Practice Free SK0-005 Exam Online Questions
A company’s security team has noticed employees seem to be blocking the door in the main data center when they are working on equipment to avoid having to gain access each time.
Which of the following should be implemented to force the employees to enter the data center properly?
- A . A security camera
- B . A mantrap
- C . A security guard
- D . A proximity card
B
Explanation:
A mantrap is a security device that consists of two interlocking doors that allow only one person to enter at a time. A mantrap would prevent employees from blocking the door in the main data center and force them to enter properly using their credentials. The other options would not enforce proper entry to the data center
A technician has moved a data drive from a new Windows server to an order Windows server. The hardware recognizes the drive, but the data is not visible to the OS.
Which of the following is the MOST Likely cause of the issue?
- A . The disk uses GPT.
- B . The partition is formatted with ext4.
- C . The -partition is formatted with FAT32.
- D . The disk uses MBn.
A
Explanation:
GPT (GUID Partition Table) is a partitioning scheme that allows creating partitions on large hard drives (more than 2 TB). It supports up to 128 partitions per drive and uses 64-bit addresses to locate them. However, GPT is not compatible with older versions of Windows, such as Windows XP or Windows Server 2003, which use MBR (Master Boot Record) as the partitioning scheme. If a disk uses GPT, it may not be recognized or accessible by an older Windows server.
Verified Reference: [GPT], [MBR]
A server administrator receives the following output when trying to ping a local host:
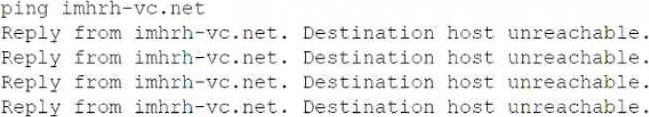
Which of the following is MOST likely the issue?
- A . Firewall
- B . DHCP
- C . DNS
- D . VLAN
A
Explanation:
A firewall is a network device or software that filters and controls the incoming and outgoing traffic based on predefined rules. A firewall can block or allow certain types of packets, ports, protocols, or IP addresses. The output of the ping command shows that the local host is unreachable, which means that there is no network connectivity between the source and the destination. This could be caused by a firewall that is blocking the ICMP (Internet Control Message Protocol) packets that ping uses to test the connectivity.
Reference: https://www.comptia.org/training/resources/exam-objectives/comptia-server-sk0-005-exam-objectives (Objective 2.2)
A server room with many racks of servers is managed remotely with occasional on-site support.
Which of the following would be the MOST cost-effective option to administer and troubleshoot network problems locally on the servers?
- A . Management port
- B . Crash cart
- C . IP KVM
- D . KVM
C
Explanation:
An IP KVM (keyboard, video, mouse) is a device that allows remote access and control of multiple servers over a network using a web browser or a client software. An IP KVM is a cost-effective option to administer and troubleshoot network problems locally on the servers, as it eliminates the need for physical presence or dedicated hardware for each server. A management port (A) is a network interface that is used for out-of-band management of network devices, such as routers or switches. A management port does not provide local access to servers. A crash cart (B) is a mobile unit that contains a monitor, keyboard, mouse, and other tools for troubleshooting servers in a data center. A crash cart requires physical access to each server and may not be cost-effective for many racks of servers. A KVM (D) is a device that allows switching between multiple servers using a single keyboard, video, and mouse. A KVM does not provide remote access over a network and requires physical connection to each server.
Reference: https://www.enterprisestorageforum.com/management/best-data-storage-solutions-and-software-2021/
https://www.microsoft.com/en-us/microsoft-365/business-insights-ideas/resources/cloud-storage-vs-on-premises-servers
A server administrator is replacing a faulty PSU. The management team has asked for a solution that prevents further downtime in the future.
Which of the following can the server administrator
implement?
- A . Separate circuits
- B . Load balancing
- C . Server monitoring
- D . Redundancy
D
Explanation:
A faulty PSU needs replacement, and the management team wants a solution to prevent future downtime.
Solution: Implement redundancy (Option D):
Redundant power supplies ensure that if one fails, the other takes over seamlessly.
Separate circuits, load balancing, and server monitoring are important but do not directly prevent PSU failures.
Reference: CompTIA Server+ Guide, Chapter 3: Hardware, Section 3.2.2 (Redundant Power Supplies)
An administrator gave Ann modify permissions to a shared folder called DATA, which is located on the company server. Other users need read access to the files in this folder.
The current configuration is as follows:
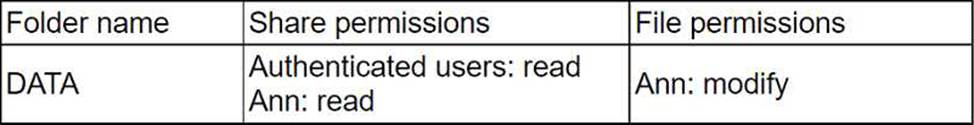
The administrator has determined Ann cannot write anything to the DATA folder using the network.
Which of the following would be the best practice to set up Ann’s permissions correctly, exposing only the minimum rights required?
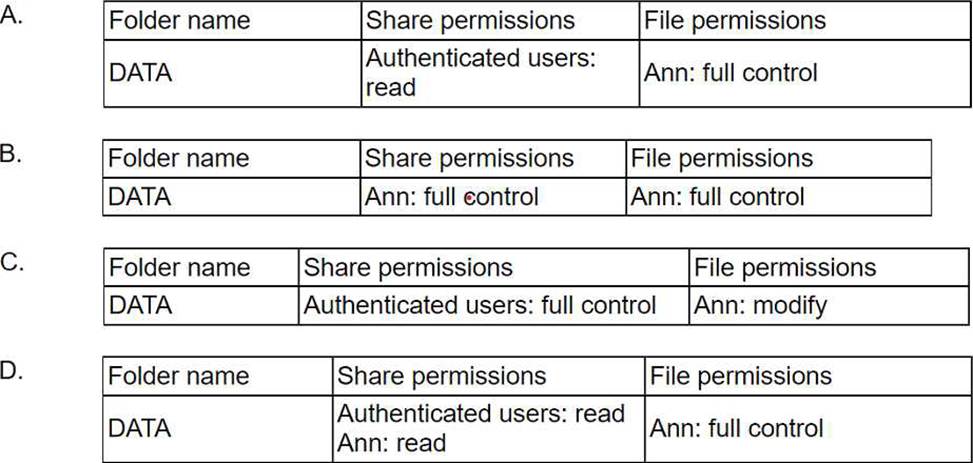
- A . Option A
- B . Option B
- C . Option C
- D . Option D
D
Explanation:
Option D is the best practice to set up Ann’s permissions correctly, exposing only the minimum rights required. Option D shows that the share permissions on the DATA folder grant Ann Change access, which allows her to read, write, and delete files in the shared folder. The file permissions grant Ann Modify access, which allows her to read, write, execute, and delete files in the folder. This combination of permissions gives Ann the ability to write anything to the DATA folder using the network, as well as to modify and delete existing files. This meets the requirement of giving Ann modify permissions to the shared folder.
Which of the following documents would be useful when trying to restore IT infrastructure operations after a non-planned interruption?
- A . Service-level agreement
- B . Disaster recovery plan
- C . Business impact analysis
- D . Business continuity plan
B
Explanation:
A disaster recovery plan would be useful when trying to restore IT infrastructure operations after a non-planned interruption. A disaster recovery plan is a document that outlines the steps and procedures to recover from a major disruption of IT services caused by natural or man-made disasters, such as fire, flood, earthquake, cyberattack, etc.
A disaster recovery plan typically includes:
A list of critical IT assets and resources that need to be protected and restored
A list of roles and responsibilities of IT staff and stakeholders involved in the recovery process
A list of backup and recovery strategies and tools for data, applications, servers, networks, etc.
A list of communication channels and methods for notifying users, customers, vendors, etc. A list of testing and validation methods for ensuring the functionality and integrity of restored systems
A list of metrics and criteria for measuring the effectiveness and efficiency of the recovery process
A disaster recovery plan helps IT organizations to minimize downtime, data loss, and financial impact of a disaster, as well as to resume normal operations as quickly as possible.
Which of the following can be BEST described as the amount of time a company can afford to be down during recovery from an outage?
- A . SLA
- B . MTBF
- C . RTO
- D . MTTR
C
Explanation:
The term that best describes the amount of time a company can afford to be down during recovery from an outage is RTO. RTO (Recovery Time Objective) is a metric that defines the maximum acceptable downtime for an application, system, or process after a disaster or disruption. RTO helps determine the level of urgency and resources required for restoring normal business operations. RTO is usually measured in minutes, hours, or days, depending on the criticality and impact of the service.
Reference: https://whatis.techtarget.com/definition/recovery-time-objective-RTO
A bad actor leaves a USB drive with malicious code on it in a company’s parking lot.
Which of the following describes this scenario?
- A . Hacking
- B . Insider threat
- C . Phishing
- D . Social engineering
D
Explanation:
Leaving a USB drive in a company parking lot is a classic example of social engineering, where the bad actor relies on human curiosity to prompt someone to pick up the USB drive and insert it into their computer, potentially infecting the system with malicious code.
Social engineering (Answer D): The attacker manipulates human behavior (in this case, curiosity) to exploit security weaknesses.
Hacking (Option A): Hacking refers to directly breaching security systems or exploiting software vulnerabilities, not manipulating humans.
Insider threat (Option B): This involves a legitimate insider within the organization carrying out malicious activities, which isn’t the case here.
Phishing (Option C): Phishing typically involves emails or messages designed to deceive individuals
into providing sensitive information.
CompTIA Server+
Reference: This topic is covered under SK0-005 Objective 4.2: Explain server security concepts and best practices.
Which of the following DR testing scenarios is described as verbally walking through each step of the DR plan in the context of a meeting?
- A . Live failover
- B . Simulated failover
- C . Asynchronous
- D . Tabletop
D
Explanation:
The DR testing scenario that is described as verbally walking through each step of the DR plan in the context of a meeting is tabletop. A tabletop test is a type of disaster recovery (DR) test that involves discussing and reviewing the DR plan with key stakeholders and participants in a simulated scenario. A tabletop test does not involve any actual execution of the DR plan or any disruption of the normal operations. A tabletop test can help identify gaps, issues, or inconsistencies in the DR plan and improve communication and coordination among the DR team members.
