Practice Free SC-900 Exam Online Questions
Question #61
Which three statements accurately describe the guiding principles of Zero Trust? Each correct answer presents a complete solution. NOTE: Each correct selection is worth one point.
- A . Define the perimeter by physical locations.
- B . Use identity as the primary security boundary.
- C . Always verity the permissions of a user explicitly.
- D . Always assume that the user system can be breached.
- E . Use the network as the primary security boundary.
Correct Answer: BCD
BCD
Explanation:
Reference: https://docs.microsoft.com/en-us/security/zero-trust/
BCD
Explanation:
Reference: https://docs.microsoft.com/en-us/security/zero-trust/
Question #62
Which Azure Active Directory (Azure AD) feature can you use to restrict Microsoft Intune-managed devices from accessing corporate resources?
- A . network security groups (NSGs)
- B . Azure AD Privileged Identity Management (PIM)
- C . conditional access policies
- D . resource locks
Correct Answer: B
Question #63
HOTSPOT
For each of the following statements, select Yes if the statement is true. Otherwise, select No. NOTE: Each correct selection is worth one point.
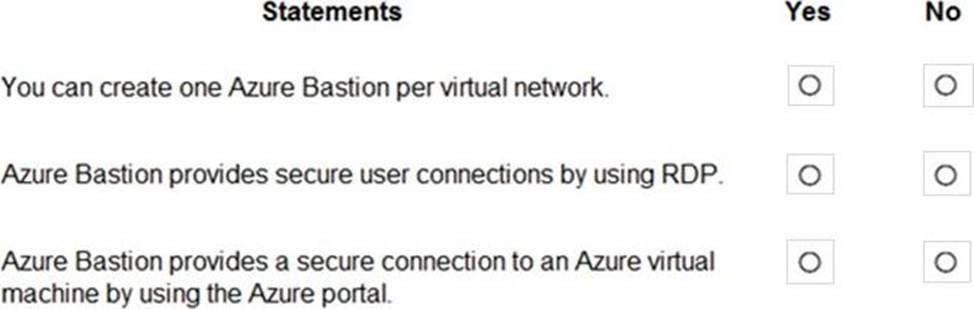
Correct Answer:
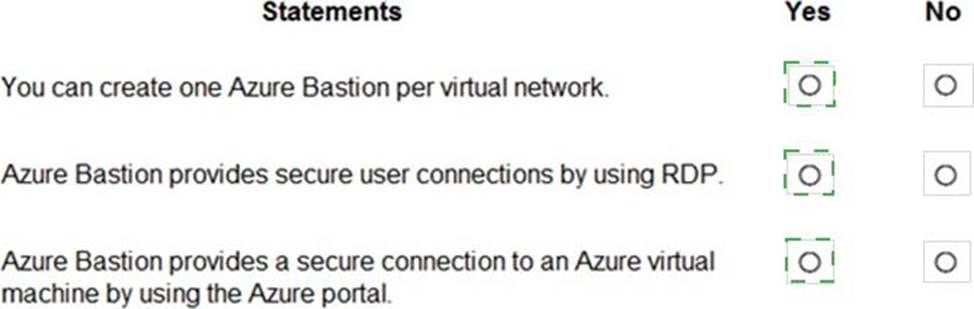
Explanation:
Reference:
https://docs.microsoft.com/en-us/azure/bastion/bastion-overview
https://docs.microsoft.com/en-us/azure/bastion/tutorial-create-host-portal
Question #64
What can be created in Active Directory Domain Services (AD DS)?
- A . line-of-business (106) applications that require modem authentication
- B . mob devices
- C . computer accounts
- D . software as a service (SaaS) applications that require modem authentication
Correct Answer: C
