Practice Free SK0-005 Exam Online Questions
An administrator received an alert that a backup job has been unsuccessful in the previous three attempts. The administrator discovers the issue occurred while backing up a user’s data on a network share.
Which of the following actions would be best to allow the job to complete successfully?
- A . Enabling open file backups in the backup job
- B . Moving the user’s data off the network share
- C . Excluding the user’s data from the backup
- D . Changing the backup job to exclude certain file types
A
Explanation:
Enabling open file backups allows the backup software to copy files that are currently open or in use
by applications. This ensures that even if a file is actively being modified during the backup process,
it will still be included in the backup.
Advantages:
Ensures consistency of backed-up data, especially for files that are frequently accessed or modified.
Prevents data loss due to files being skipped during backup.
Reference: CompTIA Server+ Guide, Chapter 6: Storage, Section 6.3.2 (Backup Types)
Microsoft Docs: Volume Shadow Copy Service (VSS)
Which of the following authentication types defines credentials as "something you have"?
- A . Swipe pattern
- B . PIN
- C . Fingerprint
- D . Smart card
D
Explanation:
The concept of authentication is rooted in the principle of verifying identity, which is commonly broken down into three categories: "something you know" (like a password or PIN), "something you have" (such as a smart card or a security token), and "something you are" (biometric data, for example, fingerprints). The question asks for the authentication type defined by "something you have."
Which of the following would be BEST to help protect an organization against social engineering?
- A . More complex passwords
- B . Recurring training and support
- C . Single sign-on
- D . An updated code of conduct to enforce social media
B
Explanation:
The best way to protect an organization against social engineering is to provide recurring training and support. Social engineering is a type of attack that exploits human psychology and behavior to manipulate people into divulging confidential information or performing malicious actions. Social engineering can take various forms, such as phishing emails, phone calls, impersonation, baiting, or quid pro quo. The best defense against social engineering is to educate and empower the employees to recognize and avoid common social engineering techniques and report any suspicious activities or incidents. Recurring training and support can help raise awareness and reinforce best practices among the employees.
A server technician is installing a new server OS on legacy server hardware.
Which of the following should the technician do FIRST to ensure the OS will work as intended?
- A . Consult the HCL to ensure everything is supported.
- B . Migrate the physical server to a virtual server.
- C . Low-level format the hard drives to ensure there is no old data remaining.
- D . Make sure the case and the fans are free from dust to ensure proper cooling.
A
Explanation:
The first thing that the technician should do before installing a new server OS on legacy server hardware is to consult the HCL (Hardware Compatibility List) to ensure everything is supported. The HCL is a list of hardware devices and components that are tested and certified to work with a specific OS or software product. The HCL helps to avoid compatibility issues and performance problems that may arise from using unsupported or incompatible hardware. Migrating the physical server to a virtual server may be a good option to improve scalability and flexibility, but it requires additional hardware and software resources and may not be feasible for legacy server hardware. Low-level formatting the hard drives may be a good practice to erase any old data and prepare the drives for a new OS installation, but it does not guarantee that the hardware will work with the new OS. Making sure the case and the fans are free from dust may be a good practice to ensure proper cooling and prevent overheating, but it does not guarantee that the hardware will work with the new OS.
Reference:
https://www.howtogeek.com/190014/virtualization-basics-understanding-techniques-and-fundamentals/
https://www.howtogeek.com/173353/how-to-low-level-format-or-write-zeros-to-a-hard-drive/
https://www.howtogeek.com/303282/how-to-manage-your-pcs-fans-for-optimal-airflow-and-cooling/
Which of the following will protect critical data during a natural disaster?
- A . Off-site storage
- B . Life-cycle management
- C . Environmental controls
- D . Data-at-rest encryption
A
Explanation:
Off-site storage involves storing data backups in a physically separate location from where the servers and primary data reside. This protects critical data in case the main site is damaged or destroyed due to a natural disaster, such as floods, fires, or earthquakes. Off-site storage can be in the form of cloud storage or physical tapes stored in a geographically distant location.
Off-site storage (Answer A): It ensures that a company’s critical data remains accessible even if the local infrastructure is compromised. This is a common part of disaster recovery planning and is crucial for business continuity.
Life-cycle management (Option B): While important for managing data from creation to deletion, it does not specifically protect data during disasters.
Environmental controls (Option C): These manage physical conditions like temperature and humidity but do not address the risk of data loss during disasters.
Data-at-rest encryption (Option D): Encryption protects the confidentiality of stored data but does
not ensure availability in the event of a disaster.
CompTIA Server+
Reference: This topic is covered under SK0-005 Objective 4.1: Summarize disaster recovery methods and concepts.
An administrator is troubleshooting a failed NIC in an application server. The server uses DHCP to get all IP configurations, and the server must use a specific IP address. The administrator replaces the NIC, but then the server begins to receive a different and incorrect IP address.
Which of the following will enable the server to get the proper IP address?
- A . Modifying the MAC used on the DHCP reservation
- B . Updating the local hosts file with the correct IP address
- C . Modifying the WWNN used on the DHCP reservation
- D . Updating the NIC to use the correct WWNN
A
Explanation:
A DHCP reservation is a way to assign a specific IP address to a device based on its MAC address, which is a unique identifier for each network interface card (NIC). When the administrator replaced the NIC, the MAC address of the server changed, and the DHCP server no longer recognized it as the same device. Therefore, the DHCP server assigned a different IP address to the server, which was incorrect for the application. To fix this problem, the administrator needs to modify the DHCP reservation to use the new MAC address of the NIC, so that the server can get the proper IP address.
A WWNN (World Wide Node Name) is a unique identifier for a Fibre Channel node, which is a device that can communicate over a Fibre Channel network. A WWNN is not related to DHCP or IP addresses, and it is not used for DHCP reservations. Therefore, options B and D are incorrect.
Updating the local hosts file with the correct IP address (option C) is also incorrect, because it does not solve the problem of getting the correct IP address from the DHCP server. The hosts file is a local file that maps hostnames to IP addresses, and it is used to override DNS queries. However, it does not affect how the DHCP server assigns IP addresses to devices. Moreover, updating the hosts file manually on every device that needs to communicate with the server is not a scalable or efficient solution.
Reference:
How to reserve IP Address in DHCP Server – Ask Ubuntu
Static IP vs DHCP Reservation – The Tech Journal
How to Configure DHCP Server Reservation in Windows … – ITIngredients
A server technician is placing a newly configured server into a corporate environment.
The server will be used by members of the accounting department, who are currently assigned by the VLAN identified below:
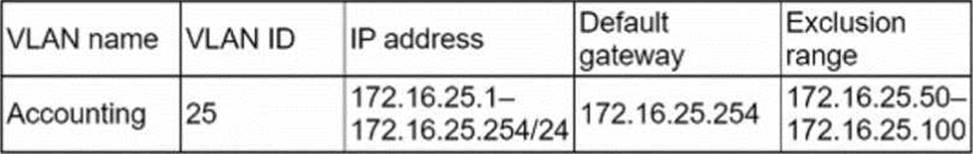
Which of the following IP address configurations should the technician assign to the new server so the members of the accounting group can access the server?
- A . IP address: 172.16.25.90/24 Default gateway: 172.16.25.254
- B . IP address: 172.16.25.101/16 Default gateway: 172.16.25.254
- C . IP address: 172.16.25.254/24 Default gateway: 172.16.25.1
- D . IP address: 172.16.26.101/24 Default gateway: 172.16.25.254
A
Explanation:
The IP address configuration that the technician should assign to the new server so the members of the accounting group can access the server is 172.16.25.90/24 for the IP address and 172.16.25.254 for the default gateway. This configuration matches the VLAN identified in the image, which has a network address of 172.16.25.0/24 and a subnet mask of 255.255.255.0. The IP address of the server must be within the same network range as the VLAN, which is from 172.16.25.1 to 172.16.25.254, excluding the network and broadcast addresses (172.16.25.0 and 172.16.25.255). The default gateway of the server must be the same as the VLAN, which is 172.16.25.254, to allow communication with other networks or devices outside the VLAN.
Reference: [CompTIA Server+ Certification Exam Objectives], Domain 4.0: Networking, Objective 4.1: Given a scenario, configure network settings for servers.
Which of the following is a method that is used to prevent motor vehicles from getting too close to building entrances and exits?
- A . Bollards
- B . Reflective glass
- C . Security guards
- D . Security cameras
A
Explanation:
Bollards are an example of a method that is used to prevent motor vehicles from getting too close to building entrances and exits. Bollards are short, sturdy posts that are installed on sidewalks, parking lots, or roads to create physical barriers and control traffic flow. Bollards can be used to protect pedestrians, buildings, or other structures from vehicle collisions or attacks. Bollards can be made of various materials, such as metal, concrete, or plastic, and can be fixed, removable, or retractable.
Reference: https://en.wikipedia.org/wiki/Bollard
Users are able to connect to the wireless network, but they are unable to access the internet. The network administrator verifies connectivity to all network devices, and there are no ISP outages. The server administrator removes the old address leases from the active leases pool, which allows users to access the internet.
Which of the following is most likely causing the internet issue?
- A . The DHCP exclusion needs to be removed.
- B . The DHCP scope is full.
- C . The DHCP scope options are misconfigured.
- D . The DHCP lease times are too short.
- E . The DHCP reservations need to be configured.
B
Explanation:
The most likely cause of the internet issue is B. The DHCP scope is full.
A DHCP scope is a range of IP addresses that a DHCP server can assign to DHCP clients on a network. A DHCP scope has a start address and an end address, and it can also have some excluded addresses that are not available for lease. A DHCP scope can have various options, such as subnet mask, default gateway, DNS server, etc., that are applied to the DHCP clients along with the IP address. A DHCP scope also has a lease time, which is the duration that a DHCP client can use an IP address before renewing it or releasing it. A DHCP scope can have reservations, which are fixed IP addresses that are assigned to specific DHCP clients based on their MAC addresses12
If a DHCP scope is full, it means that there are no more IP addresses available for lease in the scope. This can happen if the number of DHCP clients exceeds the number of IP addresses in the scope, or if the lease time is too long and the IP addresses are not released or reused frequently enough. If a DHCP scope is full, any new or existing DHCP clients that request an IP address from the DHCP server will not receive one, and they will not be able to access the network or the internet12
In this scenario, users are able to connect to the wireless network, but they are unable to access the internet. The network administrator verifies connectivity to all network devices, and there are no ISP outages. The server administrator removes the old address leases from the active leases pool, which allows users to access the internet. This indicates that the DHCP scope is full, and that removing the old leases frees up some IP addresses for lease in the scope. Therefore, option B is the most likely cause of the internet issue.
A backup application is copying only changed files each time it runs. During a restore, however, only a single file is used.
Which of the following backup methods does this describe?
- A . Open file
- B . Synthetic full
- C . Full incremental
- D . Full differential
B
Explanation:
This is the best description of a synthetic full backup method because it creates a full backup by combining previous incremental backups with the latest backup. An incremental backup copies only the files that have changed since the last backup, while a full backup copies all the files. A synthetic full backup reduces the storage space and network bandwidth required for backups, while also simplifying the restore process by using a single file.
Reference: https://www.veritas.com/support/en_US/doc/129705091-129705095-0/br731_wxrt-tot_v131910378-129705095
