Practice Free SC-100 Exam Online Questions
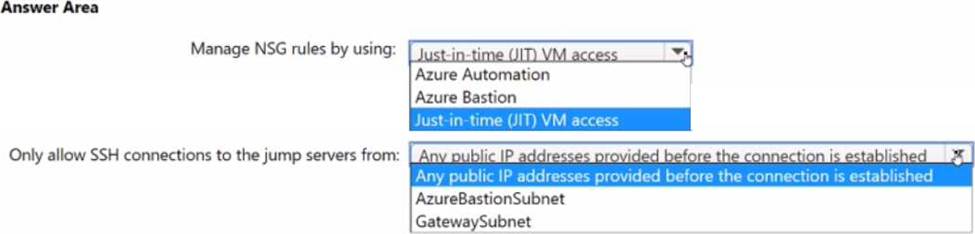
HOTSPOT
You plan to deploy a dynamically scaling, Linux-based Azure Virtual Machine Scale Set that will host jump servers. The jump servers will be used by support staff who connect f personal and kiosk devices via the internet. The subnet of the jump servers will be associated to a network security group (NSG)
You need to design an access solution for the Azure Virtual Machine Scale Set.
The solution must meet the following requirements:
• Ensure that each time the support staff connects to a jump server; they must request access to the server.
• Ensure that only authorized support staff can initiate SSH connections to the jump servers.
• Maximize protection against brute-force attacks from internal networks and the internet.
• Ensure that users can only connect to the jump servers from the internet.
• Minimize administrative effort
What should you include in the solution? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
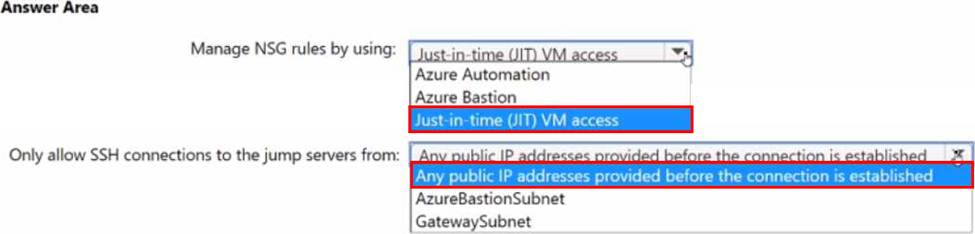
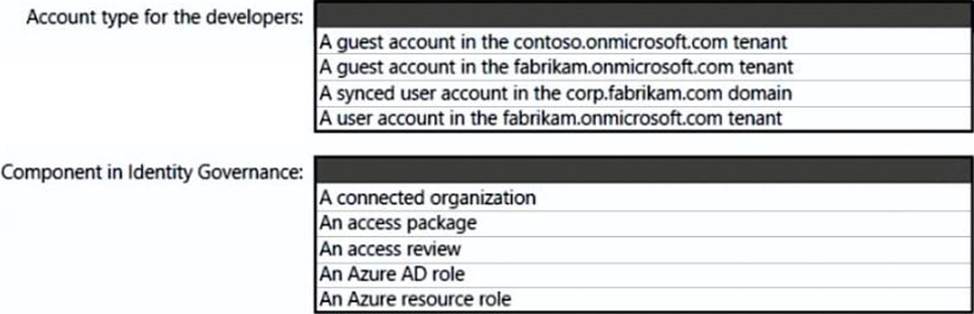
HOTSPOT
What should you create in Azure AD to meet the Contoso developer requirements?
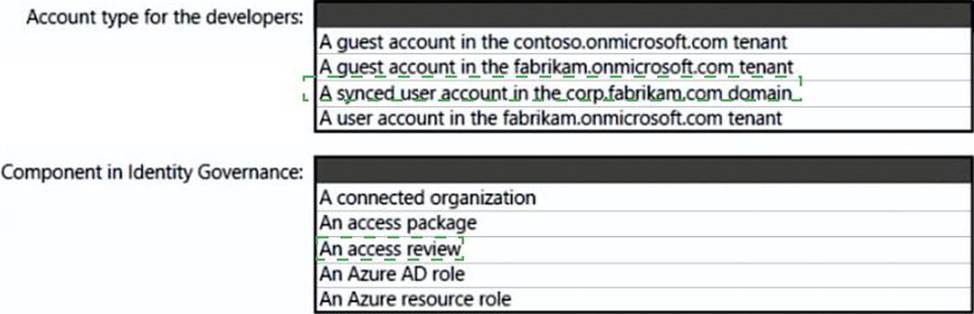
Explanation:
Box 1: A synced user account –
Need to use a synched user account.
Box 2: An access review
https://docs.microsoft.com/en-us/azure/active-directory-domain-services/synchronization
https://docs.microsoft.com/en-us/azure/active-directory/governance/access-reviews-overview
Your company is developing an invoicing application that will use Azure Active Directory (Azure AD) B2C. The application will be deployed as an App Service web app. You need to recommend a solution to the application development team to secure the application from identity related attacks.
Which two configurations should you recommend? Each correct answer presents part of the solution. NOTE: Each correct selection is worth one point.
- A . Azure AD Conditional Access integration with user flows and custom policies
- B . Azure AD workbooks to monitor risk detections
- C . custom resource owner password credentials (ROPC) flows in Azure AD B2C
- D . access packages in Identity Governance
- E . smart account lockout in Azure AD B2C
A, E
Explanation:
https://docs.microsoft.com/en-us/azure/active-directory-b2c/threat-management
https://docs.microsoft.com/en-us/azure/active-directory-b2c/conditional-access-user-flow?pivots=b2c-user-flow
Topic 1, Fabrikam, Inc Case Study 1
OverView
Fabrikam, Inc. is an insurance company that has a main office in New York and a branch office in Paris.
On-premises Environment
The on-premises network contains a single Active Directory Domain Services (AD DS) domain named corp.fabrikam.com.
Azure Environment
Fabrikam has the following Azure resources:
• An Azure Active Directory (Azure AD) tenant named fabrikam.onmicrosoft.com that syncs with corp.fabnkam.com
• A single Azure subscription named Sub1
• A virtual network named Vnetl in the East US Azure region
• A virtual network named Vnet2 in the West Europe Azure region
• An instance of Azure Front Door named FD1 that has Azure Web Application Firewall (WAR enabled
• A Microsoft Sentinel workspace
• An Azure SQL database named ClaimsDB that contains a table named ClaimDetails
• 20 virtual machines that are configured as application servers and are NOT onboarded to Microsoft Defender for Cloud
• A resource group named TestRG that is used for testing purposes only
• An Azure Virtual Desktop host pool that contains personal assigned session hosts
All the resources in Sub1 are in either the East US or the West Europe region.
Partners
Fabrikam has contracted a company named Contoso, Ltd. to develop applications.
Contoso has the following infrastructure-.
• An Azure AD tenant named contoso.onmicrosoft.com
• An Amazon Web Services (AWS) implementation named ContosoAWS1 that contains AWS EC2 instances used to host test workloads for the applications of Fabrikam Developers at Contoso will connect to the resources of Fabrikam to test or update applications. The developers will be added to a security Group named Contoso Developers in fabrikam.onmicrosoft.com that will be assigned to roles in Sub1.
The ContosoDevelopers group is assigned the db.owner role for the ClaimsDB database.
Compliance Event
Fabrikam deploys the following compliance environment:
• Defender for Cloud is configured to assess all the resources in Sub1 for compliance to the HIPAA HITRUST standard.
• Currently, resources that are noncompliant with the HIPAA HITRUST standard are remediated manually.
• Qualys is used as the standard vulnerability assessment tool for servers.
Problem Statements
The secure score in Defender for Cloud shows that all the virtual machines generate the following recommendation-. Machines should have a vulnerability assessment solution. All the virtual machines must be compliant in Defender for Cloud.
ClaimApp Deployment
Fabrikam plans to implement an internet-accessible application named ClaimsApp that will have the following specification
• ClaimsApp will be deployed to Azure App Service instances that connect to Vnetl and Vnet2.
• Users will connect to ClaimsApp by using a URL of https://claims.fabrikam.com.
• ClaimsApp will access data in ClaimsDB.
• ClaimsDB must be accessible only from Azure virtual networks.
• The app services permission for ClaimsApp must be assigned to ClaimsDB.
Application Development Requirements
Fabrikam identifies the following requirements for application development:
• Azure DevTest labs will be used by developers for testing.
• All the application code must be stored in GitHub Enterprise.
• Azure Pipelines will be used to manage application deployments.
• All application code changes must be scanned for security vulnerabilities, including application code or configuration files that contain secrets in clear text. Scanning must be done at the time the code is pushed to a repository.
Security Requirement
Fabrikam identifies the following security requirements:
• Internet-accessible applications must prevent connections that originate in North Korea.
• Only members of a group named InfraSec must be allowed to configure network security groups (NSGs} and instances of Azure Firewall, VJM. And Front Door in Sub1.
• Administrators must connect to a secure host to perform any remote administration of the virtual machines. The secure host must be provisioned from a custom operating system image.
AWS Requirements
Fabrikam identifies the following security requirements for the data hosted in ContosoAWSV.
• Notify security administrators at Fabrikam if any AWS EC2 instances are noncompliant with secure score recommendations.
• Ensure that the security administrators can query AWS service logs directly from the Azure environment.
Contoso Developer Requirements
Fabrikam identifies the following requirements for the Contoso developers;
• Every month, the membership of the ContosoDevelopers group must be verified.
• The Contoso developers must use their existing contoso.onmicrosoft.com credentials to access the resources in Sub1.
• The Comoro developers must be prevented from viewing the data in a column named MedicalHistory in the ClaimDetails table.
Compliance Requirement
Fabrikam wants to automatically remediate the virtual machines in Sub1 to be compliant with the HIPPA HITRUST standard. The virtual machines in TestRG must be excluded from the compliance assessment.
You need to recommend a solution to meet the security requirements for the InfraSec group.
What should you use to delegate the access?
- A . a subscription
- B . a custom role-based access control (RBAC) role
- C . a resource group
- D . a management group
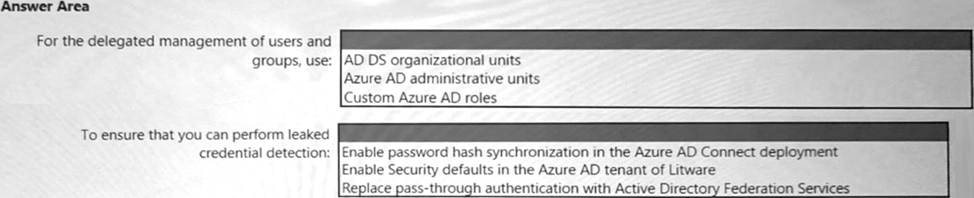
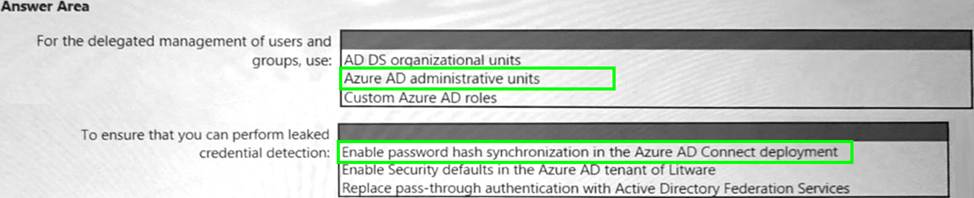
HOTSPOT
You need to recommend an identity security solution for the Azure AD tenant of Litware. The solution must meet the identity requirements and the regulatory compliance requirements.
What should you recommend? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
You have an Azure subscription that contains several storage accounts. The storage accounts are accessed by legacy applications that are authenticated by using access keys.
You need to recommend a solution to prevent new applications from obtaining the access keys of the storage accounts. The solution must minimize the impact on the legacy applications.
What should you include in the recommendation?
- A . Apply read-only locks on the storage accounts.
- B . Set the AllowSharcdKeyAccess property to false.
- C . Set the AllowBlobPublicAcccss property to false.
- D . Configure automated key rotation.
A
Explanation:
https://docs.microsoft.com/en-us/azure/azure-resource-manager/management/lock-resources
Your company has a hybrid cloud infrastructure that contains an on-premises Active Directory Domain Services (AD DS) forest, a Microsoft B65 subscription, and an Azure subscription.
The company’s on-premises network contains internal web apps that use Kerberos authentication.
Currently, the web apps are accessible only from the network.
You have remote users who have personal devices that run Windows 11.
You need to recommend a solution to provide the remote users with the ability to access the web apps.
The solution must meet the following requirements:
• Prevent the remote users from accessing any other resources on the network.
• Support Azure Active Directory (Azure AD) Conditional Access.
• Simplify the end-user experience.
What should you include in the recommendation?
- A . Azure AD Application Proxy
- B . Azure Virtual WAN
- C . Microsoft Tunnel
- D . web content filtering in Microsoft Defender for Endpoint
A
Explanation:
https://docs.microsoft.com/en-us/learn/modules/configure-azure-ad-application-proxy/2-explore
Your company plans to evaluate the security of its Azure environment based on the principles of the Microsoft Cloud Adoption Framework for Azure.
You need to recommend a cloud-based service to evaluate whether the Azure resources comply with the National Institute of Standards and Technology (NIST) Cybersecurity Framework (CSF).
What should you recommend?
- A . Compliance Manager in Microsoft Purview
- B . Microsoft Defender for Cloud
- C . Microsoft Sentinel
- D . Microsoft Defender for Cloud Apps
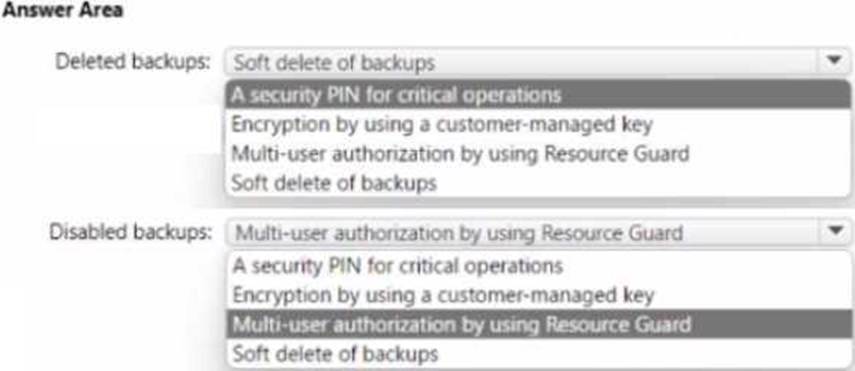
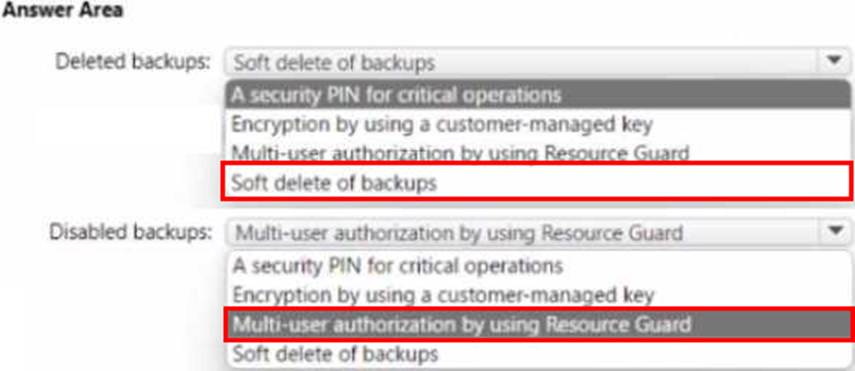
HOTSPOT
You have an Azure subscription and an on-premises datacenter. The datacenter contains 100 servers that run Windows Server. AJI the servers are backed up to a Recovery Services vault by using Azure Backup and the Microsoft Azure Recovery Services (MARS) agent.
You need to design a recovery solution for ransomware attacks that encrypt the on-premises servers.
The solution must follow Microsoft Security Best Practices and protect against the following risks:
• A compromised administrator account used to delete the backups from Azure Backup before encrypting the servers
• A compromised administrator account used to disable the backups on the MARS agent before encrypting the servers
What should you use for each risk? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point
You have a Microsoft Entra tenant named contoso.com.
You have a partner company that has a multi-tenant application named App1. App1 is registered to a Microsoft Entra tenant named fabnkam.com.
You need to ensure that the users in contoso.com can authenticate to App1.
What should you recommend creating in contoso.com?
- A . a service principal
- B . a system-assigned managed identity
- C . an application object
- D . a user-assigned managed identity
