Practice Free SC-200 Exam Online Questions
You have an Azure subscription that uses Microsoft Defender for Cloud.
You have a GitHub account named Account1 that contains 10 repositories.
You need to ensure that Defender for Cloud can assess the repositories in Account1.
What should you do first in the Microsoft Defender for Cloud portal?
- A . Add an environment.
- B . Enable security policies.
- C . Enable integrations.
- D . Enable a plan.
HOTSPOT
You have a Microsoft 365 E5 subscription that uses Microsoft Purview and contains a user named User1.
User1 shares a Microsoft Power Bi report file from the Microsoft OneDrive folder of your company to an external user by using Microsoft Teams.
You need to identity which Power BI report file was shared.
How should you configure the search? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.


Explanation:
To identify which Power BI report file was shared by User1, you should configure the search with the following parameters:
Activities: Shared Power BI report
Record Type: PowerBiAudit
Workload: PowerBi
These parameters will filter the search results to show only the events where a Power BI report was shared by a user in your organization. You can then look for the event that has User1 as the user ID and an external user as the recipient. The event details will show the name and URL of the Power BI report file that was shared. For more information, see Search the audit log for events in Power BI and Search for content in the Microsoft Purview compliance portal.
HOTSPOT
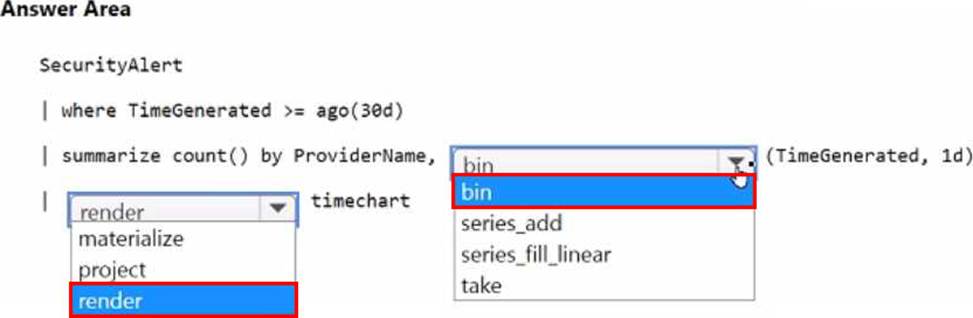
You have an Microsoft Sentinel workspace named SW1.
You plan to create a custom workbook that will include a time chart.
You need to create a query that will identify the number of security alerts per day for each provider.
How should you complete the query? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.

HOTSPOT
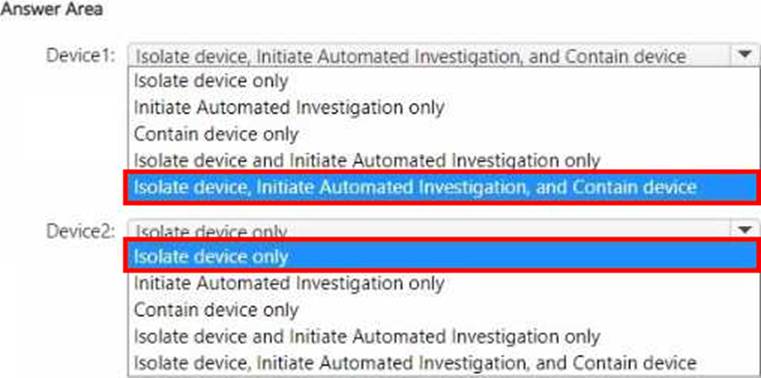
You have a Microsoft 365 E5 subscription that uses Microsoft Defender for Endpoint.
You have the on-premises devices shown in the following table.

You are preparing an incident response plan for devices infected by malware.
You need to recommend response actions that meet the following requirements:
• Block malware from communicating with and infecting managed devices.
• Do NOT affect the ability to control managed devices.
Which actions should you use for each device? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.

You need to restrict cloud apps running on CUENT1 to meet the Microsoft Defender for Endpoint requirements.
Which two configurations should you modify? Each correct answer presents part of the solution. NOTE: Each correct selection is worth one point.
- A . the Cloud Discovery settings in Microsoft Defender for Cloud Apps
- B . the Onboarding settings from Device management in Settings in Microsoft 365 Defender portal
- C . Microsoft Defender for Cloud Apps anomaly detection policies
- D . Advanced features from the Endpoints Settings in the Microsoft 365 Defender portal
You have a Microsoft 365 E5 subscription that uses Microsoft Defender for Endpoint
You need to create a query that will link the Alertlnfo, AlertEvidence, and DeviceLogonEvents tables.
The solution must return all the rows in the tables.
Which operator should you use?
- A . join kind = inner
- B . evaluate hint. Remote =
- C . search *
- D . union kind = inner
You need to complete the query for failed sign-ins to meet the technical requirements.
Where can you find the column name to complete the where clause?
- A . Security alerts in Azure Security Center
- B . Activity log in Azure
- C . Azure Advisor
- D . the query windows of the Log Analytics workspace
You have an Azure subscription that uses Microsoft Defender for Cloud and contains a storage account named storage1. You receive an alert that there was an unusually high volume of delete operations on the blobs in storage1.
You need to identify which blobs were deleted.
What should you review?
- A . the Azure Storage Analytics logs
- B . the activity logs of storage1
- C . the alert details
- D . the related entities of the alert
You are configuring Azure Sentinel.
You need to send a Microsoft Teams message to a channel whenever a sign-in from a suspicious IP address is detected.
Which two actions should you perform in Azure Sentinel? Each correct answer presents part of the solution. NOTE: Each correct selection is worth one point.
- A . Add a playbook.
- B . Associate a playbook to an incident.
- C . Enable Entity behavior analytics.
- D . Create a workbook.
- E . Enable the Fusion rule.
AB
Explanation:
Reference: https://docs.microsoft.com/en-us/azure/sentinel/tutorial-respond-threats-playbook
HOTSPOT
You have an Azure subscription that uses Microsoft Sentinel and contains a user named User1. You need to ensure that User1 can enable User and Entity Behavior Analytics (UEBA) for entity behavior in the Microsoft Entra tenant. The solution must use the principle of least privilege.
Which roles should you assign to User1? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.


