Practice Free NSE6_SDW_AD-7.6 Exam Online Questions
Refer to the exhibit.
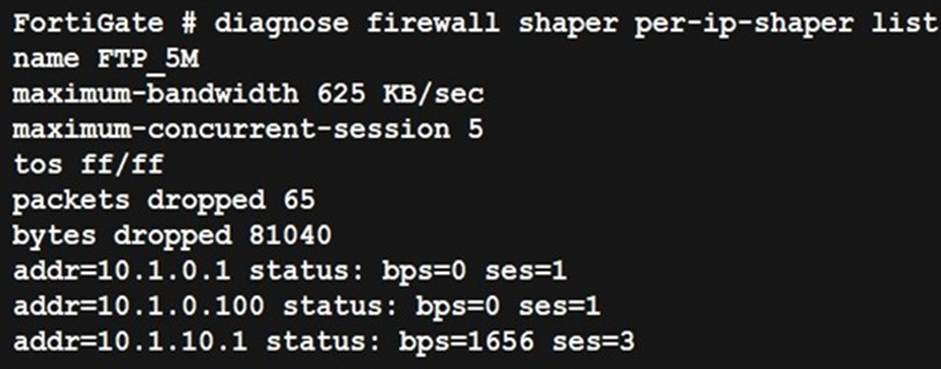
Which two statements about the debug output are correct? (Choose two.)
- A . The debug output shows per-IP shaper values and real-time readings.
- B . This traffic shaper drops traffic that exceeds the set limits.
- C . Traffic being controlled by the traffic shaper is under 1 Kbps.
- D . FortiGate provides statistics and reading based on historical traffic logs.
Which three protocols are available only on the command line to configure as performance SLA status check? (Choose three.)
- A . twamp
- B . smtp
- C . icmp
- D . tcp-echo
- E . udp-echo
Which three protocols are available only on the command line to configure as performance SLA status check? (Choose three.)
- A . twamp
- B . smtp
- C . icmp
- D . tcp-echo
- E . udp-echo
Which log can be used to troubleshoot SD-WAN performance issues?
- A . System log
- B . Application log
- C . Security log
- D . Traffic log
What is the purpose of configuring a basic SD-WAN DIA setup?
- A . To configure virtual networks
- B . To configure quality of service (QoS)
- C . To configure security policies
- D . To configure WAN optimization
Which three characteristics apply to provisioning templates available on FortiManager? (Choose three.)
- A . A template group can include a system template and an SD-WAN template.
- B . Each template group can contain up to three IPsec tunnel templates.
- C . CLI templates are applied in order, from top to bottom
- D . A CLI template group can contain CLI templates of both types.
- E . A CLI template can be of type CLI script or Perl script.
Refer to the exhibits.
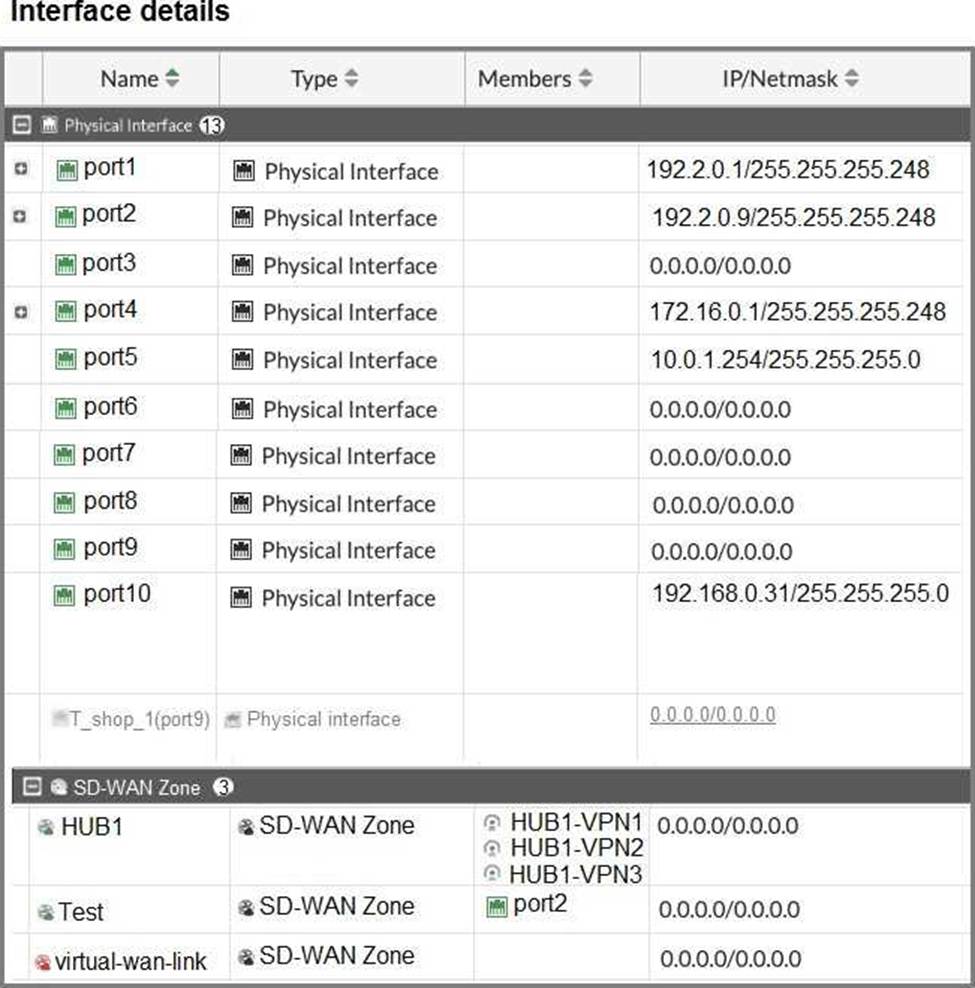
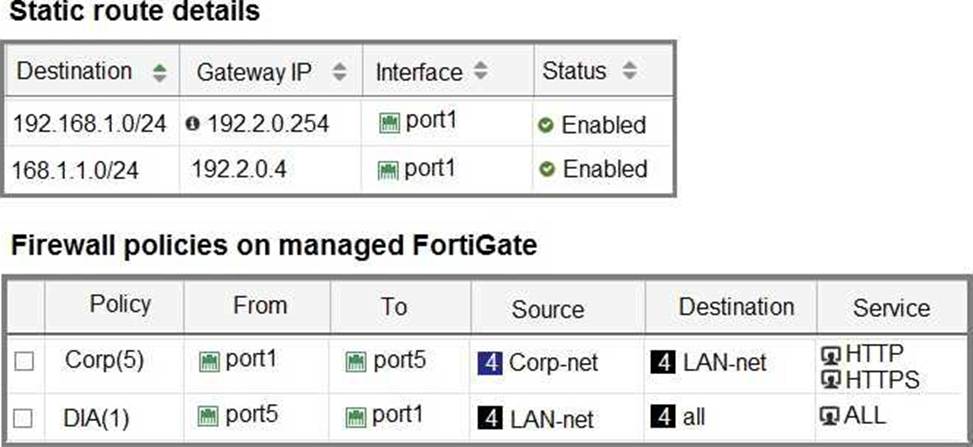
The interface details, static route configuration, and firewall policies on the managed FortiGate device are shown.
You want to configure a new SD-WAN zone, named Underlay, that contains the interfaces port1 and port2.
What must be your first action?
- A . Define port1 as an SD-WAN member.
- B . Delete the static routes.
- C . Delete the SD-WAN Zone Test.
- D . Delete the firewall policies.
Which two reasons make forward error correction (FEC) ideal to enable in a phase one VPN interface? (Choose two.)
- A . FEC is useful to increase speed at which traffic is routed through IPsec tunnels.
- B . FEC transmits the original payload in full to recover the error in transmission.
- C . FEC transmits additional packets as redundant data to the remote device.
- D . FEC improves reliability, which overcomes adverse WAN conditions such as noisy links.
- E . FEC reduces the stress on the remote device jitter buffer to reconstruct packet loss.
What is the purpose of configuring SD-WAN path control?
- A . To configure routing protocols
- B . To configure security policies
- C . To configure application performance monitoring
- D . To ensure traffic takes the most optimal path
FortiGate is connected to the internet and is obtaining the IP address on its egress interlace from the DHCP server.
Which statement is due when FortiGate restarts and receives preconfigured settings to install as part of a zero-touch provisioning process?
- A . The zero-touch provisioning process completes internally, behind FortiGate
- B . FortiManager registers FortiGate after the restart and retrieves the existing configuration
- C . The FortiGate cloud key added to the FortiGate cloud portal and FortiGate performs a factory reset before the restart
- D . FortiDeploy connects with FortiGate and provides the initial configuration to contact FortiManager
