Practice Free SC-200 Exam Online Questions
DRAG DROP
You have the resources shown in the following table.
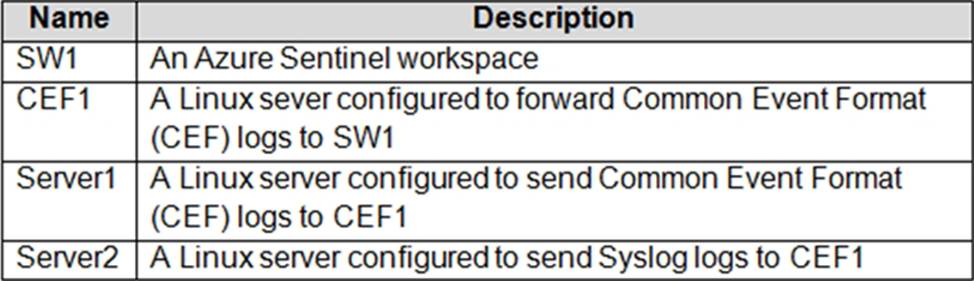
You need to prevent duplicate events from occurring in SW1.
What should you use for each action? To answer, drag the appropriate resources to the correct actions. Each resource may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content. NOTE: Each correct selection is worth one point.


Explanation:
Reference: https://docs.microsoft.com/en-us/azure/sentinel/connect-log-forwarder?tabs=rsyslog
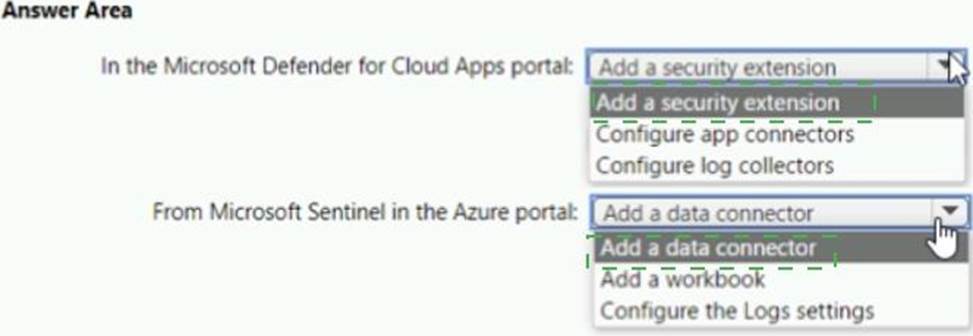
HOTSPOT
You need to configure the Microsoft Sentinel integration to meet the Microsoft Sentinel requirements.
What should you do? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.

You need to ensure that you can run hunting queries to meet the Microsoft Sentinel requirements.
Which type of workspace should you create?
- A . Azure Synapse AnarytKS
- B . AzureDalabricks
- C . Azure Machine Learning
- D . LogAnalytics
You have an existing Azure logic app that is used to block Azure Active Directory (Azure AD) users.
The logic app is triggered manually.
You deploy Azure Sentinel.
You need to use the existing logic app as a playbook in Azure Sentinel.
What should you do first?
- A . And a new scheduled query rule.
- B . Add a data connector to Azure Sentinel.
- C . Configure a custom Threat Intelligence connector in Azure Sentinel.
- D . Modify the trigger in the logic app.
D
Explanation:
https://docs.microsoft.com/en-us/azure/sentinel/playbook-triggers-actions
https://docs.microsoft.com/en-us/azure/sentinel/tutorial-respond-threats-playbook
You have 500 on-premises Windows 11 devices that use Microsoft Defender for Endpoint You enable Network device discovery.
You need to create a hunting query that will identify discovered network devices and return the identity of the onboarded device that discovered each network device.
Which built-in function should you use?
- A . current_cluster,endpoint()
- B . DeviceFromIP ()
- C . next ()
- D . SeenBy ()
HOTSPOT
You have a Microsoft Sentinel workspace named Workspaces
You configure Workspace1 to collect DNS events and deploy the Advanced Security information Model (ASIM) unifying parser for the DNS schema.
You need to query the ASIM DNS schema to list all the DNS events from the last 24 hours that have a response code of ‘NXDOMAIN’ and were aggregated by the source IP address in 15-minute intervals. The solution must maximize query performance.
How should you complete the query? To answer, select the appropriate options in the answer area NOTE: Each correct selection is worth one point.


You have a third-party security information and event management (SIEM) solution.
You need to ensure that the SIEM solution can generate alerts for Azure Active Directory (Azure AD) sign-events in near real time.
What should you do to route events to the SIEM solution?
- A . Create an Azure Sentinel workspace that has a Security Events connector.
- B . Configure the Diagnostics settings in Azure AD to stream to an event hub.
- C . Create an Azure Sentinel workspace that has an Azure Active Directory connector.
- D . Configure the Diagnostics settings in Azure AD to archive to a storage account.
B
Explanation:
Reference: https://docs.microsoft.com/en-us/azure/active-directory/reports-monitoring/overview-monitoring
You have a Microsoft 365 E5 subscription that uses Microsoft 365 Defender.
You need to review new attack techniques discovered by Microsoft and identify vulnerable resources in the subscription. The solution must minimize administrative effort.
Which blade should you use in the Microsoft 365 Defender portal?
- A . Advanced hunting
- B . Threat analytics
- C . Incidents & alerts
- D . Learning hub
B
Explanation:
To review new attack techniques discovered by Microsoft and identify vulnerable resources in the subscription, you should use the Threat Analytics blade in the Microsoft 365 Defender portal. The Threat Analytics blade provides insights into attack techniques, configuration vulnerabilities, and suspicious activities, and it can help you identify risks and prioritize threats in your environment.
Reference: https://docs.microsoft.com/en-us/microsoft-365/security/mtp/microsoft-365-defender-threat-analytics
HOTSPOT
You have an Azure subscription named Sub1 and an Azure DevOps organization named AzDO1.
AzDO1 uses Defender for Cloud and contains a project that has a YAML pipeline named Pipeline1.
Pipeline1 outputs the details of discovered open source software vulnerabilities to Defender for Cloud.
You need to configure Pipeline1 to output the results of secret scanning to Defender for Cloud.
What should you add to Pipeline1? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.


You have a Microsoft Sentinel workspace that uses the Microsoft 365 Defender data connector.
From Microsoft Sentinel, you investigate a Microsoft 365 incident.
You need to update the incident to include an alert generated by Microsoft Defender for Cloud Apps.
What should you use?
- A . the entity side panel of the Timeline card in Microsoft Sentinel
- B . the investigation graph on the Incidents page of Microsoft Sentinel
- C . the Timeline tab on the Incidents page of Microsoft Sentinel
- D . the Alerts page in the Microsoft 365 Defender portal
