Practice Free SK0-005 Exam Online Questions
A server is only able to connect to a gigabit switch at 100Mb. Other devices are able to access the network port at full gigabit speeds, and when the server is brought to another location, it is able to connect at full gigabit speed.
Which of the following should an administrator check first?
- A . The switch management
- B . The VLAN configuration
- C . The network cable
- D . The network drivers
C
Explanation:
The first thing that the administrator should check is the network cable. The network cable is a physical medium that connects a server to a switch or other network device. The network cable can affect the speed and quality of the network connection, depending on its type, length, and condition.
If the network cable is damaged, faulty, or incompatible, it can cause the server to connect at a lower speed than expected. Therefore, the administrator should check the network cable for any signs of wear, tear, or mismatch, and replace it if necessary.
Reference: CompTIA Server+ SK0-005 Certification Study Guide, Chapter 2, Lesson 2.1, Objective 2.1
A technician needs to restore data from a backup.
The technician has these files in the backup inventory:
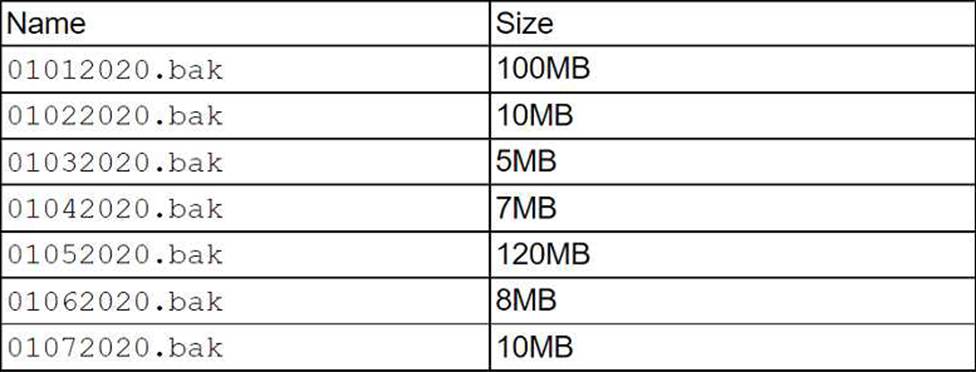
Which of the following backup types is being used if the file 01062020.bak requires another file to restore data?
- A . Full
- B . Incremental
- C . Snapshot
- D . Differential
B
Explanation:
An incremental backup only backs up files that have changed since the last backup, whether it was a full or an incremental backup. Therefore, an incremental backup file may require another file to restore data, depending on the sequence of backups. A full backup backs up all files and does not require any other file to restore data. A snapshot is a point-in-time copy of data that does not depend on other files. A differential backup backs up files that have changed since the last full backup and does not require any other file to restore data.
A technician is configuring a new server with four disks for the development team. The requirements are disk redundancy and maximum usable disk capacity.
Which of the following RAID levels should be used for this server?
- A . 0
- B . 1
- C . 5
- D . 10
D
Explanation:
Scenario: Four disks, requiring redundancy and maximum usable capacity.
RAID Level: RAID 10 (Option D) is the best choice:
RAID 10 combines mirroring (redundancy) and striping (performance).
RAID 0 lacks redundancy, RAID 1 provides less capacity, and RAID 5 requires more
A technician is configuring a new server with four disks for the development team. The requirements are disk redundancy and maximum usable disk capacity.
Which of the following RAID levels should be used for this server?
- A . 0
- B . 1
- C . 5
- D . 10
D
Explanation:
Scenario: Four disks, requiring redundancy and maximum usable capacity.
RAID Level: RAID 10 (Option D) is the best choice:
RAID 10 combines mirroring (redundancy) and striping (performance).
RAID 0 lacks redundancy, RAID 1 provides less capacity, and RAID 5 requires more
In which of the following media rotation schemes are daily, weekly, and monthly backup media utilized in a first-in, first-out method?
- A . Waterfall
- B . Synthetic full
- C . Tower of Hanoi
- D . Grandfather-father-son
D
Explanation:
Grandfather-father-son (GFS) is a common backup rotation scheme that uses daily, weekly, and monthly backup media in a first-in, first-out (FIFO) method. The daily backups are rotated on a 3-months basis using a FIFO system as above. The weekly backups are similarly rotated on a bi-yearly basis, and the monthly backups are rotated on an annual basis. The oldest backup media in each cycle are overwritten by the newest ones. This scheme provides multiple versions of backup data at different intervals, allowing for flexible restoration options. Waterfall is another name for GFS. Synthetic full is a backup method that combines an initial full backup with subsequent incremental backups to create a new full backup without transferring all data again. Tower of Hanoi is another backup rotation scheme that uses an algorithm based on moving disks between three pegs.
Reference: https://en.wikipedia.org/wiki/Backup_rotation_scheme
Which of the following script types uses commands That start with sec-?
- A . Batch
- B . Bash
- C . PowerShell
- D . JavaScript
C
Explanation:
PowerShell is a scripting language and a command-line shell that uses commands that start with sec-to perform security-related tasks. For example, sec-edit is a command that edits security policies, sec-logon is a command that manages logon sessions, and sec-policy is a command that applies security templates.
Verified Reference: [PowerShell security commands], [Security policy]
Which of the following describes the installation of an OS contained entirely within another OS installation?
- A . Host
- B . Bridge
- C . Hypervisor
- D . Guest
D
Explanation:
The installation of an OS contained entirely within another OS installation is described as a guest. A guest is a term that refers to a virtual machine (VM) that runs on top of a host operating system (OS) using a hypervisor or a virtualization software. A guest can have a different OS than the host, and can run multiple applications or services independently from the host. A guest can also be isolated from the host and other guests for security or testing purposes.
IDS alerts indicate abnormal traffic patterns are coming from a specific server in a data center that hosts sensitive data. Upon further investigation, the server administrator notices this server has been infected with a virus due to an exploit of a known vulnerability from its database software.
Which of the following should the administrator perform after removing the virus to mitigate this issue from reoccurring and to maintain high availability? (Select three).
- A . Run a vulnerability scanner on the server.
- B . Repartition the hard drive that houses the database.
- C . Patch the vulnerability.
- D . Enable a host firewall.
- E . Reformat the OS on the server.
- F . Update the antivirus software.
- G . Remove the database software.
- H . Air gap the server from the network.
ACF
Explanation:
After removing the virus from the server, the administrator should perform the following actions to mitigate the issue from reoccurring and to maintain high availability:
Run a vulnerability scanner on the server to identify any other potential weaknesses or exposures that could be exploited by attackers.
Patch the vulnerability that allowed the virus to infect the server in the first place, using the latest updates from the database software vendor or a trusted source.
Update the antivirus software on the server to ensure it has the most recent virus definitions and can detect and prevent future infections. The other options are either unnecessary or counterproductive for this scenario. Repartitioning the hard drive, reformatting the OS, removing the database software, or air gapping the server from the network would cause downtime and data loss, while enabling a host firewall would not prevent a virus infection from within the
network.
Reference: CompTIA Server+ Certification Exam Objectives, Domain 5.0: Security, Objective 5.2: Given a scenario involving a security threat/vulnerability/risk, implement appropriate mitigation techniques.
A systems engineer is configuring a new VLAN for expansion of a campus network. The engineer configures a new DHCP scope on the existing Windows DHCP server cluster and activates the scope for the clients. However, new clients in the area report they are not receiving any DHCP address information.
Which of the following should the engineer do first?
- A . Confirm the client PCs are using the correct speed on the NIC
- B . Confirm the network uses the same NTP server as the clients
- C . Confirm the network has a helper address for the DHCP server
- D . Confirm the DHCP server is authorized in Active Directory
C
Explanation:
When clients on a different VLAN cannot receive DHCP addresses, it’s often because there is no DHCP helper address configured on the router or switch. A DHCP relay/helper address forwards DHCP requests from clients on the VLAN to the DHCP server, which may reside on a different network.
Confirming the network has a helper address (Answer C): This should be the first step to ensure that DHCP requests from the VLAN are correctly routed to the DHCP server.
Checking client NIC speed (Option A): While important, incorrect NIC speed wouldn’t affect the ability to obtain an IP address from DHCP.
Checking NTP server (Option B): Time synchronization is unrelated to DHCP issues.
Authorizing the DHCP server (Option D): This is essential for DHCP operation, but since this is an existing DHCP cluster, the helper address is more likely the issue. CompTIA Server+
Reference: This topic is related to SK0-005 Objective 1. 2: Manage server network connections.
Two developers are working together on a project, and they have built out a set of snared servers that both developers can access over the internet.
Which of the following cloud models is this an example of?
- A . Hybrid
- B . Public
- C . Private
- D . Community
B
Explanation:
A public cloud is a cloud model that provides shared resources and services over the internet to multiple users or organizations. The cloud provider owns and manages the infrastructure and charges users based on their usage or subscription. A public cloud can offer scalability, flexibility, and cost-efficiency for users who need access to various applications and data without investing in their own hardware or software.
Verified Reference: [Public cloud], [Cloud model]
