Practice Free FCSS_LED_AR-7.6 Exam Online Questions
Refer to the exhibits.
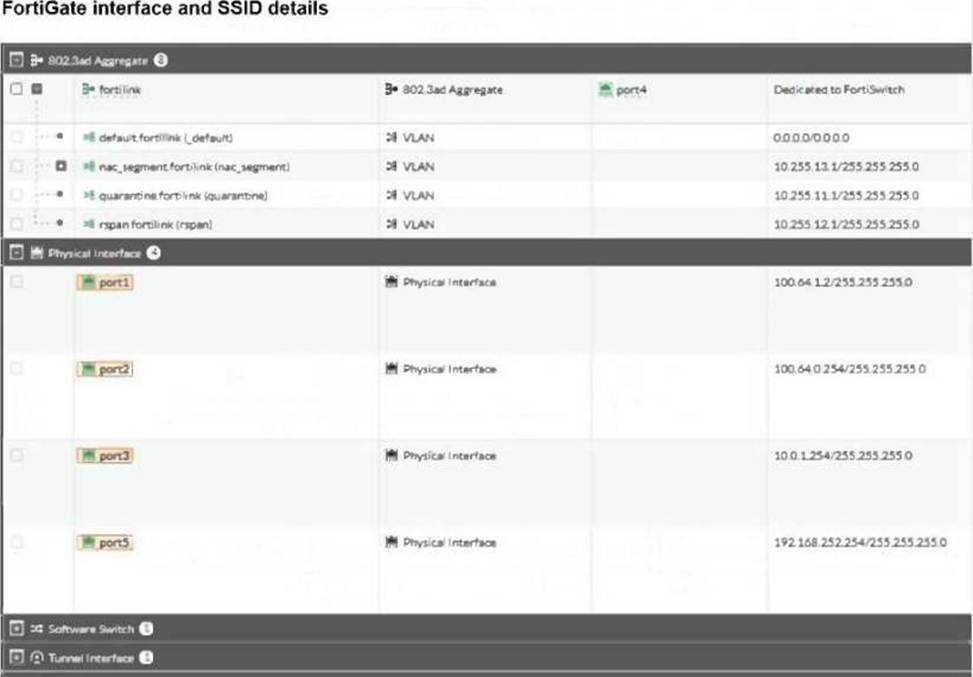
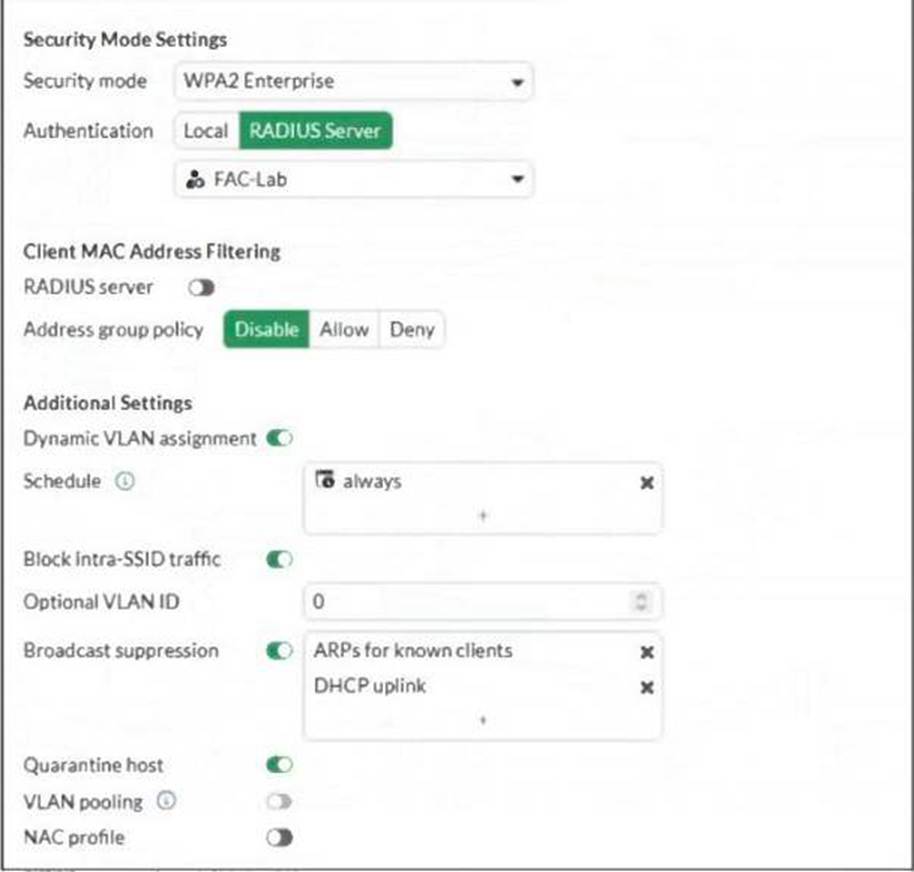
FortiGate is configured with an SSID named Corp in which dynamic VLAN assignment is enabled, and also configured with a RADIUS server to send IETF 64, IETF 65, and IETF 81 VSAs to manage VLAN allocation.
The RADIUS server has been confirmed to be sending all the required information to FortiGate. However, FortiGate is not assigning the correct VLANs to wireless clients.
Based on the information provided, what is causing the issue?
- A . The administrator must define the corresponding VLANs that are sent by the RADIUS server.
- B . Wireless clients bust be assigned an IP address from the 10.0.3.0/24 subnet.
- C . The administrator must configure a firewall policy to allow wireless clients to communicate with the RADIUS server.
- D . The RADUIS server must send the framed-ip attribute to assign wireless clients an IP address.
A network administrator connects a new FortiGate to the network, allowing it to automatically discover and register with FortiManager.
What occurs after FortiGate retrieves the FortiManager address?
- A . FortiGate establishes a secure tunnel to FortiManager over TCP port 541.
- B . The device needs to be manually authorized on FortiManager.
- C . FortiGate configures its interface settings based on a DHCP response from FortiManager.
- D . FortiGate sends a discovery request to all devices on the local network using UDP port 1068.
A
Explanation:
When a FortiGate is deployed usingZero Touch Provisioning (ZTP)or auto-discovery:
FortiGate retrieves theFortiManager IP address(from DHCP Option 240, FortiCloud/ZTNA provisioning, or manual set).
The next step isnot UI authorizationor DHCP changes―it immediately attempts to form aFGFM (FortiGateCFortiManager) tunnel.
The FGFM protocol usesTCP port 541to establish a secure management channel.
FortiManager will still require manual authorization of the deviceinside FortiManager, but this occursafterthe tunnel is established.
Therefore, the first automatic action after retrieving the FMG address iscreating the secure FGFM tunnel on TCP/541.
Refer to the exhibits.
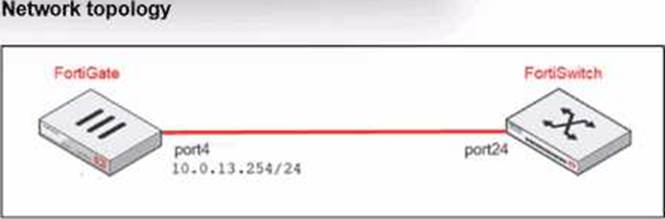
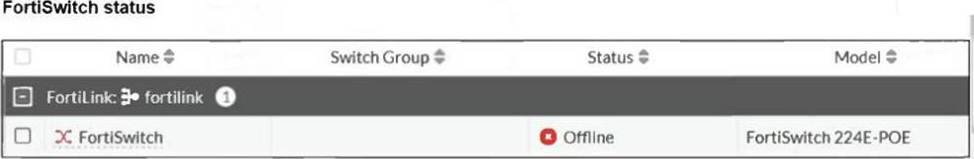
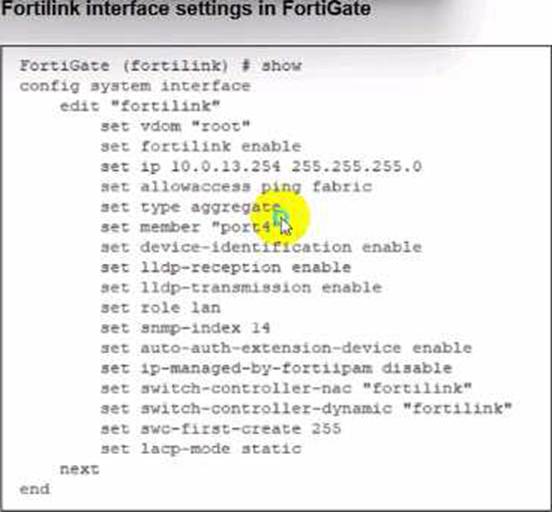
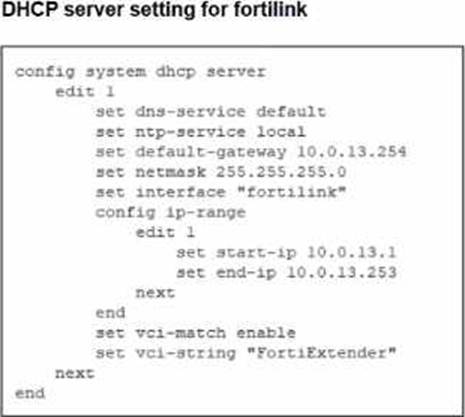
You are adding a new FortiSwitch to FortiGate for management. All necessary settings have been configured on FortiGate, but FortiSwitch remains offline. The cabling has been verified and is correctly connected.
Which misconfiguration might be preventing FortiGate from detecting FortiSwitch?
- A . The Fortilink interface setting ip-managed-by-fortiipam must be enabled.
- B . The Fortilink interface has the wrong interface member.
- C . The Fortilink interface setting cype must be physical.
- D . The DHCP server setting vci-string is misconfigured.
D
Explanation:
On FortiLink, FortiGate’s built-in DHCP server is what gives FortiSwitch its IP so it can come under management.
For automatic FortiSwitch onboarding, the DHCP server is usually set with:
set vci-match enable
set vci-string "FortiSwitch" "FortiExtender"
In the exhibit, the DHCP server for fortilink has:
set vci-match enable
set vci-string "FortiExtender"
Because theVCI string doesn’t include “FortiSwitch”, DHCP offers are only sent to clients whose Vendor Class Identifier matchesFortiExtender. The FortiSwitch never receives an IP, so it staysOffline.
OptionBis wrong: member "port4" matches the physical cabling in the topology.
OptionCis fine: FortiLink can be anaggregateinterface, not only physical.
OptionA(ip-managed-by-fortiipam) is unrelated; FortiIPAM isn’t required here.
Why is the suppression of rogue APs becoming more difficult with the introduction of new wireless security standards, such as 802.11w?
- A . 802.11w increases the processing overhead on network devices, slowing down the detection of rogue APs.
- B . The 802.11w standard reduces the range of wireless signals, limiting the ability to detect rogue APs at a distance.
- C . 802.11w encrypts all data traffic, making it difficult to identify rogue APs through packet inspection.
- D . 802.11w requires that clients authenticate management frames as legitimate, which helps prevent spoofing attacks.
A network administrator is deploying a new FortiGate firewall and wants to enable zero-touch provisioning with FortiManager. The administrator has not manually configured the FortiManager IP address or FQDN on FortiGate. However, FortiGate can still discover FortiManager automatically.
In this situation, where can FortiGate learn the FortiManager IP address or FQDN for zero-touch provisioning?
- A . By retrieving options 240 or 241 from a DHCP server
- B . By querying the local ARP table for the FortiManager IP address.
- C . By the default static route configuration on FortiGate.
- D . By checking the FortiGate factory default configuration.
Which FortiGuard licenses are required for FortiLink device detection to enable device identification and vulnerability detection?
- A . FortiGuard Vulnerability Management and FortiGuard Endpoit Protection
- B . FortiGuard Threat Intelligence and FortiGuard loT Detection
- C . FortiGuard Threat Intelligence and FortiGuard Endpoint Protection
- D . FortiGuard Attack Surface Security and FortiGuard loT Detection
D
Explanation:
FortiLink device detection relies on FortiGate’sDevice IdentificationandIoT Detectioncapabilities to classify devices connected to FortiSwitch ports.
To enabledevice identificationandvulnerability detectionfor IoT/endpoint devices in LAN Edge deployments, FortiGate must subscribe to the correct FortiGuard services.
You have decided to manage multiple FortiSwitch devices using FortiManager and its FortiSwitch Manager feature .
Which two statements accurately describe FortiSwitch Manager feature functionality? (Choose two.)
- A . FortiSwitch Manager displays the following statuses for FortiSwitch: online, offline, unauthorized, and unknown.
- B . Per-device management is useful for deploying multiple switches with the same configuration.
- C . FortiSwitch Manager displays the following statuses for FortiSwitch: active, inactive, pending, and unknown.
- D . In per-device management mode, you apply settings and profiles to individual FortiSwitch devices.
Refer to the exhibits.
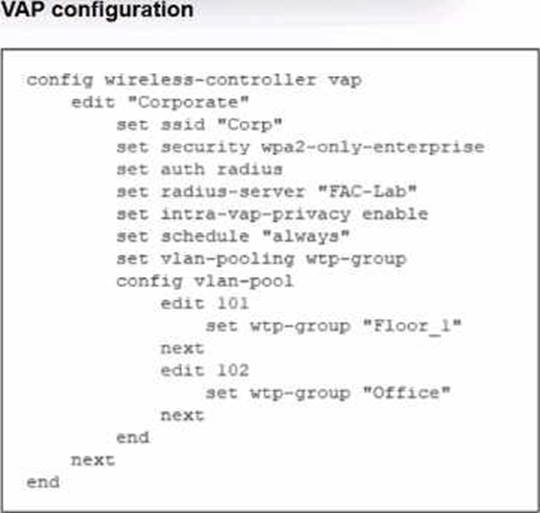

The exhibits show the VAP configuration. Wi-Fi SSIDs. and zone table.
Which two statements describe how FortiGate handles VLAN assignment for wireless clients? (Choose two.)
- A . FortiGate will load balance clients using VLAN 101 and VLAN 102 and assign them an IP address from the 10.0.3.0/24 subnet.
- B . All clients connecting to the Corp Zone will receive an IP address from the 10.0.20.0/24 subnet.
- C . Clients connecting to APs in the Floor 1 group will not be able to receive an IP address.
- D . Clients connecting to APs in the Office group will be assigned to VLAN 102.
C,D
Explanation:
The VAP configuration clearly showsVLAN pooling using WTP-groups:
set vlan-pooling wtp-group
config vlan-pool
edit 101
set wtp-group "Floor_1"
edit 102
set wtp-group "Office"
How VLAN assignment works in this mode
VLAN-pooling with wtp-group modemeans:
Each AP group (WTP group) is tied to exactly one VLAN in the pool.
The FortiGate doesnot load balanceVLANs.
Instead, VLANs are mappedper AP group, not per client.
Now verify each answer option:
Which two broad categories must be considered for wireless troubleshooting when evaluating key wireless metrics?
- A . Wireless range and network speed
- B . Signal interface and device compatibility
- C . Network reliability and signal interference
- D . Wireless health and wireless capacity
In each user certificate, you can define the subject field, expiration date. User Principal Name (UPN), URL for CRL download, and the OCSP URL.
How does the detailed configuration of these attributes impact the certificate?
- A . It makes the certificate easier to revoke manually because it reduces the need for automatic checks.
- B . It limits the validity of the certificate to specific devices and applications, reducing its general usability.
- C . It enables precise identification of the user and ensures timely certificate revocation checks.
- D . It makes the certificate compatible with a wide range of applications and services by ensuring universal validity
C
Explanation:
In user certificates used with FortiGate / FortiAuthenticator / SSL-VPN / 802.1X, the following attributes are important:
Subject field & UPN
Provide a unique identity for the user (CN and/or UPN).
FortiGate can use theSAN/UPNfield for LDAP-integrated certificate authentication.
Expiration date
Limits how long the certificate is valid, enforcing lifecycle and rotation.
CRL URL & OCSP URL
Tell FortiGate (or any relying party)where to check if the certificate has been revoked.
Enablesnear real-time revocationusing OCSP or periodic CRL downloads instead of relying only on expiration.
By carefully configuring these fields:
The certificate uniquely and correctly identifies the user.
Relying systems can performaccurate and timely revocation checks, improving security.
Why other options are wrong:
A: It does the opposite―CRL/OCSP increase automation, not manual revocation.
B: These attributes do not inherently limit a cert to specific devices; that’s done via key usage, EKU, or device certs.
D: They don’t “ensure universal validity”; they make the certprecisely boundto one identity with enforceable lifetime and revocation.
