Practice Free N10-009 Exam Online Questions
A support agent receives a report that a remote user’s wired devices are constantly disconnecting and have slow speeds. Upon inspection, the support agent sees that the user’s coaxial modern has a signal power of -97dB.
- A . Removing any spliters connecte to the line
- B . Switching the devices to wireless
- C . Moving the devices closer to the modern
- D . Lowering the network speed
A
Explanation:
A signal power of -97dB indicates a very weak signal, which can cause connectivity issues and slow speeds. Splitters on a coaxial line can degrade the signal quality further, so removing them can help improve the signal strength and overall connection quality.
Signal Quality: Splitters can reduce the signal strength by dividing the signal among multiple lines, which can be detrimental when the signal is already weak.
Direct Connection: Ensuring a direct connection from the modem to the incoming line can maximize signal quality and reduce potential points of failure.
Network
Reference: CompTIA Network+ N10-007 Official Certification Guide: Discusses troubleshooting connectivity issues and the impact of signal strength on network performance.
Cisco Networking Academy: Provides insights on maintaining optimal signal quality in network setups.
Network+ Certification All-in-One Exam Guide: Covers common network issues, including those related to signal degradation and ways to mitigate them.
Users usually use RDP to connect to a terminal server with hostname TS19 that points to 10.0.100.19. However, users recently have been unable to connect to TS19. The technician pings 10.0.100.19 and gets an unreachable error.
Which of the following is the most likely cause?
- A . The users are on the wrong subnet.
- B . The DHCP server renewed the lease.
- C . The IP address was not reserved.
- D . The hostname was changed.
A
Explanation:
If a ping to 10.0.100.19 is unreachable, the most likely issue is that users are on the wrong subnet and cannot communicate with the server.
Breakdown of Options:
After running a Cat 8 cable using passthrough plugs, an electrician notices that connected cables are experiencing a lot of cross talk.
Which of the following troubleshooting steps should the electrician take first?
- A . Inspect the connectors for any wires that are touching or exposed.
- B . Restore default settings on the connected devices.
- C . Terminate the connections again.
- D . Check for radio frequency interference in the area.
A
Explanation:
Cross talk can often be caused by improper termination of cables. The first step in troubleshooting should be to inspect the connectors for any wires that might be touching or exposed. Ensuring that all wires are correctly seated and that no conductors are exposed can help reduce or eliminate cross talk. This step should be taken before attempting to re-terminate the connections or check for other sources of interference.
Reference: CompTIA Network+ study materials.
During a security audit, a consulting firm notices inconsistencies between the documentation and the actual environment.
Which of the following can keep a record of who made the changes and what the changes are?
- A . Network access control
- B . Configuration monitoring
- C . Zero Trust
- D . Syslog
B
Explanation:
Configuration monitoring and management tools (often part of network management systems) maintain version-controlled records of device configurations, track changes, and log who made them. This provides accountability and supports compliance audits.
Which of the following does a hash provide?
- A . Non-repudiation
- B . Integrity
- C . Confidentiality
- D . Availability
B
Explanation:
The correct answer is Integrity because a hashing algorithm ensures that data has not been altered. According to CompTIA Network+ (N10-009) security objectives, hashing is a cryptographic process that takes input data of any size and produces a fixed-length output known as a hash value or digest. If even a single bit of the original data changes, the resulting hash value will be significantly different.
Hashing is commonly used to verify file integrity, validate message authenticity, and securely store passwords. For example, when downloading software, the vendor may publish a hash value so users can calculate the hash of the downloaded file and confirm it matches, ensuring the file was not tampered with.
Non-repudiation (Option A) typically requires digital signatures that combine hashing with asymmetric encryption to verify the sender’s identity. Confidentiality (Option C) is achieved through encryption, which protects data from unauthorized access. Availability (Option D) refers to ensuring systems and data are accessible when needed and is not related to hashing functions.
Therefore, hashing primarily provides data integrity verification.
Which of the following cloud deployment models is most commonly associated with multitenancy and is generally offered by a service provider?
- A . Private
- B . Community
- C . Public
- D . Hybrid
C
Explanation:
The correct answer is public cloud. In public cloud models, a provider (such as AWS, Azure, or Google Cloud) hosts infrastructure and services that are shared across multiple customers, known as multitenancy. Each tenant is logically isolated, but physical infrastructure is shared, allowing providers to achieve economies of scale.
Which of the following types of attacks is most likely to occur after an attacker sets up an evil twin?
- A . On-path
- B . DDoS
- C . ARP spoofing
- D . Phishing
A
Explanation:
Comprehensive and Detailed Explanation (paraphrased, aligned to N10-009):
An evil twin is a malicious wireless access point that impersonates a legitimate SSID. Once victims connect, the attacker can intercept and manipulate traffic, performing an on-path (man-in-the-middle) attack―capturing credentials, injecting content, or downgrading encryption.
B. DDoS overwhelms services with traffic; it’s not the typical follow-on from clients joining a rogue AP.
C. ARP spoofing is another way to become on-path on wired segments, but with an evil twin, the wireless association itself enables the on-path position.
D. Phishing is social engineering; while an evil twin could be used to present fake portals, the primary technical posture after connection is on-path.
Reference (CompTIA Network+ N10-009):
Domain: Network Security ― Wireless threats (rogue APs/evil twins), traffic interception, on-path attacks.
Before using a guest network, an administrator requires users to accept the terms of use.
Which of the following is the best way to accomplish this goal?
- A . Pre-shared key
- B . Autonomous access point
- C . Captive portal
- D . WPA2 encryption
C
Explanation:
A captive portal is a web page that users must view and interact with before being granted access to a network. It is commonly used in guest networks to enforce terms of use agreements. When a user connects to the network, they are redirected to this portal where they must accept the terms of use before proceeding. This method ensures that users are aware of and agree to the network’s policies, making it the best choice for this scenario.
Reference: CompTIA Network+ Exam Objectives and official study guides.
Network administrators are using the Telnet protocol to administer network devices that are on the 192.168.1.0/24 subnet.
Which of the following tools should the administrator use to best identify the devices?
- A . dig
- B . nmap
- C . tracert
- D . telnet
B
Explanation:
nmap (Network Mapper) is the best tool in this scenario. It can scan the 192.168.1.0/24 subnet to discover live hosts, open ports (like Telnet on port 23), and device types. It’s ideal for mapping and auditing the network.
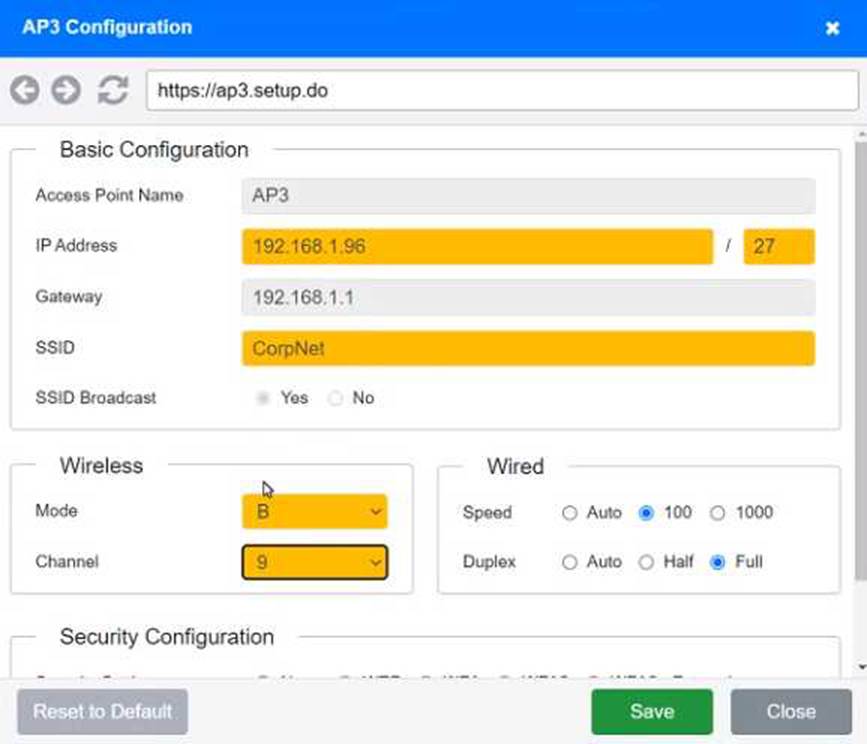
SIMULATION
You have been tasked with setting up a wireless network in an office. The network will consist of 3
Access Points and a single switch. The network must meet the following parameters:
The SSIDs need to be configured as CorpNet with a key of S3cr3t!
The wireless signals should not interfere with each other
The subnet the Access Points and switch are on should only support 30 devices maximum
The Access Points should be configured to only support TKIP clients at a maximum speed
INSTRUCTONS
Click on the wireless devices and review their information and adjust the settings of the access points to meet the given requirements.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
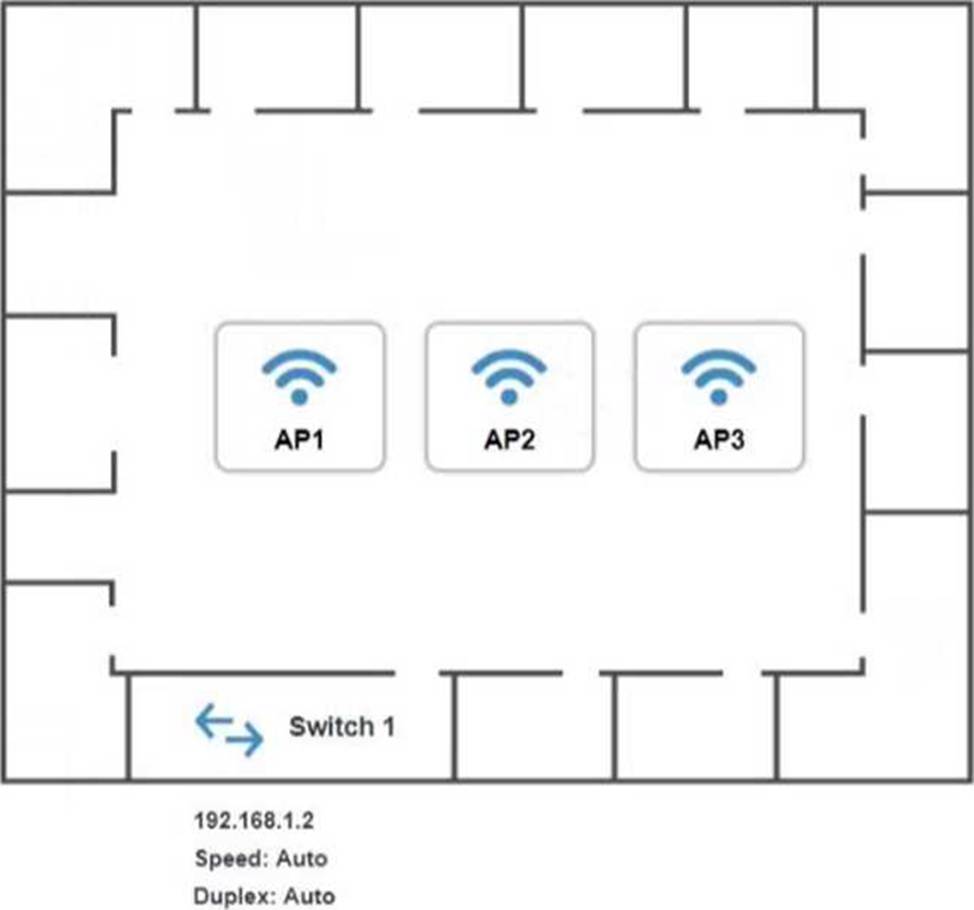
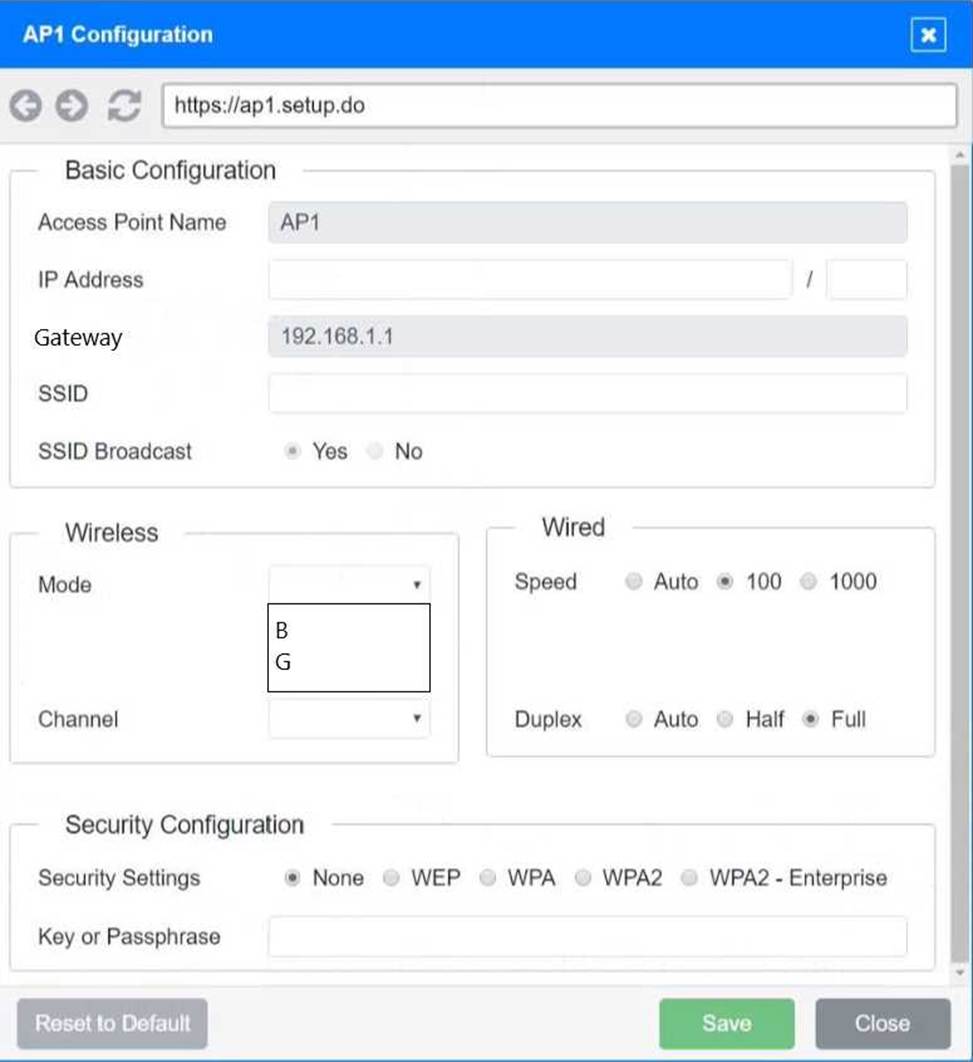
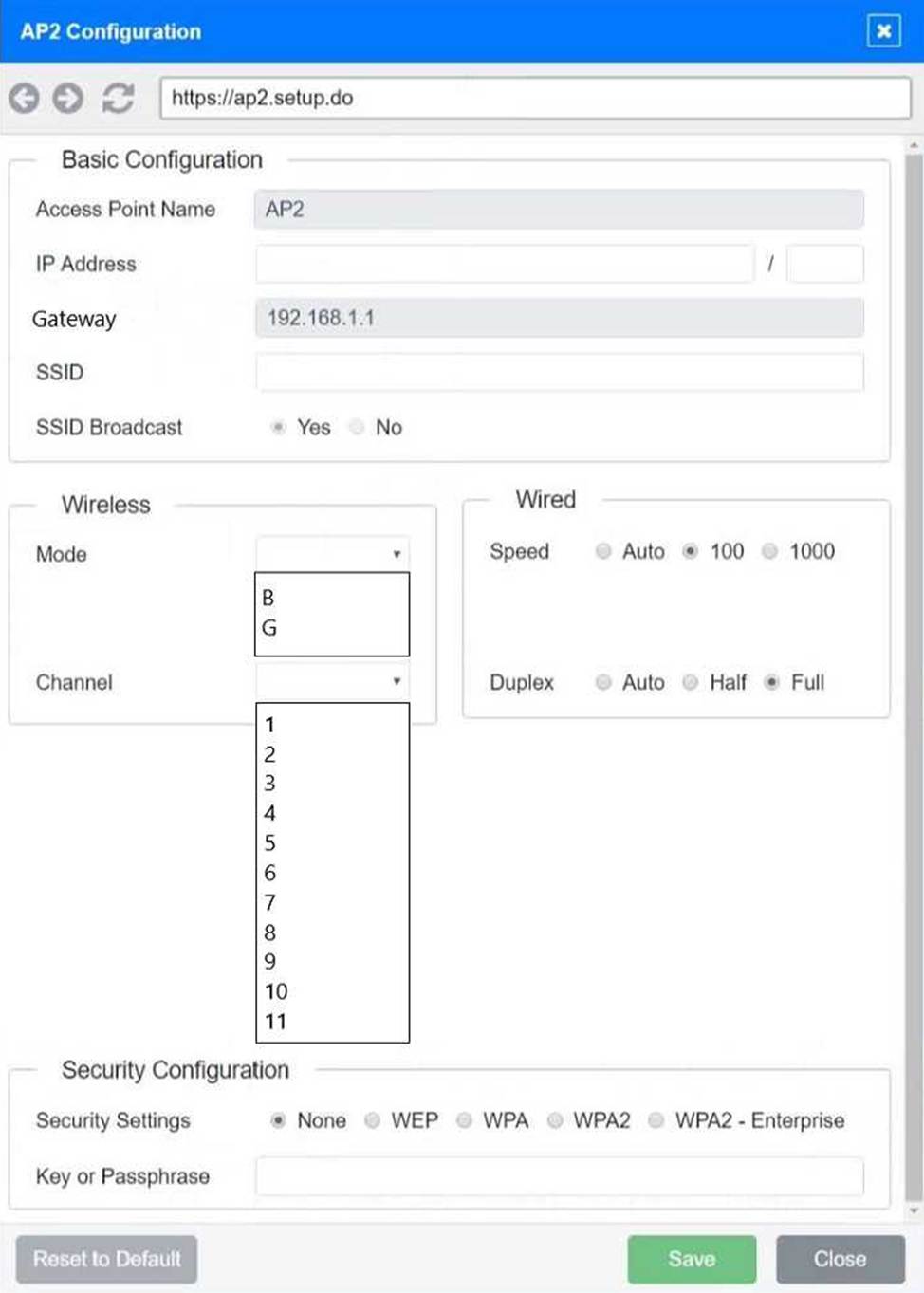
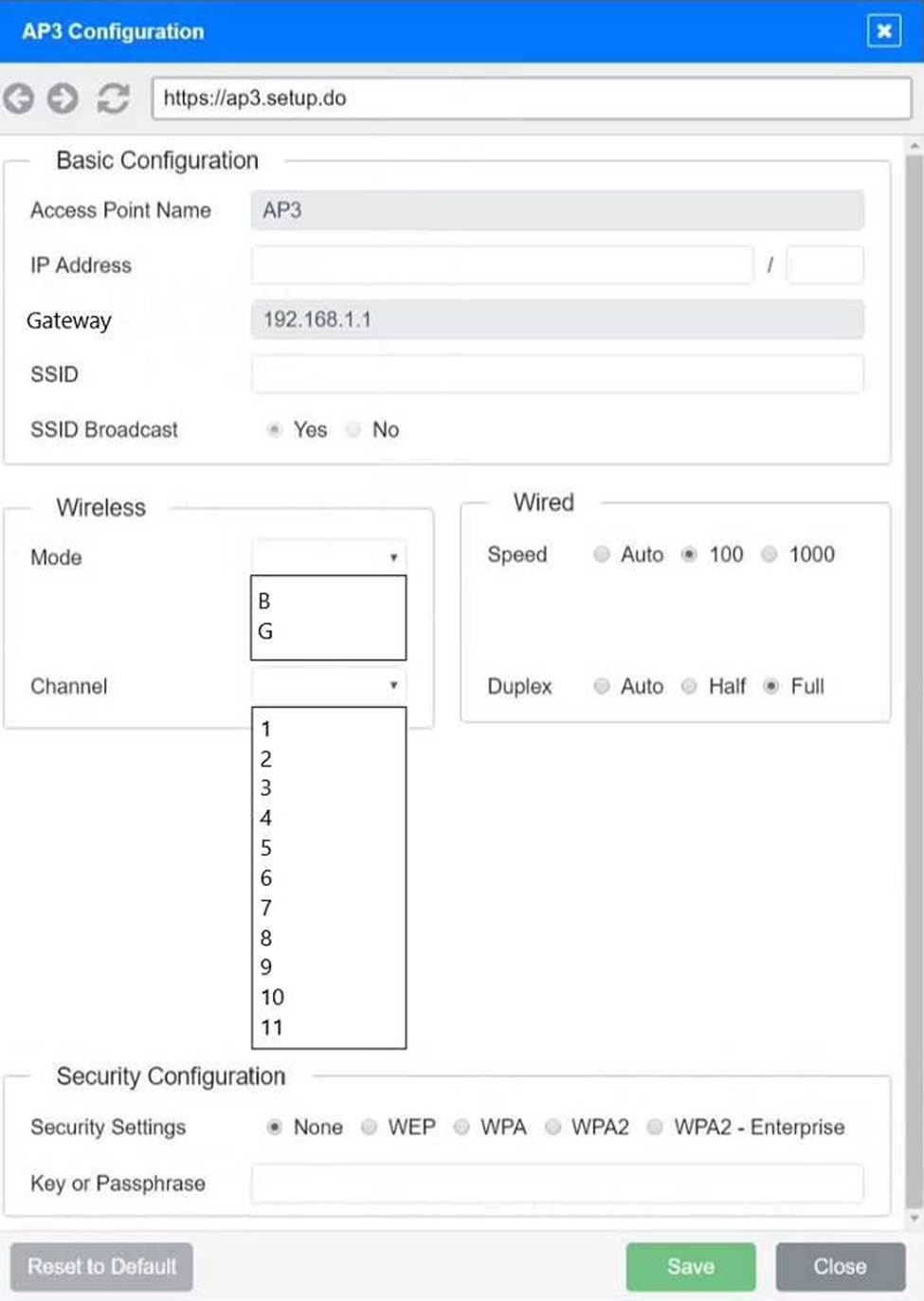
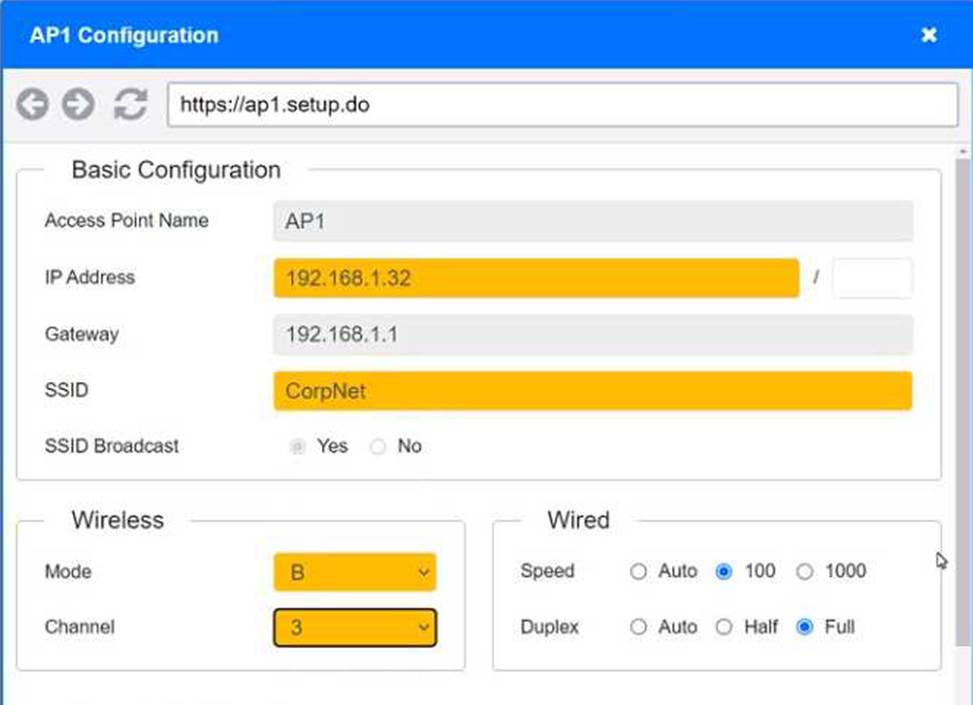
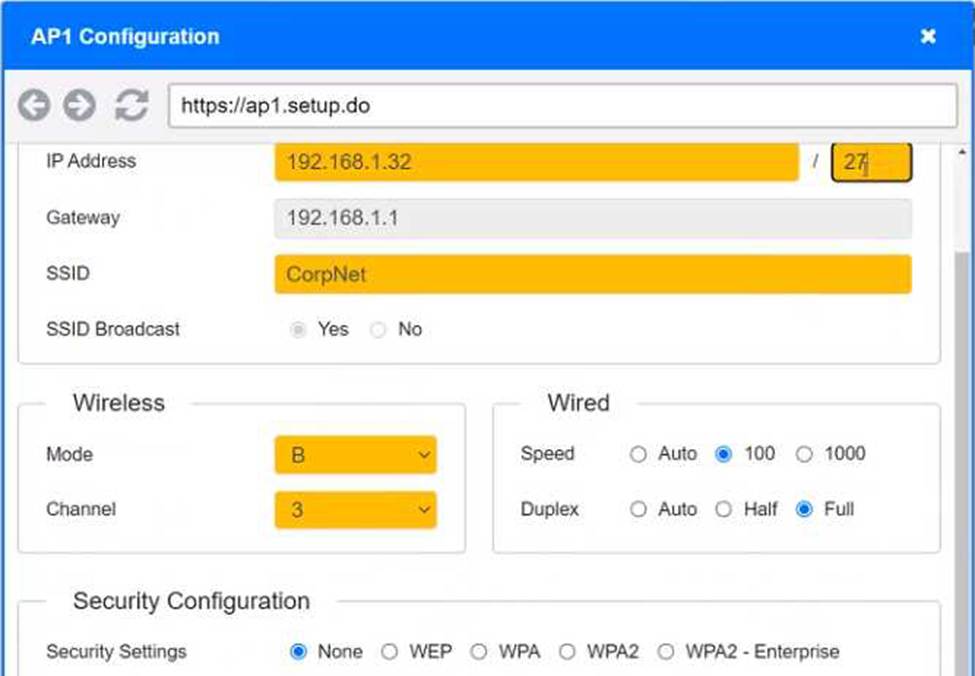
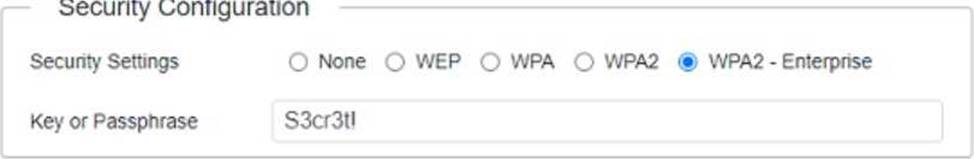
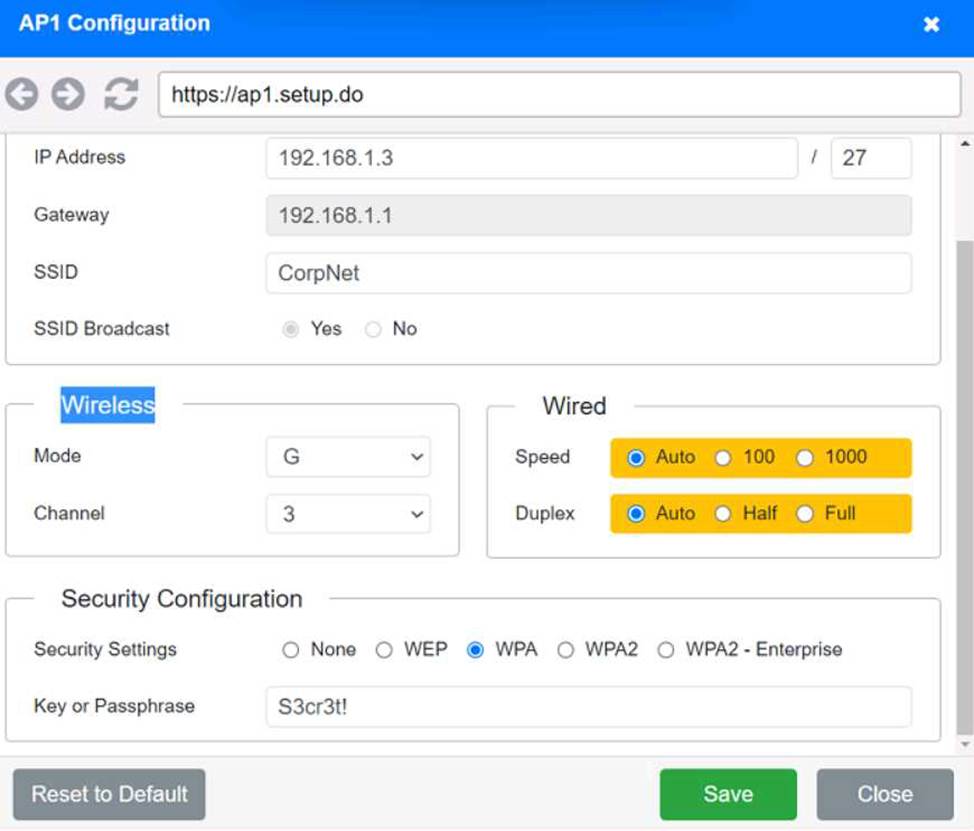
Exhibit 2 as follows
Access Point Name AP2
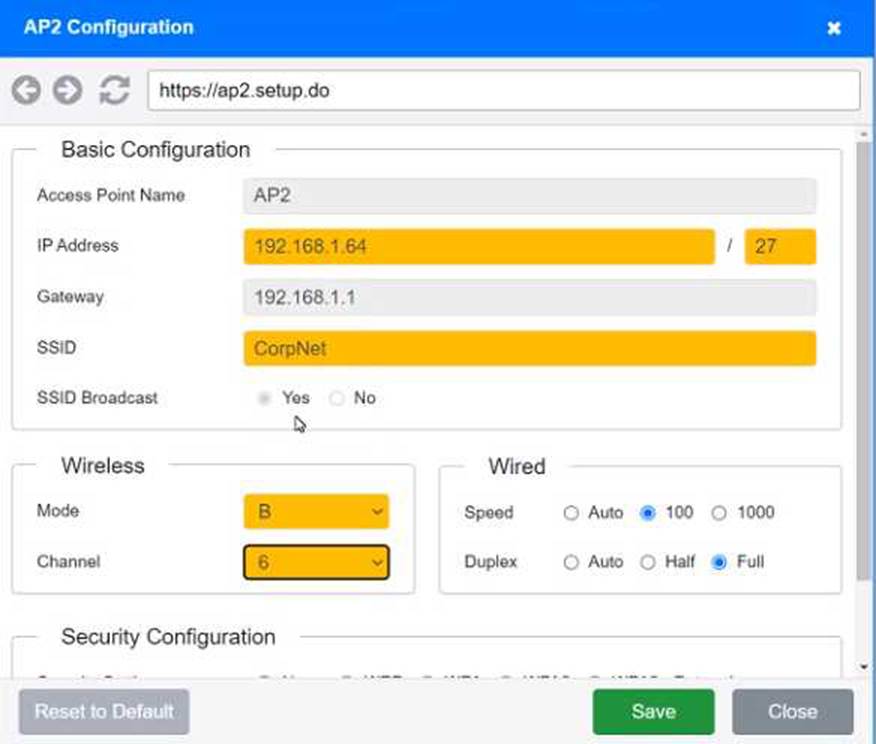

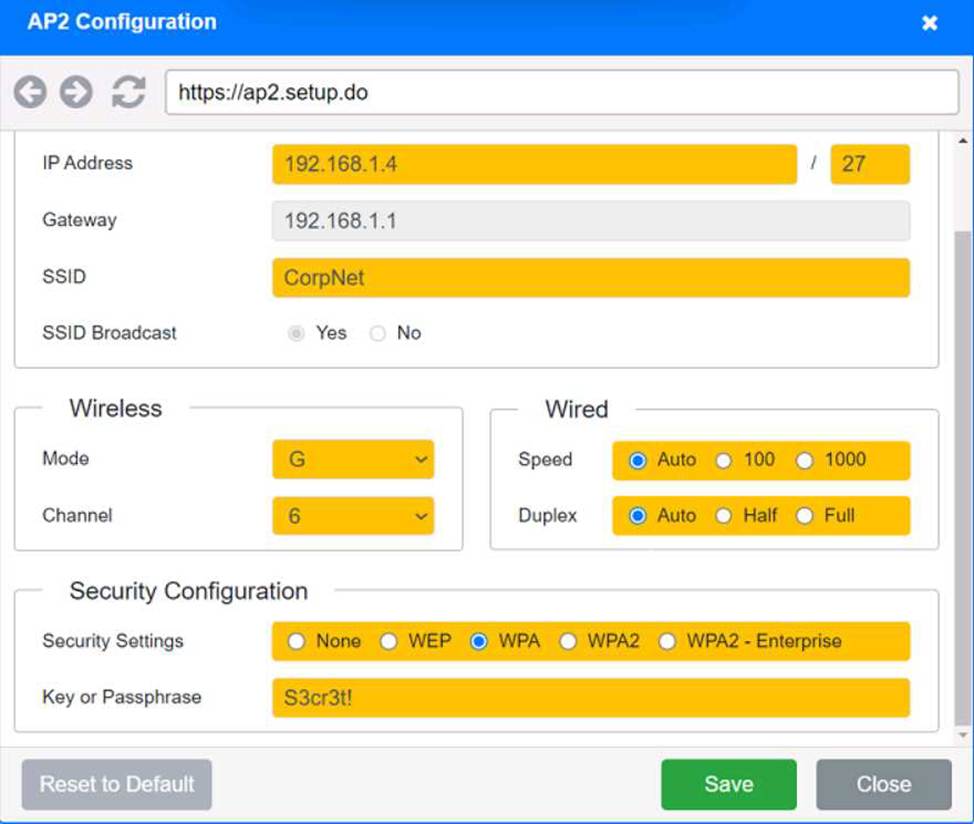
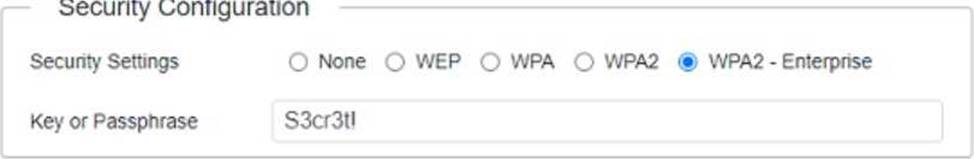
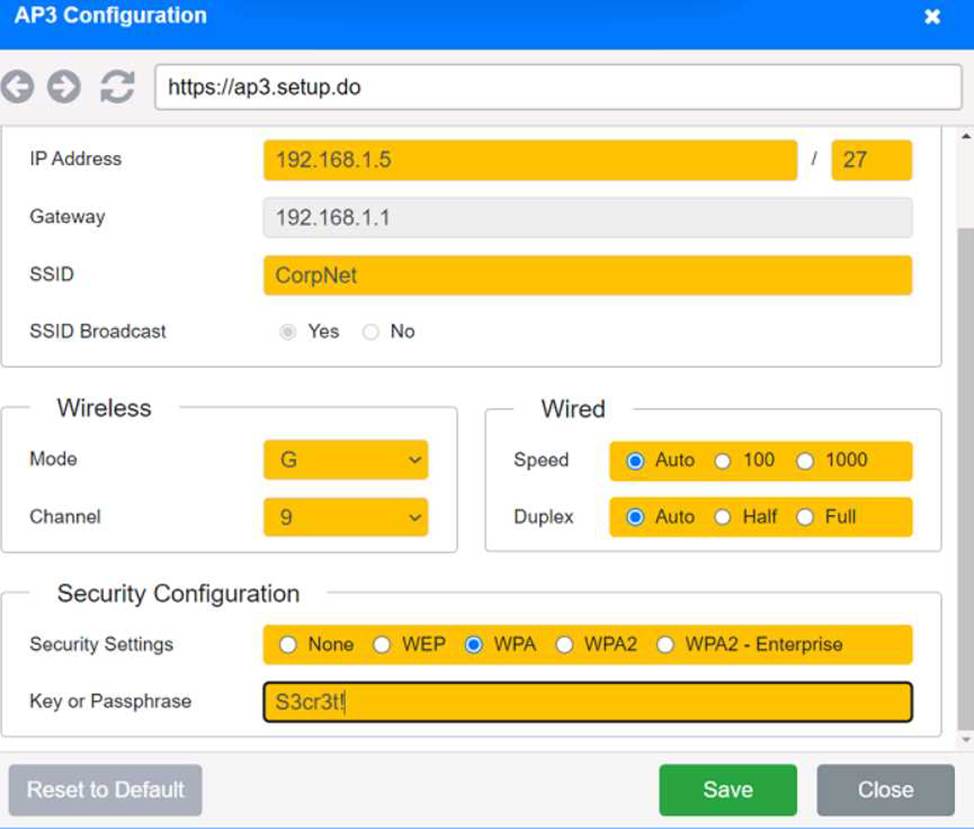
Exhibit 3 as follows
Access Point Name AP3
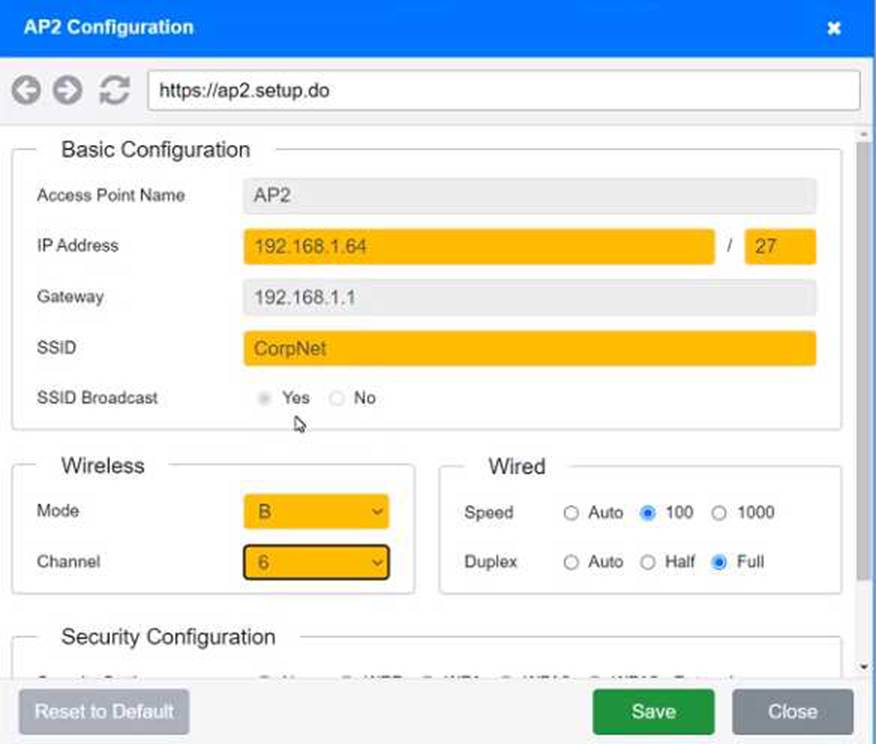
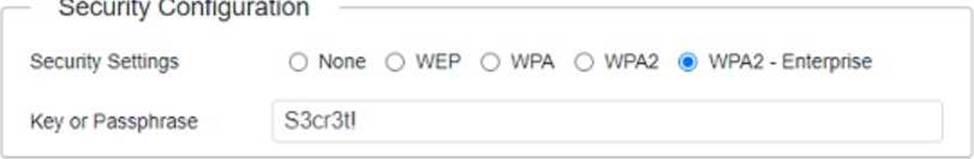
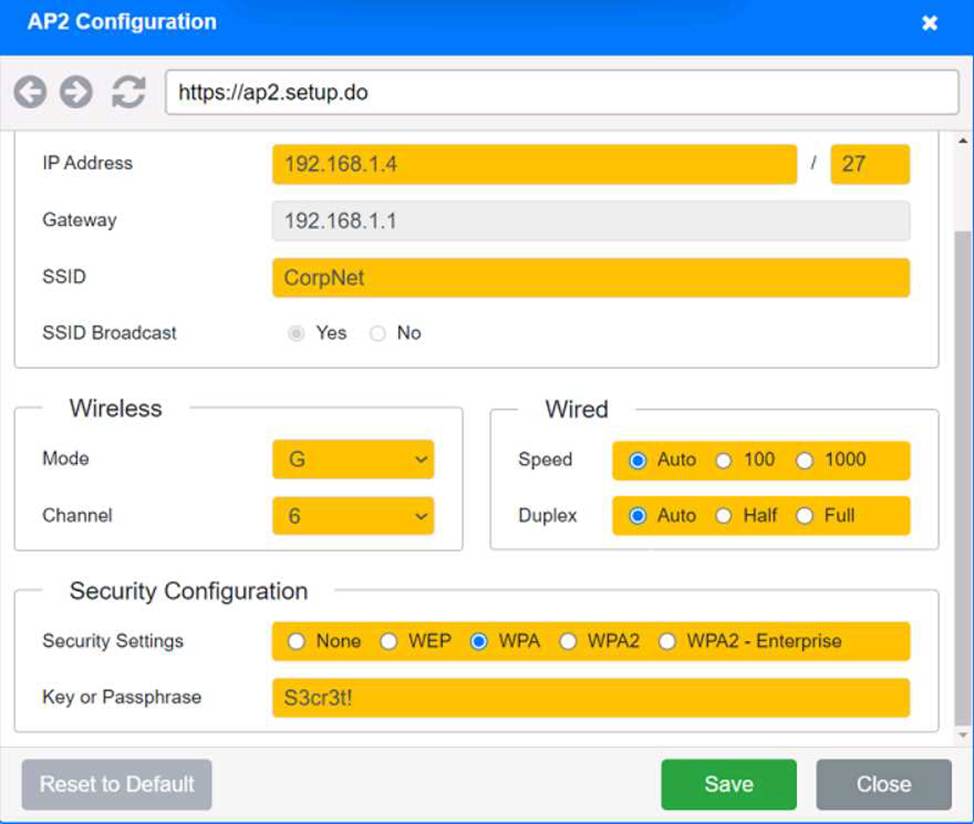
Exhibit 3 as follows
Access Point Name AP3