Practice Free NSE6_SDW_AD-7.6 Exam Online Questions
The administrator uses the FortiManager SD-WAN overlay template to prepare an SD-WAN deployment. Using information provided through the SD-WAN overlay template wizard, FortiManager creates templates ready to install on the spoke and hub devices.
What are the three templates created by the SD-WAN overlay template for a spoke device? (Choose three.)
- A . Static route template
- B . Rules template
- C . CLI template
- D . BGP template
- E . IPsec tunnel template
Which feature of SD-WAN allows for automatic failover in case of a network outage?
- A . Load balancing
- B . Quality of service (QoS)
- C . Application steering
- D . Link steering
Exhibit.
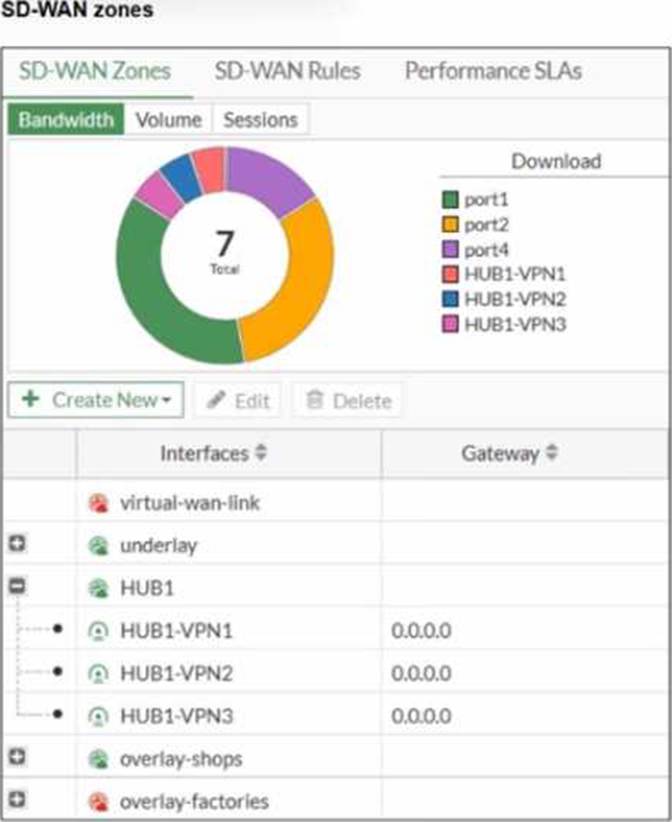
Refer to the exhibit, which shows an SD-WAN zone configuration on the FortiGate GUI.
What can you conclude about the zone and member configuration on this device?
- A . The underlay zone contains three members.
- B . You can delete the virtual-wan-link zones.
- C . The overlay-factories zone contains no member.
- D . You can move HUB1-VPN3 from the HUB1 zone to the overlay-shops zone.
You want FortiGate to use SD-WAN rules to steer local-out traffic.
Which two constraints should you consider? (Choose two.)
- A . By default, FortiGate uses SD-WAN rules only for local-out traffic that corresponds to ping and traceroute.
- B . By default, local-out traffic does not use SD-WAN.
- C . You can steer local-out traffic only with SD-WAN rules that use the manual strategy.
- D . You must configure each local-out feature individually to use SD-WAN.
What are three key routing principles of SD-WAN? (Choose three.)
- A . Directly connected routes have precedence over SD-WAN rules.
- B . Policy routes have precedence over SD-WAN rules.
- C . SD-WAN rules are skipped if the best route to the destination is a static route
- D . SD-WAN rules are skipped if the best route to the destination is not an SD-WAN member.
- E . SD-WAN members are skipped if they do not have a valid route to the destination.
Which three matching traffic criteria are available in SD-WAN rules? (Choose three.)
- A . Type of physical link connection
- B . Internet service database (ISDB) address object
- C . Source and destination IP address
- D . URL categories
- E . Application signatures
Refer to the exhibits.
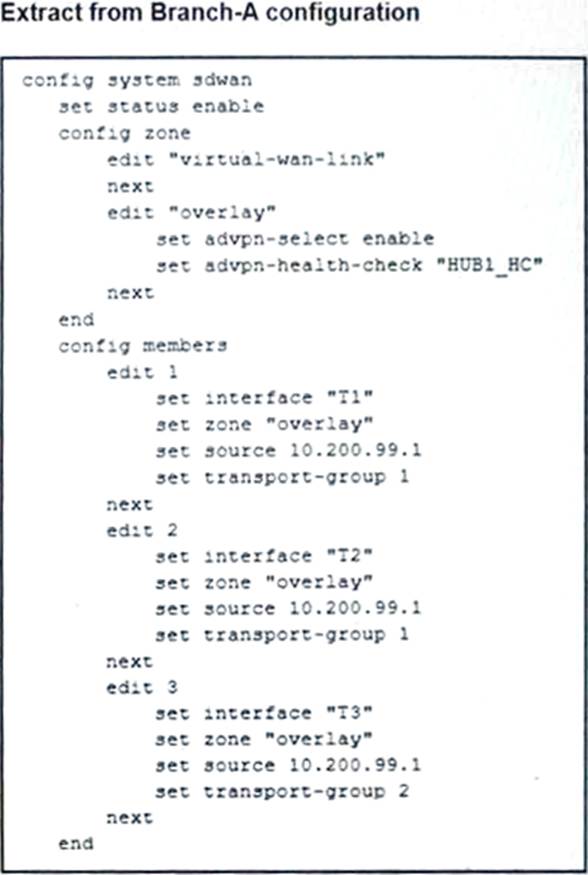
The SD-WAN zones and members configuration of two branch devices are shown. The two branch
devices are part of the same hub-and-spoke topology and connect to the same hub. The devices are configured to allow Auto-Discovery VPN (ADVPN). The configuration on the hub allows the initial communication between the two spokes.
When traffic flows require it, between which interfaces can the devices establish shortcuts? Choose one answer.
- A . Any interface in the overlay zones
- B . Interface connected to HUB only
- C . Between T3 on Branch-A and TC on Branch-B
- D . Between T2 on Branch-A and TA on Branch-B
Which three protocols can be used for the status check in a performance SLA? (Choose three.)
- A . SSH
- B . DNS
- C . traceroute
- D . TWAMP
- E . HTTP
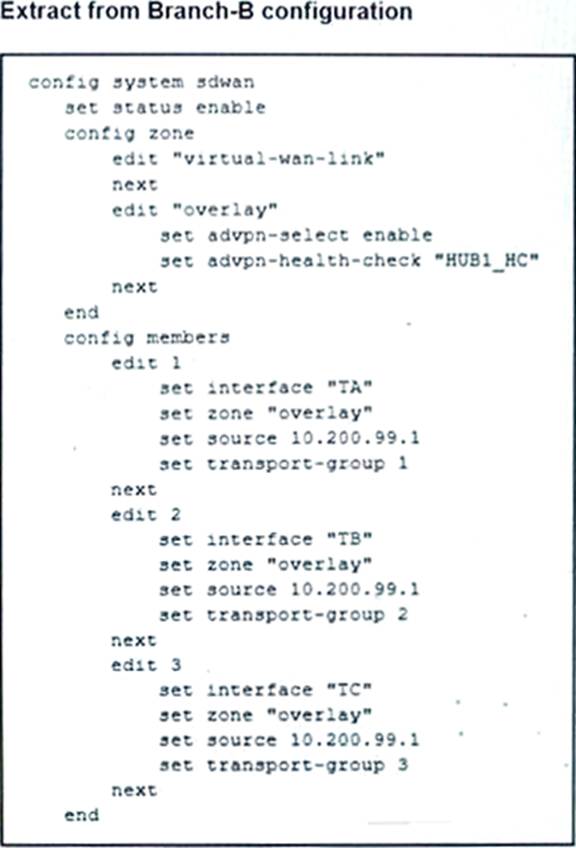
Refer to the exhibits.
The exhibits show two IPsec templates to define Branch IPsec 1 and Branch_IPsec_2. Each template defines a VPN tunnel. The error message that FortiManager displayed when the administrator tried to assign the second template to the FortiGate device is also shown.
Which statement best describes the cause of the issue?
- A . You can assign only one template with a tunnel type of static to each FortiGate device.
- B . You can assign only one IPsec template to each FortiGate device.
- C . You should review the branch1_fgt configuration for configured tunnels in the rootVDOM.
- D . You should use the same outgoing interface of both templates.
What is the purpose of configuring DIA (Direct Internet Access) in SD-WAN?
- A . To improve network security
- B . To ensure high application performance
- C . To reduce bandwidth usage
- D . To provide direct internet access to branch sites
