Practice Free HPE7-A08 Exam Online Questions
You are planning a 1 Gbps link between two CX switches.
Which type of SFP port will be required?
- A . SFP28
- B . SFP+
- C . SFP
- D . QSFP+
C
Explanation:
For a 1 Gbps link between two Aruba CX switches, the appropriate SFP port type is an SFP (Small Form-factor Pluggable). SFP+ and SFP28 are used for higher speeds such as 10 Gbps and 25 Gbps, respectively. QSFP+ is for even higher speeds (40 Gbps).
SFP supports 1 Gbps (1000BASE-X)
SFP+ supports 10 Gbps
SFP28 supports 25 Gbps and above
QSFP+ supports 40 Gbps and above
Therefore, the correct port type for a 1 Gbps link is SFP.
Reference: Aruba CX Transceiver and Port Type Compatibility Guide
HPE Aruba Networking Switch Hardware Documentation
Aruba Networking Best Practices for Link Speeds
What should you configure for an interface connected to a device you cannot trust to assign DSCP markings? (Select two.)
- A . Configure "qos trust cos"
- B . Apply a classifier-based policy to the interface to assign a Local Priority value
- C . Apply a dscp-map to the interface to assign a Local Priority value
- D . Configure Weighted Fair Queuing
- E . Configure "qos trust none"
B, E
Explanation:
For an interface connected to an untrusted device regarding DSCP markings, the recommended configurations are:
Apply a classifier-based policy to assign a Local Priority value (Option B). This overrides or marks traffic based on predefined criteria.
Configure qos trust none (Option E) to disable trusting DSCP or CoS markings from the device, preventing manipulation of QoS.
Trusting CoS (Option A) is incorrect because the device is untrusted.
DSCP maps and Weighted Fair Queuing (Options C and D) are additional QoS features but do not specifically address untrusted markings.
Reference: ArubaOS-CX QoS Configuration Guide
HPE Aruba Networking QoS Best Practices
Aruba CX Trust Model Documentation
A customer has recently deployed AP-615s at their new office and is wondering on which band the radios will operate with the default configuration after creating a tri-band SSID.
What should you tell them?
- A . The AP will operate on the 2.4GHz and 6GHz bands
- B . The AP will operate on the 2.4GHz and 5GHz bands
- C . The AP will operate on the 5GHz and 6GHz bands
- D . 6GHz will not be used unless manually configured
You want to set up NAE to monitor BGP neighbor state changes and create a helpdesk ticket whenever they occur.
Which NAE action can you configure to accomplish this?
- A . Execute shell command
- B . Send email
- C . Generate system log
- D . REST API call
D
Explanation:
To monitor BGP neighbor state changes and automatically create a helpdesk ticket, the NAE (Network Analytics Engine) action to use is a REST API call. This allows integration with external ticketing or automation systems, enabling automated ticket creation when a monitored event occurs.
Executing shell commands, sending emails, or generating logs are limited to internal actions and do
not integrate as seamlessly with helpdesk systems.
REST API calls allow custom integration and automation.
Reference: Aruba NAE Automation and REST API Documentation
HPE Aruba Network Monitoring Best Practices
ArubaOS-CX Network Analytics Engine User Guide
You’ve rebooted s-agg2 in a VSX configuration in an attempt to live-upgrade the cluster, and then you see this condition:

What would be the correct way to live-upgrade the VSX cluster?
- A . Always reload the primary switch first with the new image.
- B . Use the issu update-software option.
- C . Use vsx update-software option.
- D . Set the VSX to compatibility mode first, before rebooting the secondary switch.
C
Explanation:
Comprehensive Detailed Explanation
For live upgrading a VSX cluster, the correct procedure is to use the vsx update-software option, which allows in-service software upgrade (ISSU) with minimal disruption by upgrading switches one at a time while maintaining synchronization.
issu update-software is not a recognized command in Aruba CX.
Reloading the primary first risks service disruption.
Compatibility mode is not required prior to reboot.
Reference: Aruba VSX Upgrade Procedures Guide
HPE Aruba VSX Best Practices for Software Upgrades
ArubaOS-CX VSX Documentation
Refer to the exhibit.
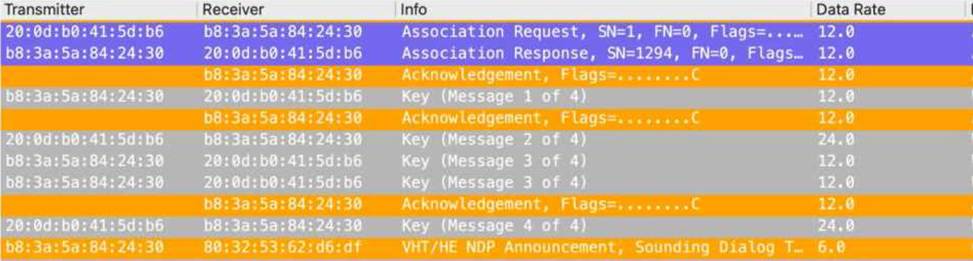

A customer is reporting that connectivity is failing for some wireless client devices.
What is your conclusion based on the capture?
- A . The client does not have an ARP entry for the default gateway
- B . The SSID is using WPA3-Enterprise key management
- C . The client has not obtained an IP address on this network previously
- D . The AP is using 20MHz wide 5GHz channels
A customer wants to prevent ‘man-in-the-middle’ attacks based on Layer 2 addressing.
What will help address that concern?
- A . Enable ARP inspection in the VLAN interface context
- B . Enable ARP inspection in the VLAN context
- C . Enable ARP inspection in the global context
- D . Enable ARP inspection in interface-level context
B
Explanation:
Comprehensive Detailed Explanation
To prevent man-in-the-middle attacks based on Layer 2 (Ethernet) addressing, enabling ARP inspection in the VLAN context is recommended. ARP inspection validates ARP packets and ensures only legitimate ARP responses are forwarded.
Enabling ARP inspection at VLAN level allows granular control.
Interface-level or global context is less typical or supported for ARP inspection on Aruba CX switches.
Reference: ArubaOS-CX Security Features Guide
HPE Aruba ARP Inspection Best Practices
Network Security Documentation for Aruba CX Switches
A Linux SFTP server is configured for IP address 192.168.1.100, and the CX 6325 switch has a management IP address 192.168.1.200.
How can you back up the saved switch configuration to a remote location?
- A . Use the command copy startup-config scp://[email protected]/switch_config.cfg vrf default on the switch.
- B . Use the command scp [email protected]:/running-config on the SFTP server.
- C . Use the command copy startup-config sftp://[email protected]/switch_config.cfg vrf mgmt on the switch.
- D . Use the command scp [email protected]:/startup-config on the SFTP server.
C
Explanation:
Backing up the switch configuration to a remote Linux SFTP server requires using the copy command with the correct protocol (SFTP in this case), username, server IP, filename, and optionally the VRF to route management traffic.
Option A uses SCP and vrf default but the question mentions SFTP server, so SFTP protocol should be used.
Option B is a server-side command (not the switch).
Option C correctly uses copy startup-config sftp://[email protected]/switch_config.cfg vrf mgmt which backs up the startup-config via SFTP using the management VRF.
Option D is also a server-side command.
Using vrf mgmt is required because the management IP is in a separate VRF on CX switches.
Reference: ArubaOS-CX Configuration Guide – Copy and File Transfer
Aruba CX VRF and Management Plane Concepts
HPE Aruba Networking SFTP/SCP Backup and Restore Examples
You are implementing a design where the campus network should be in an isolated spanning tree topology from the data centre network. The core switches are connected by a single Layer-2 interface carrying multiple VLANs.
When you examine the switches, you discover that the campus core sees the data centre core as the root bridge.
What configuration can you apply to the campus-to-data centre core link to resolve the issue?
- A . Root guard
- B . BPDU filter
- C . Admin edge
- D . BPDU guard
A
Explanation:
To prevent the campus core from seeing the data center core as the root bridge in a spanning tree topology (which can cause suboptimal paths or loops), Root Guard should be applied on the campus-to-data center core link. Root Guard enforces root bridge placement by blocking any superior BPDU from a downstream switch, maintaining the intended root bridge location.
BPDU filter blocks BPDUs entirely, which can cause problems.
Admin edge and BPDU guard are related to edge port protection, not root placement control.
Reference: Aruba Spanning Tree Configuration Guide
HPE Aruba Network Design Best Practices
IEEE 802.1D Root Guard Documentation
A customer would like to allow their IT Helpdesk to configure IoT devices to connect to a single SSID using a unique PSK that other devices cannot use.
Which solution would you recommend?
- A . MPSK AES with HPE Aruba Networking ClearPass
- B . MPSK AES with HPE Aruba Networking Central Cloud Authentication
- C . MPSK Local
- D . MPSK AES with MAC Auth
