Practice Free SC-900 Exam Online Questions
HOTSPOT
Select the answer that correctly completes the sentence.


Explanation:
In Microsoft’s security portfolio, Microsoft Defender for Cloud is the service that provides cloud workload protection for Azure and hybrid cloud resources. Microsoft describes it as a “cloud-native application protection platform (CNAPP) that helps strengthen the security posture of your cloud resources and protect workloads across multicloud and hybrid environments.” The service delivers Cloud Security Posture Management (CSPM) and Cloud Workload Protection (CWP) by continuously assessing configurations and protecting workloads such as virtual machines, containers, databases, and storage. Documentation further states that Defender for Cloud “provides threat protection for workloads running in Azure, on-premises, and in other clouds,” giving a single pane to harden resources, detect active threats, and remediate.
By contrast, Azure Monitor focuses on telemetry and observability; the Microsoft cloud security benchmark is a set of prescriptive best practices; and Microsoft Secure Score is an aggregate metric reflecting security posture. None of those deliver the workload protection and active defense capabilities (e.g., recommendations, hardening, and threat detection for servers, containers, and PaaS services) that Defender for Cloud offers. Therefore, the sentence correctly completes as: Microsoft Defender for Cloud provides cloud workload protection for Azure and hybrid cloud resources.
What can you use to provide threat detection for Azure SQL Managed Instance?
- A . Microsoft Secure Score
- B . application security groups
- C . Microsoft Defender for Cloud
- D . Azure Bastion
C
Explanation:
For Azure data services such as Azure SQL Managed Instance, Microsoft provides threat detection and protection through Microsoft Defender for Cloud (via Microsoft Defender for SQL). Microsoft documentation states that Defender for Cloud “provides advanced threat protection for your SQL resources,” including Azure SQL Database and Azure SQL Managed Instance, by “continuously monitoring for anomalous activities and potential SQL injection, brute force, and exploitation attempts.” When enabled, the plan “generates security alerts when suspicious activities are detected,” and these alerts can be surfaced in Defender for Cloud, forwarded to Microsoft Sentinel, or integrated with workflows for response. Microsoft Secure Score is a security posture metric, application security groups are for network segmentation in Azure, and Azure Bastion provides secure RDP/SSH over TLS―none of these deliver database-specific threat detection. Therefore, to provide threat detection for Azure SQL Managed Instance, you use Microsoft Defender for Cloud (Defender for SQL).
HOTSPOT
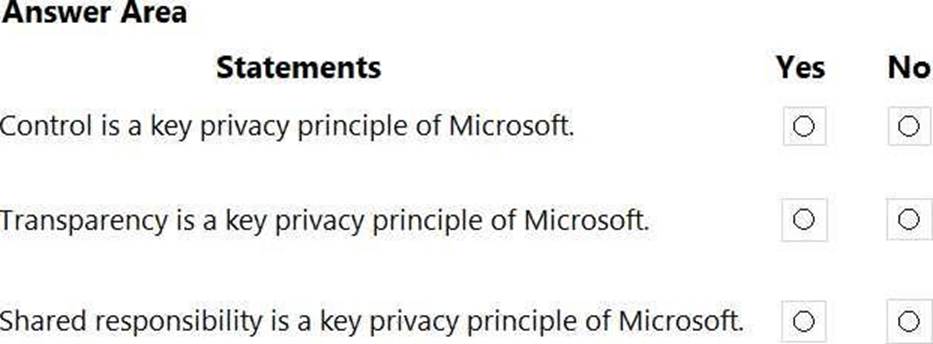
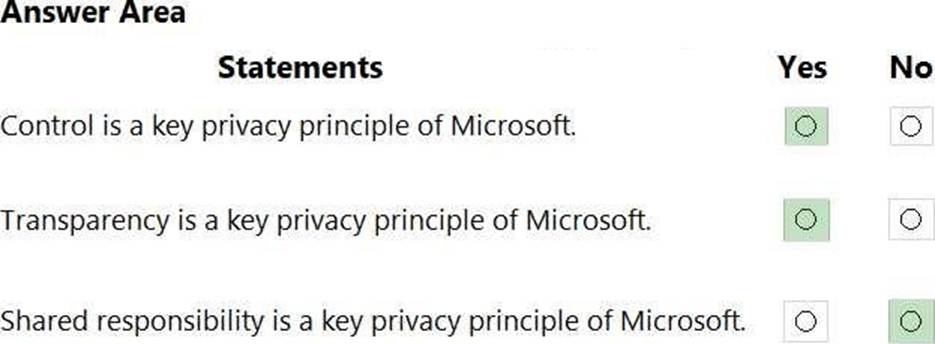
For each of the following statements, select Yes if the statement is true. Otherwise, select No. NOTE: Each correct selection is worth one point.
Explanation:
Microsoft sets out clear privacy principles for Microsoft 365 and Microsoft cloud services. In Microsoft’s privacy commitments, Microsoft states that customers control their data: “You control your data.” Microsoft also pledges transparency about data practices: “We are transparent about data collection and use.” These two commitments are among the core privacy principles articulated across Microsoft 365 privacy and Microsoft Purview documentation, which emphasize customer choice, clear explanations of data processing, and admin capabilities to access, export, and delete data. Additional Microsoft privacy principles often listed alongside these include security of your data, strong legal protections, no content-based targeting, and benefits to you, but the key point for this question is that Control and Transparency are explicitly called out as privacy principles.
By contrast, shared responsibility is not a privacy principle; it is a cloud security model used in Azure/Microsoft cloud guidance. That model explains that security is a shared responsibility between Microsoft (for the cloud infrastructure) and the customer (for their data, identities, endpoints, and configurations). It describes how duties are divided for protecting services and workloads, not a privacy promise to end users. Therefore, the correct selections are Yes for Control and Transparency, and No for Shared responsibility.
HOTSPOT
Select the answer that correctly completes the sentence.
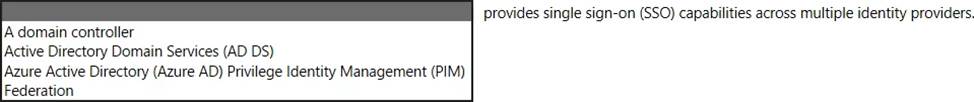
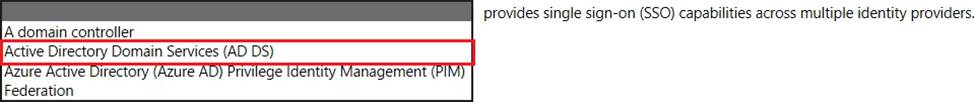
HOTSPOT
Select the answer that correctly completes the sentence.
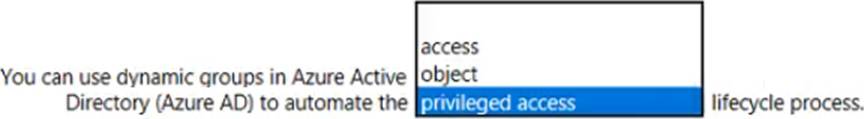
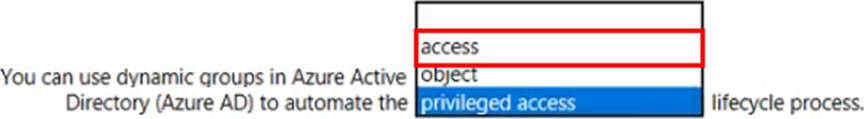
Explanation:
access
In Microsoft Entra ID (formerly Azure AD), dynamic groups are a key feature used to automate the access lifecycle for users and devices. SCI learning material on identity governance explains that organizations can automate the access lifecycle process through technologies such as dynamic groups, alongside automated user provisioning. These resources describe the access lifecycle as managing a user’s access to resources from the moment they join the organization, through role or department changes, until they leave. Dynamic groups help with this by using attribute-based rules (for example, department, job title, location, or device platform) to automatically add or remove identities from groups as their attributes change.
Because group membership typically controls access to applications, SharePoint sites, Teams, and licenses, this automatic membership update keeps access aligned with the user’s current role without manual intervention. When a user changes departments, the dynamic rules reevaluate and move them into the appropriate groups, granting new access and removing old access as required. This is exactly what Microsoft refers to as automating the access lifecycle.
The other options do not match the terminology used in SCI content: “object lifecycle” is not the term used in Entra identity governance, and “privileged access” lifecycle is handled specifically by Privileged Identity Management (PIM), not by dynamic groups. Therefore, the sentence is correctly completed with access.
HOTSPOT
For each of the following statements, select Yes if the statement is true. Otherwise, select No. NOTE: Each correct selection is worth one point.
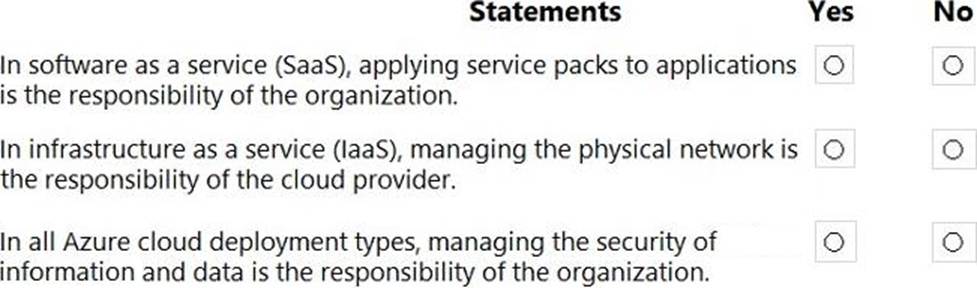
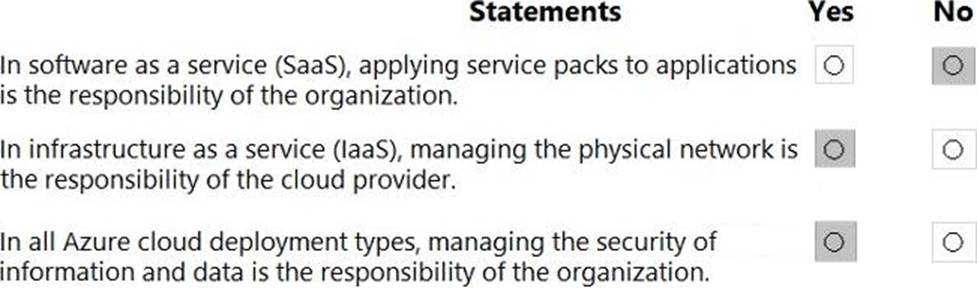
Explanation:
Microsoft’s shared-responsibility model states that the cloud provider secures the cloud, while the customer secures what they put in the cloud. The Azure Security documentation explains: “Regardless of the type of deployment, you always retain responsibility for your data, endpoints, accounts, and access management.” This applies to IaaS, PaaS, and SaaS, so statement 3 is Yes because the organization is always accountable for the security of information and data.
For SaaS, Microsoft describes that customers “don’t manage or control the underlying cloud infrastructure―including network, servers, operating systems, or even individual application capabilities” and that the provider handles service maintenance and updates. In SaaS, tasks like patching or applying service packs to the application code are owned by the service provider, while the customer focuses on data, identity, and access. Therefore, statement 1 is No.
For IaaS, Microsoft notes the provider manages the physical estate: “Microsoft is responsible for the physical hosts, network, and datacenter facilities,” while the customer configures and secures the guest OS, applications, and network controls within their subscription. Thus, managing the physical network is the cloud provider’s duty, making statement 2 Yes.
These SCI principles are foundational to Microsoft Learn/Docs guidance on Azure’s shared responsibility: provider―“security OF the cloud”; customer―“security IN the cloud,” with data protection always remaining the customer’s responsibility.
HOTSPOT
For each of the following statements, select Yes if the statement is true. Otherwise, select No. NOTE: Each correct selection is worth one point.
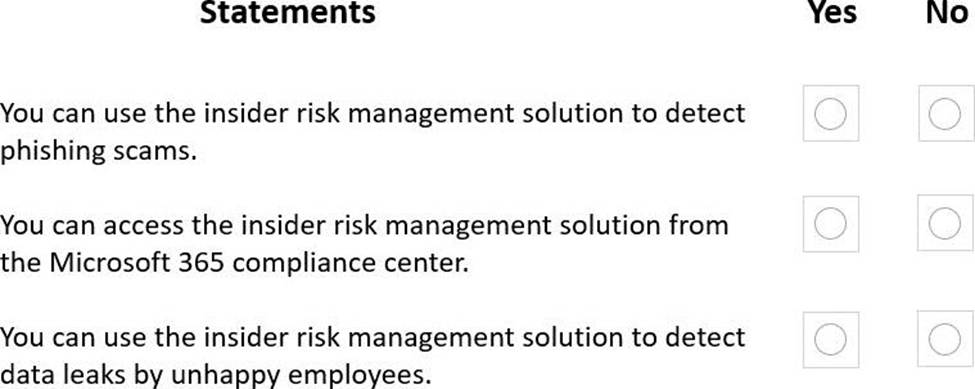
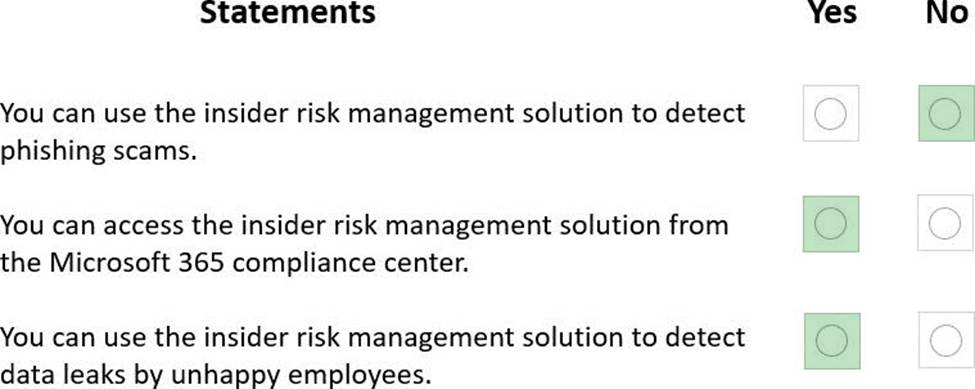
Explanation:
Box 1: Yes
Phishing scams are external threats.
Box 2: Yes
Insider risk management is a compliance solution in Microsoft 365.
Box 3: No
Insider risk management helps minimize internal risks from users.
These include:
✑ Leaks of sensitive data and data spillage
✑ Confidentiality violations
✑ Intellectual property (IP) theft
✑ Fraud
✑ Insider trading
✑ Regulatory compliance violations
Microsoft Purview Insider Risk Management is designed to identify, investigate, and act on risky activities by internal users―for example data exfiltration, data theft, policy violations, and user sentiments/signals that may indicate insider risk. SCI documentation explains that Insider Risk policies analyze signals such as file downloads, copying to USB, sharing to personal cloud, printing, or anomalous activity following events like performance warnings or resignation notices. Because it focuses on insider behaviors, it is not used to detect external threat vectors like phishing scams; those are addressed by Microsoft Defender for Office 365 and related anti-phishing protections― hence statement 1 is No. The solution is accessed in the Microsoft Purview (formerly Microsoft 365) compliance center under Insider risk management, where admins configure policies, alerts, and workflows―so statement 2 is Yes. Finally, its core purpose includes detecting and investigating potential data leaks by disgruntled or departing employees, using built-in policy templates (e.g., Data theft by departing employee, Data leaks), making statement 3 Yes.
HOTSPOT
For each of the following statements, select Yes if the statement is true. Otherwise, select No. NOTE: Each correct selection is worth one point.
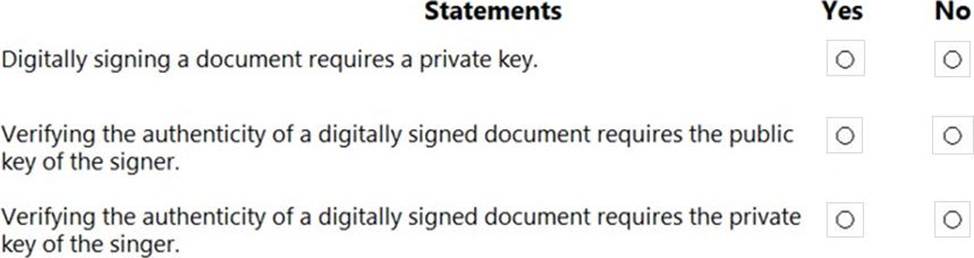
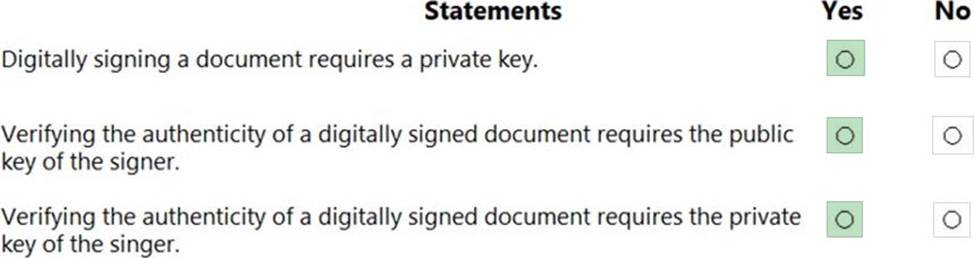
Explanation:
Box 1: Yes
A certificate is required that provides a private and a public key.
Box 2: Yes
The public key is used to validate the private key that is associated with a digital signature.
Box 3: Yes
Microsoft’s security and compliance learning content explains that digital signatures are built on public key (asymmetric) cryptography. In this model, each identity has a key pair: a private key that is kept secret and a public key that can be shared. The signing operation is performed with the private key to produce a signature bound to the content and the signer’s identity. Verification is then performed by anyone who has access to the corresponding public key, which mathematically validates the signature and confirms both integrity (the content wasn’t altered) and authenticity (it was signed by the holder of the private key). SCI materials (covering Microsoft Purview Information Protection, Azure Key Vault/PKI concepts, and identity fundamentals) emphasize that the private key must never be disclosed or required for verification; only the public key is used to validate signatures and certificates. This is the same principle used across Microsoft 365 for certificate-based trust, code signing, and document signing: sign with the private key; verify with the public key. Therefore, statements one and two are true, and the statement claiming verification requires the private key is false.
You plan to implement a security strategy and place multiple layers of defense throughout a network infrastructure.
Which security methodology does this represent?
- A . threat modeling
- B . identity as the security perimeter
- C . defense in depth
- D . the shared responsibility model
C
Explanation:
Microsoft defines defense in depth as a security strategy that uses multiple, reinforcing layers of protection to reduce the chance that a single failure leads to compromise. In Microsoft’s security guidance, defense in depth is described as employing “a series of mechanisms across multiple layers” to protect identities, endpoints, applications, data, and the network. The model spans layers such as identity, perimeter, network, compute, application, and data, with controls at each layer designed to detect, prevent, and contain attacks. Typical Azure/Microsoft 365 implementations include identity protections (MFA, Conditional Access), network controls (Azure Firewall, NSGs), perimeter filtering (WAF, DDoS Protection), endpoint safeguards (Defender for Endpoint), application security (code and runtime controls), and data protection (encryption, DLP, Purview Information Protection). By “placing multiple layers of defense throughout a network infrastructure,” an organization limits blast radius and increases resilience if one layer is bypassed. This contrasts with threat modeling (a design-time analysis technique), identity as the security perimeter (a principle of Zero Trust), and the shared responsibility model (a cloud governance concept). The scenario in the question precisely matches Microsoft’s defense in depth methodology.
HOTSPOT
Select the answer that correctly completes the sentence.
Explanation:
In Azure networking, each Network Security Group (NSG) is created with a built-in set of default security rules. Microsoft’s documentation for NSGs explains: “Azure creates several default security rules within each network security group. You can’t remove the default security rules, but you can override them by creating rules with a higher priority.” The rule processing model is priority-based: “Security rules are processed in priority order, with lower numbers processed before higher numbers. Once a rule matches traffic, processing stops.” Because the defaults have relatively low precedence (high priority numbers), an administrator can create an explicit allow or deny rule with a lower priority number to supersede the default behavior.
This is why the correct completion is override rather than copy or delete. You cannot delete the default rules; they remain present to provide baseline behavior (such as denying inbound traffic from the internet by default and allowing virtual network traffic). Instead, you override the defaults by adding your own NSG rules―using lower priority numbers―to achieve the desired access control outcome while preserving Azure’s baseline protections and evaluation logic.
