Practice Free SC-200 Exam Online Questions
You have an Azure subscription that uses Microsoft Defender XDR.
From the Microsoft Defender portal, you perform an audit search and export the results as a file named Filel.csv that contains 10,000 rows.
You use Microsoft Excel to perform Get & Transform Data operations to parse the AuditData column from Filel.csv. The operations fail to generate columns for specific JSON properties.
You need to ensure that Excel generates columns for the specific JSON properties in the audit search results.
Solution: From Excel, you apply filters to the existing columns in Filel.csv to reduce the number of rows, and then you perform the Get & Transform Data operations to parse the AuditData column.
Does this meet the requirement?
- A . Yes
- B . No
You have an Azure subscription that uses Microsoft Sentinel.
You detect a new threat by using a hunting query.
You need to ensure that Microsoft Sentinel automatically detects the threat. The solution must minimize administrative effort.
What should you do?
- A . Create a playbook.
- B . Create a watchlist.
- C . Create an analytics rule.
- D . Add the query to a workbook.
A
Explanation:
By creating an analytics rule, you can set up a query that will automatically run and alert you when the threat is detected, without having to manually run the query. This will help minimize administrative effort, as you can set up the rule once and it will run on a schedule, alerting you when the threat is detected.
Reference: https://docs.microsoft.com/en-us/azure/sentinel/analytics-create-rule
HOTSPOT
You need to implement Azure Sentinel queries for Contoso and Fabrikam to meet the technical requirements.
What should you include in the solution? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
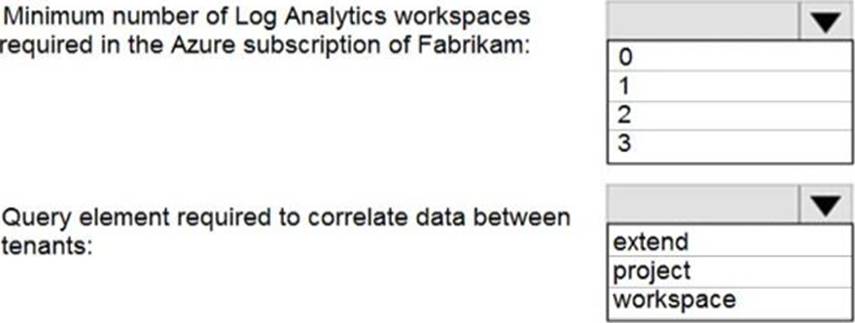
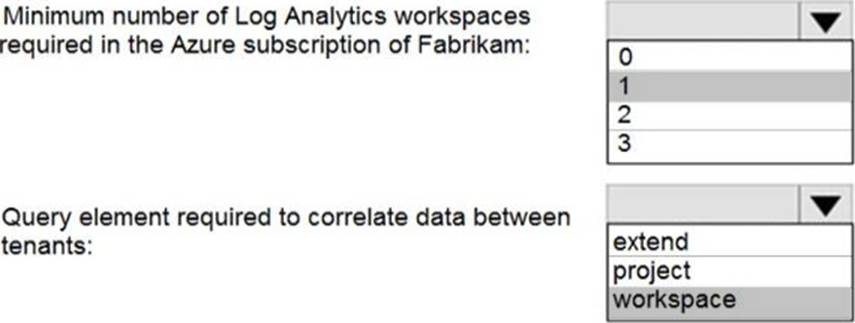
Explanation:
Reference: https://docs.microsoft.com/en-us/azure/sentinel/extend-sentinel-across-workspaces-tenants
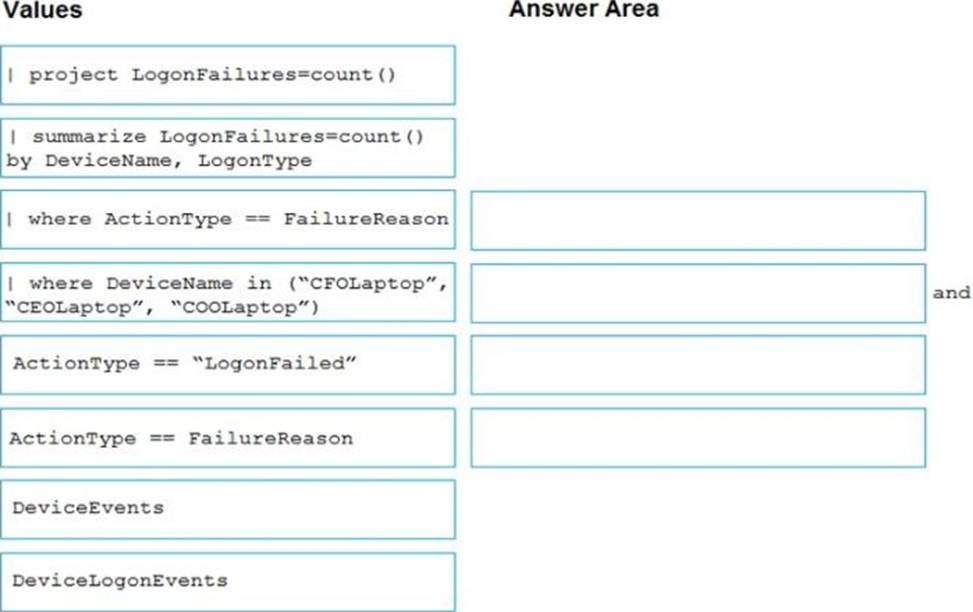
DRAG DROP
You have 50 on-premises servers.
You have an Azure subscription that uses Microsoft Defender for Cloud. The Defender for Cloud deployment has Microsoft Defender for Servers and automatic provisioning enabled.
You need to configure Defender for Cloud to support the on-premises servers.
The solution must meet the following requirements:
• Provide threat and vulnerability management.
• Support data collection rules.
Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
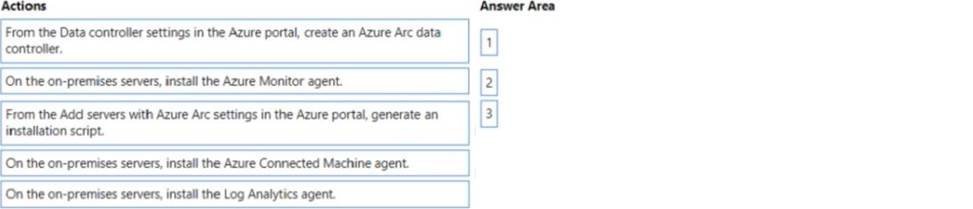
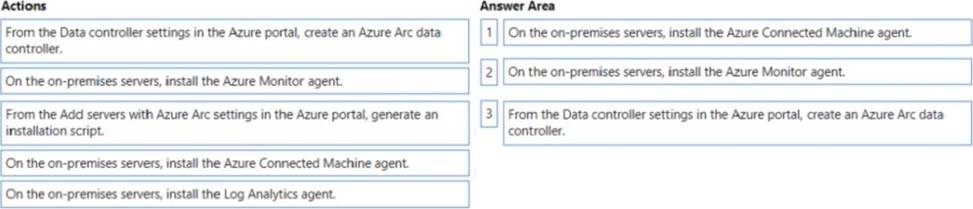
Explanation:
To configure Defender for Cloud to support the on-premises servers, you should perform the following three actions in sequence:
On the on-premises servers, install the Azure Connected Machine agent.
On the on-premises servers, install the Log Analytics agent.
From the Data controller settings in the Azure portal, create an Azure Arc data controller.
Once these steps are completed, the on-premises servers will be able to communicate with the Azure Defender for Cloud deployment and will be able to support threat and vulnerability management as well as data collection rules.
Reference: https://docs.microsoft.com/en-us/azure/security-center/deploy-azure-security-center#on-premises-deployment
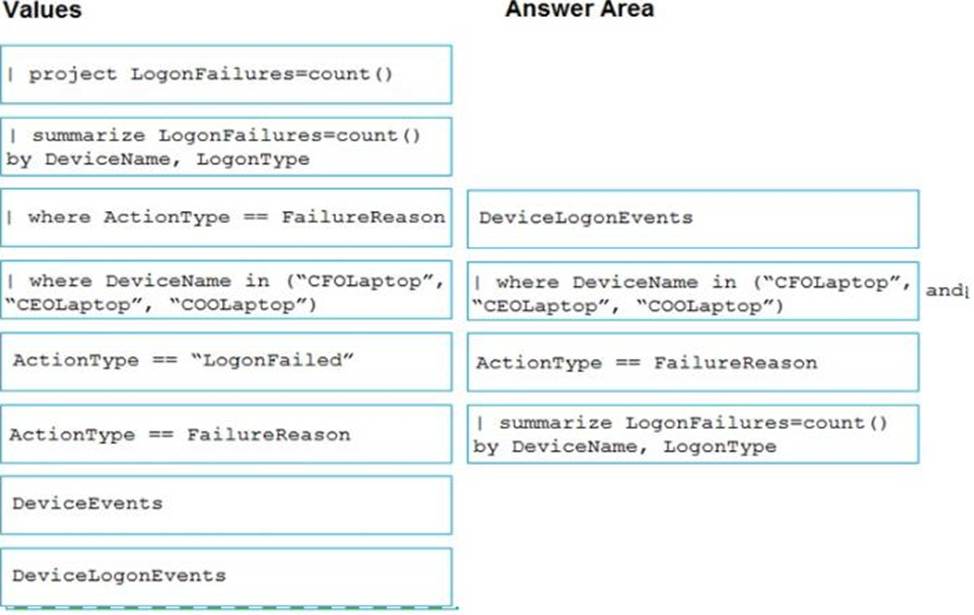
DRAG DROP
You are investigating an incident by using Microsoft 365 Defender.
You need to create an advanced hunting query to count failed sign-in authentications on three devices named CFOLaptop. CEOLaptop, and COOLaptop.
How should you complete the query? To answer, select the appropriate options in the answer area. NOTE Each correct selection is worth one point
You need to correlate data from the SecurityEvent Log Anarytks table to meet the Microsoft Sentinel
requirements for using UEBA.
Which Log Analytics table should you use?
- A . SentwlAuoNt
- B . AADRiskyUsers
- C . IdentityOirectoryEvents
- D . Identityinfo
You have a Microsoft Sentinel workspace named Workspaces
You need to exclude a built-in. source-specific Advanced Security Information Model (ASIM) parser from a built-in unified ASIM parser.
What should you create in Workspace1?
- A . a workbook
- B . a hunting query
- C . a watchlist
- D . an analytic rule
D
Explanation:
To exclude a built-in, source-specific Advanced Security Information Model (ASIM) parser from a built-in unified ASIM parser, you should create an analytic rule in the Microsoft Sentinel workspace. An analytic rule allows you to customize the behavior of the unified ASIM parser and exclude specific source-specific parsers from being used.
Reference: https://docs.microsoft.com/en-us/azure/sentinel/analytics-create-analytic-rule
You have an on-premises network.
You have a Microsoft 365 E5 subscription that uses Microsoft Defender for Identity.
From the Microsoft Defender portal, you investigate an incident on a device named Device1 of a user named User1. The incident contains the following Defender for Identity alert.
Suspected identity theft (pass-the-ticket) (external ID 2018)
You need to contain the incident without affecting users and devices. The solution must minimize administrative effort.
What should you do?
- A . Disable User 1 only.
- B . Quarantine Device1 only.
- C . Reset the password for all the accounts that previously signed in to Device1.
- D . DisableUser1 and quarantine Device1.
- E . Disable User1, quarantine Device1, and reset the password for all the accounts that previously signed in to Device1.
You have a Microsoft 365 subscription that uses Microsoft Defender XDR.
You discover that when Microsoft Defender for Endpoint generates alerts for a commonly used executable file, it causes alert fatigue. You need to tune the alerts.
Which two actions can an alert tuning rule perform for the alerts?
Each correct answer presents a complete solution. NOTE: Each correct selection is worth one point.
- A . delete
- B . hide
- C . resolve
- D . merge
- E . assign
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You are configuring Azure Sentinel.
You need to create an incident in Azure Sentinel when a sign-in to an Azure virtual machine from a malicious IP address is detected.
Solution: You create a scheduled query rule for a data connector.
Does this meet the goal?
- A . Yes
- B . No
B
Explanation:
Reference: https://docs.microsoft.com/en-us/azure/sentinel/connect-azure-security-center
