Practice Free N10-009 Exam Online Questions
A network engineer connects a business to a new ISP. A simple ping test to 8.8.8.8 is successful. However, users complain of extreme slowness to any website and periods of no connectivity.
Which of the following is the most likely cause?
- A . Incorrect default gateway
- B . VLAN mismatch
- C . Subnet mask configuration
- D . Duplicate ISP IP address
D
Explanation:
If the business shares or duplicates the ISP-assigned public IP address, routing instability and conflicts will occur. Pinging a public IP like 8.8.8.8 may work (since ICMP can bypass certain conflicts), but browsing websites (which requires stable sessions and return traffic) will fail intermittently.
Which of the following is the best example of a networking appliance that connects different network segments and directs allowed traffic between specific segments?
- A . Firewall
- B . IDS
- C . Unmanaged switch
- D . (Not provided)
A
Explanation:
A firewall is the best example of an appliance that can sit between network segments and permit or deny traffic flows based on security policy. In Network+ terms, firewalls enforce segmentation controls by applying rules that match on items such as source/destination IP, ports, protocols, and (with next-generation firewalls) even applications. This makes a firewall a common choice for directing allowed traffic between specific segments (for example, allowing users in a workstation VLAN to reach only certain ports on a server VLAN, while blocking everything else). This function is core to network security architecture and is frequently paired with concepts like network segmentation, ACL-style rule sets, and creating security zones.
An IDS (intrusion detection system) primarily monitors traffic and generates alerts on suspicious activity; it does not typically control or “direct allowed traffic” unless it is specifically an IPS (prevention) with inline blocking. An unmanaged switch operates at Layer 2 and forwards frames within a broadcast domain; it does not provide policy-based filtering between security segments. Therefore, the correct answer is Firewall.
Users cannot connect to an internal website with an IP address 10.249.3.76.
A network administrator runs a command and receives the following output:
1 3ms 2ms 3ms 192.168.25.234
2 2ms 3ms 1ms 192.168.3.100
3 4ms 5ms 2ms 10.249.3.1
4 *
5 ’
6 *
7 •
Which of the following command-line tools is the network administrator using?
- A . tracert
- B . netstat
- C . tcpdump
- D . nmap
A
Explanation:
Understanding Tracert:
tracert (Traceroute in Windows) is a command-line tool used to trace the path that packets take from the source to the destination. It records the route (the specific gateways at each hop) and measures transit delays of packets across an IP network.
Output Analysis:
The output shows a series of IP addresses with corresponding round-trip times (RTTs) in milliseconds.
The asterisks (*) indicate that no response was received from those hops, which is typical for routers or firewalls that block ICMP packets used by tracert.
Comparison with Other Tools:
netstat: Displays network connections, routing tables, interface statistics, and more, but does not trace packet routes.
tcpdump: Captures network packets for analysis, used for detailed network traffic inspection.
nmap: A network scanning tool used to discover hosts and services on a network, not for tracing packet routes.
Usage:
tracert helps identify the path to a destination and locate points of failure or congestion in the network.
Reference: CompTIA Network+ study materials on network troubleshooting and diagnostic tools.
A network administrator is managing network traffic so that classified services and applications are prioritized.
Which of the following technologies should the network administrator use?
- A . Load balancing
- B . Time to live
- C . Quality of service
- D . Content delivery network
C
Explanation:
Quality of Service (QoS) is used to prioritize certain types of traffic to ensure critical applications receive the bandwidth, low latency, and low jitter they need―especially during congestion. Network+ objectives cover QoS concepts such as classification, marking, queuing, and policing/shaping to manage how traffic is handled on interfaces and across links. If the requirement is to prioritize “classified services and applications,” QoS policies can match traffic using ports, protocols, DSCP markings, VLAN tags, or application identifiers and then place that traffic into higher-priority queues or reserve bandwidth for it. Load balancing distributes traffic across multiple servers/paths but does not inherently prioritize one class of traffic over another on congested links. TTL (time to live) is an IP header field used to prevent routing loops and is unrelated to prioritization. A CDN improves content delivery and caching for distributed users, but it is not a traffic-prioritization mechanism within an organization’s network. Therefore, QoS is the correct technology for prioritizing specific services and applications.
Which of the following is a major difference between an IPS and IDS?
- A . An IPS needs to be installed in line with traffic and an IDS does not.
- B . An IPS is signature-based and an IDS is not.
- C . An IPS is less susceptible to false positives than an IDS.
- D . An IPS requires less administrative overhead than an IDS.
A
Explanation:
The key difference is that an Intrusion Prevention System (IPS) is installed in line with network traffic, allowing it to actively block threats. In contrast, an Intrusion Detection System (IDS) only monitors and alerts without actively blocking traffic.
Breakdown of Options:
A network engineer needs to deploy an access point at a remote office so that it will not communicate back to the wireless LAN controller.
Which of the following deployment methods must the engineer use to accomplish this task?
- A . Lightweight
- B . Autonomous
- C . Mesh
- D . Ad hoc
B
Explanation:
Autonomous access points operate independently without needing to communicate with a central wireless LAN controller. This is ideal for remote deployments.
From Andrew Ramdayal’s guide:
“Autonomous access points are stand-alone devices that manage their own configurations and operations. They do not require a WLC and are ideal for small or remote office deployments.”
A company is opening a new site that needs to be divided into subnets that accommodate 75 hosts each.
Which of the following is the most efficient subnet?
- A . 192.168.13.0/25
- B . 192.168.13.0/26
- C . 192.168.13.0/27
- D . 192.168.13.0/28
A
Explanation:
To support 75 hosts per subnet, you must choose a subnet size that provides at least 75 usable IP addresses. In IPv4, usable hosts per subnet equals 2^(host bits) − 2 (subtracting network and broadcast). A /25 leaves 7 host bits (32C25 = 7), giving 2^7 − 2 = 128 − 2 = 126 usable hosts, which meets the requirement and is the smallest (most efficient) option listed that does so. A /26 leaves 6 host bits, giving 62 usable hosts, which is insufficient. A /27 gives 30 usable, and a /28 gives 14 usable, both far below 75. Network+ subnetting objectives emphasize selecting the smallest subnet that satisfies the host requirement to conserve address space while meeting growth and design constraints. Therefore, 192.168.13.0/25 is the most efficient option that accommodates at least 75 hosts per subnet.
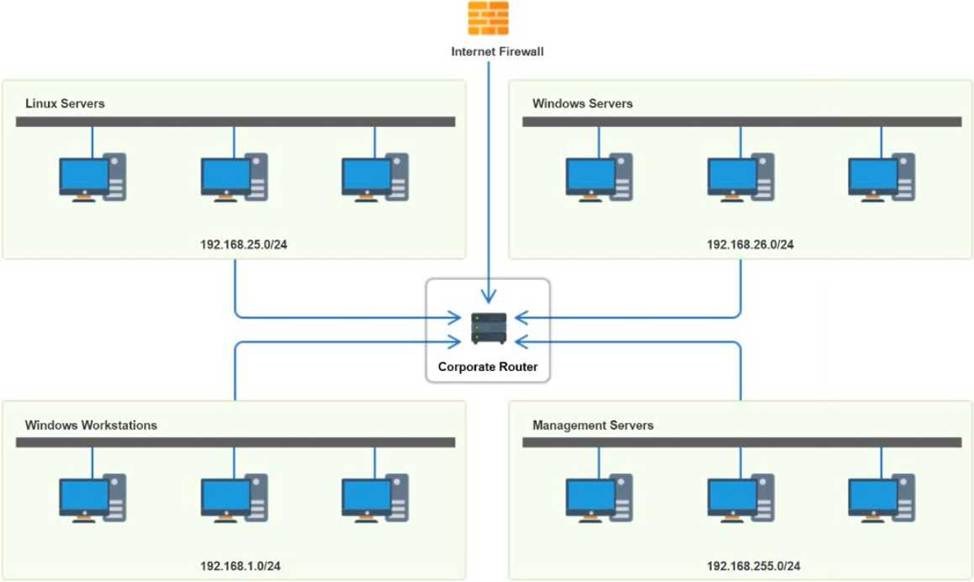
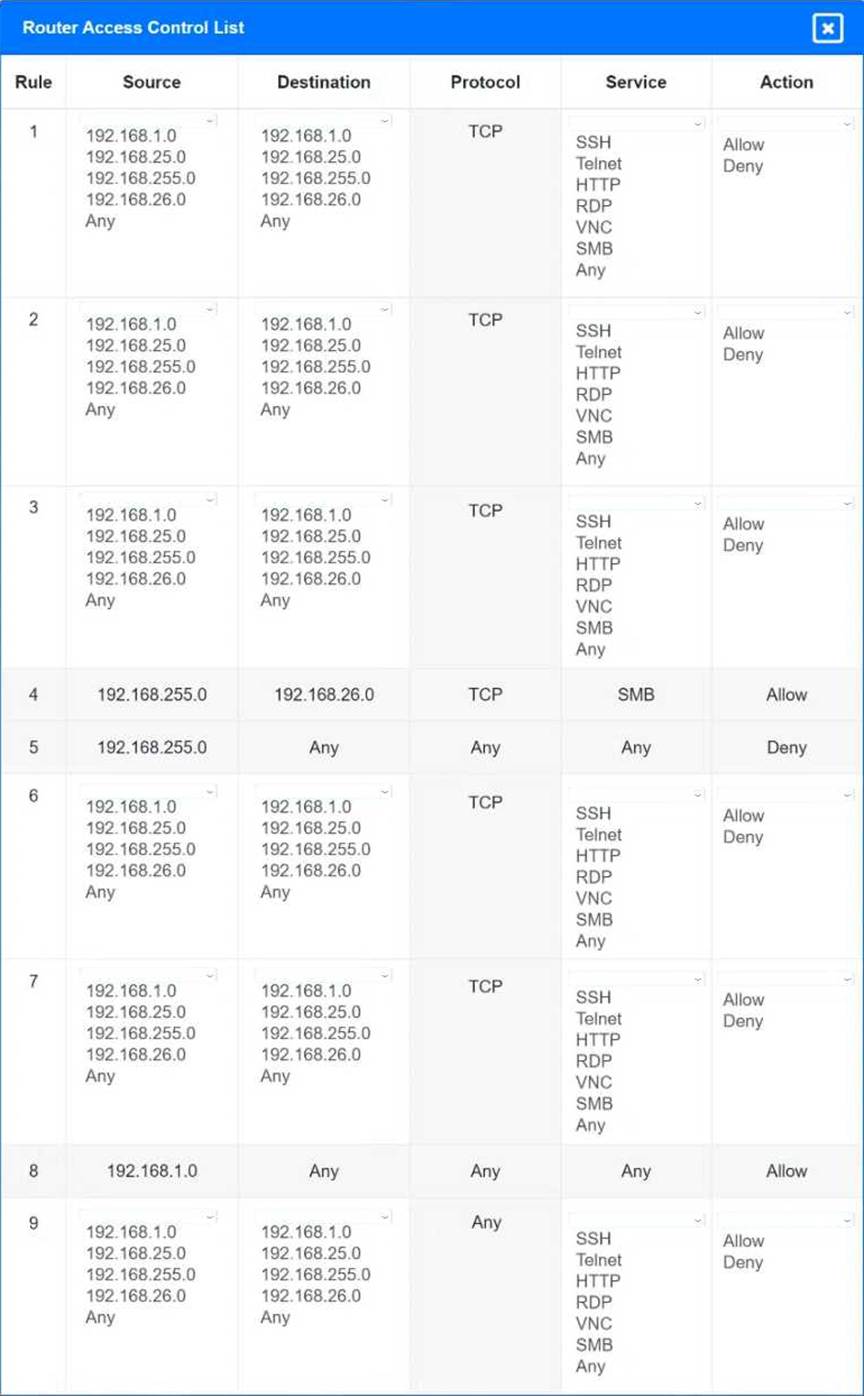
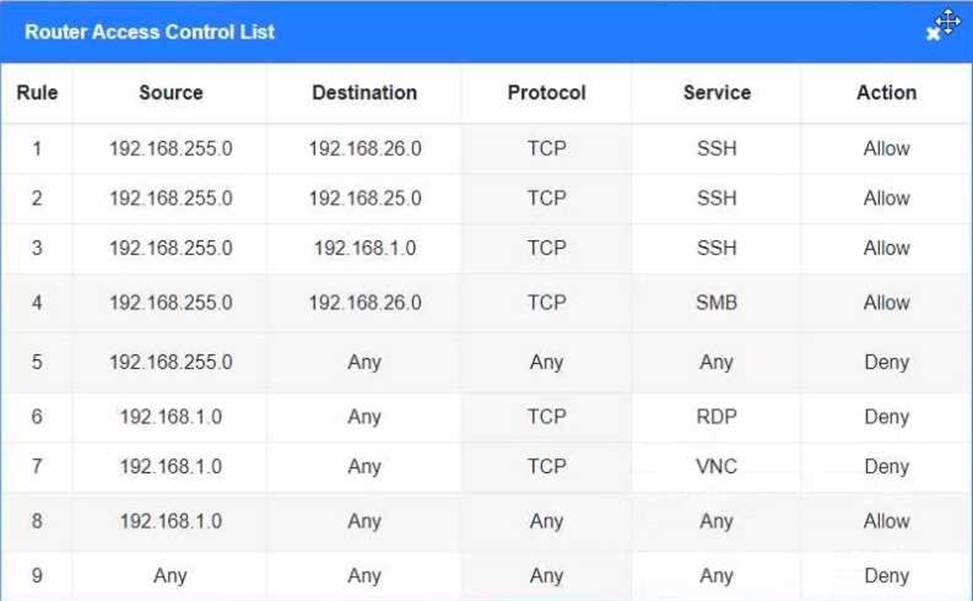
Prohibit any traffic that has not been specifically allowed.
INSTRUCTIONS
Use the drop-downs to complete the ACL
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
Which of the following routing protocols is most commonly used to interconnect WANs?
- A . IGP
- B . EIGRP
- C . BGP
- D . OSPF
C
Explanation:
Border Gateway Protocol (BGP): BGP is the most commonly used routing protocol for interconnecting WANs, especially across the internet. It is used for exchanging routing information between autonomous systems (AS), making it the backbone protocol for large-scale WANs.
IGP (A): Interior Gateway Protocols like OSPF and EIGRP are typically used within a single AS, not between them.
EIGRP (B): While it is efficient, EIGRP is primarily used for intra-domain routing and not ideal for WAN interconnection.
OSPF (D): While OSPF can be used for WANs, it is not as common as BGP for inter-AS communication.
Reference: CompTIA Network+ Official Study Guide, Domain 1.3 (WAN Concepts), Domain 2.5 (Routing Protocols).
Which of the following internal routing protocols is best characterized as having fast convergence and being loop-free?
- A . BGP
- B . STP
- C . OSPF
- D . RIP
C
Explanation:
The correct answer is OSPF (Open Shortest Path First). OSPF is a link-state routing protocol known for its fast convergence and use of the Dijkstra algorithm to calculate the shortest loop-free path. It efficiently scales to large enterprise networks and avoids routing loops by maintaining a complete topology map.
