Practice Free SY0-701 Exam Online Questions
A security analyst finds a rogue device during a monthly audit of current endpoint assets that are connected to the network. The corporate network utilizes 002.1X for access control. To be allowed on the network, a device must have a Known hardware address, and a valid user name and password must be entered in a captive portal.
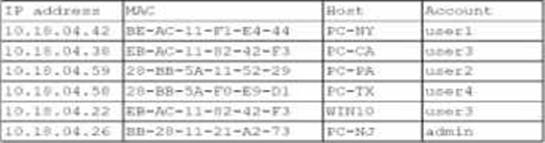
The following is the audit report:
Which of the following is the most likely way a rogue device was allowed to connect?
- A . A user performed a MAC cloning attack with a personal device.
- B . A DMCP failure caused an incorrect IP address to be distributed
- C . An administrator bypassed the security controls for testing.
- D . DNS hijacking let an attacker intercept the captive portal traffic.
A
Explanation:
The most likely way a rogue device was able to connect to the network is through a MAC cloning attack. In this attack, a personal device copies the MAC address of an authorized device, bypassing the 802.1X access control that relies on known hardware addresses for network access. The matching MAC addresses in the audit report suggest that this technique was used to gain unauthorized network access.
Reference =
CompTIA Security+ SY0-701 Course Content: Domain 03 Security Architecture.
CompTIA Security+ SY0-601 Study Guide: Chapter on Network Security and MAC Address Spoofing.
An administrator learns that users are receiving large quantities of unsolicited messages. The administrator checks the content filter and sees hundreds of messages sent to multiple users.
Which of the following best describes this kind of attack?
- A . Watering hole
- B . Typosquatting
- C . Business email compromise
- D . Phishing
D
Explanation:
The scenario describes a large number of unsolicited emails sent to multiple users. This is characteristic of phishing, which SY0-701 defines as mass-distributed fraudulent messages designed to trick recipients into clicking malicious links, downloading malware, or divulging sensitive information.
Phishing campaigns typically involve:
High volume
Non-targeted messaging
Use of spoofed addresses or fake content
Delivery through email systems
A watering-hole attack (A) compromises a legitimate website frequented by targets―not email. Typosquatting (B) relies on malicious websites with deceptive URLs. Business Email Compromise (C) involves highly targeted spear-phishing or impersonation attacks, not bulk email blasts.
Because this incident involves “hundreds of messages” delivered to “multiple users,” it clearly matches the characteristics of a phishing attack, not a sophisticated targeted attack type.
Phishing is the most common form of social engineering and is emphasized heavily in the Security+ exam due to its frequency and effectiveness.
A company is considering an expansion of access controls for an application that contractors and internal employees use to reduce costs.
Which of the following risk elements should the implementation team understand before granting access to the application?
- A . Threshold
- B . Appetite
- C . Avoidance
- D . Register
B
Explanation:
Risk appetite refers to the level of risk an organization is willing to accept before implementing security measures. When expanding access controls, the company must assess how much risk is acceptable in terms of data exposure, unauthorized access, and compliance obligations.
Reference: CompTIA Security+ SY0-701 Official Study Guide, Risk Management domain.
Which of the following provides the details about the terms of a test with a third-party penetration tester?
- A . Rules of engagement
- B . Supply chain analysis
- C . Right to audit clause
- D . Due diligence
A
Explanation:
Rules of engagement are the detailed guidelines and constraints regarding the execution of information security testing, such as penetration testing. They define the scope, objectives, methods, and boundaries of the test, as well as the roles and responsibilities of the testers and the clients. Rules of engagement help to ensure that the test is conducted in a legal, ethical, and professional manner, and that the results are accurate and reliable.
Rules of engagement typically include the following elements:
The type and scope of the test, such as black box, white box, or gray box, and the target systems, networks, applications, or data.
The client contact details and the communication channels for reporting issues, incidents, or emergencies during the test.
The testing team credentials and the authorized tools and techniques that they can use.
The sensitive data handling and encryption requirements, such as how to store, transmit, or dispose of any data obtained during the test.
The status meeting and report schedules, formats, and recipients, as well as the confidentiality and non-disclosure agreements for the test results.
The timeline and duration of the test, and the hours of operation and testing windows.
The professional and ethical behavior expectations for the testers, such as avoiding unnecessary damage, disruption, or disclosure of information.
Supply chain analysis, right to audit clause, and due diligence are not related to the terms of a test with a third-party penetration tester. Supply chain analysis is the process of evaluating the security and risk posture of the suppliers and partners in a business network. Right to audit clause is a provision in a contract that gives one party the right to audit another party to verify their compliance with the contract terms and conditions. Due diligence is the process of identifying and addressing the cyber risks that a potential vendor or partner brings to an organization.
Reference =
https://www.yeahhub.com/every-penetration-tester-you-should-know-about-this-rules-of-engagement/
https://bing.com/search?q=rules+of+engagement+penetration+testing
As part of new compliance audit requirements, multiple servers need to be segmented on different networks and should be reachable only from authorized internal systems.
Which of the following would meet the requirements?
- A . Configure firewall rules to block external access to Internal resources.
- B . Set up a WAP to allow internal access from public networks.
- C . Implement a new IPSec tunnel from internal resources.
- D . Deploy an Internal Jump server to access resources.
A
Explanation:
"Network segmentation is a security practice that divides a network into smaller, isolated segments to limit access and reduce the attack surface. Firewalls are commonly used to enforce segmentation by creating rules that allow or deny traffic based on source, destination, and port. To meet compliance requirements, such as restricting access to internal servers, firewall rules can be configured to block all external traffic while permitting only authorized internal systems to communicate with the segmented servers. This ensures that sensitive resources are isolated from unauthorized access."
Reference: CompTIA Security+ SY0-701 Study Guide, Domain 2.0: Architecture and Design, Section:
"Secure Network Architecture Concepts" (Firewalls and network segmentation are key topics).
The requirement is to segment servers on different networks and restrict access to only authorized internal systems.
Option A directly addresses this by using firewall rules to block external access while allowing internal traffic, aligning with network segmentation best practices.
Option B (WAP) refers to a Wireless Access Point, which doesn’t fit the context of segmentation and could expose resources to public networks.
Option C (IPSec tunnel) secures communication but doesn’t inherently segment networks.
Option D (jump server) adds a layer of access control but doesn’t address the segmentation requirement alone. Thus, A is the best fit.
Users at a company are reporting they are unable to access the URL for a new retail website because it is flagged as gambling and is being blocked.
Which of the following changes would allow users to access the site?
- A . Creating a firewall rule to allow HTTPS traffic
- B . Configuring the IPS to allow shopping
- C . Tuning the DLP rule that detects credit card data
- D . Updating the categorization in the content filter
D
Explanation:
A content filter is a device or software that blocks or allows access to web content based on predefined rules or categories. In this case, the new retail website is mistakenly categorized as gambling by the content filter, which prevents users from accessing it. To resolve this issue, the content filter’s categorization needs to be updated to reflect the correct category of the website, such as shopping or retail. This will allow the content filter to allow access to the website instead of blocking it.
Reference: CompTIA Security+ Study Guide: Exam SY0-701, 9th Edition, Chapter 3: Technologies and Tools, page 1221. CompTIA Security+ Certification Kit: Exam SY0-701, 7th Edition, Chapter 3: Technologies and Tools, page 1222.
Users at a company are reporting they are unable to access the URL for a new retail website because it is flagged as gambling and is being blocked.
Which of the following changes would allow users to access the site?
- A . Creating a firewall rule to allow HTTPS traffic
- B . Configuring the IPS to allow shopping
- C . Tuning the DLP rule that detects credit card data
- D . Updating the categorization in the content filter
D
Explanation:
A content filter is a device or software that blocks or allows access to web content based on predefined rules or categories. In this case, the new retail website is mistakenly categorized as gambling by the content filter, which prevents users from accessing it. To resolve this issue, the content filter’s categorization needs to be updated to reflect the correct category of the website, such as shopping or retail. This will allow the content filter to allow access to the website instead of blocking it.
Reference: CompTIA Security+ Study Guide: Exam SY0-701, 9th Edition, Chapter 3: Technologies and Tools, page 1221. CompTIA Security+ Certification Kit: Exam SY0-701, 7th Edition, Chapter 3: Technologies and Tools, page 1222.
Which of the following best explains the role of compensating controls?
- A . Reducing the attack surface by isolating vulnerable components within a segmented environment
- B . Providing an alternative security measure when standard remediation is not feasible
- C . Delaying remediation timelines by replacing affected systems in a maintenance window
- D . Remediating software flaws by modifying source code to remove insecure functions
B
Explanation:
The best answer is B. Providing an alternative security measure when standard remediation is not feasible.
A compensating control is a substitute safeguard used when the preferred or required control cannot be implemented immediately or at all. It helps reduce risk in another way until proper remediation is possible, or when direct remediation is impractical.
Examples include:
increasing monitoring when a system cannot be patched segmenting a legacy application that cannot be upgraded restricting access to a vulnerable system that must remain in service Why the other options are incorrect:
Which of the following are the best for hardening end-user devices? (Select two)
- A . Full disk encryption
- B . Group-level permissions
- C . Account lockout
- D . Endpoint protection
- E . Proxy server
- F . Segmentation
A,D
Explanation:
Full disk encryption (A)ensures that data stored on the device is protected even if the device is physically stolen. This is a fundamental security control for end-user devices, especially laptops and mobile devices, to prevent data breaches.
Endpoint protection (D)refers to anti-malware, antivirus, and host-based firewall solutions that safeguard end-user devices from malware, ransomware, and unauthorized access.
These measures are explicitly referenced in the CompTIA Security+ SY0-701exam objective2.2: Given a scenario, apply security concepts in support of organizational risk mitigation under Device hardening.
Reference: CompTIA Security+ SY0-701 Official Exam Objectives, Domain 2.2 C “Device hardening (e.g., full disk encryption, antivirus/antimalware, endpoint detection and response).”
An organization is adopting cloud services at a rapid pace and now has multiple SaaS applications in use. Each application has a separate log-in. so the security team wants to reduce the number of credentials each employee must maintain.
Which of the following is the first step the security team should take?
- A . Enable SAML
- B . Create OAuth tokens.
- C . Use password vaulting.
- D . Select an IdP
D
Explanation:
The first step in reducing the number of credentials each employee must maintain when using multiple SaaS applications is to select an Identity Provider (IdP). An IdP provides a centralized authentication service that supports Single Sign-On (SSO), enabling users to access multiple applications with a single set of credentials.
Enabling SAML would be part of the technical implementation but comes after selecting an IdP.
OAuth tokens are used for authorization, but selecting an IdP is the first step in managing authentication.
Password vaulting stores multiple passwords securely but doesn’t reduce the need for separate logins.
