Practice Free SY0-701 Exam Online Questions
A security administrator recently reset local passwords and the following values were recorded in the system:
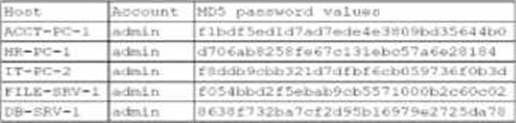
Which of the following in the security administrator most likely protecting against?
- A . Account sharing
- B . Weak password complexity
- C . Pass-the-hash attacks
- D . Password compromise
A company wants to use new Wi-Fi-enabled environmental sensors to automatically collect metrics.
Which of the following will the security team most likely do?
- A . Add the sensor software to the risk register.
- B . Create a VLAN for the sensors.
- C . Physically air gap the sensors.
- D . Configure TLS 1.2 on all sensors.
B
Explanation:
Creating a VLAN for Wi-Fi-enabled environmental sensors is the most likely and appropriate action. Security+ SY0-701 recommends network segmentation for IoT and sensor devices to reduce attack surface and limit lateral movement. A dedicated VLAN isolates sensors from critical systems while allowing controlled access to data collectors or management platforms.
Adding items to a risk register (A) documents risk but does not provide protection. Physically air gapping (C) contradicts the requirement for Wi-Fi connectivity. Configuring TLS 1.2 (D) is beneficial for data-in-transit protection but does not address network-level isolation and blast-radius reduction.
Thus, B: Create a VLAN for the sensors best aligns with secure design.
During a SQL update of a database, a temporary field that was created was replaced by an attacker in order to allow access to the system.
Which of the following best describes this type of vulnerability?
- A . Race condition
- B . Memory injection
- C . Malicious update
- D . Side loading
22.48.102 — 26/April/2023 22:05:11.22 GET "http://www.databaseInfo.com/index.html/../storedSQLqueries" 404
Which of the following attacks is most likely being attempted?
- A . Denial of service
- B . Password spraying
- C . SQL injection
- D . Directory traversal
D
Explanation:
The log entries show repeated attempts to access directories using patterns such as ../, which is a common directory traversal attack technique. Directory traversal (or path traversal) aims to access files and directories outside the web server’s root directory by manipulating file paths. The ../ sequence is used to move up one directory level, which attackers exploit to try and retrieve sensitive files.
Reference: CompTIA Security+ SY0-701 Official Study Guide, Domain 2.2: "Directory traversal attacks attempt to access files and directories outside of the web root by manipulating the file path with ../ sequences."
Exam Objectives 2.2: “Given a scenario, analyze potential indicators associated with application attacks.”
Which of the following has been implemented when a host-based firewall on a legacy Linux system allows connections from only specific internal IP addresses?
- A . Compensating control
- B . Network segmentation
- C . Transfer of risk
- D . SNMP traps
A
Explanation:
A compensating control is a security measure that is implemented to mitigate the risk of a vulnerability or a weakness that cannot be resolved by the primary control. A compensating control does not prevent or eliminate the vulnerability or weakness, but it can reduce the likelihood or impact of an attack. A host-based firewall on a legacy Linux system that allows connections from only specific internal IP addresses is an example of a compensating control, as it can limit the exposure of the system to potential threats from external or unauthorized sources. A host-based firewall is a software application that monitors and filters the incoming and outgoing network traffic on a single host, based on a set of rules or policies. A legacy Linux system is an older version of the Linux operating system that may not be compatible with the latest security updates or patches, and may have known vulnerabilities or weaknesses that could be exploited by attackers. = Security Controls C SY0-601 CompTIA Security+: 5.1, Security Controls C CompTIA Security+ SY0-501 C 5.7, CompTIA Security+ Study Guide with over 500 Practice Test Questions: Exam SY0-701, 9th Edition, Chapter 5, page 240. CompTIA Security+ (SY0-701) Certification Exam Objectives, Domain 5.1, page 18.
Which of the following control types is AUP an example of?
- A . Physical
- B . Managerial
- C . Technical
- D . Operational
B
Explanation:
An Acceptable Use Policy (AUP) is an example of a managerial control. Managerial controls are policies and procedures that govern an organization’s operations, ensuring security through directives and rules. The AUP defines acceptable behavior and usage of company resources, setting guidelines for employees.
Physical controls refer to security measures like locks, fences, or security guards.
Technical controls involve security mechanisms such as firewalls or encryption.
Operational controls are procedures for maintaining security, such as backup and recovery plans.
Which of the following control types is AUP an example of?
- A . Physical
- B . Managerial
- C . Technical
- D . Operational
B
Explanation:
An Acceptable Use Policy (AUP) is an example of a managerial control. Managerial controls are policies and procedures that govern an organization’s operations, ensuring security through directives and rules. The AUP defines acceptable behavior and usage of company resources, setting guidelines for employees.
Physical controls refer to security measures like locks, fences, or security guards.
Technical controls involve security mechanisms such as firewalls or encryption.
Operational controls are procedures for maintaining security, such as backup and recovery plans.
Which of the following security measures is required when using a cloud-based platform for loT management?
- A . Encrypted connection
- B . Federated identity
- C . Firewall
- D . Single sign-on
A company wants to protect a specialized legacy platform that controls the physical flow of gas inside
of pipes.
Which of the following environments does the company need to secure to best achieve this goal?
- A . IaaS
- B . SCADA
- C . SDN
- D . IoT
B
Explanation:
Systems that control physical industrial processes―such as pumping gas, water control, electrical grids, or manufacturing lines―fall under SCADA (Supervisory Control and Data Acquisition) environments. SCADA systems are part of larger OT (Operational Technology) infrastructures and manage sensors, actuators, valves, flow controls, and telemetry.
CompTIA Security+ SY0-701 explains that SCADA environments typically:
Use legacy protocols (e.g., Modbus, DNP3)
Require high availability
Often run outdated operating systems
Have control systems that cannot easily be patched
Require specialized segmentation and monitoring
This exactly matches the scenario describing a “specialized legacy platform controlling gas flow inside pipes.”
IaaS (A) is cloud infrastructure and unrelated to industrial control. SDN (C) relates to software-defined networking, not physical industrial controls. IoT (D) includes smart devices but is not typically used for large-scale industrial gas control.
Thus, securing SCADA is the correct answer.
A Chief Information Security Officer (CISO) has developed information security policies that relate to the software development methodology.
Which of the following would the CISO most likely include in the organization’s documentation?
- A . Peer review requirements
- B . Multifactor authentication
- C . Branch protection tests
- D . Secrets management configurations
