Practice Free H12-811_V2.0-ENU Exam Online Questions
What is the broadcast address of the network that contains a host with IP address 192.168.1.147/28?
- A . 192.168.1.157
- B . 192.168.1.255
- C . 192.168.1.159
- D . 192.168.1.145
C
Explanation:
A /28 subnet mask corresponds to 255.255.255.240, which means each subnet contains 16 IP addresses. The subnet boundaries in the last octet increase in steps of 16: 0, 16, 32, 48, 64, 80, 96, 112, 128, 144, 160, and so on. The host address 192.168.1.147 falls within the subnet range 192.168.1.144 to 192.168.1.159.
In that subnet, the network address is 192.168.1.144, the usable host range is 192.168.1.145 through 192.168.1.158, and the broadcast address is 192.168.1.159. Therefore, option C is correct.
Option D is the first usable host address, not the broadcast address.
Option A is just another usable host address.
Option B would be the broadcast address only for a /24 network, not for a /28. HCIA-Datacom requires learners to master subnetting because it is essential for IP planning, gateway deployment, route summarization, and troubleshooting Layer 3 communication issues in campus and enterprise networks.
On an STP network, an administrator wants SW2 to be elected as the root bridge.
Which of the following methods can be used to achieve this goal?
- A . Set a lower port priority on SW2.
- B . Set a higher system priority on SW2.
- C . Set a lower system priority on SW2.
- D . Set a lower root path cost on SW2.
C
Explanation:
In STP, the root bridge is elected based on the lowest bridge ID (BID). A BID is composed of the bridge priority and the MAC address of the switch. The device with the smallest BID becomes the root bridge. Therefore, if an administrator wants SW2 to become the root bridge, the most direct and correct method is to configure a lower system priority on SW2, making option C correct.
Option A is incorrect because port priority affects port-role selection in some tie-breaking scenarios, but it does not determine root-bridge election.
Option B is the opposite of what is required, because a higher system priority makes the BID larger and reduces the chance of being elected as root.
Option D is also incorrect because root path cost is used by non-root bridges to select the best path to the existing root bridge; it does not determine which switch becomes the root bridge in the first place. HCIA-Datacom stresses that bridge priority tuning is the standard administrative method used to control root bridge placement in campus networks for stable and predictable Layer 2 topology design.
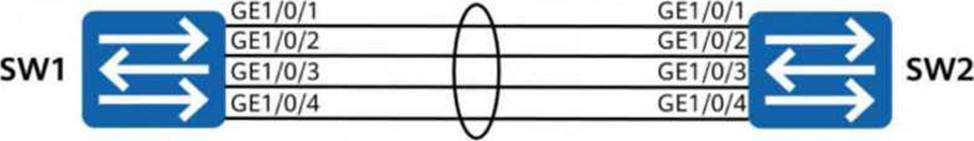
Four links between two switches establish an Eth-Trunk in manual mode, and the bandwidth of each link is 1 Gbit/s. One of the links fails.
Which of the following statements are true about this scenario? (Select all that apply)
- A . The Eth-Trunk interfaces on the switches are still in the Up state.
- B . The available link bandwidth between the switches is 3 Gbit/s.
- C . The service traffic originally carried by the faulty link stops being forwarded by the switches until the faulty link recovers.
- D . All TCP sessions established over the Eth-Trunk are immediately interrupted and re-established.
A, B
Explanation:
In an Eth-Trunk working in manual mode, multiple physical member links are bundled into one logical interface to provide higher bandwidth and link redundancy. If one of four 1 Gbit/s member links fails, the Eth-Trunk does not go down as long as at least one valid member link remains active. Therefore, statement A is correct. Since one link has failed and three member links remain available, the total available bandwidth becomes 3 Gbit/s, so statement B is also correct.
Statement C is incorrect because the traffic originally hashed to the failed link is not permanently stopped. Instead, after the link failure is detected, traffic is redistributed across the remaining active member links according to the trunk load-balancing mechanism.
Statement D is also incorrect because Eth-Trunk provides link-level redundancy. Existing upper-layer sessions such as TCP are not necessarily interrupted and re-established simply because one member link fails. HCIA-Datacom emphasizes that Eth-Trunk improves reliability and bandwidth utilization by allowing traffic to continue across surviving links when a single member fails. This is one of the main advantages of link aggregation in campus and data center switching networks.
When a Huawei network device functions as an FTP server, which of the following are possible causes of an FTP client failing to log in to the FTP server? (Select all that apply)
- A . The FTP server function is not enabled on the device.
- B . The authorized directory is not specified for FTP users.
- C . The FTP user name and password are not configured.
- D . The network between the device and the FTP client is unreachable.
A, B, C, D
Explanation:
All four options are possible causes of FTP login failure, so the correct answer is A, B, C, and D.
Option A is correct because if the FTP server function is not enabled on the Huawei device, the device cannot provide FTP services and the client cannot log in.
Option B is also correct because if the authorized directory is not specified for the FTP user, the user may not be able to complete login
or access file services properly, depending on the FTP user configuration requirements.
Option C is correct because an FTP user account must be configured with the required username and password; otherwise, authentication cannot succeed.
Option D is also correct because if the network between the FTP client and the device is unreachable, the client cannot establish the FTP connection at all.
In HCIA-Datacom troubleshooting, FTP login failure is usually checked from four aspects: service enablement, user configuration, permission or directory authorization, and network connectivity. This question tests standard remote maintenance troubleshooting logic for file transfer services on Huawei network devices.
Network administrators need to manage and maintain devices on the campus network.
Which of the following protocols cannot modify device configurations, such as interface IP addresses, device names, and so on?
- A . SNMP
- B . STelnet
- C . SFTP
- D . NETCONF
C
Explanation:
The protocol that cannot directly modify device configurations such as interface IP addresses or device names is SFTP, so option C is correct. SFTP is a secure file transfer protocol that runs over SSH and is mainly used to upload, download, and manage files between a client and a network device. It is commonly used for tasks such as transferring configuration files, system software, patches, or log files, but it does not itself provide an interactive or structured configuration modification mechanism.
By contrast, STelnet allows secure remote CLI login, through which an administrator can directly enter commands to change device settings. NETCONF is specifically designed for network configuration management and can modify configurations in a structured manner. SNMP can also modify certain managed object values through write operations when permissions and MIB support allow it, although in practice it is used more often for monitoring. HCIA-Datacom distinguishes between management-plane protocols based on their roles: interactive access, structured configuration, monitoring, and file transfer. This question checks whether the learner can identify SFTP as a file transfer tool rather than a direct configuration protocol.
The following command output is displayed on R1:
[R1] display aaa configuration
Domain Name Delimiter: @
Domainname parse direction: Left to right
Domainname location: After-delimiter
Administrator user default domain: default_admin
Normal user default domain: default
Domain: total: 256 used: 3
Authentication-scheme: total: 32 used: 2
Accounting-scheme: total: 32 used: 1
Authorization-scheme: total: 32 used: 2
Service-scheme: total: 256 used: 0
Recording-scheme: total: 32 used: 0
Local-user: total: 512 used: 2
Remote-admin-user block retry-interval: 5 Min(s)
Remote-admin-user block retry-time: 3
Remote-admin-user block time: 5 Min(s)
Session timeout invalid enable: No
Which of the following statements is false?
- A . The maximum number of consecutive authentication failures of the local account is 3.
- B . The local account lockout duration is 30 minutes.
- C . The domain name delimiter is at sign (@).
- D . A maximum of 512 local users can be created. Two local users have been created.
B
Explanation:
Comprehensive and Detailed 150 to 200 words of Explanation From Datacom knowledge:
The false statement is B. From the AAA configuration output, the value of Remote-admin-user block time is clearly shown as 5 Min(s), which means the account lockout duration is 5 minutes, not 30 minutes.
Option A is true because Remote-admin-user block retry-time: 3 indicates that after 3 consecutive authentication failures, the account will be blocked.
Option C is also true because the displayed Domain Name Delimiter is @, which is the separator used in usernames such as [email protected].
Option D is true as well because the output shows Local-user: total: 512 used: 2, meaning that the device supports a maximum of 512 local users, and currently 2 local users have been created.
This question checks the ability to correctly read AAA configuration output on Huawei devices. In HCIA-Datacom knowledge, it is important to distinguish between retry interval, retry count, and block time, because these values represent different security control parameters and are often confused during troubleshooting or configuration review.
In the leader AP networking architecture, the leader AP functions as a WAC and uses the CAPWAP protocol to uniformly manage and configure Fit APs.
- A . TRUE
- B . FALSE
A
Explanation:
This statement is true. In the leader AP networking architecture, one AP acts as the leader AP, taking on controller-like functions similar to those of a WAC for a small or medium-sized WLAN deployment. It can centrally manage other Fit APs and deliver unified wireless configurations such as SSIDs, security settings, and radio parameters. CAPWAP is used for management and control communication between the leader AP and the managed Fit APs.
This architecture is useful in scenarios where deploying a dedicated WAC is unnecessary or uneconomical, but centralized AP management is still desired. It provides a balance between simplicity and control and is commonly used in branch offices, small campuses, and similar environments. HCIA-Datacom explains leader AP networking as an intermediate solution between fully autonomous AP deployment and full WAC + Fit AP enterprise architecture. The key point is that the leader AP behaves as the management node for the other APs and enables unified configuration and control. Therefore, the statement correctly describes both the role of the leader AP and the use of CAPWAP in this architecture.
On the OSPF network shown in the figure, all IP addresses can communicate with each other.
Then the following configurations are added on R1:
[R1] acl 3000
[R1-acl4-advance-3000] rule deny ip source 10.0.1.1 0.0.0.0
[R1-acl4-advance-3000] rule deny ip source 10.1.1.1 0.0.0.0
[R1-acl4-advance-3000] rule permit ip source 10.3.1.1 0.0.0.0
[R1-acl4-advance-3000] rule permit ip
[R1-acl4-advance-3000] quit
[R1] traffic classifier test
[R1-classifier-test] if-match acl 3000
[R1-classifier-test] quit
[R1] traffic behavior test
[R1-behavior-test] permit
[R1-behavior-test] quit
[R1] traffic policy test
[R1-trafficpolicy-test] classifier test behavior test
[R1-trafficpolicy-test] quit
[R1] interface GE 0/0/1
[R1-GE0/0/1] traffic-policy test outbound
[R1-GE0/0/1] quit
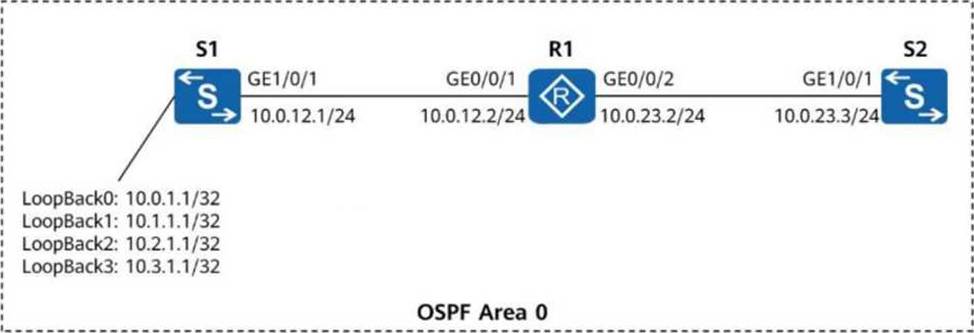
Which IP addresses of S1 can successfully ping 10.0.23.3? (Select all that apply)
- A . 10.3.1.1
- B . 10.2.1.1
- C . 10.0.1.1
- D . 10.1.1.1
A, B, C, D
Explanation:
All four addresses can successfully ping 10.0.23.3, so the correct answer is A, B, C, D.
The key point is that the traffic policy is applied outbound on GE0/0/1 of R1, which is the interface facing S1. When S1 pings 10.0.23.3, the echo request travels from S1 to R1 and then to S2. The return echo reply from 10.0.23.3 comes back to R1 and is then sent outbound on GE0/0/1 toward S1. Therefore, the traffic policy examines the reply packets, not the original ping request packets.
In those reply packets, the source IP address is 10.0.23.3, and the destination is one of S1’s loopback addresses. The ACL rules denying 10.0.1.1 and 10.1.1.1 as source addresses do not match these reply packets, because those addresses appear as destination addresses, not source addresses. In addition, the ACL contains rule permit ip, which permits all remaining IP traffic. As a result, replies to all four S1 addresses are forwarded successfully, so every listed address can ping 10.0.23.3.
The traditional Fat AP networking usually applies to WLANs of small and micro stores. For a large-scale WLAN, the WAC + Fit AP networking is typically used.
Which of the following statements are true about the WAC + Fit AP networking architecture? (Select all that apply)
- A . The WAC controls and manages all APs on the WLAN.
- B . Users need to log in to the Fit AP to configure wireless services.
- C . Layer 2 connectivity is required for the WAC and APs to communicate with each other using the
CAPWAP protocol. - D . Fit APs provide 802.11-based wireless access for STAs and function as bridges between wired and wireless networks.
A, D
Explanation:
In a WAC + Fit AP architecture, the WAC (Wireless Access Controller) centrally manages and controls the Fit APs, so option A is correct. Service configurations such as SSIDs, security policies, radio parameters, and access control are generally delivered from the WAC to the APs. The Fit AP mainly forwards wireless user traffic and executes the configuration issued by the controller.
Option D is also correct because a Fit AP provides 802.11 wireless access for stations (STAs) and serves as a bridge between the wireless side and the wired network. This is one of its basic roles in enterprise WLAN deployment.
Option B is incorrect because users or administrators do not normally need to log in to each Fit AP individually to configure wireless services; centralized management by the WAC is the whole advantage of this architecture.
Option C is incorrect because CAPWAP communication between the WAC and AP does not require Layer 2 adjacency; the WAC and AP can communicate over Layer 3 as long as IP connectivity exists. HCIA-Datacom emphasizes centralized configuration, simplified operations, and scalable deployment as key benefits of WAC + Fit AP networking.
During WLAN deployment, a Fit AP fails to go online on the WAC. You log in to the WAC and run the display ap online-fail-record command to locate the fault. The command output shows that the cause is Insufficient license resources. This means that the license resources on the WAC are insufficient and that you need to expand the license capacity.
- A . TRUE
- B . FALSE
A
Explanation:
This statement is true. On a Huawei WAC, the number of APs that can go online is controlled by the available license resources. If a Fit AP fails to come online and the command display ap online-fail-record shows Insufficient license resources, it means the controller does not currently have enough licensed capacity to allow additional APs to register successfully.
In this case, the administrator must expand the license capacity or adjust existing license allocation so that the AP can be admitted. This is a common WLAN deployment issue, especially when new APs are added without first verifying the current AP license limit on the WAC. HCIA-Datacom troubleshooting methodology emphasizes interpreting controller diagnostics and fault records accurately. An AP can fail to go online for many reasons, including CAPWAP reachability problems, version mismatch, authentication issues, or licensing limitations. When the failure reason explicitly indicates insufficient license resources, the troubleshooting direction is clear: the controller’s AP license capacity must be checked and, if necessary, increased. This question tests the ability to map a specific WAC alarm record to the correct operational response.
