Practice Free SC-200 Exam Online Questions
You have a Microsoft Sentinel workspace that contains a custom workbook named Workbook1.
You need to create a visual based on the SecuntyEvent table.
The solution must meet the following requirements:
• Identify the number of security events ingested during the past week.
• Display the count of events by day in a timechart
What should you add to Workbook1?
- A . a query
- B . a metric
- C . a group
- D . links or tabs
You have a Microsoft Sentinel workspace that has user and Entity Behavior Analytics (UEBA) enabled for Signin Logs.
You need to ensure that failed interactive sign-ins are detected.
The solution must minimize administrative effort.
What should you use?
- A . a scheduled alert query
- B . a UEBA activity template
- C . the Activity Log data connector
- D . a hunting query
The issue for which team can be resolved by using Microsoft Defender for Office 365?
- A . executive
- B . marketing
- C . security
- D . sales
B
Explanation:
Reference: https://docs.microsoft.com/en-us/microsoft-365/security/office-365-security/atp-for-spo-odb-and-teams?view=o365-worldwide
HOTSPOT
You have an Azure subscription named Sub1 that uses Microsoft Defender for Cloud.
You have an Azure DevOps organization named AzDO1.
You need to integrate Sub! and AzDO1.
The solution must meet the following requirements:
• Detect secrets exposed in pipelines by using Defender for Cloud.
• Minimize administrative effort.


HOTSPOT
You manage the security posture of an Azure subscription that contains two virtual machines name vm1 and vm2.
The secure score in Azure Security Center is shown in the Security Center exhibit. (Click the Security Center tab.)
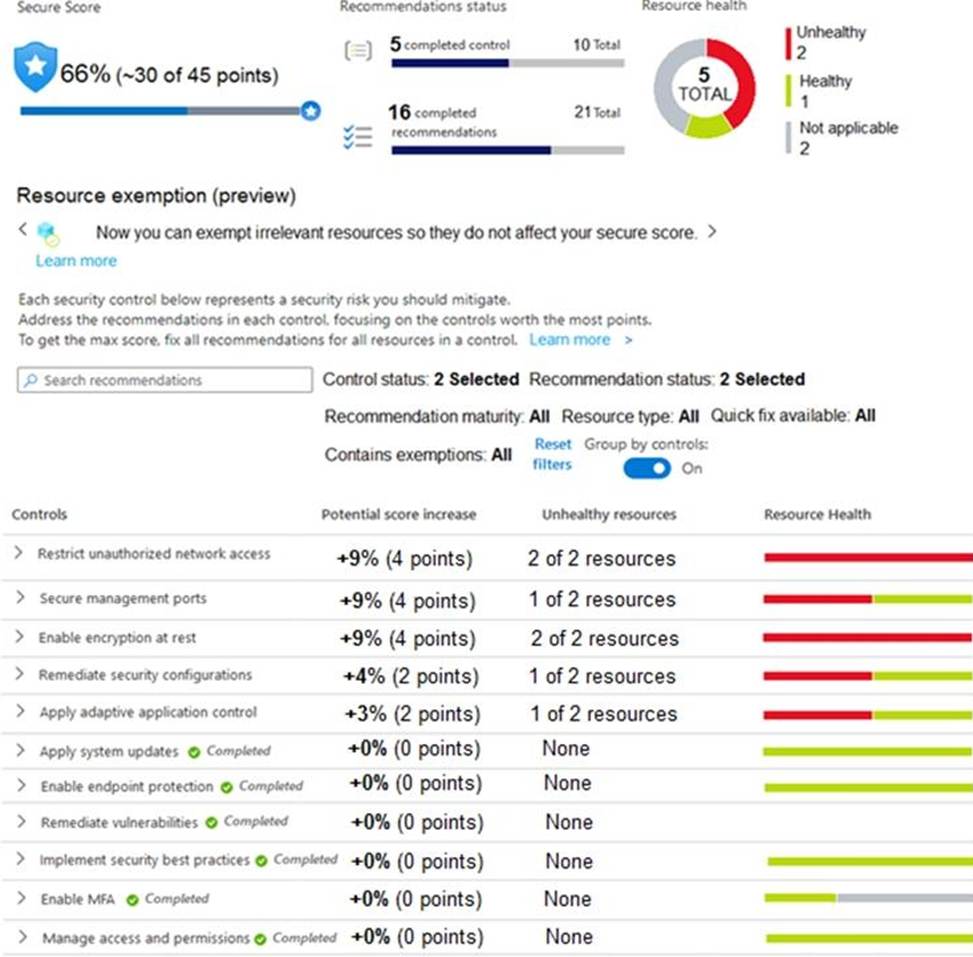
Azure Policy assignments are configured as shown in the Policies exhibit. (Click the Policies tab.)
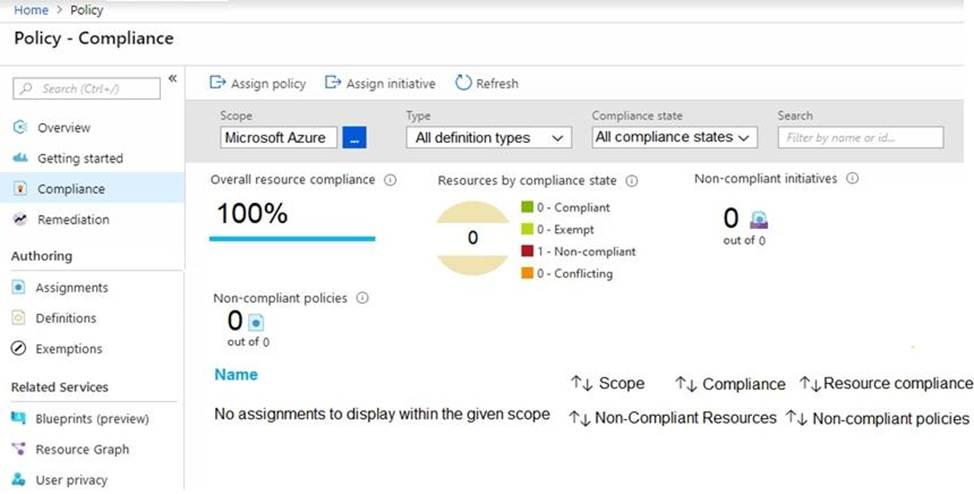
For each of the following statements, select Yes if the statement is true. Otherwise, select No. NOTE: Each correct selection is worth one point.


Explanation:
Reference:
https://techcommunity.microsoft.com/t5/azure-security-center/security-control-restrict-unauthorized-network-access/ba-p/1593833
https://techcommunity.microsoft.com/t5/azure-security-center/security-control-secure-management-ports/ba-p/1505770
HOTSPOT
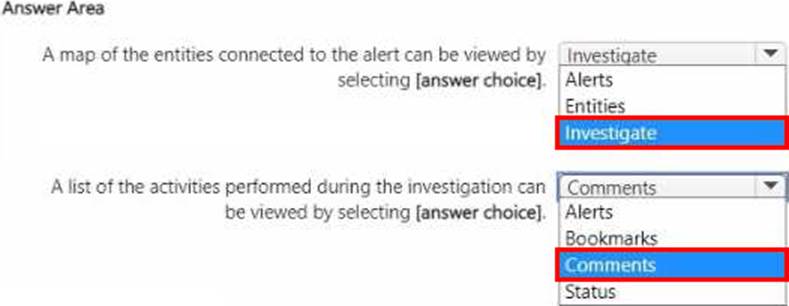
You have a Microsoft Sentinel workspace.
A Microsoft Sentinel incident is generated as shown in the following exhibit.

Use the drop-down menus to select the answer choice that completes each statement based on the information presented in [the graphic. NOTE: Each correct selection is worth one point.

You have an Azure subscription that contains a Log Analytics workspace.
You need to enable just-in-time (JIT) VM access and network detections for Azure resources.
Where should you enable Azure Defender?
- A . at the subscription level
- B . at the workspace level
- C . at the resource level
A
Explanation:
Reference: https://docs.microsoft.com/en-us/azure/security-center/enable-azure-defender
You need to receive a security alert when a user attempts to sign in from a location that was never used by the other users in your organization to sign in.
Which anomaly detection policy should you use?
- A . Impossible travel
- B . Activity from anonymous IP addresses
- C . Activity from infrequent country
- D . Malware detection
C
Explanation:
Activity from a country/region that could indicate malicious activity. This policy profiles your environment and triggers alerts when activity is detected from a location that was not recently or was never visited by any user in the organization. Activity from the same user in different locations within a time period that is shorter than the expected travel time between the two locations. This can indicate a credential breach, however, it’s also possible that the user’s actual location is masked, for example, by using a VPN.
Reference: https://docs.microsoft.com/en-us/cloud-app-security/anomaly-detection-policy
HOTSPOT
You need to create a query for a workbook.
The query must meet the following requirements:
✑ List all incidents by incident number.
✑ Only include the most recent log for each incident.
How should you complete the query? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.


Explanation:
Reference: https://www.drware.com/whats-new-soc-operational-metrics-now-available-in-sentinel/
HOTSPOT
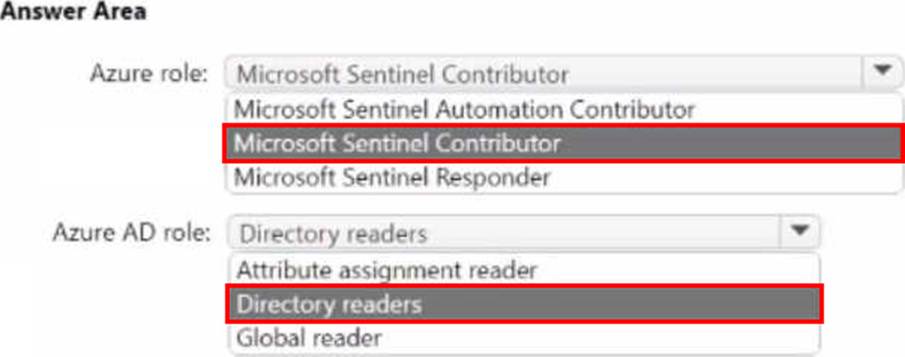
You have an Azure subscription that contains a quest user named User1 and a Microsoft Sentinel
workspace named workspace1.
You need to ensure that User1 can triage Microsoft Sentinel incidents in workspace1. The solution must use the principle of least privilege.
Which roles should you assign to User1? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.