Practice Free CV0-004 Exam Online Questions
A cloud solutions architect is designing a VM-based solution that requires reducing the cost as much as possible.
Which of the following solutions will best satisfy this requirement?
- A . Using ephemeral storage on replicated VMs
- B . Creating Spot VMs in one availability zone
- C . Spreading the VMs across different regions
- D . Using provisioned IOPS storage
B
Explanation:
Using Spot VMs is a cost-effective solution as these are available at significantly reduced prices compared to standard instances. Spot VMs are ideal for workloads that can tolerate interruptions and are a way to take advantage of unused cloud capacity.
Reference: The concept of Spot VMs and their cost benefits are included in the financial aspects of managing cloud resources, as per the CompTIA Cloud+ certification guidelines.
A cloud server needs to automatically allocate more resources during sudden peak times. This allocation does not need to occur in regular intervals.
Which of the following scaling approaches should be used?
- A . Event
- B . Manual
- C . Trending
- D . Scheduled
A
Explanation:
Event-based scaling is designed to allocate more resources automatically in response to specific events, such as sudden peak times that are not regular or predictable. This type of scaling ensures that resources are available when needed without the need to schedule them in advance or adjust them manually.
Reference: CompTIA Cloud+ Guide to Cloud Computing (ISBN: 978-1-64274-282-2)
A company has decided to adopt a microservices architecture for its applications that are deployed to the cloud.
Which of the following is a major advantage of this type of architecture?
- A . Increased security
- B . Simplified communication
- C . Reduced server cost
- D . Rapid feature deployment
D
Explanation:
A major advantage of adopting a microservices architecture is rapid feature deployment. Microservices allow for independent development, deployment, and scaling of individual service components, enabling teams to bring new features to market more quickly and efficiently compared to monolithic architectures.
Reference: The CompTIA Cloud+ certification covers cloud design aspects, including architectural models like microservices, emphasizing their role in facilitating agile development practices and rapid feature release cycles in cloud environments.
The PMO wants to streamline the routing and approval of project activities to provide up-to-date visibility of the status.
Which of the following collaboration tools would be most appropriate to use?
- A . Real-time, multi-authoring tool
- B . Wiki knowledge base and search engine
- C . Workflow and e-signature platform
- D . File-sharing platform and storage system
C
Explanation:
A workflow and e-signature platform automates approvals, routing, and visibility of project tasks. This ensures that documents and activities are approved quickly and transparently, supporting operational efficiency. Real-time editing or file storage doesn’t inherently provide workflow automation.
Reference: CompTIA Project+ PK0-005 C Collaboration & Approval Tools; CompTIA Cloud+ CV0-004 Operations & Support domain.
A company experienced a data leak through its website.
A security engineer, who is investigating the issue, runs a vulnerability scan against the website and receives the following output:
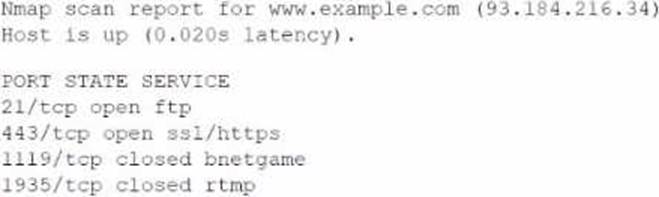
Which of the following is the most likely cause of this leak?
- A . RTMP port open
- B . SQL injection
- C . Privilege escalation
- D . Insecure protocol
D
Explanation:
The data leak is most likely caused by the use of an insecure protocol. The vulnerability scan output shows that port 21/tcp for FTP (File Transfer Protocol) is open. FTP is known for transmitting data unencrypted, which could allow sensitive data to be intercepted during transfer.
Reference: The security risks associated with the use of insecure or unencrypted protocols are covered under cloud security best practices in the CompTIA Cloud+ curriculum.
A company experienced a data leak through its website.
A security engineer, who is investigating the issue, runs a vulnerability scan against the website and receives the following output:
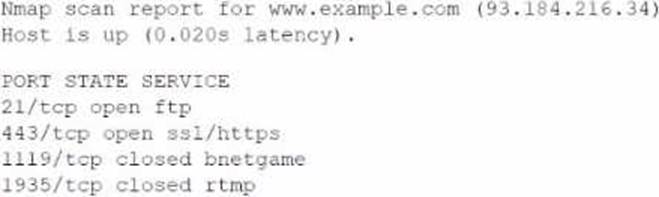
Which of the following is the most likely cause of this leak?
- A . RTMP port open
- B . SQL injection
- C . Privilege escalation
- D . Insecure protocol
D
Explanation:
The data leak is most likely caused by the use of an insecure protocol. The vulnerability scan output shows that port 21/tcp for FTP (File Transfer Protocol) is open. FTP is known for transmitting data unencrypted, which could allow sensitive data to be intercepted during transfer.
Reference: The security risks associated with the use of insecure or unencrypted protocols are covered under cloud security best practices in the CompTIA Cloud+ curriculum.
A network administrator is budding a site-to-site VPN tunnel from the company’s headquarters office 10 the company’s public cloud development network. The network administrator confirms the following:
The VPN tunnel is established on the headquarter office firewall.
While inside the office, developers report that they cannot connect to the development network resources.
While outside the office on a client VPN, developers report that they can connect to the development network resources.
The office and the client VPN have different IP subnet ranges.
The firewall flow logs show VPN traffic is reaching the development network from the office.
Which of the following is the next step the next network administrator should take to troubleshoot the VPN tunnel?
- A . Review the development network routing table.
- B . Change the ciphers on the site-to-site VPN.
- C . Restart the site-to-site VPN tunnel.
- D . Check the ACLS on the development workloads
A
Explanation:
The next step in troubleshooting the VPN tunnel issue is to review the development network routing table. This action will help determine if the routing configurations are correctly directing traffic from the headquarters office through the VPN tunnel to the development network resources. Proper routing ensures that data packets find their way to the correct destination within the cloud environment, which is critical for establishing successful communication between different network segments.
Reference: CompTIA Cloud+ materials stress the importance of networking fundamentals in cloud environments, including VPN configurations and routing, to ensure secure and efficient connectivity between on-premises infrastructure and cloud resources.
Which of the following cloud deployment models is the best way to replicate a workload non-disruptively between on-premises servers and a public cloud?
- A . Public
- B . Community
- C . Private
- D . Hybrid
D
Explanation:
A hybrid cloud deployment model is the best way to replicate workloads non-disruptively between on-premises servers and a public cloud. This model integrates on-premises infrastructure, or private clouds with public clouds, allowing data and applications to be shared between them.
Reference: CompTIA Cloud+ Study Guide (Exam CV0-004) – Chapter on Cloud Deployment Models
A software engineer is integrating an application lo The cloud that is web socket based.
Which of the following applications is the engineer most likely deploying?
- A . Image-sharing
- B . Data visualization
- C . Chat
- D . File transfer
C
Explanation:
A chat application is most likely to be deployed when integrating a web socket-based application to the cloud. Web sockets provide full-duplex communication channels over a single, long-lived connection, which is ideal for real-time applications like chat services that require persistent connections between the client and server for instant data exchange.
Reference: CompTIA Cloud+ materials cover cloud networking concepts, emphasizing the importance of choosing the right technologies, like web sockets, for specific application requirements to ensure efficient and responsive cloud-based services.
A company wants to implement a work environment that will have low operational overhead and highly accessible enterprise resource planning, email, and data resources.
Which of the following cloud service models should the company implement?
- A . laaS
- B . PaaS
- C . DBaaS
- D . SaaS
D
Explanation:
A company that requires low operational overhead and highly accessible enterprise resources would benefit from implementing Software as a Service (SaaS). SaaS provides access to applications hosted in the cloud, eliminating the need for internal infrastructure or application development, which aligns with the requirement of having low operational overhead.
Reference: CompTIA Cloud+ Study Guide (Exam CV0-004) by Todd Montgomery and Stephen Olson
