Practice Free SK0-005 Exam Online Questions
An upper management team is investigating a security breach of the company’s filesystem. It has been determined that the breach occurred within the human resources department.
Which of the following was used to identify the breach in the human resources department?
- A . User groups
- B . User activity reports
- C . Password policy
- D . Multifactor authentication
B
Explanation:
User activity reports were used to identify the security breach in the human resources department. User activity reports are records of the actions and events performed by users on a system or network, such as login/logout times, files accessed or modified, commands executed, or websites visited. User activity reports can help monitor and audit user behavior, detect and investigate security incidents, and enforce policies and compliance. User activity reports can be generated by various tools, such as log management software, security information and event management (SIEM) systems, or user and entity behavior analytics (UEBA) solutions.
Reference: [CompTIA Server+ Certification Exam Objectives], Domain 5.0: Security, Objective 5.2: Given a scenario, apply logical access control methods.
A company is reviewing options for its current disaster recovery plan and potential changes to it. The security team will not allow customer data to egress to non-company equipment, and the company has requested recovery in the shortest possible time.
Which of the following will BEST meet these goals?
- A . A warm site
- B . A hot site
- C . Cloud recovery
- D . A cold site
B
Explanation:
A hot site is a type of disaster recovery site that has all the equipment and data ready to resume operations as soon as possible after a disaster. A hot site is usually located in a different geographic area than the primary site and has redundant power, cooling, network, and security systems. A hot site is best for the company that wants to recover in the shortest possible time and does not want customer data to egress to non-company equipment. A warm site is a type of disaster recovery site that has some equipment and data ready, but requires some configuration and restoration before resuming operations. A cold site is a type of disaster recovery site that has only basic infrastructure and space available, but requires significant setup and installation before resuming operations. Cloud recovery is a type of disaster recovery service that uses cloud-based resources and platforms to store backups and restore data and applications after a disaster.
Reference:
https://www.techopedia.com/definition/11172/hot-site
https://www.techopedia.com/definition/11173/warm-site
https://www.techopedia.com/definition/11174/cold-site
https://www.techopedia.com/definition/29836/cloud-recovery
A systems administrator is setting up a new server that will be used as a DHCP server. The administrator installs the OS but is then unable to log on using Active Directory credentials. The administrator logs on using the local administrator account and verifies the server has the correct IP address, subnet mask, and default gateway. The administrator then gets on another server and can ping the new server.
Which of the following is causing the issue?
- A . Port 443 is not open on the firewall
- B . The server is experiencing a downstream failure
- C . The local hosts file is blank
- D . The server is not joined to the domain
D
Explanation:
The server is not joined to the domain is causing the issue. A domain is a logical grouping of computers that share a common directory database and security policy on a network. Active Directory is a Microsoft technology that provides domain services for Windows-based computers. To use Active Directory credentials to log on to a server, the server must be joined to the domain that hosts Active Directory. If the server is not joined to the domain, it will not be able to authenticate with Active Directory and will only accept local accounts for logon. To join a server to a domain, the administrator must have a valid domain account with sufficient privileges and must know the name of the domain controller that hosts Active Directory.
A technician is able to copy a Me to a temporary folder on another partition but is unable to copy it to a network share or a USB flash drive.
Which of the following is MOST likely preventing the file from being copied to certain locations?
- A . An ACL
- B . Antivirus
- C . DLP
- D . A firewall
C
Explanation:
DLP (Data Loss Prevention) is a security measure that prevents unauthorized copying, transferring, or leaking of sensitive data from a server or a network. It can block or alert the user when they try to copy a file to certain locations, such as a network share or a USB flash drive, based on predefined policies and rules.
Verified Reference: [DLP], [Data loss]
Users cannot access a new server by name, but the server does respond to a ping request using its IP address. All the user workstations receive their IP information from a DHCP server.
Which of the following would be the best step to perform NEXT?
- A . Run the tracert command from a workstation.
- B . Examine the DNS to see if the new server record exists.
- C . Correct the missing DHCP scope.
- D . Update the workstation hosts file.
B
Explanation:
If users cannot access a new server by name, but the server does respond to a ping request using its IP address, it means that there is a problem with name resolution. The DNS (Domain Name System) is a service that maps hostnames to IP addresses and vice versa. Therefore, the best step to perform next is to examine the DNS to see if the new server record exists and matches its IP address. If not, the DNS record needs to be added or updated accordingly. Running the tracert command from a workstation would not help with name resolution, as it only shows the route taken by packets to reach a destination by IP address. Correcting the missing DHCP scope would not help either, as DHCP (Dynamic Host Configuration Protocol) only assigns IP addresses and other network settings to clients, but does not resolve names. Updating the workstation hosts file would be a temporary workaround, but not a permanent solution, as it would require manually editing every workstation’s hosts file with the new server’s name and IP address.
Reference: https://www.howtogeek.com/164981/how-to-use-nslookup-to-check-domain-name-information-in-microsoft-windows/ https://www.howtogeek.com/howto/27350/beginner-geek-how-to-edit-your-hosts-file/
Which of the following factors would most likely impact the selection of an organization’s cloud provider?
- A . Industry standards
- B . Government regulations
- C . Company policy
- D . Organizational procedures
B
Explanation:
Government regulations often dictate the legal requirements for data storage, privacy, and security, which can greatly impact the selection of a cloud provider. Compliance with regulations like GDPR, HIPAA, or other local laws is critical when choosing a cloud provider to avoid legal repercussions.
Government regulations (Answer B): Cloud providers must comply with legal and regulatory requirements, making this a significant factor in provider selection.
Industry standards (Option A): While important, standards can be more flexible and are often not legally binding.
Company policy (Option C): Internal policies are important but usually stem from the need to comply with regulations.
Organizational procedures (Option D): Procedures help guide operations but don’t typically dictate
the choice of cloud providers.
CompTIA Server+
Reference: This topic is covered under SK0-005 Objective 1. 6: Explain the importance of cloud-based concepts and services.
A technician needs to set up a server backup method for some systems. The company’s management team wants to have quick restores but minimize the amount of backup media required.
Which of the following are the BEST backup methods to use to support the management’s priorities? (Choose two.)
- A . Differential
- B . Synthetic full
- C . Archive
- D . Full
- E . Incremental
- F . Open file
AE
Explanation:
The best backup methods to use to support the management’s priorities are differential and incremental. A backup is a process of copying data from a source to a destination for the purpose of restoring it in case of data loss or corruption. There are different types of backup methods that vary in terms of speed, efficiency, and storage requirements. Differential and incremental backups are two types of partial backups that only copy the data that has changed since the last full backup. A full backup is a type of backup that copies all the data from the source to the destination. A full backup provides the most complete and reliable restore option, but it also takes the longest time and requires the most storage space. A differential backup copies only the data that has changed since the last full backup. A differential backup provides a faster restore option than an incremental backup, but it also takes more time and requires more storage space than an incremental backup. An incremental backup copies only the data that has changed since the last backup, whether it was a full or an incremental backup. An incremental backup provides the fastest and most efficient backup option, but it also requires multiple backups to restore the data completely.
A server is performing slowly, and users are reporting issues connecting to the application on that
server. Upon investigation, the server administrator notices several unauthorized services running on
that server that are successfully communicating to an external site.
Which of the following are MOST likely causing the issue? (Choose two.)
- A . Adware is installed on the users’ devices
- B . The firewall rule for the server is misconfigured
- C . The server is infected with a virus
- D . Intrusion detection is enabled on the network
- E . Unnecessary services are disabled on the server
- F . SELinux is enabled on the server
CB
Explanation:
The server is infected with a virus and SELinux is enabled on the server are most likely causing the issue of unauthorized services running on the server. A virus is a type of malicious software that infects a system and performs unwanted or harmful actions, such as creating, modifying, deleting, or executing files. A virus can also create backdoors or open ports on a system to allow remote access or communication with external sites. SELinux (Security-Enhanced Linux) is a security module for Linux systems that enforces mandatory access control policies on processes and files. SELinux can prevent unauthorized services from running on a server by restricting their access to resources based on their security context. However, SELinux can also cause problems if it is not configured properly or if it conflicts with other security tools.
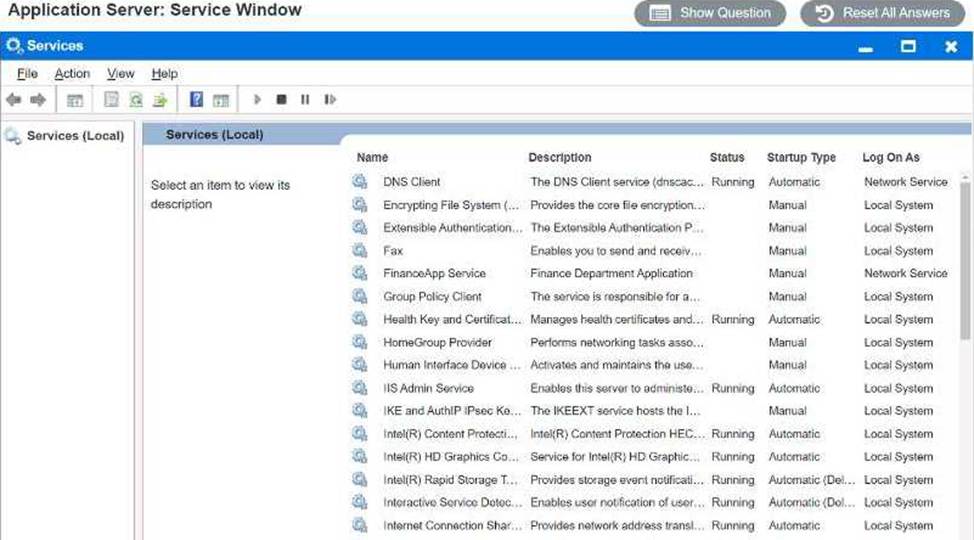
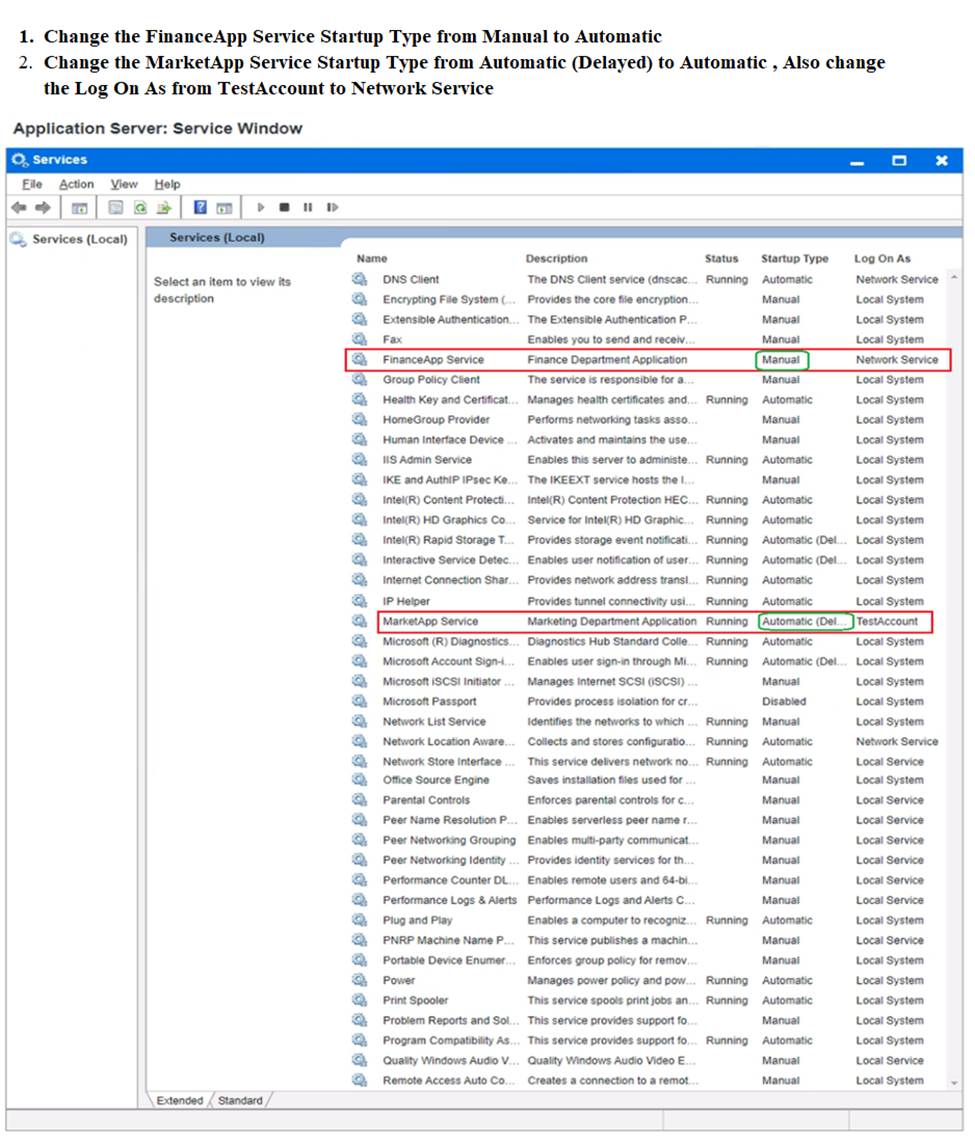
Users report that the FinanceApp software is not running, and they need immediate access. Issues with the FinanceApp software occur every week after the IT team completes server system updates. The users, however, do not want to contact the help desk every time the issue occurs. The users also report the new MarketApp software is not usable when it crashes, which can cause significant downtime. The technician who restarted the MarketApp software noticed it is running under a test account, which is a likely cause of the crashes.
INSTRUCTIONS
Using the Services menu provided, modify the appropriate application services to remedy the stated issues.
Winch of the following is a type of replication in which all files are replicated, all the time?
- A . Constant
- B . Application consistent
- C . Synthetic full
- D . Full
A
Explanation:
Constant replication is a type of replication in which all files are replicated, all the time. Replication is a process of copying data from one location to another for backup, recovery, or distribution purposes. Constant replication is also known as real-time replication or synchronous replication. It ensures that any changes made to the source data are immediately reflected on the target data without any delay or lag. Constant replication provides high availability and consistency, but it requires high bandwidth and low latency. Application consistent replication is a type of replication that ensures that the replicated data is consistent with the state of the application that uses it. It involves quiescing or pausing the application before taking a snapshot of the data and resuming the application after the snapshot is taken. Application consistent replication provides better recovery point objectives than crash consistent replication, which does not quiesce the application before taking a snapshot. Synthetic full replication is a type of replication that involves creating a new full backup by using the previous full backup and related incremental backups. It reduces the backup window and network bandwidth consumption by transferring only changed data from the source to the target. Full replication is a type of replication that involves copying all data from the source to the target regardless of whether it has changed or not. It provides a complete backup of the data, but it
requires more storage space and network bandwidth than incremental or differential replication.
Reference:
https://www.howtogeek.com/199068/how-to-upgrade-your-existing-hard-drive-in-under-an-hour/
https://www.howtogeek.com/202794/what-is-the-difference-between-127.0.0.1-and-0.0.0.0/
https://www.howtogeek.com/443611/how-to-encrypt-your-macs-system-drive-removable-devices-and-individual-files/
