duplicate IP address. The ARP table shows two different MAC addresses (0c00.1134.0001 and 0c00.1298.d239) associated with the same IP address (192.168.1.10), which leads to ARP table conflicts and intermittent connectivity.
From Andrew Ramdayal’s guide:
“Duplicate IP addresses occur when two devices on the same network are assigned the same IP address, causing network conflicts. Common issues include manual configuration errors or DHCP lease issues. Resolution includes using IP management tools and avoiding overlaps in DHCP and static IP assignments.”
A network administrator is configuring a new switch and wants to ensure that only assigned devices can connect to the switch.
Which of the following should the administrator do?
- A . Configure ACLs.
- B . Implement a captive portal.
- C . Enable port security.
- D . Disable unnecessary services.
C
Explanation:
Reference: CompTIA Network+ Certification Exam Objectives – Network Security section.
A network administrator is configuring a new switch and wants to ensure that only assigned devices can connect to the switch.
Which of the following should the administrator do?
- A . Configure ACLs.
- B . Implement a captive portal.
- C . Enable port security.
- D . Disable unnecessary services.
C
Explanation:
Reference: CompTIA Network+ Certification Exam Objectives – Network Security section.
A network administrator needs to create a way to redirect a network resource that has been on the local network but is now hosted as a SaaS solution.
Which of the following records should be used to accomplish the task?
- A . TXT
- B . AAA
- C . PTR
- D . CNAME
D
Explanation:
To redirect a network resource that has moved from a local network to a Software-as-a-Service (SaaS) solution, the network administrator needs to configure a DNS record that maps an alias to the new canonical name (hostname) of the SaaS provider’s server. The CNAME (Canonical Name) record is used to alias one domain name to another, effectively redirecting requests to the new hostname without needing to update the IP address directly. This is ideal for SaaS solutions, where the provider’s server hostname is used, and the IP address may change dynamically.
Why not TXT? A TXT record is used to store arbitrary text data, such as SPF records for email authentication or verification strings, not for redirecting resources.
Why not AAA? There is no such thing as an "AAA" record in DNS. This might be a typo for AAAA (IPv6 address record), but AAAA maps a hostname to an IPv6 address, not an alias.
Why not PTR? A PTR record is used for reverse DNS lookups (mapping an IP address to a hostname), not for redirecting a resource to a new hostname.
Reference: CompTIA Network+ N10-009 Objective 1.5: Compare and contrast common network services and ports. The CNAME record is discussed under DNS configuration in the CompTIA Network+ Certification Study Guide (e.g., Mike Meyers’ CompTIA Network+ Guide, Chapter 7: TCP/IP Applications). The guide explains that CNAME records are used to create aliases for hostnames, particularly useful for redirecting services to external providers like SaaS solutions.
