Practice Free 300-410 Exam Online Questions
Refer to the exhibit.
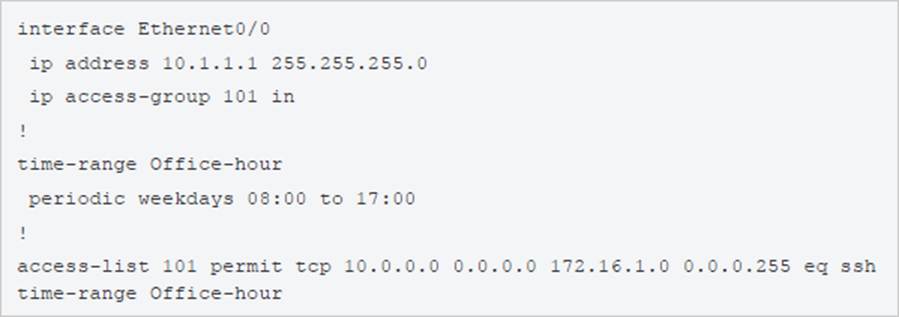
An IT staff member comes into the office during normal office hours and cannot access devices through SSH.
Which action should be taken to resolve this issue?
- A . Modify the access list to use the correct IP address.
- B . Configure the correct time range.
- C . Modify the access list to correct the subnet mask
- D . Configure the access list in the outbound direction.
A
Explanation:
To ACL should be permit tcp 101 10.1.1.1 0.0.0.0
A network administrator is tasked to permit http and https traffic only toward the internet from the User1 laptop to adhere to company’s security policy. The administrator can still ping to www.cisco.com.
Which interface should the access list 101 be applied to resolve this issue?
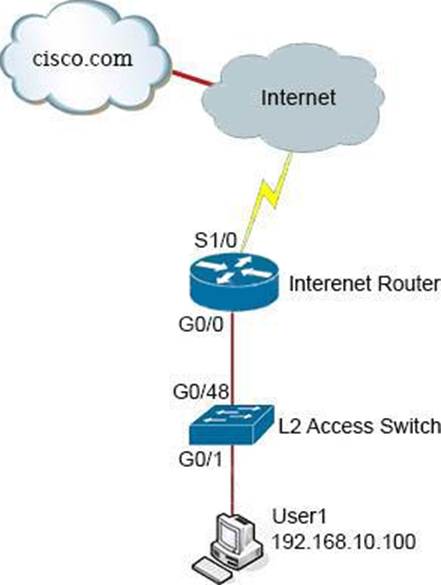
- A . Interface G0/48 in the incoming direction
- B . Interface G0/0 in the outgoing direction.
- C . Interface S1/0 in the outgoing direction.
- D . Interface G0/0 in the incoming direction.
What is a role of route distinguishers in an MPLS network?
- A . Route distinguishers define which prefixes are imported and exported on the edge router
- B . Route distinguishers allow multiple instances of a routing table to coexist within the edge router.
- C . Route distinguishers are used for label bindings.
- D . Route distinguishers make a unique VPNv4 address across the MPLS network
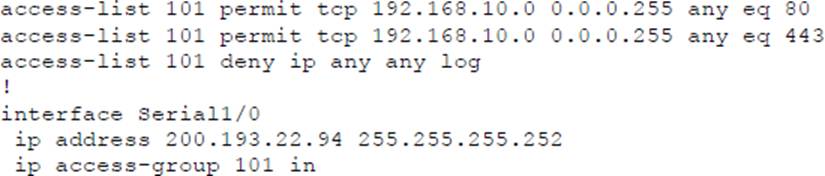
Refer to the exhibit.
R4 is experiencing packet drop when trying to reach 172.16.2.7 behind R2.
Which action resolves the issue?
- A . Insert a /16 floating static route on R2 toward R3 with metric 254
- B . Insert a /24 floating static route on R2 toward R3 with metric 254
- C . Enable auto summarization on all three routers R1, R2, and R3
- D . Disable auto summarization on R2
Refer to the exhibit.
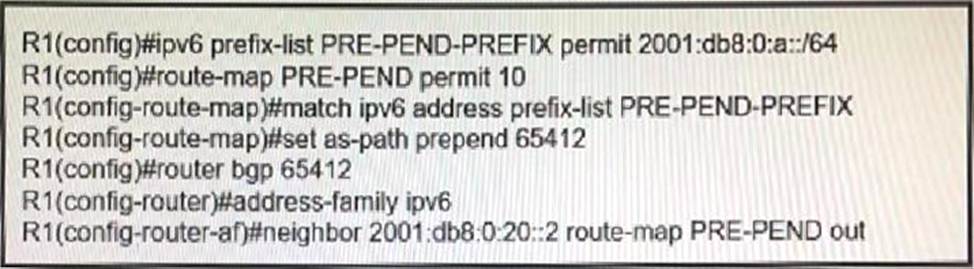
R1 has a route map configured, which results in a loss of partial IPv6 prefixes for the BGP neighbor, resulting in service degradation.
How can the full service be restored?
- A . The neighbor requires a soft reconfiguration, and this will clear the policy without resetting the BGP TCP connection.
- B . The prefix lit requires all prefixes that R1 is advertising to be added to it, and this will allow additional prefixes to be advertised.
- C . The route map requires a deny 20 statement without set conditions, and this will allow additional prefixes to be advertised.
- D . The route map requires a permit 20 statement without set conditions, and this will allow additional prefixes to be advertised.
Refer to the exhibit.
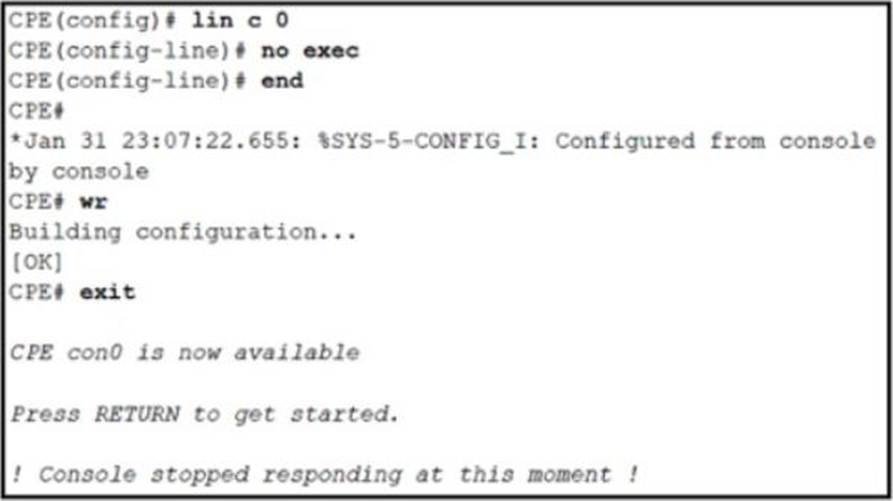
An administrator is attempting to disable the automatic logout after a period of inactivity. After logging out the console stopped responding to all keyword inputs.
Remote access through SSH still work resolves the issue?
- A . Configure the exec command on line con 0.
- B . Configure the absolute-timeout command on line con 0.
- C . Configure the default exec-timeout command on line con 0.
- D . Configure the no exec-timeout command on line con 0.
Refer to the exhibit.
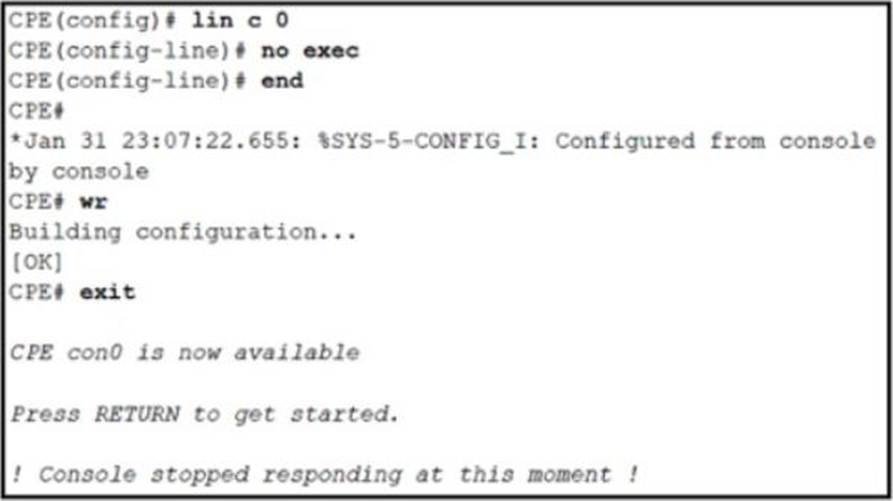
An administrator is attempting to disable the automatic logout after a period of inactivity. After logging out the console stopped responding to all keyword inputs.
Remote access through SSH still work resolves the issue?
- A . Configure the exec command on line con 0.
- B . Configure the absolute-timeout command on line con 0.
- C . Configure the default exec-timeout command on line con 0.
- D . Configure the no exec-timeout command on line con 0.
Which two statements about VRF-Lite configurations are true? (Choose two.)
- A . They support the exchange of MPLS labels
- B . Different customers can have overlapping IP addresses on different VPNs
- C . They support a maximum of 512.000 routes
- D . Each customer has its own dedicated TCAM resources
- E . Each customer has its own private routing table.
- F . They support IS-IS
Which two statements about VRF-Lite configurations are true? (Choose two.)
- A . They support the exchange of MPLS labels
- B . Different customers can have overlapping IP addresses on different VPNs
- C . They support a maximum of 512.000 routes
- D . Each customer has its own dedicated TCAM resources
- E . Each customer has its own private routing table.
- F . They support IS-IS
Which feature drops packets if the source address is not found in the snooping table?
- A . IPv6 Source Guard
- B . IPv6 Destination Guard
- C . IPv6 Prefix Guard
- D . Binding Table Recovery
A
Explanation:
https://www.cisco.com/c/en/us/td/docs/ios-xml/ios/ipv6_fhsec/configuration/xe-3s/ip6f-xe-3s-book/ip6-snooping.pdf
