Practice Free SY0-701 Exam Online Questions
A government worker secretly copies classified files that contain defense tactics information to an external drive. The government worker then gives the external drive to a corrupt organization.
Which of the following best describes the motivation of the worker?
- A . Espionage
- B . Data exfiltration
- C . Financial gain
- D . Blackmail
A
Explanation:
The act described is espionage, where classified information is stolen and provided to adversaries or unauthorized parties, usually for political, military, or strategic advantage.
Data exfiltration (B) is the technical act of stealing data but doesn’t specify motivation. Financial gain (C) or blackmail (D) could be motivations but are not clearly indicated here.
Espionage is a classic threat actor motivation outlined in the Threats domain 【 6:Chapter 2†CompTIA Security+ Study Guide 】 .
Which of the following provides the best protection against unwanted or insecure communications to and from a device?
- A . System hardening
- B . Host-based firewall
- C . Intrusion detection system
- D . Anti-malware software
B
Explanation:
A host-based firewall controls incoming and outgoing network traffic on a device by enforcing security rules, effectively blocking unwanted or insecure communications. It is specifically designed to protect the device from unauthorized access and malicious traffic.
System hardening (A) reduces vulnerabilities by disabling unnecessary services and patching but does not control communications dynamically. Intrusion detection systems (C) detect suspicious traffic but typically do not block it (unless paired with prevention). Anti-malware (D) protects against malicious software but not directly network communication filtering.
Host-based firewalls are a fundamental component of endpoint security highlighted in the Security Operations domain of SY0-701 【 6:Chapter 11†CompTIA Security+ Study Guide 】 .
An administrator discovers that some files on a database server were recently encrypted. The administrator sees from the security logs that the data was last accessed by a domain user.
Which of the following best describes the type of attack that occurred?
- A . Insider threat
- B . Social engineering
- C . Watering-hole
- D . Unauthorized attacker
A
Explanation:
An insider threat is a type of attack that originates from someone who has legitimate access to an organization’s network, systems, or data. In this case, the domain user who encrypted the files on the database server is an example of an insider threat, as they abused their access privileges to cause harm to the organization. Insider threats can be motivated by various factors, such as financial gain, revenge, espionage, or sabotage.
Reference: CompTIA Security+ Study Guide: Exam SY0-701, 9th Edition, Chapter 1: General Security
Concepts, page 251. CompTIA Security+ Certification Kit: Exam SY0-701, 7th Edition, Chapter 1:
General Security Concepts, page 252.
A security analyst is reviewing the following logs:
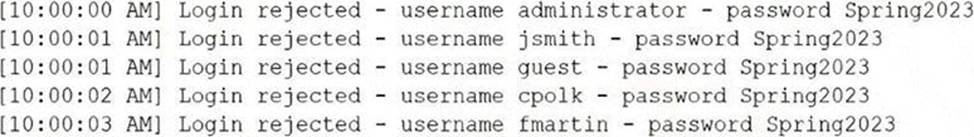
Which of the following attacks is most likely occurring?
- A . Password spraying
- B . Account forgery
- C . Pass-t he-hash
- D . Brute-force
A
Explanation:
Password spraying is a type of brute force attack that tries common passwords across several accounts to find a match. It is a mass trial-and-error approach that can bypass account lockout protocols. It can give hackers access to personal or business accounts and information. It is not a targeted attack, but a high-volume attack tactic that uses a dictionary or a list of popular or weak passwords12.
The logs show that the attacker is using the same password ("password123") to attempt to log in to different accounts ("admin", "user1", "user2", etc.) on the same web server. This is a typical pattern of password spraying, as the attacker is hoping that at least one of the accounts has a weak password that matches the one they are trying. The attacker is also using a tool called Hydra, which is one of the most popular brute force tools, often used in cracking passwords for network authentication3.
Account forgery is not the correct answer, because it involves creating fake accounts or credentials to impersonate legitimate users or entities. There is no evidence of account forgery in the logs, as the attacker is not creating any new accounts or using forged credentials.
Pass-the-hash is not the correct answer, because it involves stealing a hashed user credential and using it to create a new authenticated session on the same network. Pass-the-hash does not require the attacker to know or crack the password, as they use the stored version of the password to initiate a new session4. The logs show that the attacker is using plain text passwords, not hashes, to try to log in to the web server.
Brute-force is not the correct answer, because it is a broader term that encompasses different types of attacks that involve trying different variations of symbols or words until the correct password is found. Password spraying is a specific type of brute force attack that uses a single common password against multiple accounts5. The logs show that the attacker is using password spraying, not brute force in general, to try to gain access to the web server.
Reference = 1: Password spraying: An overview of password spraying attacks … – Norton, 2: Security: Credential Stuffing vs. Password Spraying – Baeldung, 3: Brute ForceAttack: A definition + 6 types to know | Norton, 4:.
What is a Pass-the-Hash Attack? – CrowdStrike, 5:.
What is a Brute Force Attack? | Definition, Types & How It Works – Fortinet
Following a security review, an organization must ensure users verify their identities against the company’s identity services with individual credentials leveraging WPA2-Enterprise for wireless access.
Which of the following configuration steps correctly applies RADIUS in this environment?
- A . Enabling 802.1X authentication and integrating it with the corporate directory
- B . Installing self-signed certificates on all user devices
- C . Enabling MAC filters for all wireless clients
- D . Configuring the wireless controller to require multifactor authentication
A
Explanation:
WPA2-Enterprise is designed for environments where users authenticate with unique, individual credentials backed by an enterprise identity store, rather than a shared preshared key. The Study Guide explicitly states: “WPA2-Enterprise relies on a RADIUS authentication server as part of an 802.1X implementation for authentication. Users can thus have unique credentials and be individually identified.” That maps directly to the requirement that users verify identity against the company’s identity services using individual credentials. It further explains how this is implemented operationally: “802.1X is an IEEE standard for access control… In wireless networks, 802.1X is used to integrate with RADIUS servers, allowing enterprise users to authenticate and gain access to the network.”
Therefore, the correct configuration step is enabling 802.1X and tying authentication into the organization’s identity source (commonly a corporate directory). The other choices don’t correctly “apply RADIUS” for WPA2-Enterprise: self-signed certs are not universally required for all EAP types and can introduce trust issues; MAC filters are weak and spoofable; and MFA might be beneficial but is not the fundamental step that enables RADIUS-backed WPA2-Enterprise authentication.
Reference: WPA2-Enterprise uses RADIUS + 802.1X and supports unique user credentials; 802.1X integrates wireless authentication with RADIUS.
While troubleshooting a firewall configuration, a technician determines that a “deny any” policy should be added to the bottom of the ACL. The technician updates the policy, but the new policy causes several company servers to become unreachable.
Which of the following actions would prevent this issue?
- A . Documenting the new policy in a change request and submitting the request to change management
- B . Testing the policy in a non-production environment before enabling the policy in the production network
- C . Disabling any intrusion prevention signatures on the ‘deny any* policy prior to enabling the new policy
- D . Including an ‘allow any1 policy above the ‘deny any* policy
B
Explanation:
A firewall policy is a set of rules that defines what traffic is allowed or denied on a network. A firewall policy should be carefully designed and tested before being implemented, as a misconfigured policy can cause network disruptions or security breaches. A common best practice is to test the policy in a non-production environment, such as a lab or a simulation, before enabling the policy in the production network. This way, the technician can verify the functionality and performance of the policy, and identify and resolve any issues or conflicts, without affecting the live network. Testing the policy in a non-production environment would prevent the issue of the ‘deny any’ policy causing several company servers to become unreachable, as the technician would be able to detect and correct the problem before applying the policy to the production network.
Documenting the new policy in a change request and submitting the request to change management is a good practice, but it would not prevent the issue by itself. Change management is a process that ensures that any changes to the network are authorized, documented, and communicated, but it does not guarantee that the changes are error-free or functional. The technician still needs to test the policy before implementing it.
Disabling any intrusion prevention signatures on the ‘deny any’ policy prior to enabling the new policy would not prevent the issue, and it could reduce the security of the network. Intrusion prevention signatures are patterns that identify malicious or unwanted traffic, and allow the firewall to block or alert on such traffic. Disabling these signatures would make the firewall less effective in detecting and preventing attacks, and it would not affect the reachability of the company servers.
Including an ‘allow any’ policy above the ‘deny any’ policy would not prevent the issue, and it would render the ‘deny any’ policy useless. A firewall policy is processed from top to bottom, and the first matching rule is applied. An ‘allow any’ policy would match any traffic and allow it to pass through the firewall, regardless of the source, destination, or protocol. This would negate the purpose of the ‘deny any’ policy, which is to block any traffic that does not match any of the previous rules. Moreover, an ‘allow any’ policy would create a security risk, as it would allow any unauthorized or malicious traffic to enter or exit the network.
Reference = CompTIA Security+ SY0-701 Certification Study Guide, page 204-205; Professor Messer’s CompTIA SY0-701 Security+ Training Course, video 2.1 – Network Security Devices, 8:00 – 10:00.
An analyst is evaluating the implementation of Zero Trust principles within the data plane.
Which of the following would be most relevant for the analyst to evaluate?
- A . Secured zones
- B . Subject role
- C . Adaptive identity
- D . Threat scope reduction
D
Explanation:
The data plane, also known as the forwarding plane, is the part of the network that carries user traffic and data. It is responsible for moving packets from one device to another based on the routing and switching decisions made by the control plane. The data plane is a critical component of the Zero Trust architecture, as it is where most of the attacks and breaches occur. Therefore, implementing Zero Trust principles within the data plane can help to improve the security and resilience of the network.
One of the key principles of Zero Trust is to assume breach and minimize the blast radius and segment access. This means that the network should be divided into smaller and isolated segments or zones, each with its own security policies and controls. This way, if one segment is compromised, the attacker cannot easily move laterally to other segments and access more resources or data. This principle is also known as threat scope reduction, as it reduces the scope and impact of a potential threat.
The other options are not as relevant for the data plane as threat scope reduction. Secured zones are a concept related to the control plane, which is the part of the network that makes routing and switching decisions. Subject role is a concept related to the identity plane, which is the part of the network that authenticates and authorizes users and devices. Adaptive identity is a concept related to the policy plane, which is the part of the network that defines and enforces the security policies and rules.
Reference =
https://bing.com/search?q=Zero+Trust+data+plane
https://learn.microsoft.com/en-us/security/zero-trust/deploy/data
A store is setting up wireless access for employees. Management wants to limit the number of access points while ensuring full coverage.
Which tool will help determine how many access points are needed?
- A . Signal locator
- B . WPA3
- C . Heat map
- D . Site survey
D
Explanation:
A site survey is the formal process used to determine the required number, placement, and configuration of wireless access points (APs). Security+ SY0-701 states that site surveys measure RF propagation, identify dead zones, account for building materials, detect interference sources, and evaluate coverage overlap. This information allows network engineers to deploy the fewest APs necessary while still ensuring full coverage.
Although heat maps (C) are generated as a result of a site survey, they are visualization tools―not the actual survey process. A signal locator (A) is not a standardized tool in wireless planning. WPA3 (B) is a wireless security protocol and has no impact on access point planning or coverage optimization.
A full site survey ensures optimal AP placement to balance coverage, performance, and cost―exactly the concern described in the scenario.
Thus, the correct answer is D: Site survey.
An employee emailed a new systems administrator a malicious web link and convinced the administrator to change the email server’s password. The employee used this access to remove the mailboxes of key personnel.
Which of the following security awareness concepts would help prevent this threat in the future?
- A . Recognizing phishing
- B . Providing situational awareness training
- C . Using password management
- D . Reviewing email policies
A cybersecurity incident response team at a large company receives notification that malware is present on several corporate desktops No known Indicators of compromise have been found on the network.
Which of the following should the team do first to secure the environment?
- A . Contain the Impacted hosts
- B . Add the malware to the application blocklist.
- C . Segment the core database server.
- D . Implement firewall rules to block outbound beaconing
A
Explanation:
The first step in responding to a cybersecurity incident, particularly when malware is detected, is to contain the impacted hosts. This action prevents the spread of malware to other parts of the network, limiting the potential damage while further investigation and remediation actions are planned.
Reference = CompTIA Security+ SY0-701 study materials, particularly on incident response procedures and the importance of containment in managing security incidents.
