Practice Free SY0-701 Exam Online Questions
An alert references attacks associated with a zero-day exploit. An analyst places a bastion host in the network to reduce the risk of the exploit.
Which of the following types of controls is the analyst implementing?
- A . Compensating
- B . Detective
- C . Operational
- D . Physical
A
Explanation:
The correct answer is Compensating because a bastion host is being used as an alternative safeguard to reduce risk when a primary control cannot yet be fully implemented. In the context of the Security+ SY0-701 objectives, compensating controls are designed to provide protection when standard preventive controls are not available, effective, or feasible―such as during a zero-day exploit where no vendor patch or permanent fix exists.
A zero-day exploit represents a vulnerability that is actively being exploited before developers or vendors have released a fix. Since patching is not immediately possible, organizations must rely on compensating controls to limit exposure and reduce the likelihood or impact of exploitation. A bastion host is a hardened system placed in a network segment―often in a demilitarized zone (DMZ)―that acts as a controlled access point between untrusted and trusted networks. By routing access through this tightly secured host, the analyst reduces the attack surface and restricts direct access to internal systems that may be vulnerable to the zero-day.
Option B, Detective, is incorrect because detective controls are focused on identifying or alerting on malicious activity after it occurs, such as logging, monitoring, or intrusion detection systems.
Option C, Operational, refers to processes and procedures carried out by people, such as incident response or change management, rather than a technical safeguard.
Option D, Physical, applies to tangible protections like locks, cameras, or fencing, which are not relevant in this network-based scenario.
The SY0-701 study guide emphasizes the importance of layered security and adaptive risk management. When preventive controls fail or are temporarily unavailable, compensating controls like bastion hosts, network segmentation, and access restrictions allow organizations to maintain security posture and continuity of operations while longer-term solutions are developed.
A new security regulation was announced that will take effect in the coming year. A company must comply with it to remain in business.
Which of the following activities should the company perform next?
- A . Gap analysis
- B . Policy review
- C . Security procedure evaluation
- D . Threat scope reduction
Which of the following is a common source of unintentional corporate credential leakage in cloud environments?
- A . Code repositories
- B . Dark web
- C . Threat feeds
- D . State actors
- E . Vulnerability databases
A
Explanation:
Code repositories are a common source of unintentional corporate credential leakage, especially in cloud environments. Developers may accidentally commit and push sensitive information, such as API keys, passwords, and other credentials, to public or poorly secured repositories. These credentials can then be accessed by unauthorized users, leading to security breaches. Ensuring that repositories are properly secured and that sensitive data is never committed is critical for protecting against this type of leakage.
Reference =
CompTIA Security+ SY0-701 Course Content: Domain 03 Security Architecture.
CompTIA Security+ SY0-601 Study Guide: Chapter on Threats and Vulnerability Management.
During an investigation, an incident response team attempts to understand the source of an incident.
Which of the following incident response activities describes this process?
- A . Analysis
- B . Lessons learned
- C . Detection
- D . Containment
A
Explanation:
Analysis is the incident response activity that describes the process of understanding the source of an incident. Analysis involves collecting and examining evidence, identifying the root cause, determining the scope and impact, and assessing the threat actor’s motives and capabilities. Analysis helps the incident response team to formulate an appropriate response strategy, as well as to prevent or mitigate future incidents. Analysis is usually performed after detection and before containment, eradication, recovery, and lessons learned.
Reference = CompTIA Security+ Study Guide with over 500 Practice Test Questions: Exam SY0-701, 9th Edition, Chapter 6, page 223. CompTIA Security+ SY0-701 Exam Objectives, Domain 4.2, page 13.
HOTSPOT
You are security administrator investigating a potential infection on a network.
Click on each host and firewall. Review all logs to determine which host originated the Infecton and then deny each remaining hosts clean or infected.
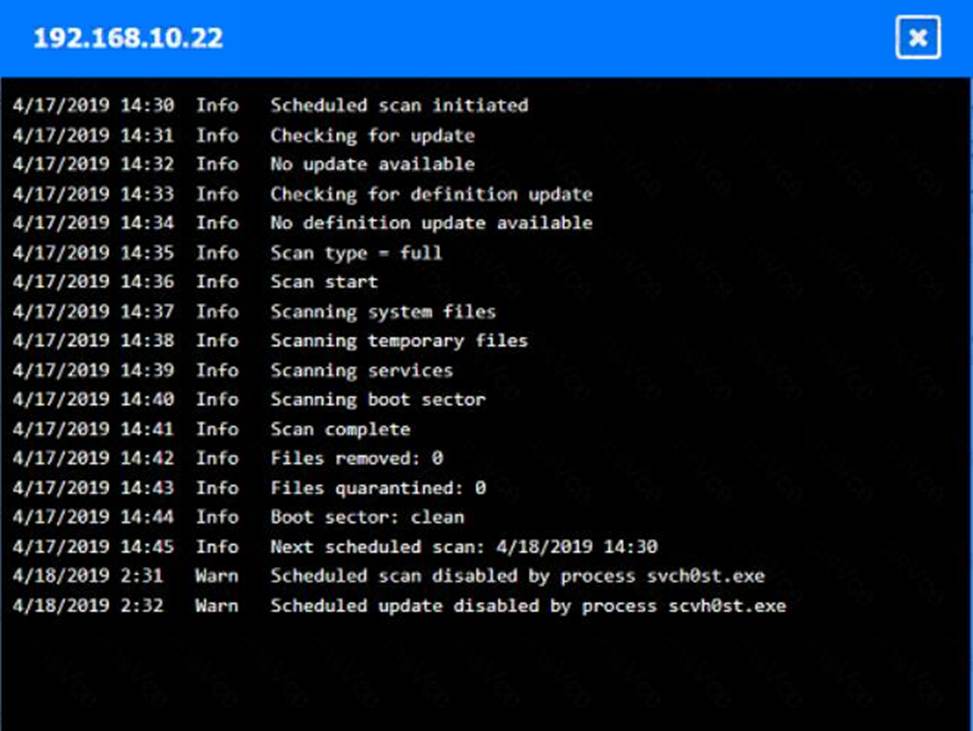
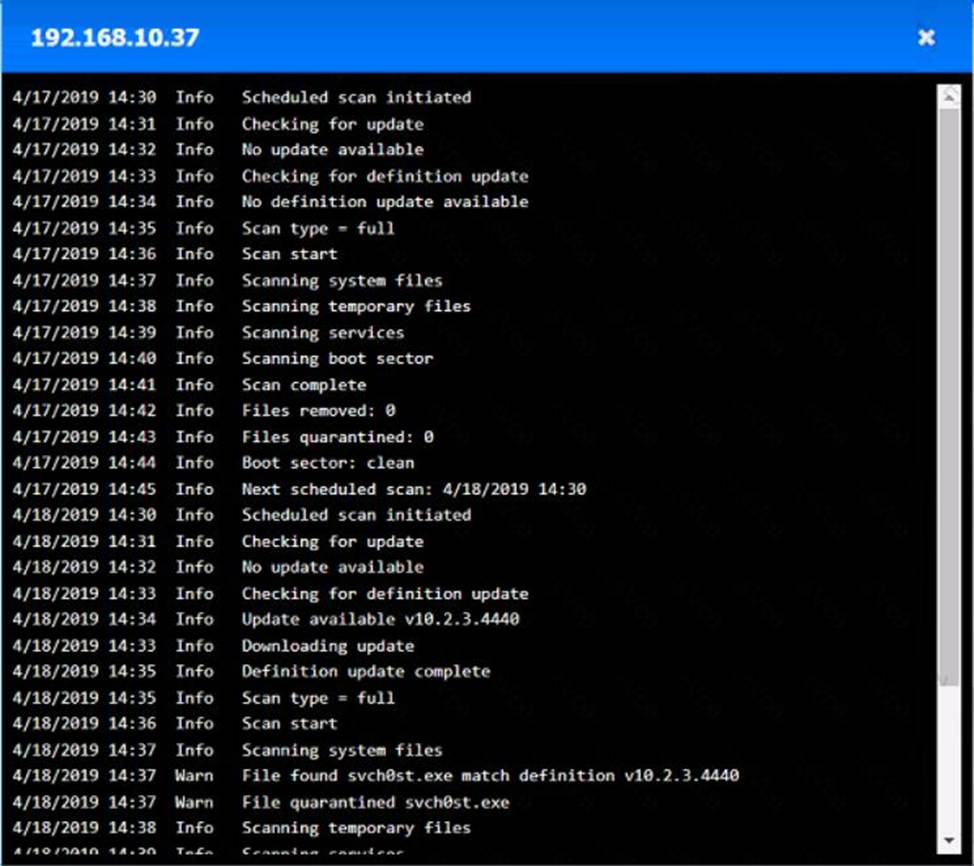
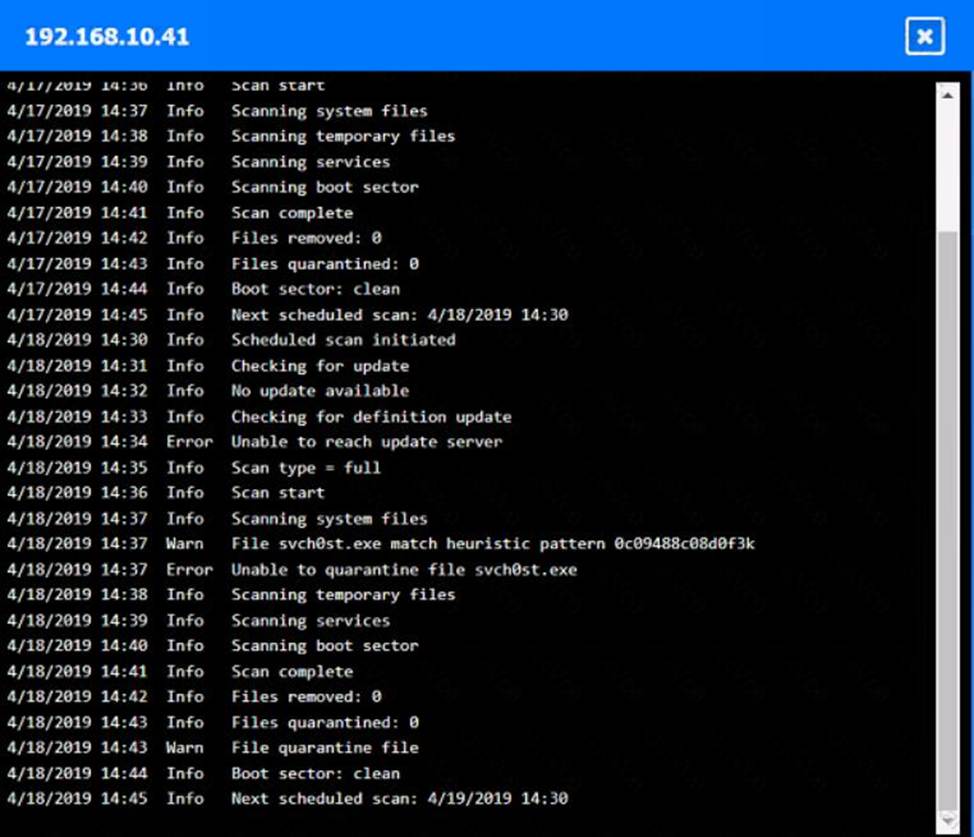
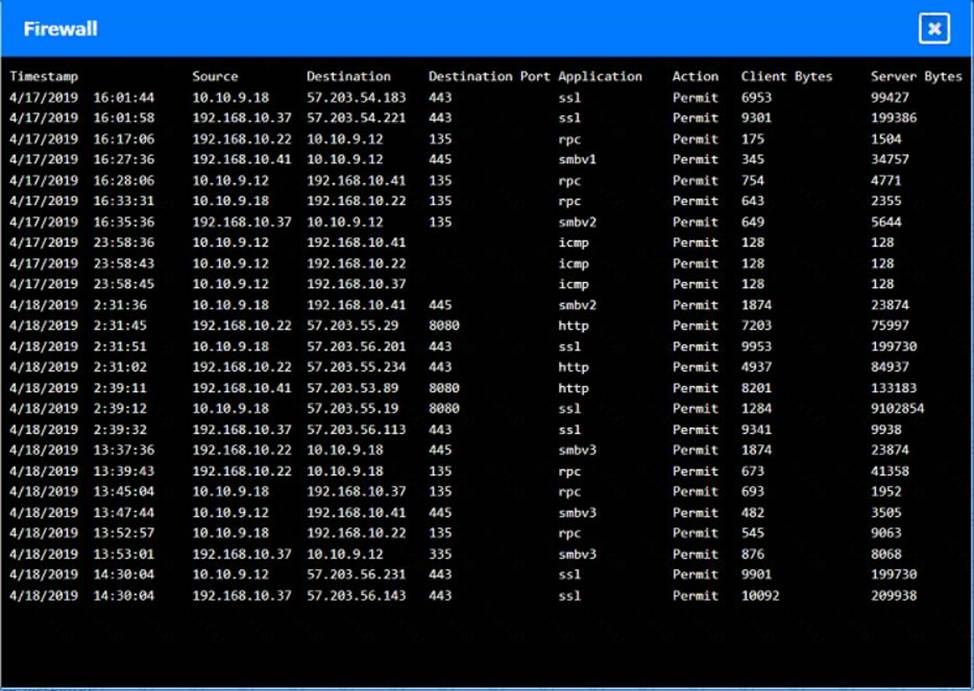
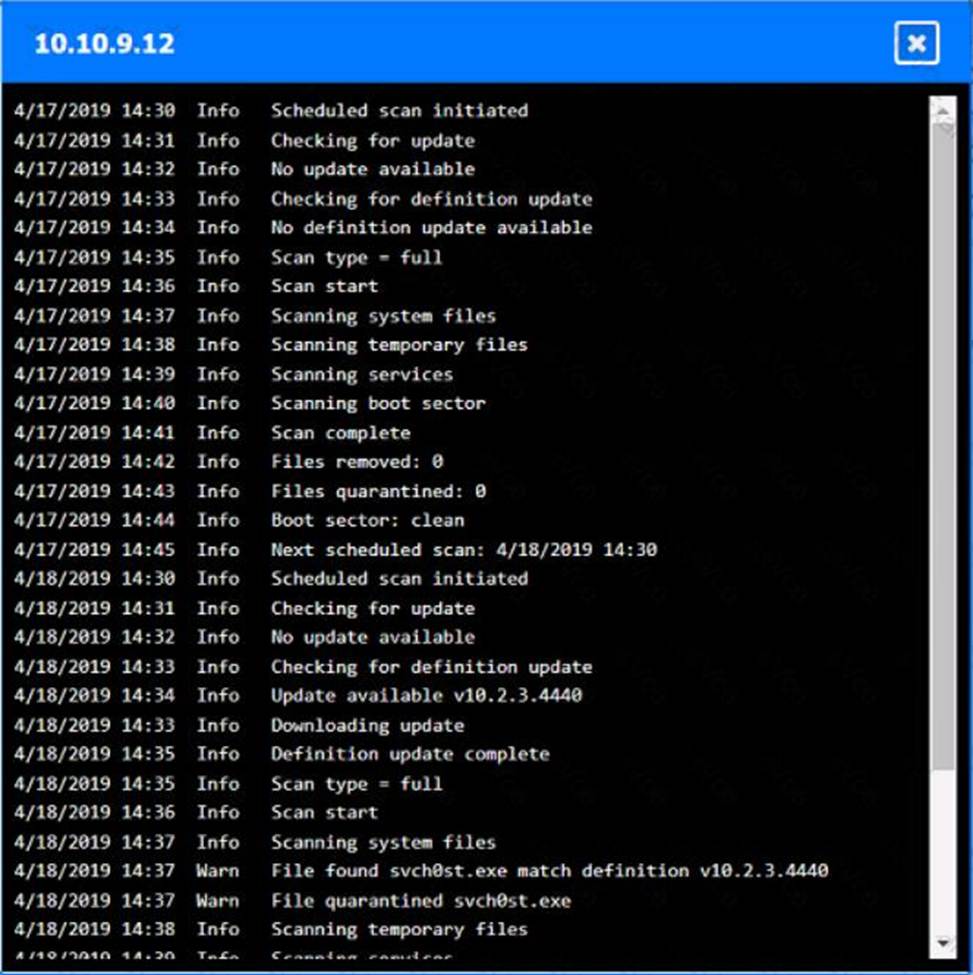
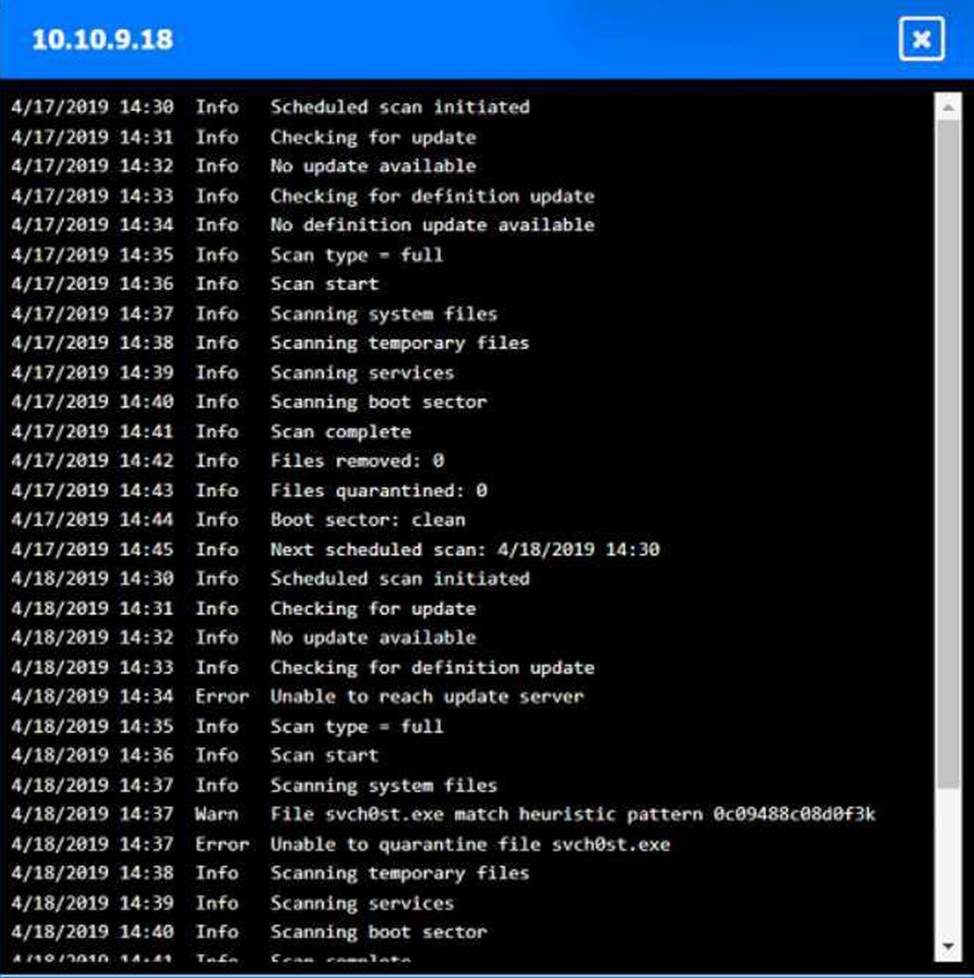
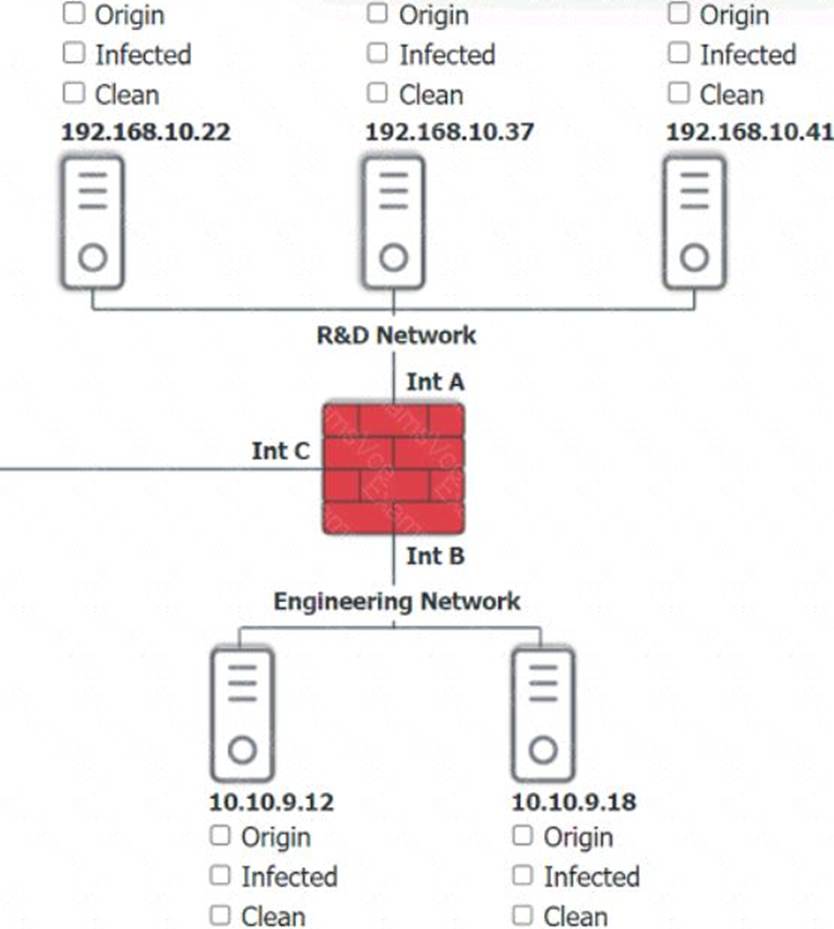
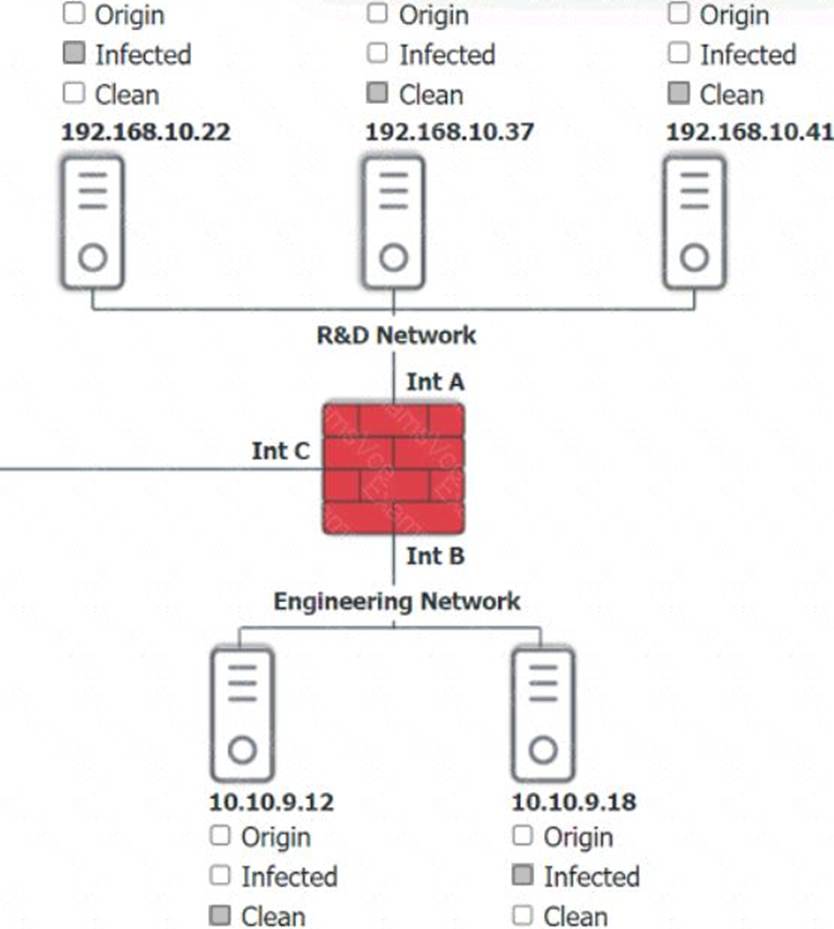
Explanation:
A screenshot of a computer AI-generated content may be incorrect.
Based on the logs, it seems that the host that originated the infection is 192.168.10.22. This host has a suspicious process named svchost.exe running on port 443, which is unusual for a Windows service. It also has a large number of outbound connections to different IP addresses on port 443, indicating that it is part of a botnet.
The firewall log shows that this host has been communicating with 10.10.9.18, which is another infected host on the engineering network. This host also has a suspicious process named svchost.exe running on port 443, and a large number of outbound connections to different IP addresses on port 443.
The other hosts on the R&D network (192.168.10.37 and 192.168.10.41) are clean, as they do not have any suspicious processes or connections.
A security officer observes that a software development team is not complying with its corporate security policy on encrypting confidential data.
Which of the following categories refers to this type of non-compliance?
- A . External
- B . Standard
- C . Regulation
- D . Internal
D
Explanation:
Non-compliance with internal policies, such as corporate security policies, falls under internal non-compliance. These are rules created and enforced within the organization to maintain security standards.
External non-compliance (A) refers to violations of outside regulations or laws. Standards (B) are generally established best practices or industry guidelines, and regulation (C) refers to legal or governmental requirements.
Internal compliance management is a key focus area in the Security Program Management domain of SY0-701 【 6:Chapter 16†CompTIA Security+ Study Guide 】 .
An employee clicked a malicious link in an email and downloaded malware onto the company’s computer network. The malicious program exfiltrated thousands of customer records.
Which of the following should the company implement to prevent this in the future?
- A . User awareness training
- B . Network monitoring
- C . Endpoint protection
- D . Data loss prevention
A
Explanation:
Comprehensive and Detailed In-Depth
User awareness training is essential in preventing security incidents caused by human error, such as clicking on malicious links. Employees need to be educated on recognizing phishing attempts, verifying email senders, and avoiding suspicious downloads.
Network monitoring detects and alerts on malicious activity but does not prevent employees from clicking on harmful links.
Endpoint protection can mitigate malware infections but is not foolproof, especially if users continue to fall for phishing attacks.
Data loss prevention (DLP)can prevent data exfiltration but does not stop malware from being introduced into the system.
By training employees to recognize and avoid phishing scams, organizations can reduce the risk of malware infections and data breaches.
A company’s marketing department collects, modifies, and stores sensitive customer data. The infrastructure team is responsible for securing the data while in transit and at rest.
Which of the following data roles describes the customer?
- A . Processor
- B . Custodian
- C . Subject
- D . Owner
C
Explanation:
According to the CompTIA Security+ SY0-701 Certification Study Guide, data subjects are the individuals whose personal data is collected, processed, or stored by an organization. Data subjects have certain rights and expectations regarding how their data is handled, such as the right to access, correct, delete, or restrict their data. Data subjects are different from data owners, who are the individuals or entities that have the authority and responsibility to determine how data is classified, protected, and used. Data subjects are also different from data processors, who are the individuals or entities that perform operations on data on behalf of the data owner, such as collecting, modifying, storing, or transmitting data. Data subjects are also different from data custodians, who are the individuals or entities that implement the security controls and procedures specified by the data owner to protect data while in transit and at rest.
Reference CompTIA Security+ SY0-701 Certification Study Guide, Chapter 2: Data Security, page 511
A company’s Chief Information Security Officer (CISO) wants to enhance the capabilities of the incident response team. The CISO directs the incident response team to deploy a tool that rapidly analyzes host and network data from potentially compromised systems and forwards the data for further review.
Which of the following tools should the incident response team deploy?
- A . NAC
- B . IPS
- C . SIEM
- D . EDR
D
Explanation:
Comprehensive and Detailed In-Depth
An Endpoint Detection and Response (EDR)solution is designed to monitor, detect, and respond to security incidents on endpoints (such as workstations and servers). It collects and analyzes data, detecting suspicious activity and forwarding relevant information for further investigation.
Network Access Control (NAC) (A)enforces network access policies but does not analyze security threats on hosts.
Intrusion Prevention Systems (IPS) (B)detect and block network threats but do not provide deep endpoint analytics.
Security Information and Event Management (SIEM) (C)aggregates logs and provides security analytics but lacks direct endpoint detection and response capabilities.
EDR is the best choice for analyzing and responding to endpoint security incidents.
Which of the following describes the difference between encryption and hashing?
- A . Encryption protects data in transit, while hashing protects data at rest.
- B . Encryption replaces cleartext with ciphertext, while hashing calculates a checksum.
- C . Encryption ensures data integrity, while hashing ensures data confidentiality.
- D . Encryption uses a public-key exchange, while hashing uses a private key.
B
Explanation:
Encryption is a reversible process that transforms cleartext data into ciphertext to protect confidentiality. It uses cryptographic keys to both encrypt and decrypt data, ensuring that only authorized parties can access the original data.
Hashing, on the other hand, is a one-way function that converts data into a fixed-length hash value or checksum. Hashing is primarily used to verify data integrity by detecting changes, since any modification in the input will produce a different hash output. Unlike encryption, hashing cannot be reversed to obtain the original data.
While encryption can protect data both at rest and in transit, hashing does not protect data confidentiality but supports integrity verification. Public-key exchange is a cryptographic mechanism within asymmetric encryption but is unrelated to hashing key usage.
This distinction is thoroughly explained in the Cryptography chapter of the SY0-701 syllabus 【 6:Chapter 7†CompTIA Security+ Study Guide 】 .
