Practice Free N10-009 Exam Online Questions
A network administrator configures a new network discovery tool and is concerned that it might disrupt business operations.
Which of the following scan types should the administrator configure?
- A . Authenticated
- B . Ad hoc
- C . Unauthenticated
- D . Scheduled
D
Explanation:
If the administrator is concerned a new discovery tool could disrupt operations, the safest option is to configure scheduled scans. Network+ (N10-009) operations guidance emphasizes minimizing impact by running potentially noisy tasks (discovery, vulnerability checks, inventory scans) during defined maintenance windows or off-peak hours. A scheduled scan allows controlled timing, predictable load, and easier coordination with change management, monitoring, and support teams. This reduces the risk of saturating links, overwhelming devices with queries, or triggering alerts during business-critical periods.
Ad hoc scanning is on-demand and may occur at any time, which increases the chance of disruption if run during peak usage. Authenticated versus unauthenticated describes whether the scanner uses credentials to log into systems for deeper visibility; that choice affects depth and accuracy, but it doesn’t directly address when scanning occurs to reduce business impact. An authenticated scan can still be disruptive if run at the wrong time, and an unauthenticated scan can still generate significant traffic. Since the key concern is operational disruption, controlling scan timing via scheduled scans is the best mitigation.
A company’s Chief Information Security Officer requires that servers and firewalls have accurate time stamps when creating log files so that security analysts can correlate events during incident investigations.
Which of the following should be implemented?
- A . Syslog server
- B . SMTP
- C . NTP
- D . SNMP
C
Explanation:
The correct solution is NTP (Network Time Protocol). Accurate timestamps across servers, firewalls, and network devices are critical for correlating logs during incident response. NTP synchronizes device clocks to a trusted time source, ensuring consistency across the network.
Network administrators are using the Telnet protocol to administer network devices that are on the 192.168.1.0/24 subnet.
Which of the following tools should the administrator use to best identify the devices?
- A . dig
- B . nmap
- C . tracert
- D . telnet
B
Explanation:
nmap (Network Mapper) is the best tool in this scenario. It can scan the 192.168.1.0/24 subnet to discover live hosts, open ports (like Telnet on port 23), and device types. It’s ideal for mapping and auditing the network.
SIMULATION
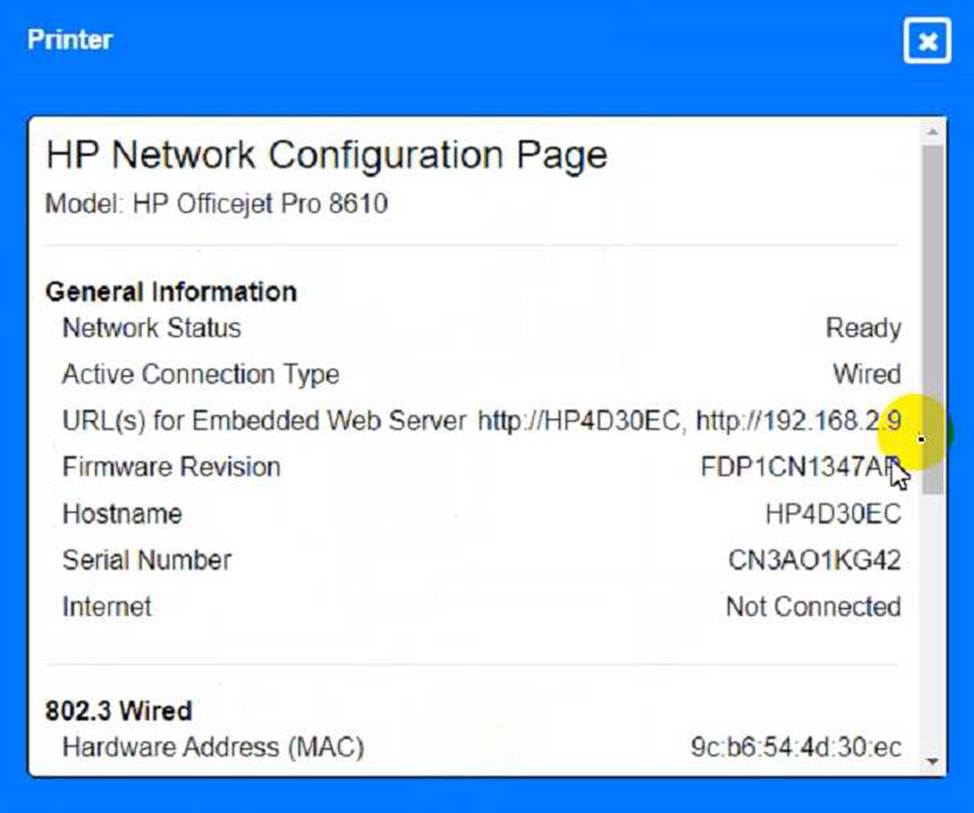
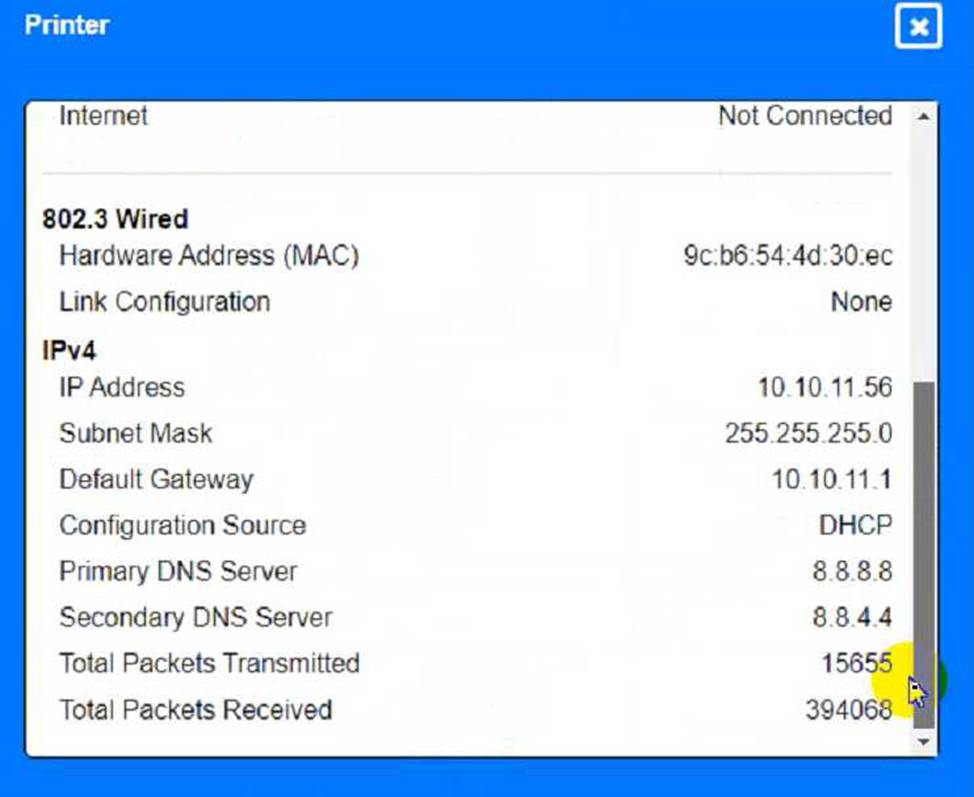
A network technician needs to resolve some issues with a customer’s SOHO network.
The customer reports that some of the devices are not connecting to the network, while others appear to work as intended.
INSTRUCTIONS
Troubleshoot all the network components and review the cable test results by Clicking on each device and cable.
Diagnose the appropriate component(s) by identifying any components with a problem and recommend a solution to correct each problem.
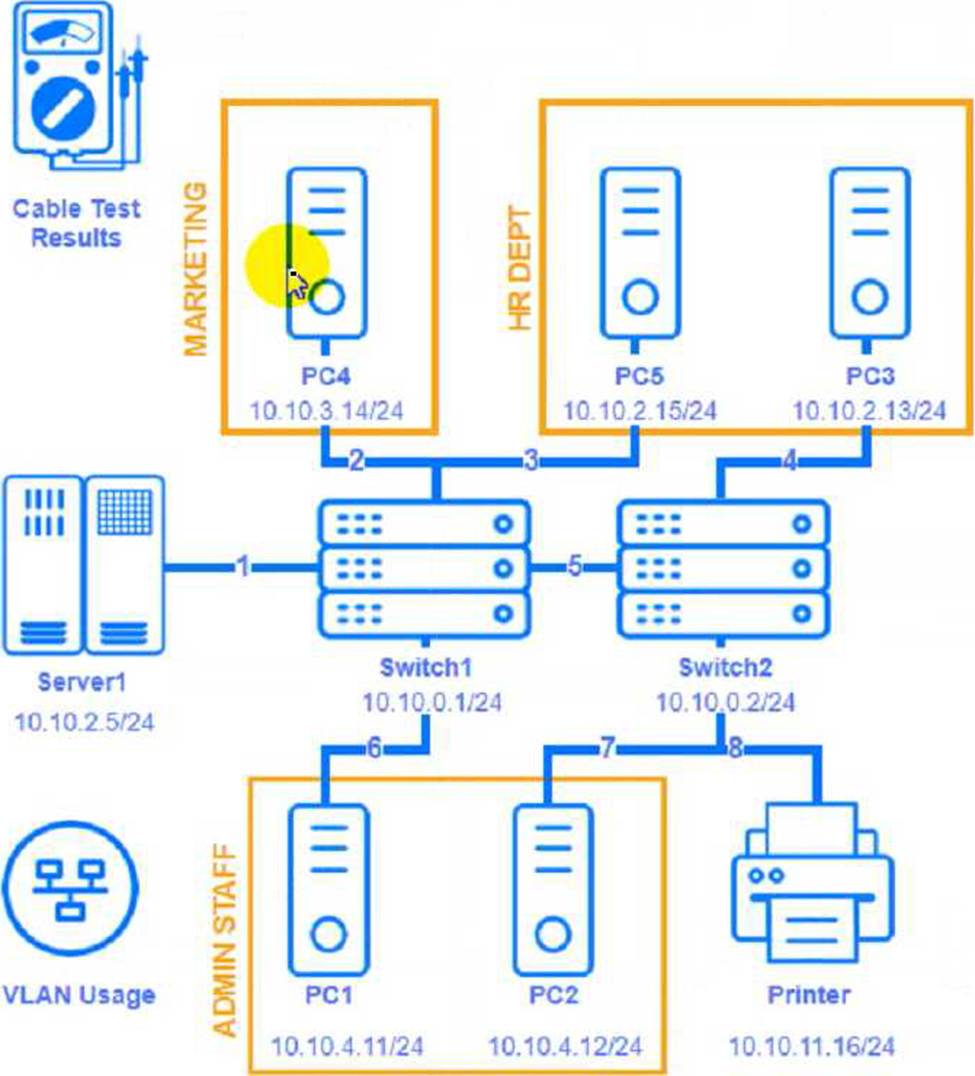


Cable Test Results:
Cable 1:
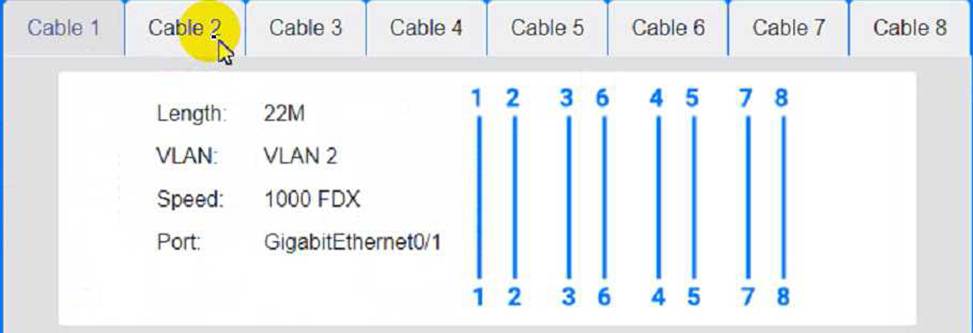
Cable 2:
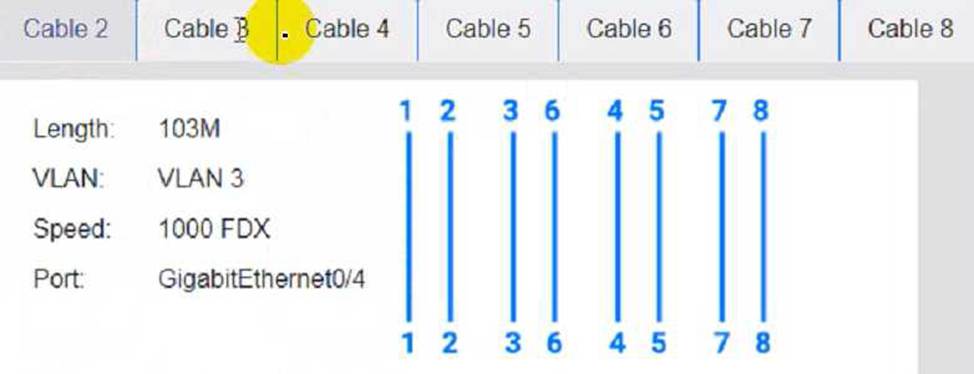
Cable 3:
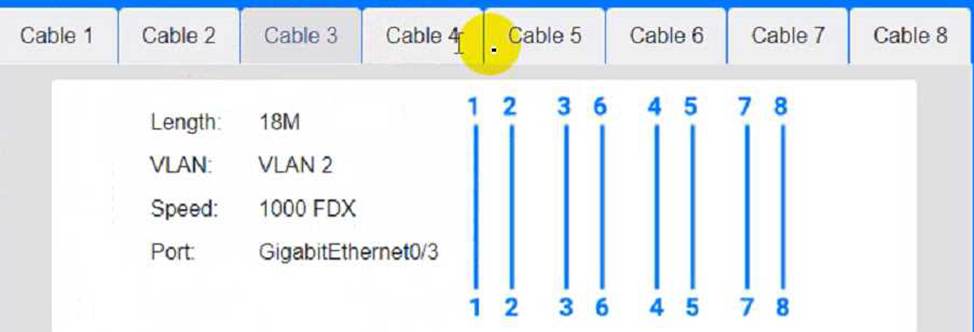
Cable 4:
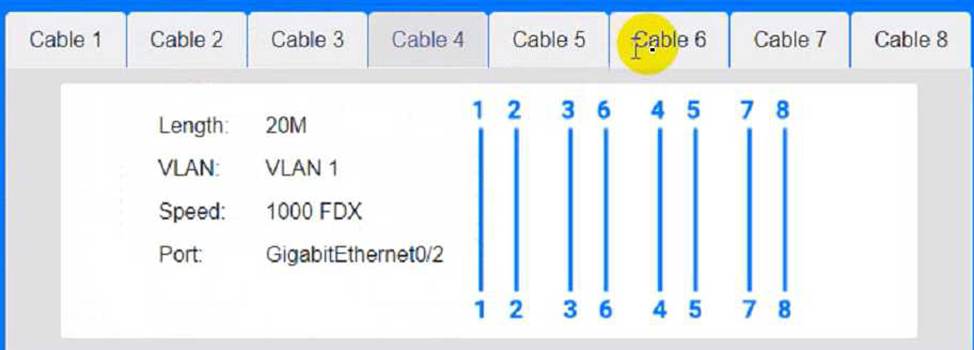
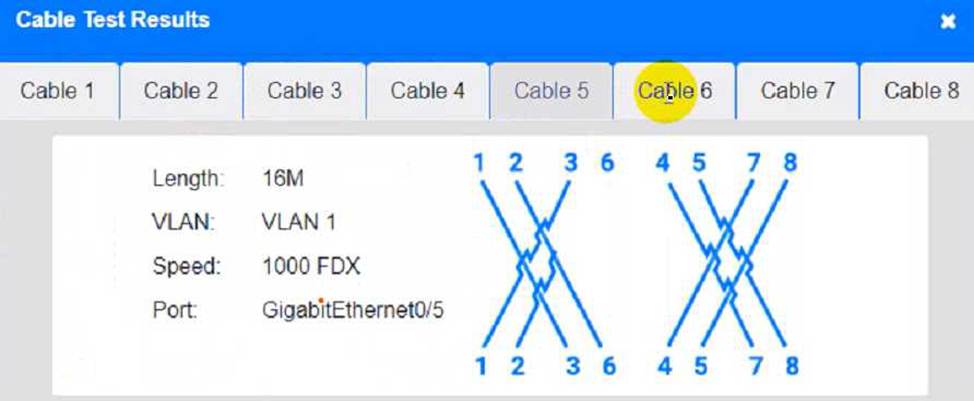
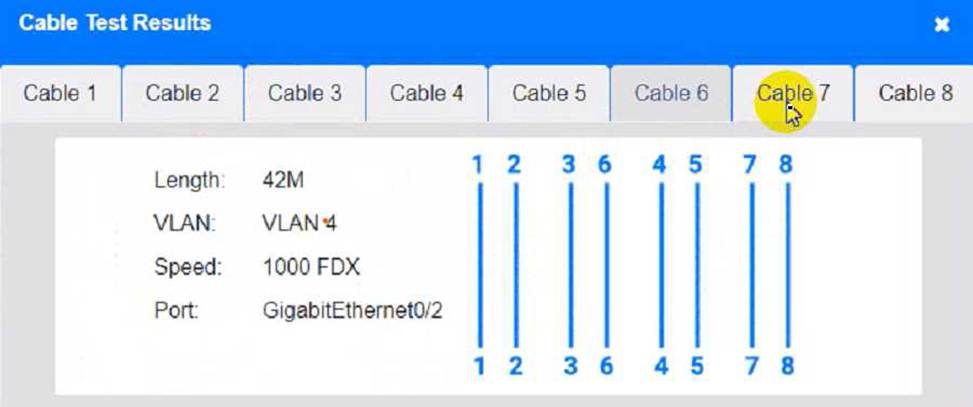
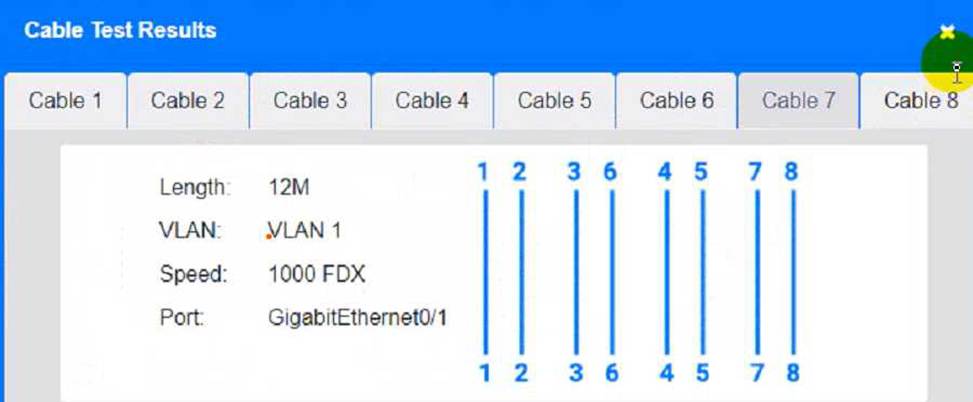
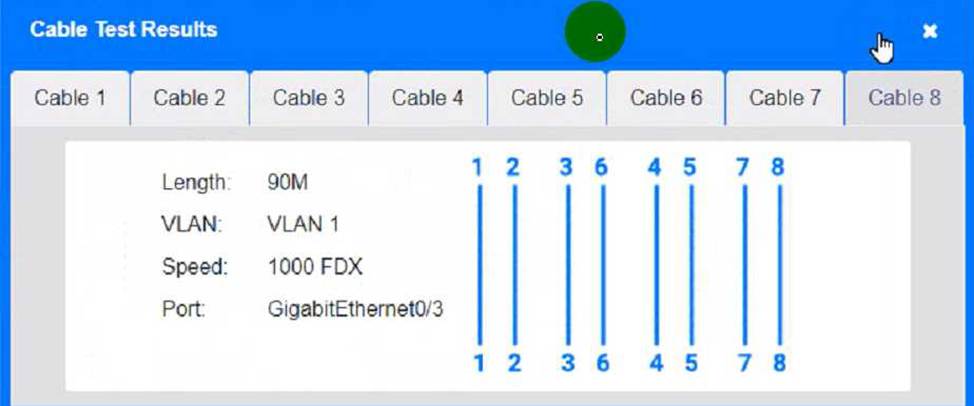
To troubleshoot all the network components and review the cable test results, you can use the following steps:
Click on each device and cable to open its information window.
Review the information and identify any problems or errors that may affect the network connectivity or performance.
Diagnose the appropriate component(s) by identifying any components with a problem and recommend a solution to correct each problem.
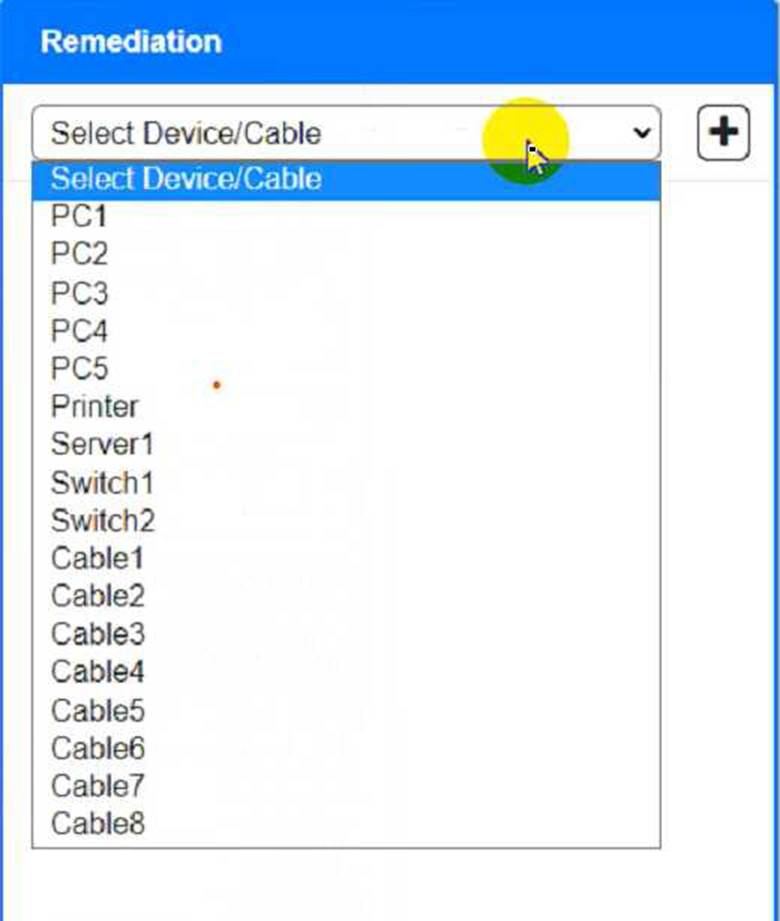
Fill in the remediation form using the drop-down menus provided.
Here is an example of how to fill in the remediation form for PC1:
The component with a problem is PC1.
The problem is Incorrect IP address.
The solution is Change the IP address to 192.168.1.10.
You can use the same steps to fill in the remediation form for other components.
To enter commands in each device, you can use the following steps:
Click on the device to open its terminal window.
Enter the command ipconfig /all to display the IP configuration of the device, including its IP address, subnet mask, default gateway, and DNS servers.
Enter the command ping <IP address> to test the connectivity and reachability to another device on the network by sending and receiving echo packets. Replace <IP address> with the IP address of the
destination device, such as 192.168.1.1 for Core Switch 1.
Enter the command tracert <IP address> to trace the route and measure the latency of packets from the device to another device on the network by sending and receiving packets with increasing TTL values. Replace <IP address> with the IP address of the destination device, such as 192.168.1.1 for Core Switch 1.
Here is an example of how to enter commands in PC1:
Click on PC1 to open its terminal window.
Enter the command ipconfig /all to display the IP configuration of PC1. You should see that PC1 has an incorrect IP address of 192.168.2.10, which belongs to VLAN 2 instead of VLAN 1.
Enter the command ping 192.168.1.1 to test the connectivity to Core Switch 1. You should see that PC1 is unable to ping Core Switch 1 because they are on different subnets.
Enter the command tracert 192.168.1.1 to trace the route to Core Switch 1. You should see that PC1 is unable to reach Core Switch 1 because there is no route between them.
You can use the same steps to enter commands in other devices, such as PC3, PC4, PC5, and Server 1.
A network administrator is in the process of installing 35 PoE security cameras. After the administrator installed and tested the new cables, the administrator installed the cameras. However, a small number of the cameras do not work.
Which of the following is the most reason?
- A . Incorrect wiring standard
- B . Power budget exceeded
- C . Signal attenuation
- D . Wrong voltage
B
Explanation:
When installing multiple Power over Ethernet (PoE) devices like security cameras, it is crucial to ensure that the total power requirement does not exceed the power budget of the PoE switch. Each PoE switch has a maximum power capacity, and exceeding this capacity can cause some devices to fail to receive power.
PoE Standards: PoE switches conform to standards such as IEEE 802.3af (PoE) and 802.3at (PoE+), each with specific power limits per port and total power capacity.
Power Calculation: Adding up the power requirements of all connected PoE devices can help determine if the total power budget of the switch is exceeded.
Symptoms: When the power budget is exceeded, some devices, typically those farthest from the switch or connected last, may not power up or function correctly.
Network
Reference: CompTIA Network+ N10-007 Official Certification Guide: Covers PoE standards and troubleshooting power issues.
Cisco Networking Academy: Discusses PoE technologies, power budgeting, and managing PoE devices.
Network+ Certification All-in-One Exam Guide: Provides information on PoE setup, including power budget considerations.
After installing a new 6E wireless router in a small office, a technician notices that some wireless devices are not able to achieve the rated speeds.
Which of the following should the technician check to troubleshoot the issue? (Select two)
- A . Client device compatibility
- B . Back-end cabling
- C . Weather phenomena
- D . Voltage source requirements
- E . Interference levels
- F . Processing power
A company is opening a new site that needs to be divided into subnets that accommodate 75 hosts each.
Which of the following is the most efficient subnet?
- A . 192.168.13.0/25
- B . 192.168.13.0/26
- C . 192.168.13.0/27
- D . 192.168.13.0/28
A
Explanation:
To support 75 hosts per subnet, you must choose a subnet size that provides at least 75 usable IP addresses. In IPv4, usable hosts per subnet equals 2^(host bits) − 2 (subtracting network and broadcast). A /25 leaves 7 host bits (32C25 = 7), giving 2^7 − 2 = 128 − 2 = 126 usable hosts, which meets the requirement and is the smallest (most efficient) option listed that does so. A /26 leaves 6 host bits, giving 62 usable hosts, which is insufficient. A /27 gives 30 usable, and a /28 gives 14 usable, both far below 75. Network+ subnetting objectives emphasize selecting the smallest subnet that satisfies the host requirement to conserve address space while meeting growth and design constraints. Therefore, 192.168.13.0/25 is the most efficient option that accommodates at least 75 hosts per subnet.
A public library wants to implement a solution in which users need to connect to the wireless network and then authenticate via HTTPS with provided credentials.
Which of the following technologies fulfills this requirement?
- A . WPA3
- B . Captive portal
- C . Single sign-on
- D . SAML
B
Explanation:
The correct choice is B. Captive portal. This is the common setup used in places like libraries, hotels, airports, and cafés. A user first joins the wireless network, opens a browser, and is redirected to a web page where they must log in, accept terms, or enter provided credentials. Since the question specifically mentions authentication through HTTPS, that matches the behavior of a captive portal very closely.
The other options do not line up with the scenario. WPA3 is a wireless encryption and authentication standard, but it is not the same as a browser-based login page after connection. Single sign-on and SAML are identity and federation technologies used to simplify authentication across applications or services, not to provide the typical guest Wi-Fi web login experience.
The important clue is the sequence described in the question: first connect to Wi-Fi, then authenticate through a web page.
That is exactly how a captive portal works
In many public-access wireless environments, the portal sits between the client and normal internet access until the user successfully authenticates or accepts the usage policy. For Network+ exam purposes, browser-based guest wireless authentication is most directly associated with a captive portal.
A network engineer needs to order cabling to connect two buildings within the same city.
Which of the following media types should the network engineer use?
- A . Coaxial
- B . Twinaxial
- C . Single-mode fiber
- D . Cat 5
C
Explanation:
Single-mode fiber is best suited for long-distance communication, often exceeding 10 km (6.2 miles). It’s immune to EMI and offers high bandwidth ― making it the ideal choice for connecting buildings across a city.
Coaxial (A) and Twinaxial (B) are used for shorter distances and specific use cases (e.g., storage or legacy systems).
Cat 5 (D) is limited to 100 meters and is not suitable for city-level interconnects.
✅ For long-distance, high-speed, and reliable communication between buildings, Single-mode fiber is the professional choice.
Reference: CompTIA Network+ N10-009 Official Study Guide ― Objective 3.4: "Summarize the properties and purposes of physical network topologies and network types."
Which of the following would describe a data recovery goal?
- A . MTBF
- B . RPO
- C . BCP
- D . MTTR
B
Explanation:
RPO (Recovery Point Objective) describes a data recovery goal by defining the maximum acceptable amount of data loss measured in time. For example, an RPO of 4 hours means the organization must be able to restore data to a point no more than four hours before the outage―so backups, replication, or snapshots must occur frequently enough to meet that target. In Network+ (N10-009) operations objectives, disaster recovery and business continuity concepts include understanding recovery metrics and how they influence backup strategies, replication design, and service resilience planning. RPO specifically answers: “How much data can we afford to lose?”
By contrast, MTBF (Mean Time Between Failures) is a reliability metric describing how often failures occur. MTTR (Mean Time To Repair/Recover) measures how long it takes to restore a system after failure, which is more aligned with service restoration time rather than data loss. BCP (Business Continuity Plan) is the overall plan/process for keeping critical business functions running during disruptions; it is not a single data recovery metric. Therefore, RPO is the correct term for a data recovery goal.
