Practice Free SC-200 Exam Online Questions
You have a Microsoft 365 B5 subscription that contains a user named User1. The subscription uses Microsoft 365 Copilot for Security. Copilot for Security uses the Sentinel plugin. User1 is assigned the Copilot Contributor role.
During an investigation, User1 submits a prompt and receives a notification that Copilot for Security cannot respond to requests because the security compute unit (SCU) usage is nearing the provisioned capacity limit.
You need to ensure that User1 can use Copilot for Security to generate a successful response.
What should User1 do?
- A . Open a second Copilot for Security session and submit the prompt.
- B . Wait one hour and resubmit the prompt.
- C . Run the Microsoft Sentinel Optimization Workbook.
- D . Update the provisioned SCUs.
You need to assign a role-based access control (RBAC) role to admin1 to meet the Azure Sentinel requirements and the business requirements.
Which role should you assign?
- A . Automation Operator
- B . Automation Runbook Operator
- C . Azure Sentinel Contributor
- D . Logic App Contributor
C
Explanation:
Reference: https://docs.microsoft.com/en-us/azure/sentinel/roles
HOTSPOT
You deploy Azure Sentinel.
You need to implement connectors in Azure Sentinel to monitor Microsoft Teams and Linux virtual machines in Azure. The solution must minimize administrative effort.
Which data connector type should you use for each workload? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.


Explanation:
Reference:
https://docs.microsoft.com/en-us/azure/sentinel/connect-office-365
https://docs.microsoft.com/en-us/azure/sentinel/connect-syslog
You have an Azure subscription that uses resource type for Cloud.
You need to filter the security alerts view to show the following alerts:
• Unusual user accessed a key vault
• Log on from an unusual location
• Impossible travel activity
Which severity should you use?
- A . Informational
- B . Low
- C . Medium
- D . High
Your company has an on-premises network that uses Microsoft Defender for Identity.
The Microsoft Secure Score for the company includes a security assessment associated with unsecure Kerberos delegation.
You need remediate the security risk.
What should you do?
- A . Install the Local Administrator Password Solution (LAPS) extension on the computers listed as exposed entities.
- B . Modify the properties of the computer objects listed as exposed entities.
- C . Disable legacy protocols on the computers listed as exposed entities.
- D . Enforce LDAP signing on the computers listed as exposed entities.
B
Explanation:
To remediate the security risk associated with unsecure Kerberos delegation, you should modify the properties of the computer objects listed as exposed entities. Specifically, you should set the
Kerberos delegation settings to either ‘Trust this computer for delegation to any service’ or ‘Trust this computer for delegation to specified services only’. This will ensure that the computer is not allowed to use Kerberos delegation to access other computers on the network.
Reference: https://docs.microsoft.com/en-us/windows/security/identity-protection/microsoft-defender-for-identity/configure-kerberos-delegation
You have a Microsoft Sentinel workspace named SW1.
In SW1, you investigate an incident that is associated with the following entities:
• Host
• IP address
• User account
• Malware name
Which entity can be labeled as an indicator of compromise (loC) directly from the incident s page?
- A . malware name
- B . host
- C . user account
- D . IP address
DRAG DROP
A company wants to analyze by using Microsoft 365 Apps.
You need to describe the connected experiences the company can use.
Which connected experiences should you describe? To answer, drag the appropriate connected experiences to the correct description. Each connected experience may be used once, more than once, or not at all. You may need to drag the split between panes or scroll to view content. NOTE: Each correct selection is worth one point.


DRAG DROP
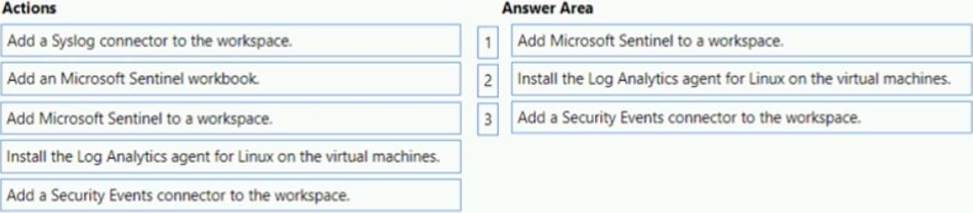
You have an Azure subscription that contains 100 Linux virtual machines.
You need to configure Microsoft Sentinel to collect event logs from the virtual machines.
Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.

You create an Azure subscription.
You enable Azure Defender for the subscription.
You need to use Azure Defender to protect on-premises computers.
What should you do on the on-premises computers?
- A . Install the Log Analytics agent.
- B . Install the Dependency agent.
- C . Configure the Hybrid Runbook Worker role.
- D . Install the Connected Machine agent.
A
Explanation:
Security Center collects data from your Azure virtual machines (VMs), virtual machine scale sets, IaaS containers, and non-Azure (including on-premises) machines to monitor for security vulnerabilities and threats.
Data is collected using:
The Log Analytics agent, which reads various security-related configurations and event logs from the machine and copies the data to your workspace for analysis. Examples of such data are: operating system type and version, operating system logs (Windows event logs), running processes, machine name, IP addresses, and logged in user.
Security extensions, such as the Azure Policy Add-on for Kubernetes, which can also provide data to Security Center regarding specialized resource types.
Reference: https://docs.microsoft.com/en-us/azure/security-center/security-center-enable-data-collection
You create a hunting query in Azure Sentinel.
You need to receive a notification in the Azure portal as soon as the hunting query detects a match on the query. The solution must minimize effort.
What should you use?
- A . a playbook
- B . a notebook
- C . a livestream
- D . a bookmark
C
Explanation:
Use livestream to run a specific query constantly, presenting results as they come in.
Reference: https://docs.microsoft.com/en-us/azure/sentinel/hunting
