Practice Free SY0-701 Exam Online Questions
Which of the following best represents an application that does not have an on-premises requirement and is accessible from anywhere?
- A . Pass
- B . Hybrid cloud
- C . Private cloud
- D . IaaS
- E . SaaS
E
Explanation:
Software as a Service (SaaS) represents an application that is hosted in the cloud and accessible via the internet from anywhere, with no requirement for on-premises infrastructure. SaaS applications are managed by a third-party provider, allowing users to access them through a web browser, making them highly scalable and flexible for remote access.
CompTIA Security+ SY0-701 Course Content: Domain 3: Security Architecture, where cloud service models such as SaaS are discussed, highlighting their accessibility and lack of on-premises requirements.
SIMULATION
A security analyst is creating the first draft of a network diagram for the company’s new customer-facing payment application that will be hosted by a third-party cloud service provider.
Explanation:
Step 1: Understand Requirements & Security Principles
Requirements:
Customer-facing payment application (PCI DSS compliance applies)
Hosted on third-party cloud (e.g., AWS)
Must segment public-facing and internal resources
Needs to be scalable and resilient
Must have strong security controls
Step 2: Design the High-Level Network Layout
Core Components:
VPC (Virtual Private Cloud): Isolates your environment from other tenants in the cloud.
Subnets:
Public subnet: For resources that must communicate with the internet.
Private subnet: For internal resources, NOT directly exposed to the internet.
Step 3: Place Resources in Appropriate Subnets
Public Subnet:
Internet-facing Load Balancer (LB): Distributes traffic to application servers.
Web Application Firewall (WAF): Protects against web exploits.
Autoscaling Instances: EC2 (or VM) servers running your web front-end, automatically scaling as traffic grows.
Private Subnet:
Application servers: Back-end logic, not exposed to internet directly.
Database: Sensitive data storage, only accessible by application servers.
Internal Load Balancer: Manages traffic among app servers.
WAF: Can be used internally as well for defense-in-depth.
Step 4: Add Connectivity and Security Controls
Internet Gateway: Allows resources in public subnet to communicate with the internet.
NAT Gateway: Allows outbound internet traffic from private subnet without exposing private IPs. Security Groups: Firewalls at the instance level; allow only necessary traffic (e.g., LB to web server, web server to DB).
Network ACLs: Subnet-level firewalls for additional control.
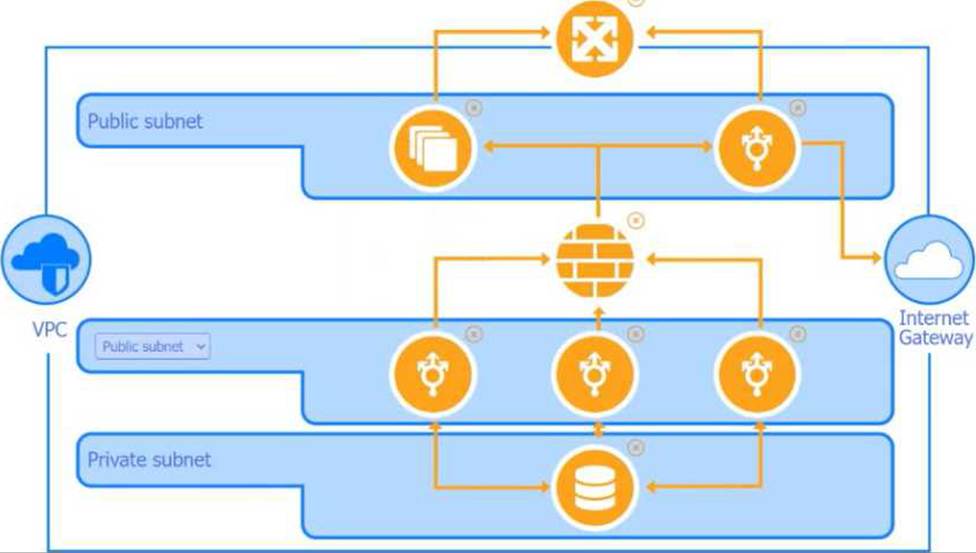
Step 5: Network Diagram Explanation (Based on Your Images)
Public Subnet (Top Layer)
Load Balancer
Accepts HTTPS traffic from customers.
Sends only necessary HTTP/HTTPS to web servers in public subnet.
WAF (Web Application Firewall)
Sits in front of Load Balancer.
Filters malicious requests (SQLi, XSS, etc.).
Autoscaling Group
Multiple web servers for redundancy and scalability.
Placed in public subnet to respond to traffic spikes.
Private Subnet (Bottom Layer)
Application Servers
Receive requests from public subnet’s load balancer.
Not directly exposed to the internet.
Database
Only accessible from application servers, never public.
Security groups restrict all inbound traffic except from app servers.
Internal Load Balancer
Balances requests to application servers.
Step 6: Flow of Data (Step-by-Step)
Client -> Internet Gateway -> WAF -> Load Balancer (Public Subnet):
Customers initiate connections to your app over the internet.
Load Balancer -> Autoscaling Web Servers (Public Subnet): Load balancer routes requests to available web servers. Web Servers -> Application Logic (Private Subnet):
Web servers pass necessary requests to the internal application servers.
App Servers -> Database (Private Subnet):
Application servers query/update customer payment data in the database.
Outbound (NAT Gateway):
App servers may need to access updates or external APIs―use NAT Gateway for secure outbound
connections.
Step 7: Security Best Practices
Security Groups: Only allow necessary ports (e.g., 443 for HTTPS to LB, 3306 for MySQL between app server and DB).
Network ACLs: Add another layer of subnet-level restrictions.
Encryption: Use HTTPS for all external connections, encrypt data at rest and in transit (TLS, disk encryption).
IAM Roles/Policies: Principle of least privilege for accessing resources.
Monitoring/Logging: Enable VPC flow logs, cloud service logs, and application logging.
Patch Management: Automate patching for OS and applications.
Backups: Regular, secure backups of critical data.
Step 8: Compliance Considerations
For payment applications (PCI DSS):
Isolate cardholder data environment (CDE).
Strong access controls (multi-factor authentication, role separation).
Regular vulnerability assessments and penetration testing.
Retain logs for auditing.
Step 9: Draw the Architecture (Summary)
Internet Gateway: Allows inbound/outbound internet access.
Public Subnet: WAF, Load Balancer, Autoscaling group.
Private Subnet: App servers, DB, internal LB.
NAT Gateway: Outbound access for private resources.
Security Groups/ACLs: Control all traffic flows.
Monitoring/Logging: Enabled at all levels.
Bonus: Sample Security Group Rules
Web Server (Public Subnet):
Inbound: 443 (HTTPS) from Internet
Outbound: 80/443 to App Servers
App Server (Private Subnet):
Inbound: 80/443 from Web Servers
Outbound: 3306 (MySQL) to Database
Database (Private Subnet):
Inbound: 3306 from App Servers
Outbound: None (unless replication required)
Reference to Security+ Domains
A systems administrator is auditing all company servers to ensure. They meet the minimum security baseline While auditing a Linux server, the systems administrator observes the /etc/shadow file has permissions beyond the baseline recommendation.
Which of the following commands should the systems administrator use to resolve this issue?
- A . chmod
- B . grep
- C . dd
- D . passwd
A
Explanation:
The chmod command is used to change file permissions on Unix and Linux systems. If the /etc/shadow file has permissions beyond the baseline recommendation, the systems administrator should use chmod to modify the file’s permissions, ensuring it adheres to the security baseline and limits access to authorized users only.
= CompTIA Security+ SY0-701 study materials, focusing on system hardening and file permissions management.
A company discovers suspicious transactions that were entered into the company’s database and attached to a user account that was created as a trap for malicious activity.
Which of the following is the user account an example of?
- A . Honeytoken
- B . Honeynet
- C . Honeypot
- D . Honeyfile
C
Explanation:
A honeypot is a decoy system or account designed to attract attackers and detect malicious activity.
Creating a user account as a trap fits this definition.
Honeytoken (A) is a decoy data element, honeynet (B) is a network of honeypots, and honeyfile (D) is a decoy file.
Honeypots are important tools in Security Operations and incident detection 【 6:Chapter 14†CompTIA Security+ Study Guide 】
An organization has been experiencing issues with deleted network share data and improperly assigned permissions.
Which of the following would best help track and remediate these issues?
- A . DLP
- B . EDR
- C . FIM
- D . ACL
C
Explanation:
File Integrity Monitoring (FIM) is the best tool for detecting unauthorized file deletions, modifications, or improper permission changes within network shares. FIM works by creating cryptographic hashes and baselines for protected files or directories and then continuously monitoring for deviations. Any unauthorized deletion, modification, or permission change triggers alerts.
Security+ SY0-701 identifies FIM as a foundational integrity control used in compliance frameworks (PCI-DSS, HIPAA) and operational security monitoring. Because the organization is experiencing unpredictable changes to shared files and permissions, FIM provides visibility and accountability for who changed what and when.
DLP (A) prevents data leakage but does not detect permission changes. EDR (B) focuses on endpoint threat behavior, not file integrity on network shares. ACLs (D) define permissions but do not track changes or detect unauthorized modifications.
Therefore, C: FIM is the correct choice.
During a penetration test in a hypervisor, the security engineer is able to inject a malicious payload and access the host filesystem.
Which of the following best describes this vulnerability?
- A . VM escape
- B . Cross-site scripting
- C . Malicious update
- D . SQL injection
A
Explanation:
Injecting malicious payloads into a hypervisor and accessing the host system is an example of VM escape, where the isolation between virtual machines and the host breaks down, allowing unauthorized control.
Cross-site scripting (B), malicious updates (C), and SQL injection (D) are unrelated to hypervisor host access.
VM escape is a critical vulnerability unique to virtualized environments described in SY0-701 【 6:Chapter 2†CompTIA Security+ Study Guide 】 .
A security analyst is reviewing the following logs about a suspicious activity alert for a user’s VPN log-ins.
Which of the following malicious activity indicators triggered the alert?
✅ Log Summary:
User logs in from Chicago, IL multiple times, then suddenly a successful login appears from Rome, Italy, followed again by Chicago logins ― all within a short time span.
- A . Impossible travel
- B . Account lockout
- C . Blocked content
- D . Concurrent session usage
A
Explanation:
Impossible travel (A)refers to logins from geographically distant locations within a time period that makes travel between them physically impossible. In this case, a user logging in from Chicago and Rome within a short timeframe triggers this anomaly.
This is a strong indicator of a compromised account or stolen credentials being used elsewhere.
Reference: CompTIA Security+ SY0-701 Objectives, Domain 2.1 C “Indicators of malicious activity:
Impossible travel (geolocation anomalies).”
Which of the following are the best security controls for controlling on-premises access? (Select two.)
- A . Swipe card
- B . Picture ID
- C . Phone authentication application
- D . Biometric scanner
- E . Camera
- F . Memorable
A,D
Explanation:
Detailed Swipe cards and biometric scanners are commonly used to control on-premises access due to their reliability and ability to restrict unauthorized entry. Swipe cards provide physical access control, while biometric scanners ensure identity verification.
Reference: CompTIA Security+ SY0-701 Study Guide, Domain 1: General Security Concepts, Section: "Physical Security Controls".
Which of the following is die most important security concern when using legacy systems to provide production service?
- A . Instability
- B . Lack of vendor support
- C . Loss of availability
- D . Use of insecure protocols
B
Explanation:
The most important security concern when using legacy systems is the lack of vendor support. Without support from the vendor, systems may not receive critical security patches and updates, leaving them vulnerable to exploitation. This lack of support can result in increased risk of security breaches, as vulnerabilities discovered in the software may never be addressed.
= CompTIA Security+ SY0-701 study materials, particularly in the context of risk management and the challenges posed by legacy systems.
A forensic engineer determines that the root cause of a compromise is a SQL injection attack.
Which of the following should the engineer review to identify the command used by the threat actor?
- A . Metadata
- B . Application log
- C . System log
- D . Netflow log
B
Explanation:
To identify the exact command or input used during a SQL injection attack, the application log (B)is the most relevant. It records inputs, errors, and processing activities within the application layer. Under Domain 2.1, CompTIA emphasizes reviewing application logs to detect indicators of malicious activity, including web application attacks like SQL injection.
Reference: CompTIA Security+ SY0-701 Objectives, Domain 2.1 C “Indicators of malicious activity:
SQL injection; review application logs.”
