Practice Free SC-200 Exam Online Questions
Your company uses Azure Sentinel to manage alerts from more than 10,000 IoT devices.
A security manager at the company reports that tracking security threats is increasingly difficult due to the large number of incidents.
You need to recommend a solution to provide a custom visualization to simplify the investigation of threats and to infer threats by using machine learning.
What should you include in the recommendation?
- A . built-in queries
- B . livestream
- C . notebooks
- D . bookmarks
C
Explanation:
Reference: https://docs.microsoft.com/en-us/azure/sentinel/notebooks
DRAG DROP
You need to configure DC1 to meet the business requirements.
Which four actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.

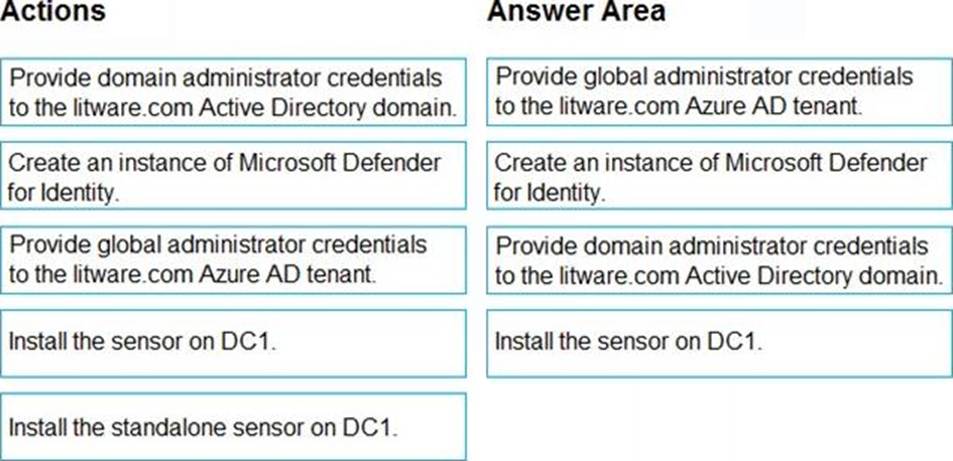
Explanation:
Step 1: log in to https://portal.atp.azure.com as a global admin
Step 2: Create the instance
Step 3. Connect the instance to Active Directory
Step 4. Download and install the sensor.
Reference:
https://docs.microsoft.com/en-us/defender-for-identity/install-step1
https://docs.microsoft.com/en-us/defender-for-identity/install-step4
You have a Microsoft 365 subscription that uses Microsoft Defender for Endpoint and contains a user named user1 and a Microsoft 365 group named Group1. All users are assigned a Defender for Endpoint Plan 1 license.
You enable Microsoft Defender XDR Unified role-based access control (RBAC) for Endpoints & Vulnerability Management.
You need to ensure that User1 can configure alerts that will send email notifications to Group1. The solution must follow the principle of least privilege.
Which permissions should you assign to User1?
- A . Alerts investigation
- B . Manage security settings
- C . Defender Vulnerability Management -Remediation handling
- D . Live response capabilities: Basic
You use Microsoft Sentinel.
You need to receive an alert in near real-time whenever Azure Storage account keys are enumerated.
Which two actions should you perform? Each correct answer presents part of the solution. NOTE: Each correct selection is worth one point
- A . Create a bookmark.
- B . Create an analytics rule.
- C . Create a livestream.
- D . Create a hunting query.
- E . Add a data connector.
You have a Microsoft 365 subscription that uses Microsoft Defender for Endpoint Plan 2 and contains 500 Windows devices.
As part of an incident investigation, you identify the following suspected malware files:
• sys
• pdf
• docx
• xlsx
You need to create indicator hashes to block users from downloading the files to the devices.
Which files can you block by using the indicator hashes?
- A . File1.sysonly
- B . File1.sysand File3.docxonly
- C . File1.sys. File3.docx, and File4jclsx only
- D . File2.pdf. File3.docxr and File4.xlsx only
- E . File1.sys, File2.pdf, File3.dooc, and File4.xlsx
HOTSPOT
You need to configure the Azure Sentinel integration to meet the Azure Sentinel requirements.
What should you do? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
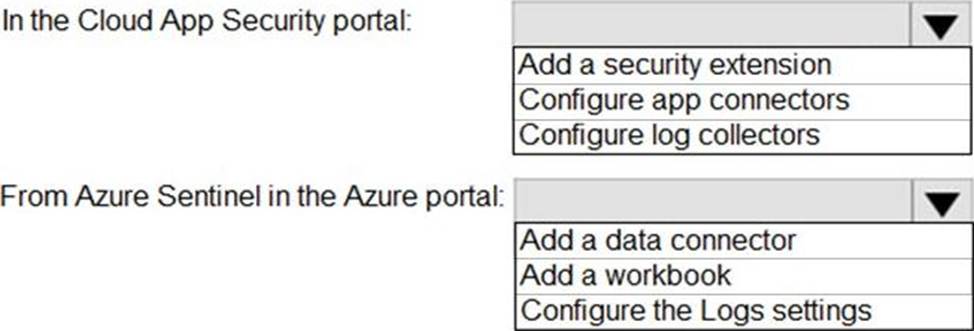

Explanation:
Reference: https://docs.microsoft.com/en-us/cloud-app-security/siem-sentinel
You have a Microsoft 365 subscription that uses Microsoft Defender for Endpoint Plan 2 and contains 500 Windows devices. You plan to create a Microsoft Defender XDR custom deception rule. You need to ensure that the rule will be applied to only 10 specific devices.
What should you do first?
- A . Add the IP address of each device to the list of decoy accounts and hosts of the rule.
- B . Add the devices to a group.
- C . Add custom lures to the rule.
- D . Assign a tag to the devices
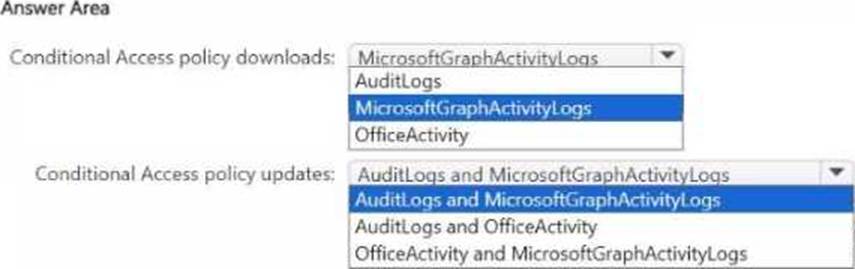
HOTSPOT
You have a Microsoft 365 E5 subscription that uses Microsoft Defender XDR.
You have a Microsoft Sentinel workspace.
Microsoft Sentinel connectors are configured as shown in the following table.
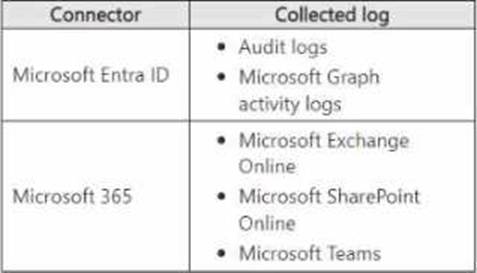
You use Microsoft Sentinel to investigate suspicious Microsoft Graph API activity related to Conditional Access policies.
You need to search for the following activities:
• Downloads of the Conditional Access policies by using PowerShell
• Updates to the Conditional Access policies by using the Microsoft Entra admin center
Which tables should you query for each activity? lo answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.

HOTSPOT
You have an Azure subscription that contains a Microsoft Sentinel workspace named WS1.
You need to ensure that the incidents in WS1 include a list of actions that must be performed.
The solution must meet the following requirements:
• Ensure that you can build a tailored list of actions for each type of incident.
• Minimize administrative effort.
What should you do? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.


A security administrator receives email alerts from Azure Defender for activities such as potential malware uploaded to a storage account and potential successful brute force attacks.
The security administrator does NOT receive email alerts for activities such as antimalware action failed and suspicious network activity. The alerts appear in Azure Security Center.
You need to ensure that the security administrator receives email alerts for all the activities.
What should you configure in the Security Center settings?
- A . the severity level of email notifications
- B . a cloud connector
- C . the Azure Defender plans
- D . the integration settings for Threat detection
A
Explanation:
Reference: https://techcommunity.microsoft.com/t5/microsoft-365-defender/get-email-notifications-on-new-incidents-from-microsoft-365/ba-p/2012518
