Practice Free N10-009 Exam Online Questions
A network administrator needs to connect a department to a new network segment. They need to use a DHCP server located on another network.
Which of the following can the administrator use to complete this task?
- A . IP Helper
- B . Reservation
- C . Exclusion
- D . Scope
A
Explanation:
An IP Helper (IP Helper Address) allows DHCP requests to pass through routers and reach a DHCP server on another network.
DHCP broadcasts are not forwarded across routers by default, so an IP Helper Address is needed to relay the request.
This is crucial for large networks where a single DHCP server serves multiple subnets.
Option B (Reservation): Ensures a specific IP address is assigned to a MAC address but does not relay DHCP across networks.
Option C (Exclusion): Prevents specific IP addresses from being assigned, but does not help with DHCP relay.
Option D (Scope): Defines the range of IP addresses available for DHCP clients but does not assist in cross-network communication.
Reference: CompTIA Network+ (N10-009) Official Study Guide C Section: DHCP and IP Addressing
A network security administrator needs to monitor the contents of data sent between a secure network and the rest of the company.
Which of the following monitoring methods will accomplish this task?
- A . Port mirroring
- B . Flow data
- C . Syslog entries
- D . SNMP traps
A
Explanation:
To monitor the contents of data (i.e., inspect the actual packets/frames and their payloads) moving between networks, the administrator should use port mirroring (also called SPAN on some platforms). Port mirroring copies traffic from one or more switch ports (or VLANs) to a designated monitoring port where a packet analyzer/IDS sensor can capture and inspect the traffic in detail. This aligns with Network+ (N10-009) security and monitoring concepts that distinguish between packet-level visibility and higher-level summaries or logs. If the requirement is explicitly to monitor “contents,” you need a method that provides full packet capture capability, not just metadata.
Flow data (e.g., NetFlow) provides summarized metadata―who talked to whom, how much, ports, and timestamps―but not full payload contents. Syslog entries are device/application-generated logs and only show events a device chooses to report; they don’t provide full data content visibility. SNMP traps are alerts about status changes (interfaces, thresholds, etc.) and similarly do not include traffic contents. Therefore, port mirroring is the correct monitoring method for inspecting data contents in transit.
Which of the following ports is used for secure email?
- A . 25
- B . 110
- C . 143
- D . 587
D
Explanation:
Port 587 is used for secure email submission. This port is designated for message submission by mail clients to mail servers using the SMTP protocol, typically with STARTTLS for encryption.
Port 25: Traditionally used for SMTP relay, but not secure and often blocked by ISPs for outgoing mail due to spam concerns.
Port 110: Used for POP3 (Post Office Protocol version 3), not typically secured.
Port 143: Used for IMAP (Internet Message Access Protocol), which can be secured with STARTTLS or SSL/TLS.
Port 587: Specifically used for authenticated email submission (SMTP) with encryption, ensuring secure transmission of email from clients to servers.
Network
Reference: CompTIA Network+ N10-007 Official Certification Guide: Discusses email protocols and ports, including secure email transmission.
Cisco Networking Academy: Provides training on securing email communications and the use of appropriate ports.
Network+ Certification All-in-One Exam Guide: Explains email protocols, ports, and security considerations for email transmission.
A network engineer configures an application server so that it automatically adjusts resource allocation as demand changes. This server will host a new application and demand is not predictable.
Which of the following concepts does this scenario demonstrate?
- A . Scalability
- B . Software as a Service
- C . Hybrid cloud
- D . Elasticity
D
Explanation:
Elasticity is the ability of a system (often in cloud environments) to automatically scale resources up or down in real time based on demand.
A network administrator is configuring a network for a new site that will have 150 users. Within the next year, the site is expected to grow by ten users. Each user will have two IP addresses, one for a computer and one for a phone connected to the network.
Which of the following classful IPv4 address ranges will be best-suited for the network?
- A . Class D
- B . Class B
- C . Class A
- D . Class C
D
Explanation:
IPv4 addresses are divided into classes:
Class A: Supports 16,777,214 hosts (large enterprises).
Class B: Supports 65,534 hosts (medium to large networks).
Class C: Supports 254 hosts (small to medium networks).
Class D: Used for multicast, not for assigning IPs to hosts.
Step-by-step Calculation:
The network will have 150 users initially, with a projected growth of 10 users, totaling 160 users.
Each user has two devices, so 160 × 2 = 320 IP addresses needed.
A Class C subnet has 254 usable IPs by default, which is not sufficient.
A Class B subnet can support thousands of hosts, making it the most appropriate option.
Incorrect Options:
Which of the following troubleshooting steps provides a change advisory board with the information needed to make a decision?
- A . Identify the problem
- B . Develop a theory of probable cause
- C . Test the theory to determine cause
- D . Establish a plan of action
D
Explanation:
When dealing with troubleshooting and change management, the plan of action outlines the steps, risks, and mitigation strategies. A change advisory board (CAB) uses this documented plan to decide whether to approve the change.
A network engineer is now in charge of all SNMP management in the organization. The engineer must use a SNMP version that does not utilize plaintext data.
Which of the following is the minimum version of SNMP that supports this requirement?
- A . v1
- B . v2c
- C . v2u
- D . v3
D
Explanation:
SNMPv3 is the version of the Simple Network Management Protocol that introduces security enhancements, including message integrity, authentication, and encryption. Unlike previous versions (v1 and v2c), SNMPv3 supports encrypted communication, ensuring that data is not transmitted in plaintext. This provides confidentiality and protects against eavesdropping and unauthorized access.
Reference: CompTIA Network+ study materials.
A research facility is expecting to see an exponential increase in global network traffic in the near future. The offices are equipped with 2.5Gbps fiber connections from the ISP, but the facility is currently only utilizing 1Gbps connections.
Which of the following would need to be configured in order to use the ISP’s connection speed?
- A . 802.1Q tagging
- B . Network address translation
- C . Port duplex
- D . Link aggregation
D
Explanation:
Understanding Link Aggregation:
Definition: Link aggregation combines multiple network connections into a single logical link to increase bandwidth and provide redundancy.
Usage in High-Bandwidth Scenarios:
Combining Links: By aggregating multiple 1Gbps connections, the facility can utilize the full 2.5Gbps bandwidth provided by the ISP.
Benefits: Enhanced throughput, load balancing, and redundancy, ensuring better utilization of available bandwidth.
Comparison with Other Options:
SIMULATION
A network technician was recently onboarded to a company. A manager has tasked the technician with documenting the network and has provided the technician With partial information from previous documentation.
Instructions:
Click on each switch to perform a network discovery by entering commands into the terminal. Fill in the missing information using drop-down menus provided.
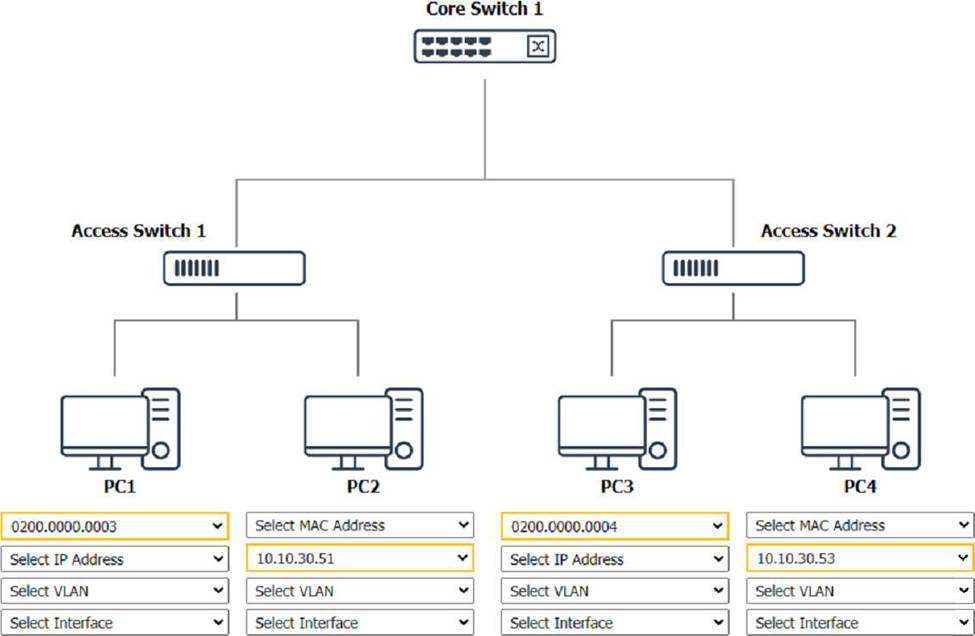
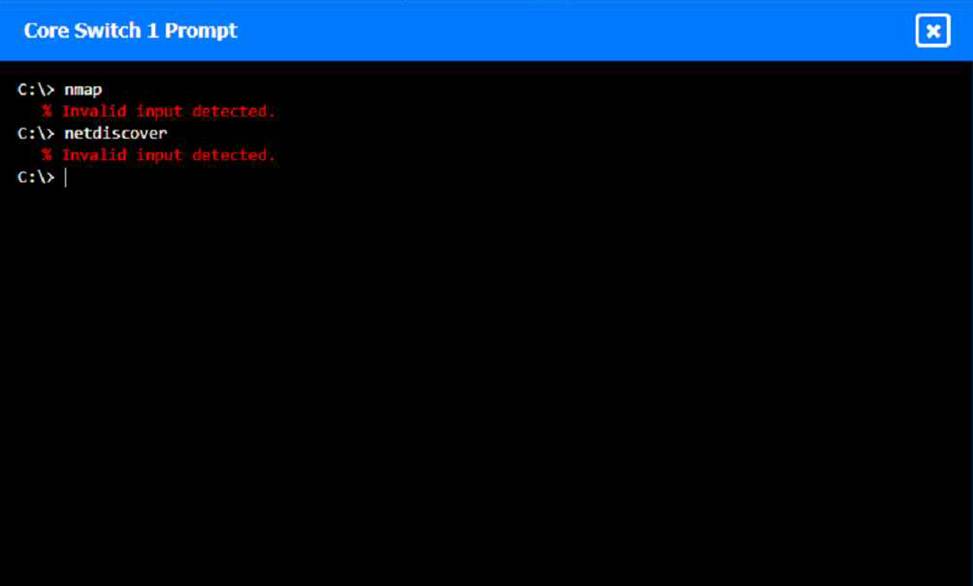
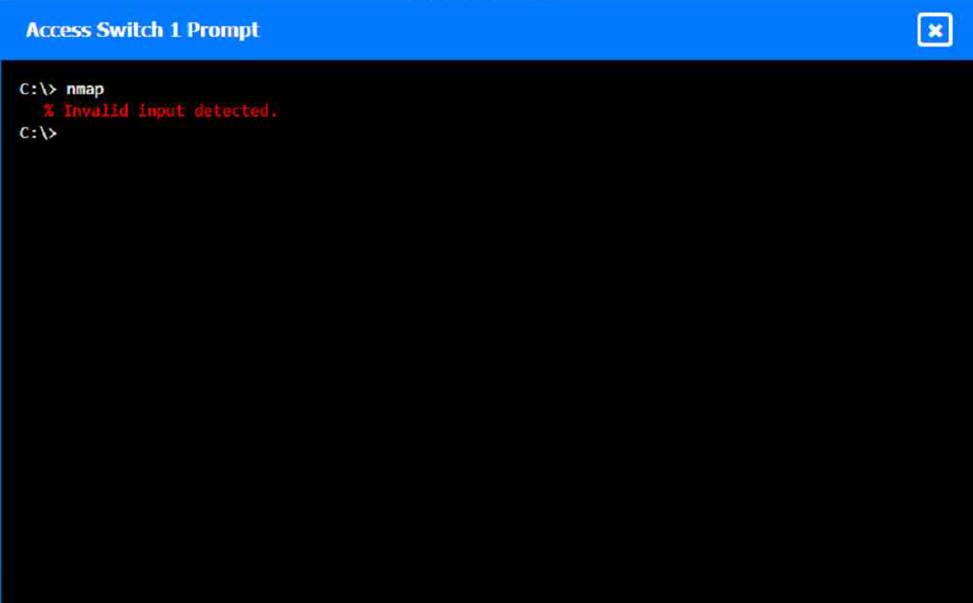
To perform a network discovery by entering commands into the terminal, you can use the following steps:
Click on each switch to open its terminal window.
Enter the command show ip interface brief to display the IP addresses and statuses of the switch interfaces.
Enter the command show vlan brief to display the VLAN configurations and assignments of the switch interfaces.
Enter the command show cdp neighbors to display the information about the neighboring devices that are connected to the switch.
Fill in the missing information in the diagram using the drop-down menus provided.
Here is an example of how to fill in the missing information for Core Switch 1:
The IP address of Core Switch 1 is 192.168.1.1.
The VLAN configuration of Core Switch 1 is VLAN 1: 192.168.1.0/24, VLAN 2: 192.168.2.0/24, VLAN 3:
Which of the following connection methods allows a network engineer to automate the configuration deployment for network devices across the environment?
- A . RDP
- B . Telnet
- C . GUI
- D . API
D
Explanation:
Comprehensive and Detailed Explanation (aligned to N10-009):
APIs (Application Programming Interfaces) allow automation tools and scripts to push configurations to network devices programmatically. Modern network automation platforms rely on APIs to ensure consistency and scalability.
