Practice Free SC-200 Exam Online Questions
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You have Linux virtual machines on Amazon Web Services (AWS).
You deploy Azure Defender and enable auto-provisioning.
You need to monitor the virtual machines by using Azure Defender.
Solution: You manually install the Log Analytics agent on the virtual machines.
Does this meet the goal?
- A . Yes
- B . No
B
Explanation:
Reference: https://docs.microsoft.com/en-us/azure/defender-for-cloud/quickstart-onboard-machines?pivots=azure-arc
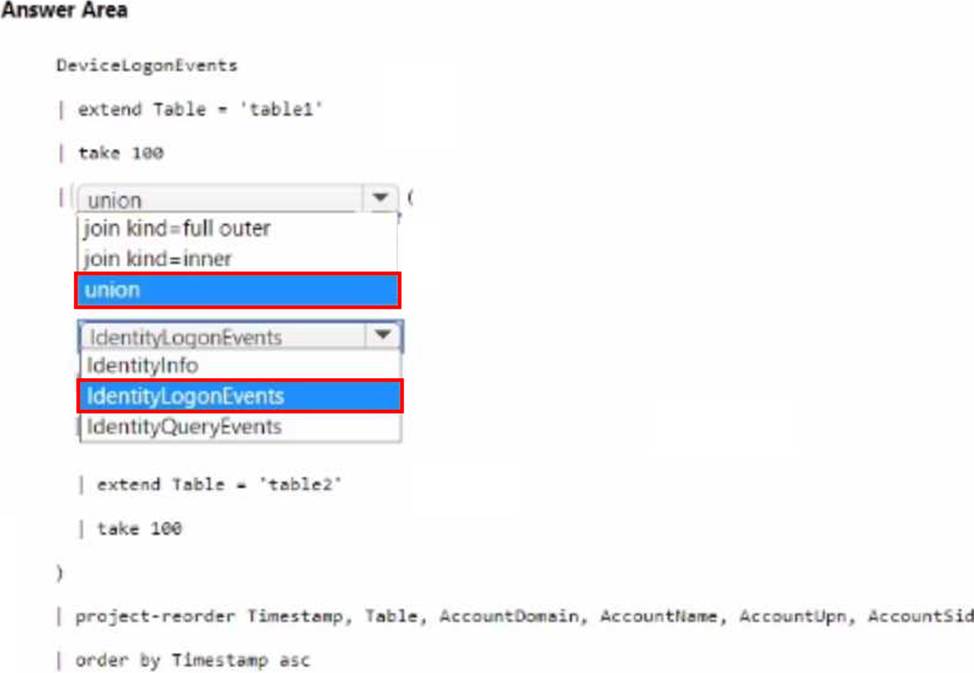
HOTSPOT
You have a Microsoft 365 E5 subscription that uses Microsoft Defender 36S.
Your network contains an on-premises Active Directory Domain Services (AD DS) domain that syncs with Azure AD.
You need to identify the 100 most recent sign-in attempts recorded on devices and AD DS domain controllers.
How should you complete The KQL query? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.

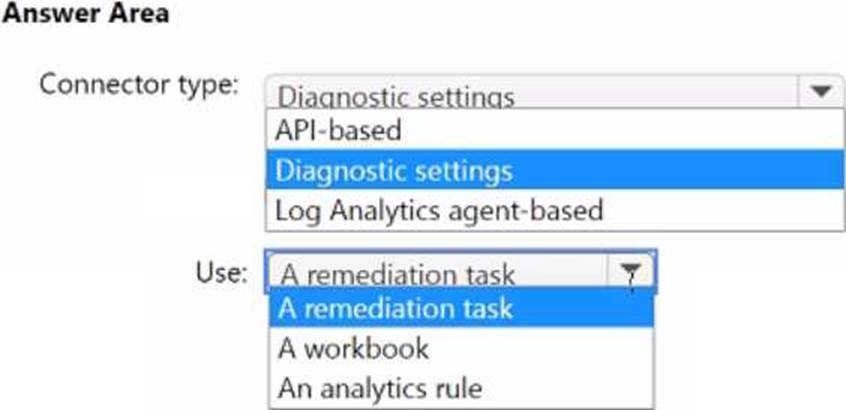
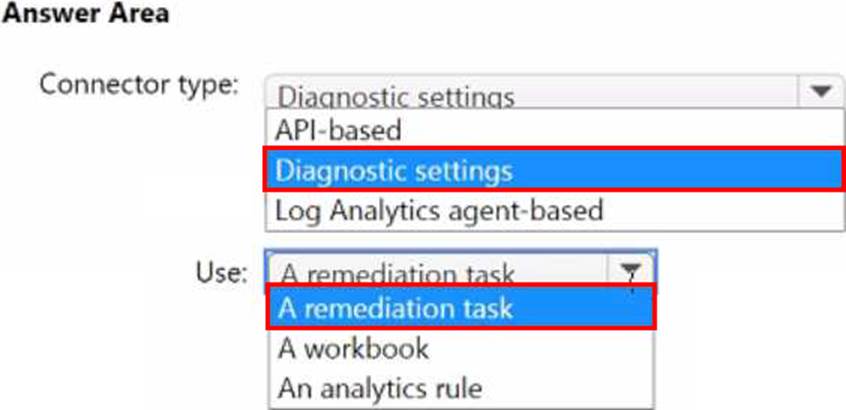
HOTSPOT
You have four Azure subscriptions. One of the subscriptions contains a Microsoft Sentinel workspace.
You need to deploy Microsoft Sentinel data connectors to collect data from the subscriptions by using Azure Policy. The solution must ensure that the policy will apply to new and existing resources in the subscriptions.
Which type of connectors should you provision, and what should you use to ensure that all the resources are monitored? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
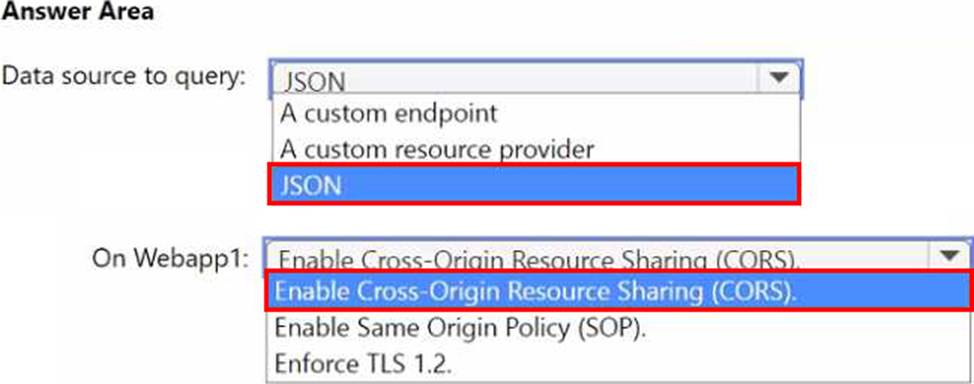
HOTSPOT
You need to implement the query for Workbook1 and Webapp1. The solution must meet the Microsoft Sentinel requirements.
How should you configure the query? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.

You have an Azure subscription that contains a Microsoft Sentinel workspace named WS1.
You create a hunting query that detects a new attack vector. The attack vector maps to a tactic listed in the MITRE ATT&CK database.
You need to ensure that an incident is created in WS1 when the new attack vector is detected.
What should you configure?
- A . a Fusion rule
- B . a query bookmark
- C . a scheduled query rule
- D . a hunting livestream session
HOTSPOT
You need to meet the Microsoft Defender for Cloud Apps requirements
What should you do? To answer. select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.


HOTSPOT
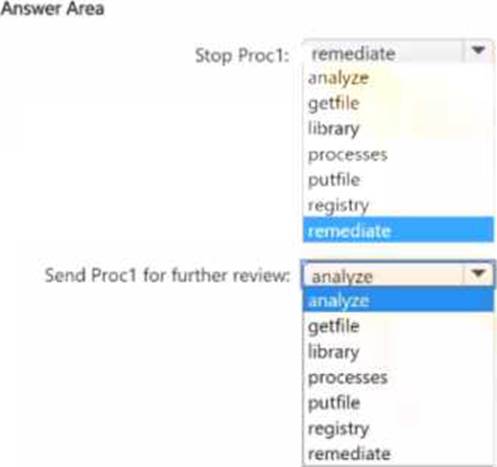
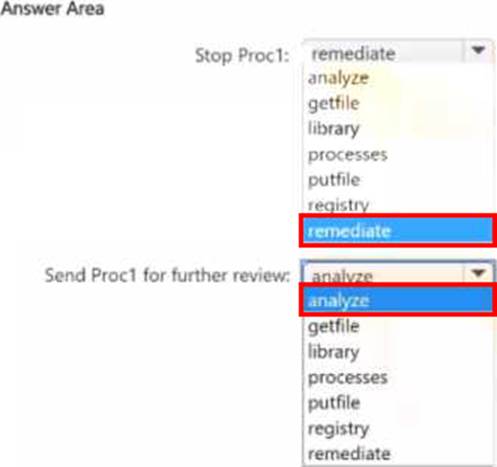
You have a Microsoft 365 subscription that uses Microsoft Defender XOR and contains a Windows device named Oevice1. You investigate a suspicious process named Prod on Device! by using a live response session.
You need to perform the following actions:
• Stop Prod.
• Send Prod for further review.
Which live response command should you run for each action? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
You have a Microsoft 365 E5 subscription that uses Microsoft Copilot for Security. Copilot for Security has the default settings configured.
You need to ensure that a user named User1 can use Copilot for Security to perform the following tasks:
• Upload files.
• View the usage dashboard.
• Share promptbooks with all users.
The solution must follow the principle of least privilege.
Which role should you assign to User1?
- A . Security Administrator
- B . Cloud Application Administrator
- C . Copilot Contributor
- D . Copilot Owner
You are investigating an incident in Azure Sentinel that contains more than 127 alerts.
You discover eight alerts in the incident that require further investigation.
You need to escalate the alerts to another Azure Sentinel administrator.
What should you do to provide the alerts to the administrator?
- A . Create a Microsoft incident creation rule
- B . Share the incident URL
- C . Create a scheduled query rule
- D . Assign the incident
D
Explanation:
Reference: https://docs.microsoft.com/en-us/azure/sentinel/investigate-cases
HOTSPOT
You have on-premises servers that run Windows Server.
You have a Microsoft Sentinel workspace named SW1. SW1 is configured to collect Windows Security log entries from the servers by using the Azure Monitor Agent data connector.
You plan to limit the scope of collected events to events 4624 and 462S only.
You need to use a PowerShell script to validate the syntax of the filter applied to the connector.
How should you complete the script? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.


