Practice Free NSE6_SDW_AD-7.6 Exam Online Questions
Refer to the exhibits.
Exhibit A
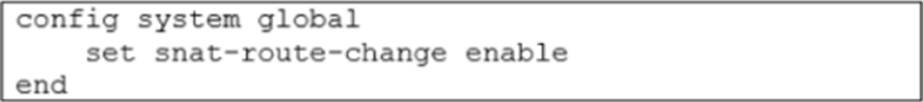
Exhibit B
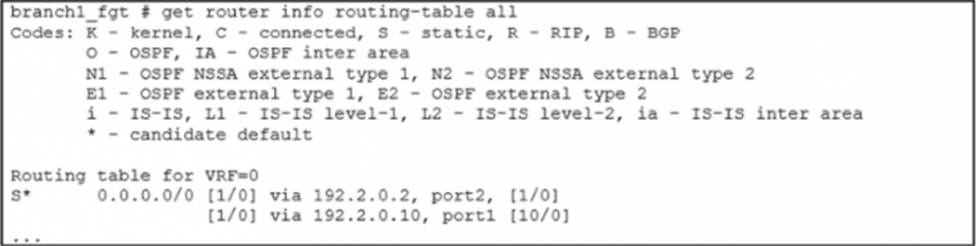
Exhibit A shows the source NAT (SNAT) global setting and exhibit B shows the routing table on FortiGate.
Based on the exhibits, which two actions does FortiGate perform on existing sessions established over port2, if the administrator increases the static route priority on port2 to 20? (Choose two.)
- A . FortiGate flags the sessions as dirty.
- B . FortiGate continues routing the sessions with no SNAT, over port2.
- C . FortiGate performs a route lookup for the original traffic only.
- D . FortiGate updates the gateway information of the sessions with SNAT so that they use port1 instead of port2.
Which type of SD-WAN deployment is typically used for small to medium-sized businesses?
- A . Hybrid SD-WAN
- B . Internet-only SD-WAN
- C . Cloud-delivered SD-WAN
- D . On-premises SD-WAN
What is the purpose of configuring SD-WAN Members and Performance SLAs?
- A . To configure routing protocols
- B . To configure security policies
- C . To configure application performance monitoring
- D . To configure VPN connectivity
Refer to the exhibit.
Based on the exhibit, which two actions does FortiGate perform on traffic passing through port2? (Choose two.)
- A . FortiGate does not change the routing information on existing sessions that use a valid gateway, after a route change.
- B . FortiGate performs routing lookups for new sessions only, after a route change.
- C . FortiGate always blocks all traffic, after a route change.
- D . FortiGate flushes all routing information from the session table, after a route change.
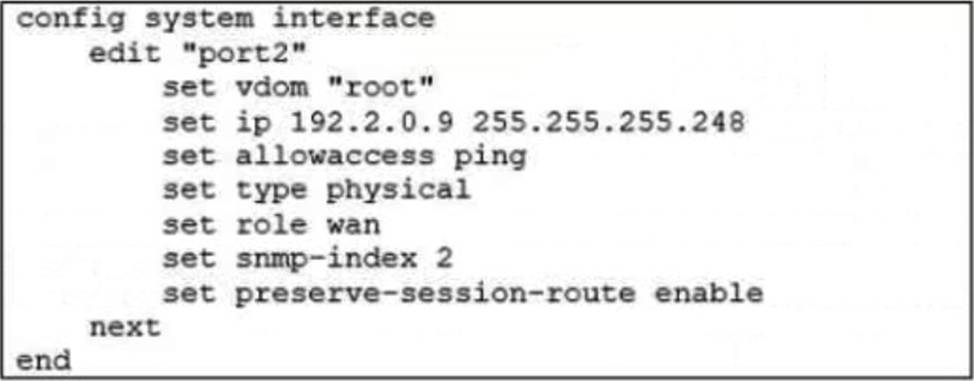
Refer to exhibits.
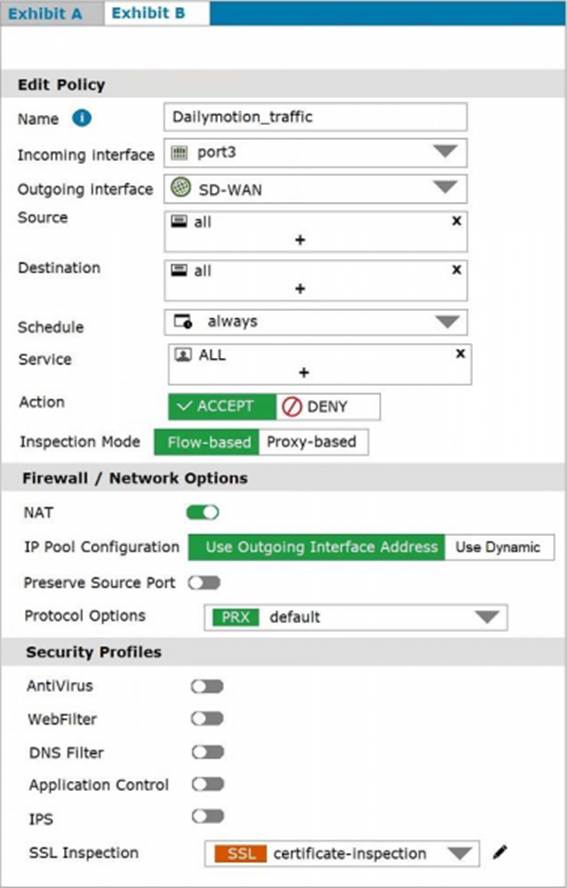
Exhibit A shows the traffic shaping policy and exhibit B shows the firewall policy. FortiGate is not performing traffic shaping as expected, based on the policies shown in the exhibits.
To correct this traffic shaping issue on FortiGate, what configuration change must be made on which policy?
- A . The URL category must be specified on the traffic shaping policy.
- B . The shaper mode must be applied per-IP shaper on the traffic shaping policy.
- C . The web filter profile must be enabled on the firewall policy.
- D . The application control profile must be enabled on the firewall policy.
Which command can be used to troubleshoot SD-WAN routing issues?
- A . traceroute
- B . ping
- C . netstat
- D . route
What is the purpose of deploying ADVPN in a hub-and-spoke IPsec topology for SD-WAN?
- A . To ensure secure communication between sites
- B . To improve application performance
- C . To simplify configuration and management
- D . To provide high-speed internet connectivity
You want to configure ADVPN without route reflection on your SD-WAN topology.
Which two statements apply to this scenario? (Choose two.)
- A . ADVPN without route reflection is compatible with BGP on loopback.
- B . ADVPN without route reflection is also called ADVPN 2.0.
- C . ADVPN without route reflection allows hub-side steering by route tag.
- D . ADVPN without route reflection is compatible with static routing on the overlay.
You are configuring SD-WAN to load balance network traffic and you want to take into account the link quality.
Which two facts should you consider? Choose two answers.
- A . When applicable, FortiGate load balances the traffic through all members that meet the SLA target.
- B . You can select the best quality strategy and allow SD-WAN load balancing.
- C . You can select the lowest cost service level agreement (SLA) strategy and allow SD-WAN load balancing.
- D . The best quality strategy supports only the round-robin hash mode.
Which command can be used to verify the connectivity between SD-WAN members?
- A . traceroute
- B . ping
- C . netstat
- D . route
