Practice Free HPE7-A08 Exam Online Questions
How would you describe the firmware upgrade process for an HPE Aruba Networking VSX cluster?
- A . After the upgrade, the vsx-syned process can resume synchronization even if the switches are in a different firmware version
- B . After the upgrade, the vsx-syned process will continue synchronization, once vsx-upgrade commit is issued
- C . During the upgrade, the vsx-syned process will stop synchronization while the software versions are mismatched
- D . During the upgrade, the vsx-syned process will continue synchronization while the software
versions are mismatched
C
Explanation:
During a VSX firmware upgrade, the vsx-syned process stops synchronization while the switches have mismatched software versions. Synchronization resumes once both switches run the same software.
VSX synchronization cannot continue while versions mismatch (contrary to options B and D).
Compatibility mode is not required before rebooting secondary switch (Option D incorrect).
This behavior ensures consistency and avoids split-brain during upgrades.
Reference: Aruba VSX Firmware Upgrade Guide
HPE Aruba VSX Cluster Management Documentation
ArubaOS-CX Upgrade Procedures
Your network monitoring system has issued a critical alert indicating that the ISL between two VSX core switches is down.

What can you determine from the log output below?
- A . Core-2 has disabled its VSX LAG interfaces.
- B . Keepalive packets are being dropped.
- C . Both switches are forwarding traffic over VSX LAGs.
- D . Downstream switches are not able to forward traffic.
A
Explanation:
If the ISL between two VSX core switches is down and logs indicate that Core-2 has disabled its VSX LAG interfaces, it means Core-2 has disabled its VSX LAG interfaces, likely as a protective or failover mechanism.
Keepalive packets being dropped (Option B) may cause issues but logs specifically state interface disablement.
Both switches forwarding traffic (Option C) is unlikely if ISL is down.
Downstream switches inability to forward traffic (Option D) is a consequence, not the cause.
Reference: Aruba VSX Troubleshooting and Logs Documentation
HPE Aruba VSX High Availability Design Guide
ArubaOS-CX VSX Monitoring Best Practices
In a WLAN network with a tunneled SSID, you see the following events in HPE Aruba Networking Central:
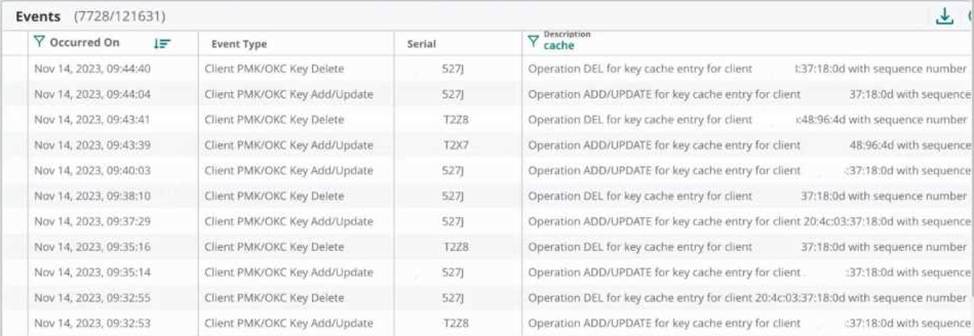
The customer asks you to investigate log messages.
What should you tell them?
- A . This indicates a security issue. The client with a MAC address ending with 37:18:0d is performing a Denial-of-Service attack on your network. You should track down the client and remove it from the network
- B . There is a roaming issue. Enable Fast Roaming 802.11r and OKC to resolve the issue
- C . This indicates a client WLAN driver issue for the client with a MAC address ending with 37:18:0d. You should upgrade the client WLAN driver
- D . This is normal, expected behavior. No further actions are needed
The HPE Aruba Networking CX 8320 VSX configuration is running the current software:
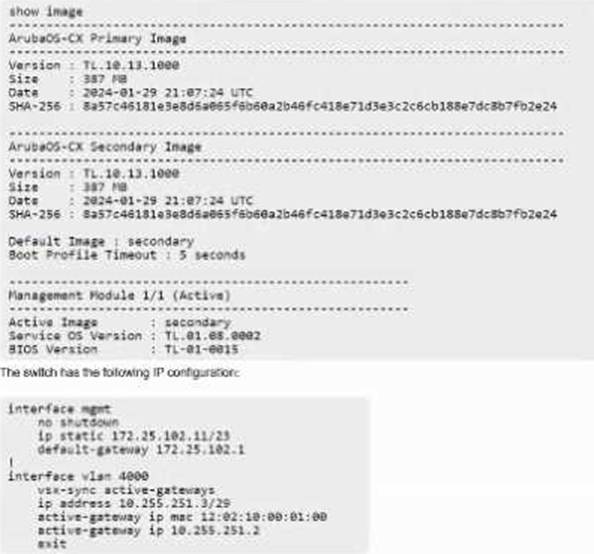
How do you upgrade the VSX cluster with the least amount of downtime from a remote server 172.25.101.10 reachable from 172.25.102.11?
- A . vsx update-software scp://172.25.101.10/image vrf mgmt
- B . vsx update-software scp://172.25.101.10/image primary
- C . vsx update-software tftp://172.25.101.10/image vrf mgmt
- D . vsx update-software tftp://172.25.101.10/image primary
A
Explanation:
To upgrade an HPE Aruba Networking CX 8320 VSX cluster with minimal downtime from a remote server, the correct command is:
vsx update-software scp://172.25.101.10/image vrf mgmt
Using SCP (Secure Copy Protocol) ensures secure transfer.
Specifying vrf mgmt ensures the update uses the management VRF for connectivity.
Using TFTP is less secure and not recommended for production upgrades.
The primary keyword is not valid for the vsx update-software command.
This method allows an in-service software upgrade (ISSU) with least disruption.
Reference: Aruba VSX Software Upgrade Guide
HPE Aruba CX Upgrade Best Practices
ArubaOS-CX CLI Reference for VSX Commands
Refer to the exhibit.

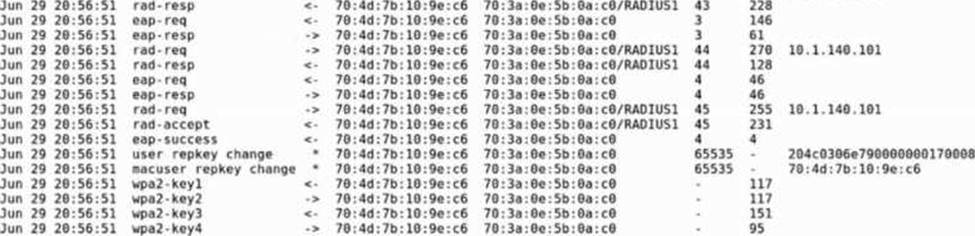
A network administrator is validating client connectivity and executes the show command shown in the exhibit.
Which authentication method was used by the wireless station?
- A . MAC authentication
- B . 802.1X user authentication
- C . WEBauth authentication
- D . 802.1X machine authentication
You would like to receive a monthly report tracking your available HPE Aruba Networking Central licenses and their expiration dates.
Which report should you schedule?
- A . Switch Capacity Planning
- B . Resource Utilization
- C . Network
- D . Infra Inventory
D
Explanation:
To receive a monthly report tracking available licenses and their expiration dates in Aruba Central, the Infra Inventory report should be scheduled. It provides detailed information about device inventories, including licenses and expiration.
Switch Capacity Planning focuses on resource utilization.
Resource Utilization monitors system performance.
Network report focuses on topology and health.
Reference: Aruba Central Reports and Analytics Documentation
HPE Aruba Central User Guide
Aruba Licensing Management Best Practices
A customer’s infrastructure is set up to use both primary and secondary gateway clusters on the SSID profile based on best practices.
Why do they have an equal split of their 144 APs across the primary gateway cluster and the secondary gateway cluster?
- A . The secondary gateway cluster is a heterogeneous cluster with four nodes.
- B . The primary and secondary gateway clusters are up, and the cluster preemption is enabled.
- C . The primary and secondary gateway clusters are up, but the cluster preemption is not enabled.
- D . The secondary gateway cluster is a homogeneous cluster with six nodes.
You recently added HPE Aruba Networking ClearPass as an authentication server to a group in HPE Aruba Networking Central. RADIUS authentication with Local User Roles (LUR) works fine, but the same access points cannot use Downloadable User Roles (DUR).
What should be corrected in this configuration to fix the issue with DUR?
- A . Add a new Enforcement Policy of type "WEBAUTH" on ClearPass and associate it with the matching service on ClearPass
- B . Add the correct values for "CPPM Username" and "CPPM Password" in the authentication server configuration on HPE Aruba Networking Central
- C . Uncheck the "Dynamic Authorization" checkbox in the authentication server configuration on HPE Aruba Networking Central
- D . Modify the shared secret on the switch to match CPPM using the "radius-server host" command
Your customer’s CISO would like to deploy colorless ports across the network.
Which will you need to configure to meet this requirement?
- A . VRRP
- B . VNBT
- C . VSF
- D . VRF
B
Explanation:
Colorless ports allow network devices to move or replace endpoints without changing port-level configurations, typically by automatically assigning network policies dynamically to any port.
HPE Aruba’s solution for colorless ports is the VNBT (Virtual Network Boundary Tagging) feature. VNBT allows dynamic segmentation of traffic, so ports can automatically take on the policies assigned to devices regardless of physical port location.
VRRP is a first-hop redundancy protocol and unrelated to port colorlessness.
VSF (Virtual Switching Framework) is for switch stacking.
VRF (Virtual Routing and Forwarding) is for traffic segmentation.
Thus, VNBT is the correct feature to meet colorless port requirements.
Reference: Aruba Dynamic Segmentation and VNBT Whitepapers
ArubaOS-CX User Guide for Dynamic Segmentation
Aruba Tech Docs on Colorless Ports and VNBT
The output of the show LACP interfaces shows the following:
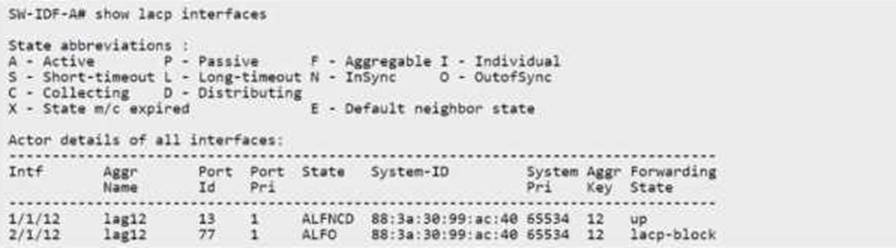
What is causing this issue?
- A . The AP is configured with LACP active.
- B . Each AP interface is connected to a routed-only interface on different networks.
- C . Spanning tree and loop protect are enabled on both AP uplink ports.
- D . e0 is connected to a smart rate interface, and e is connected to a non-smart rate interface.
