Practice Free SY0-701 Exam Online Questions
Which of the following methods to secure credit card data is best to use when a requirement is to see only the last four numbers on a credit card?
- A . Encryption
- B . Hashing
- C . Masking
- D . Tokenization
C
Explanation:
Masking is a method to secure credit card data that involves replacing some or all of the digits with symbols, such as asterisks, dashes, or Xs, while leaving some of the original digits visible. Masking is best to use when a requirement is to see only the last four numbers on a credit card, as it can prevent unauthorized access to the full card number, while still allowing identification and verification of the cardholder. Masking does not alter the original data, unlike encryption, hashing, or tokenization, which use algorithms to transform the data into different formats.
Reference: CompTIA Security+ Study Guide: Exam SY0-701, 9th Edition, Chapter 2: Compliance and
Operational Security, page 721. CompTIA Security+ Certification Kit: Exam SY0-701, 7th Edition,
Chapter 2: Compliance and Operational Security, page 722.
Which of the following threat actors would most likely target an organization by using a logic bomb within an internally-developed application?
- A . Nation-state
- B . Trusted insider
- C . Organized crime group
- D . Hacktivist
B
Explanation:
A logic bomb is a malicious code segment hidden inside legitimate software that triggers under specific conditions (dates, system states, user actions). Because logic bombs require direct access to source code or the development environment, the most likely attacker is a trusted insider― especially a disgruntled developer or administrator with the ability to modify internal applications.
Security+ SY0-701 emphasizes that insider threats have:
Elevated access
Knowledge of internal systems
Ability to manipulate production code
Motivation driven by revenge, termination, or personal grievances
These factors make insiders uniquely capable of embedding logic bombs into internally-developed applications.
Nation-state actors (A) typically target critical infrastructure or advanced espionage, not internal business apps. Organized crime groups (C) seek financial gain and generally do not have internal code access. Hacktivists (D) focus on ideological disruption, typically through external attacks, not internal code manipulation.
Thus, the threat actor most likely to plant a logic bomb in internal software is B: Trusted insider.
A security analyst reviews domain activity logs and notices the following:
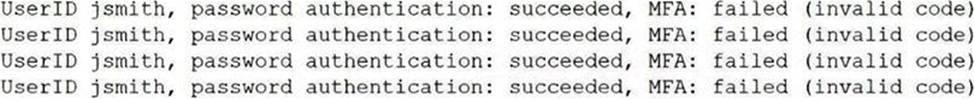
Which of the following is the best explanation for what the security analyst has discovered?
- A . The user jsmith’s account has been locked out.
- B . A keylogger is installed on [smith’s workstation
- C . An attacker is attempting to brute force ismith’s account.
- D . Ransomware has been deployed in the domain.
C
Explanation:
Brute force is a type of attack that tries to guess the password or other credentials of a user account by using a large number of possible combinations. An attacker can use automated tools or scripts to perform a brute force attack and gain unauthorized access to the account. The domain activity logs show that the user ismith has failed to log in 10 times in a row within a short period of time, which is a strong indicator of a brute force attack. The logs also show that the source IP address of the failed logins is different from the usual IP address of ismith, which suggests that the attacker is using a different device or location to launch the attack. The security analyst should take immediate action to block the attacker’s IP address, reset ismith’s password, and notify ismith of the incident.
Reference = CompTIA Security+ Study Guide with over 500 Practice Test Questions: Exam SY0-701, 9th Edition, Chapter 1, page 14. CompTIA Security+ (SY0-701) Certification Exam Objectives, Domain 1.1, page 2. Threat Actors and Attributes C SY0-601 CompTIA Security+: 1.1
Which of the following types of identification methods can be performed on a deployed application during runtime?
- A . Dynamic analysis
- B . Code review
- C . Package monitoring
- D . Bug bounty
A
Explanation:
Dynamic analysis is performed on software during execution to identify vulnerabilities based on how the software behaves in real-world scenarios. It is useful in detecting security issues that only appear when the application is running.
Reference: CompTIA SY0-701 Course Content.
An administrator is installing an SSL certificate on a new system. During testing, errors indicate that the certificate is not trusted. The administrator has verified with the issuing CA and has validated the private key.
Which of the following should the administrator check for next?
- A . If the wildcard certificate is configured
- B . If the certificate signing request is valid
- C . If the root certificate is installed
- D . If the public key is configured
Which of the following describes the reason for using an MDM solution to prevent jailbreaking?
- A . To secure end-of-life devices from incompatible firmware updates
- B . To avoid hypervisor attacks through VM escape
- C . To eliminate buffer overflows at the application layer
- D . To prevent users from changing the OS of mobile devices
D
Explanation:
Mobile Device Management (MDM) solutions can enforce security policies that prevent users from jailbreaking or rooting their devices―that is, from modifying the operating system to remove restrictions and gain unauthorized control. Jailbreaking can introduce significant security risks, so MDM is used to ensure device integrity by preventing users from making these changes.
Reference: CompTIA Security+ SY0-701 Official Study Guide, Domain 3.2: "MDM solutions can be used to prevent users from jailbreaking or rooting devices, maintaining the integrity of the OS."
Exam Objectives 3.2: “Summarize security implications of embedded and specialized systems.”
A systems administrator just purchased multiple network devices.
Which of the following should the systems administrator perform to prevent attackers from accessing the devices by using publicly available information?
- A . Install endpoint protection
- B . Disable ports/protocols
- C . Change default passwords
- D . Remove unnecessary software
C
Explanation:
Changing default passwords is a critical first step after acquiring new devices. Default credentials are widely known and publicly documented, so changing them prevents unauthorized access using this information.
Reference: CompTIA Security+ SY0-701 Official Study Guide, Domain 3.1: "Changing default passwords prevents attackers from exploiting publicly available device information."
Exam Objectives 3.1: “Implement secure network architecture concepts.”
An organization is developing a security program that conveys the responsibilities associated with the general operation of systems and software within the organization.
Which of the following documents would most likely communicate these expectations?
- A . Business continuity plan
- B . Change management procedure
- C . Acceptable use policy
- D . Software development life cycle policy
C
Explanation:
Detailed
A software development life cycle (SDLC) policy outlines responsibilities, best practices, and standards for developing, deploying, and maintaining secure systems and software.
Reference: CompTIA Security+ SY0-701 Study Guide, Domain 5: Security Program Management, Section: "Policies and Standards".
A systems administrator creates a script that validates OS version, patch levels, and installed applications when users log in.
Which of the following examples best describes the purpose of this script?
- A . Resource scaling
- B . Policy enumeration
- C . Baseline enforcement
- D . Guardrails implementation
C
Explanation:
Detailed
Baseline enforcement ensures that all systems adhere to predefined security configurations, such as approved OS versions and patch levels, improving compliance and reducing vulnerabilities.
Reference: CompTIA Security+ SY0-701 Study Guide, Domain 4: Security Operations, Section: "System Baselines and Monitoring".
While a user reviews their email, a host gets infected by malware from an external hard drive plugged into the host. The malware steals all the user’s credentials stored in the browser.
Which of the following training topics should the user review to prevent this situation from reoccurring?
- A . Operational security
- B . Removable media and cables
- C . Password management
- D . Social engineering
B
Explanation:
Detailed This scenario highlights the need for training on the secure use of removable media. Users should learn to avoid using untrusted external storage devices to prevent malware infections.
Reference: CompTIA Security+ SY0-701 Study Guide, Domain 4: Security Operations, Section: "Removable Media Controls and User Awareness Training".
