Practice Free NSE6_EDR_AD-7.0 Exam Online Questions
Refer to the exhibit.
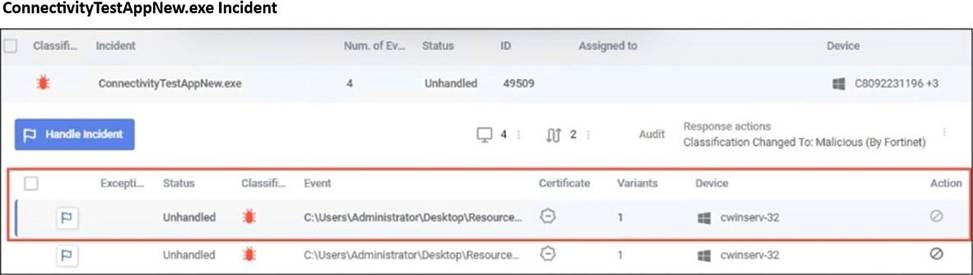
What observation can you make about the Connectivity TestAppNew.exe incident?
- A . The incident was archived from the console unhandled.
- B . A rule assigned action is set to block but the policy is in simulation mode.
- C . The incident was handled automatically by the communication control policy.
- D . The incident has not been handled by a console administrator.
D
Explanation:
The incident status in the incident handler view is clearly marked as Unhandled. This indicates that no console administrator has taken action to investigate, resolve, or close the incident from the FortiEDR management console.
What action does an on-premises reputation server take when it receives a hash request that is not found in its local database?
- A . Automatically blocks applications with unknown hashes
- B . Ignores them until manually updated
- C . Requests the missing hashes from the cloud reputation service
- D . Stores them locally and waits for endpoint input
C
Explanation:
When the on-premises reputation server receives a hash query that does not exist in its local database, it forwards the request to the FortiEDR cloud reputation service. The cloud service provides the reputation verdict for the hash, which is then returned to the requesting component and can also be cached locally for future queries.
You are asked to create a playbook to isolate a device with a collector.
Which action category does isolating a device with a collector fall under?
- A . Investigation
- B . Custom
- C . Notifications
- D . Remediation
D
Explanation:
Isolating a device is an automated response action used to contain a threat by restricting the endpoint’s network communication. In FortiEDR playbooks, containment and corrective actions such as isolating a device are categorized under remediation because they actively mitigate or stop malicious activity on the endpoint.
You added three new applications to FortiEDR using only the Path attribute.
What are two expected outcomes of this configuration? (Choose two.)
- A . These applications will be disabled until explicitly enabled.
- B . All instances of these applications will be blocked, regardless of location.
- C . These applications will be blocked only if the file name also matches.
- D . Only applications in the specified directory paths will be blocked.
C,D
Explanation:
When an application is defined using the Path attribute, the rule applies only to executables located in the specified directory path. FortiEDR identifies applications using attributes such as file name and path, so the block applies only when the executable file name also matches within that defined path.
An employee leaves the company and no longer has access to the FortiEDR system. You must ensure GDPR compliance regarding the employee’s personal data stored in FortiEDR.
Which two data types must be removed to meet GDPR requirements? (Choose two.)
- A . Installed applications
- B . Installed OS name
- C . Device and user name
- D . IP address and MAC address
C,D
Explanation:
GDPR requires the removal of personally identifiable information related to individuals. Device and user names can directly identify a specific employee, and network identifiers such as IP addresses and MAC addresses can also be linked to an individual device or user. These data elements must be removed to ensure compliance with GDPR requirements.
Refer to the exhibit.
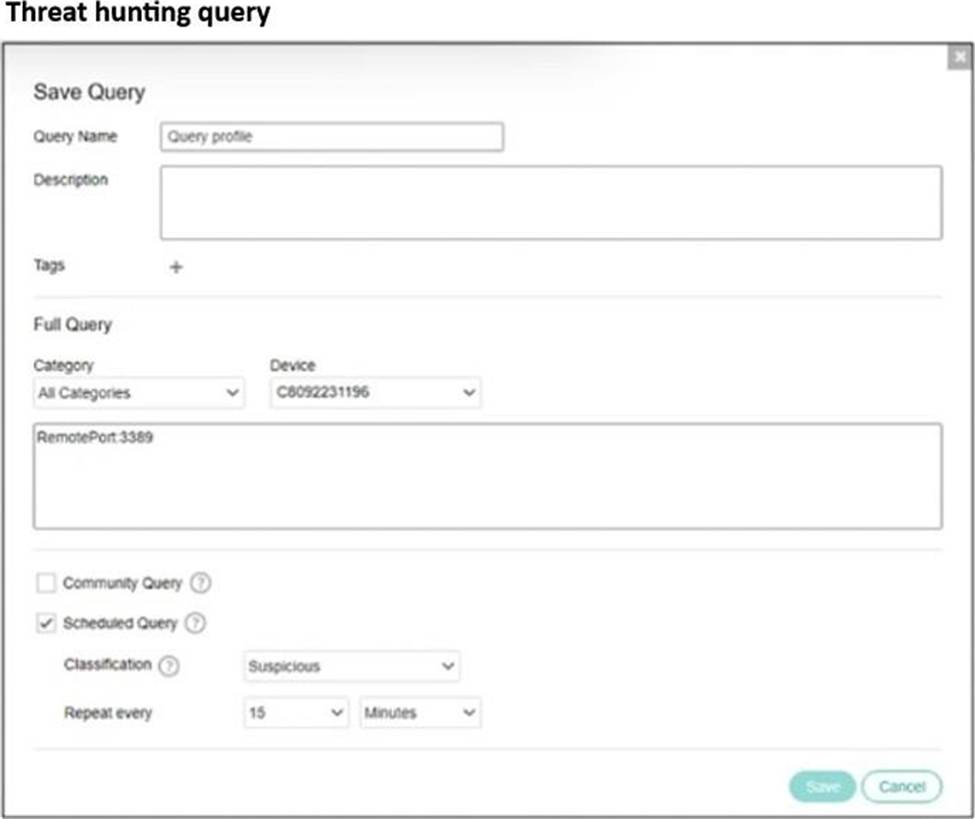
Based on the exhibit, which statement about this treat hunting query is true?
- A . RDP connections will be automatically blocked and classified as suspicious.
- B . A security incident will be generated whenever the device attempts an RDP connection.
- C . The query is limited to detecting network activity and does not inspect process behavior.
- D . The query is configured as a global hunting rule and is automatically visible across all organizations.
B
Explanation:
The query searches for network activity where the remote port is 3389, which corresponds to RDP traffic. The query is configured as a scheduled threat hunting query with a suspicious classification and runs repeatedly at a defined interval.
When the query condition is matched, FortiEDR generates a security event for that activity, resulting in a security incident being created when the device attempts an RDP connection.
You are asked to configure a query to run every 15 minutes, automatically searching for specific registry modifications across all endpoints.
Which FortiEDR feature must you configure?
- A . A communication control rule with a 15-minute delav
- B . A manual query linked to a policy override
- C . A new playbook trigger based on the registry change event
- D . A scheduled query defined within a threat hunting profile
D
Explanation:
Scheduled queries in FortiEDR threat hunting profiles allow automated searches for specific indicators or behaviors across endpoints at defined intervals. By configuring a scheduled query with a 15-minute recurrence, the system continuously scans for the specified registry modification activity across all endpoints.
Which two statements correctly describe the IoT probing process on FortiEDR? (Choose two.)
- A . Collectors running on servers are always used for IoT probing.
- B . It identifies nearby devices by retrieving details such as hostname and IP address
- C . Only healthy collectors participate in loT probing.
- D . It captures all traffic from neighboring devices for deep packet inspection.
B,C
Explanation:
The IoT probing process identifies nearby devices on the network by gathering basic information such as hostname and IP address to build visibility of unmanaged or IoT devices. Only collectors that are healthy and functioning properly participate in the probing process to ensure reliable discovery and accurate device information.
Refer to the exhibit.
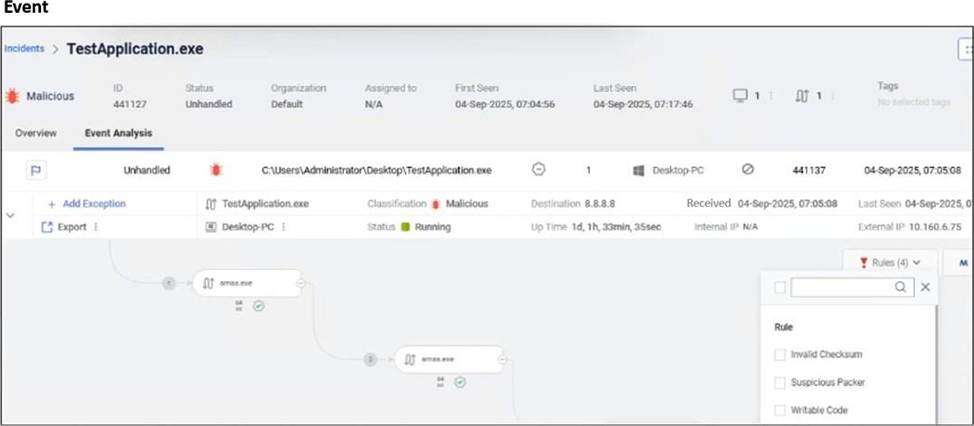
Based on the event shown in the exhibit, which two statements about the event are true? (Choose two.)
- A . The user was able to launch TestApplication.exe
- B . The event is marked as Handled.
- C . FCS classified the event as malicious.
D TestApplication.exe is sophisticated malware.
A,C
Explanation:
The event view shows the process TestApplication.exe with status Running, indicating the application was successfully launched on the endpoint. The classification label indicates the event is marked as malicious and the classification source is FortinetCloud Services, confirming that FCS performed the malicious classification.
A collector attempts to access a known malicious website. FortiEDR is configured for eXtended detection with FortiAnalyzer.
What two roles does Fortinet Cloud Services (FCS) perform in this process? (Choose two.)
- A . FCS sends a log record to FortiAnalyzer.
- B . FCS sends OS metadata to the FortiEDR manager.
- C . FCS identifies if a malicious event has taken place and reports the detection incident.
- D . FCS correlates and analyzes the collected logs.
C,D
Explanation:
Fortinet Cloud Services performs advanced cloud-based analysis of events collected from endpoints and integrated systems. It correlates and analyzes the collected logs and telemetry to determine malicious activity. After identifying that a malicious event has occurred, it classifies the event and reports the detection incident back to the FortiEDR system.
