Practice Free CV0-004 Exam Online Questions
The project manager must create a project charter.
Which of the following should be included in the charter?
- A . Project schedule
- B . Resource allocation
- C . Risk plan
- D . Stakeholder identification
D
Explanation:
The project charter is a high-level authorization document that outlines the purpose, objectives, and identifies key stakeholders. It does not contain detailed schedules, risk management plans, or resource allocation ― those come later in the planning process.
Reference: CompTIA Project+ PK0-005 C Project Initiation & Charter Development; CompTIA Cloud+ CV0-004 Governance & Compliance domain.
A cloud consultant needs to modernize a legacy application that can no longer address user demand and is expensive to maintain.
Which of the following is the best migration strategy?
- A . Retain
- B . Rehost
- C . Refactor
- D . Replatform
C
Explanation:
Refactoring is the process of restructuring existing computer code without changing its external behavior. In cloud computing, it often means modifying the application to better leverage cloud-native features and services. This can address user demand and reduce maintenance costs by making the application more scalable, resilient, and manageable.
Reference: CompTIA Cloud+ Certification Study Guide (Exam CV0-004) by Scott Wilson and Eric Vanderburg
A developer is deploying a new version of a containerized application.
The DevOps team wants:
• No disruption
• No performance degradation * Cost-effective deployment
• Minimal deployment time
Which of the following is the best deployment strategy given the requirements?
- A . Canary
- B . In-place
- C . Blue-green
- D . Rolling
C
Explanation:
The blue-green deployment strategy is the best given the requirements for no disruption, no performance degradation, cost-effective deployment, and minimal deployment time. It involves maintaining two identical production environments (blue and green), where one hosts the current application version and the other is used to deploy the new version. Once testing on the green environment is complete, traffic is switched from blue to green, ensuring a seamless transition with no downtime.
Reference: Understanding various cloud deployment strategies, such as blue-green deployments, is essential for managing cloud environments effectively, as highlighted in the CompTIA Cloud+ objectives, to ensure smooth and efficient application updates.
Which of the following provides secure, private communication between cloud environments
without provisioning additional hardware or appliances?
- A . VPN
- B . VPC peering
- C . BGP
- D . Transit gateway
B
Explanation:
VPC peering provides secure, private communication between cloud environments without the need for provisioning additional hardware or appliances. It allows direct network connectivity between two Virtual Private Clouds (VPCs), enabling resources in either VPC to communicate with each other using private IP addresses.
Reference: Cloud networking options such as VPC peering and its benefits are included in the networking concepts of cloud environments in the CompTIA Cloud+ certification.
A software engineer needs to transfer data over the internet using programmatic access while also being able to query the data.
Which of the following will best help the engineer to complete this task?
- A . SQL
- B . Web sockets
- C . RPC
- D . GraphQL
D
Explanation:
GraphQL is the best option for transferring data over the internet with programmatic access and querying capabilities. It is a query language for APIs and a runtime for executing those queries with existing data, providing a more efficient, powerful, and flexible alternative to the REST API.
Reference: Data transfer and querying methods are part of the technical knowledge associated with cloud computing, as included in CompTIA Cloud+.
A company recently migrated to a public cloud provider. The company’s computer incident response team needs to configure native cloud services tor detailed logging.
Which of the following should the team implement on each cloud service to support root cause analysis of past events? {Select two).
- A . Log retention
- B . Tracing
- C . Log aggregation
- D . Log rotation
- E . Hashing
- F . Encryption
A, C
Explanation:
For detailed logging to support root cause analysis of past events, the team should implement log retention to ensure logs are kept for the necessary amount of time and log aggregation to compile logs from various sources for easier analysis and correlation.
Reference: Log management practices, including retention and aggregation, are part of the cloud management strategies covered in the CompTIA Cloud+ curriculum, particularly in the domain of technical operations.
A developer at a small startup company deployed some code for a new feature to its public repository. A few days later, a data breach occurred. A security team investigated the incident and found that the database was hacked.
Which of the following is the most likely cause of this breach?
- A . Database core dump
- B . Hard-coded credentials
- C . Compromised deployment agent
- D . Unpatched web servers
B
Explanation:
Hard-coded credentials within code, especially when deployed in a public repository, are a common security vulnerability. If credentials such as passwords or API keys are embedded in the code, anyone with access to the repository can potentially use them to gain unauthorized access to databases or other sensitive resources. This is a likely cause of the data breach in the scenario described.
Reference: CompTIA Security+ Guide to Network Security Fundamentals by Mark Ciampa.
Which of the following models will best reduce the cost of running short-term, non-critical workloads?
- A . Reserved
- B . Spot Instance
- C . Pay-as-you-go
- D . Dedicated host
An administrator needs to adhere to the following requirements when moving a customer’s data to the cloud:
• The new service must be geographically dispersed.
• The customer should have local access to data
• Legacy applications should be accessible.
Which of the following cloud deployment models is most suitable?
- A . On-premises
- B . Private
- C . Hybrid
- D . Public
C
Explanation:
A hybrid cloud deployment model is most suitable given the requirements. This model combines on-premises infrastructure (or private cloud) with public cloud services, providing geographic dispersion while allowing local access to data. It also facilitates the use of legacy applications that might not be well-suited for a full public cloud environment.
Reference: The hybrid model is a fundamental concept within the CompTIA Cloud+ curriculum, under the section of Cloud Concepts, that explains deployment models.
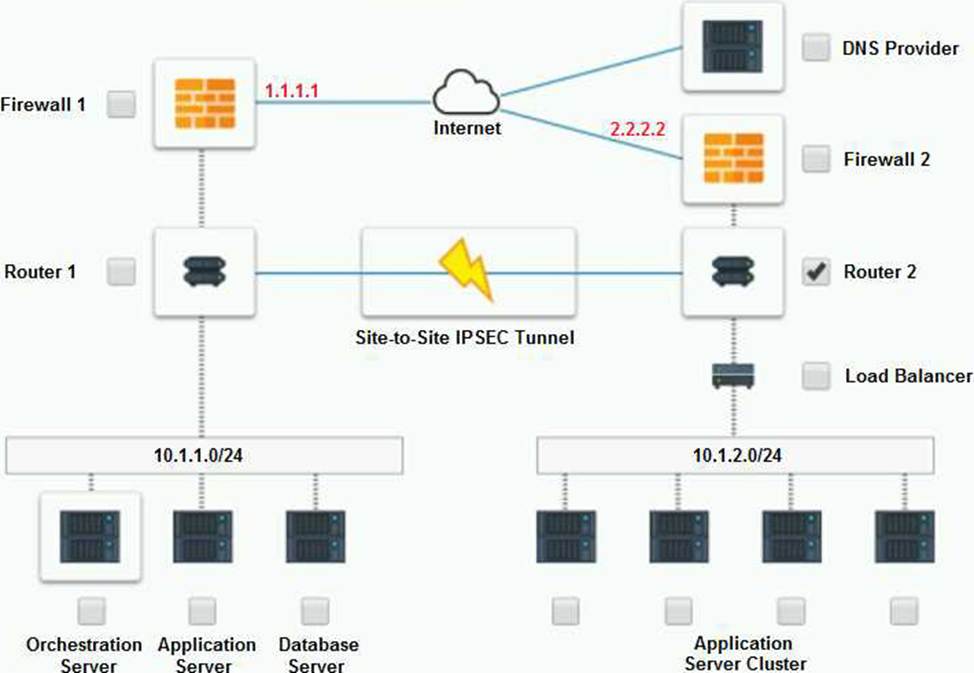
A company has decided to scale its e-commerce application from its corporate datacenter to a commercial cloud provider to meet an anticipated increase in demand during an upcoming holiday.
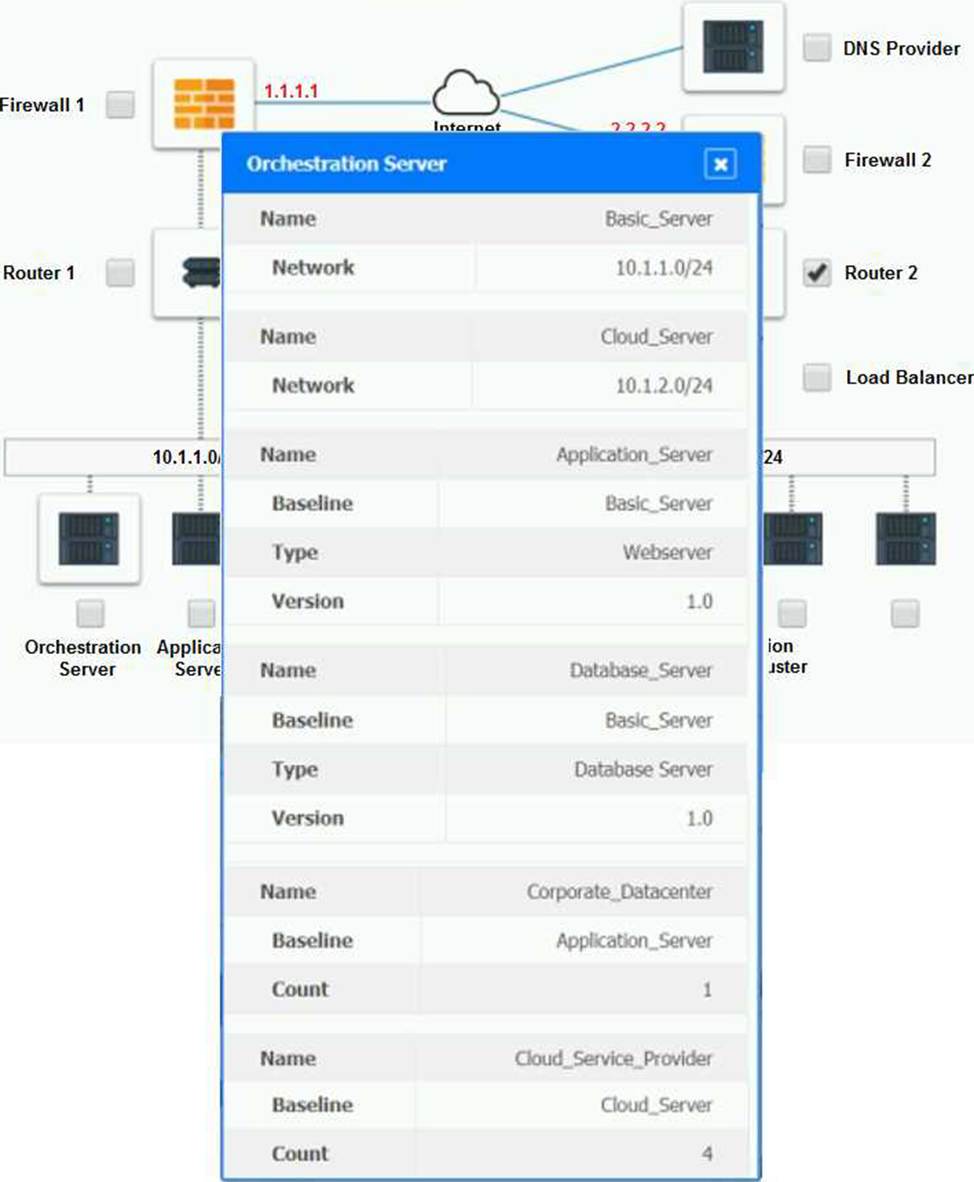
The majority of the application load takes place on the application server under normal conditions. For this reason, the company decides to deploy additional application servers into a commercial cloud provider using the on-premises orchestration engine that installs and configures common software and network configurations.
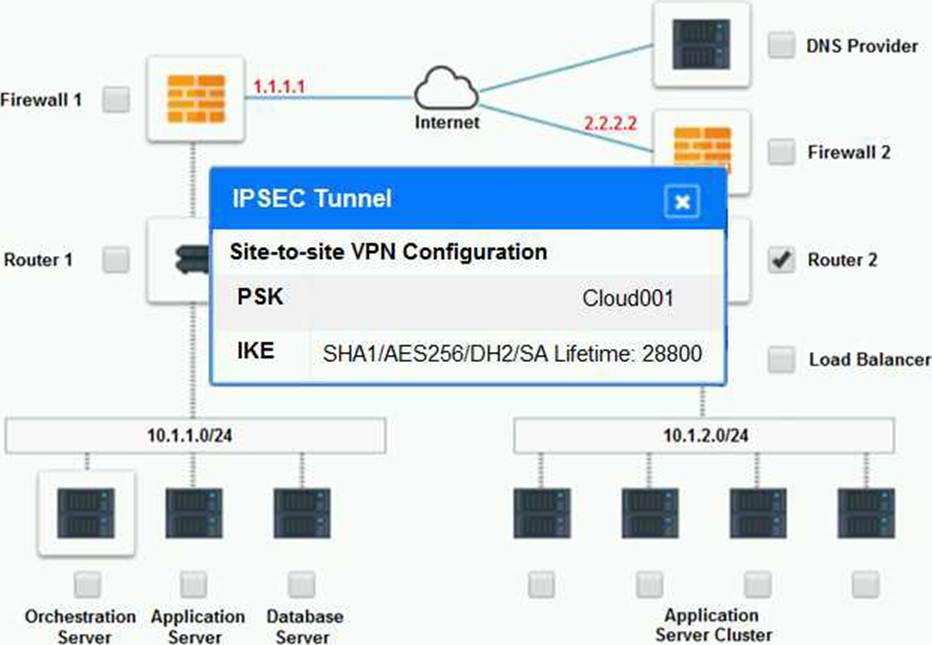
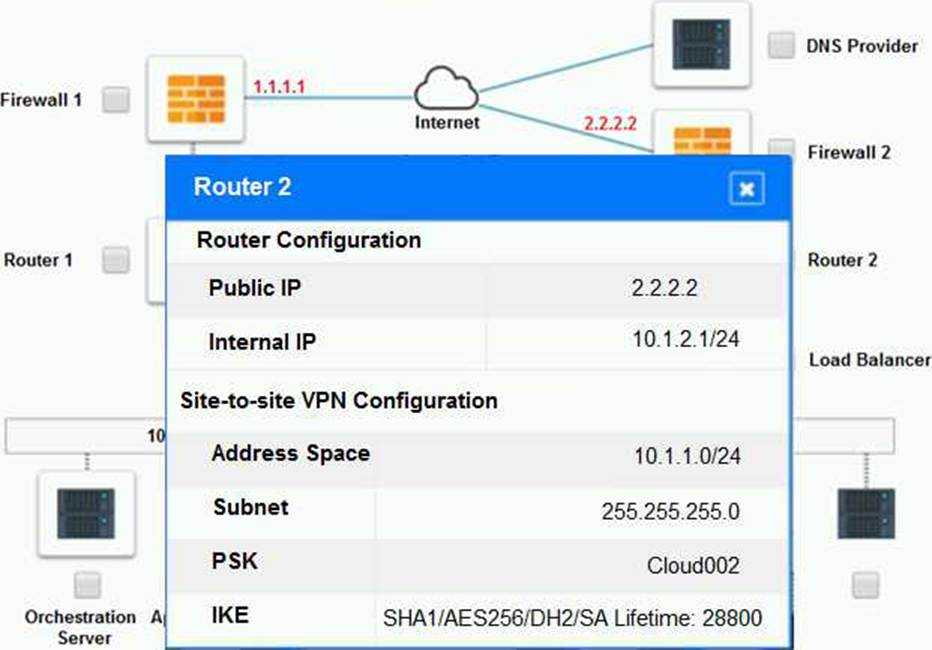
The remote computing environment is connected to the on-premises datacenter via a site-to-site
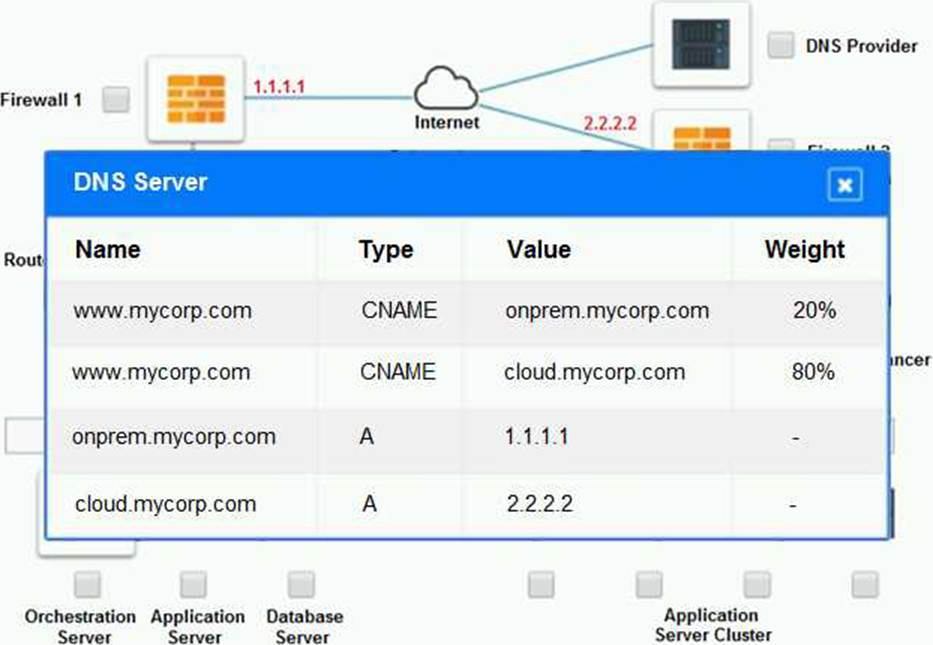
IPSec tunnel. The external DNS provider has been configured to use weighted round-robin routing to load balance connections from the Internet.
During testing, the company discovers that only 20% of connections completed successfully.
INSTRUCTIONS
Review the network architecture and supporting documents and fulfill these requirements:
Part 1:
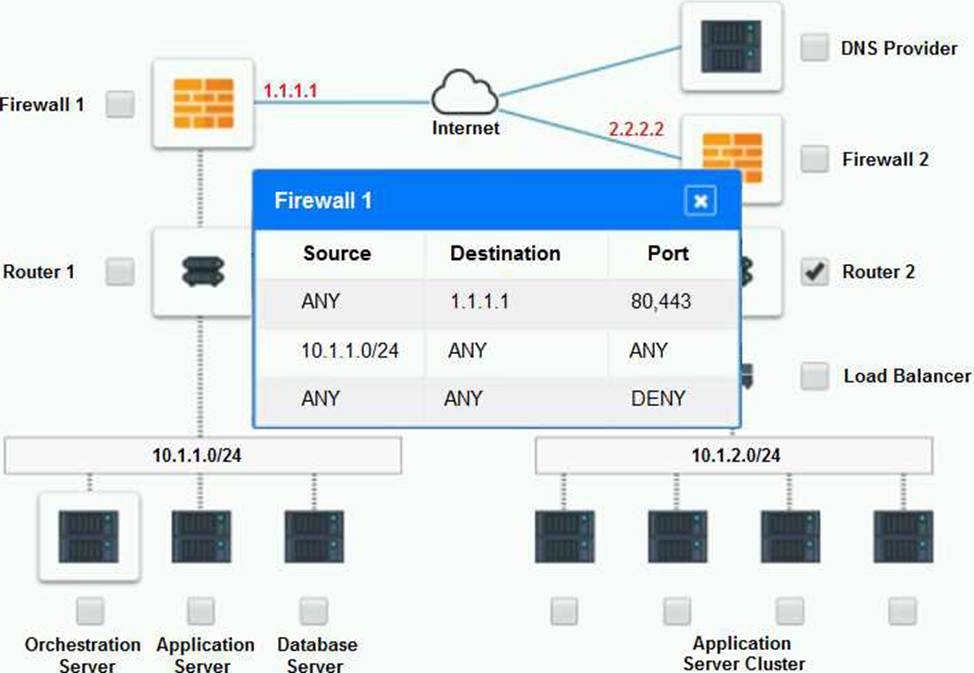
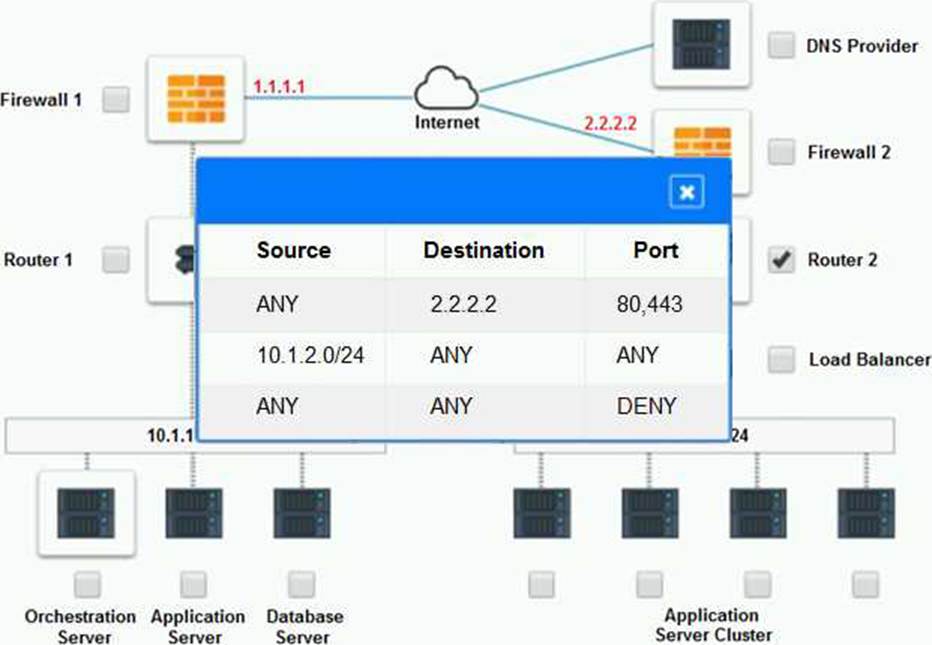
– Analyze the configuration of the following components: DNS, Firewall 1, Firewall 2, Router 1, Router 2, VPN and Orchestrator Server.
– Identify the problematic device(s).
Part 2:
– Identify the correct options to provide adequate configuration for hybrid cloud architecture.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
Part 1:
Cloud Hybrid Network Diagram

Part 2:
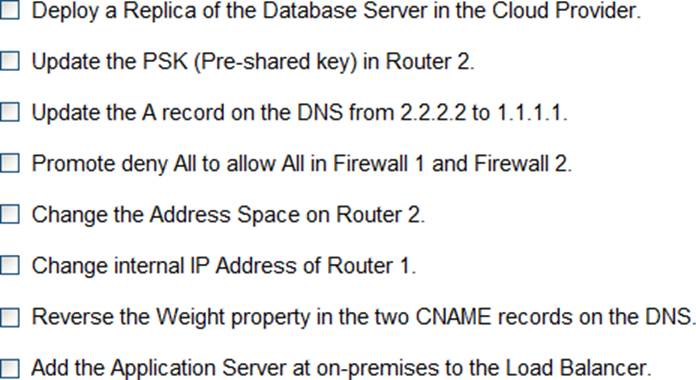
Only select a maximum of TWO options from the multiple choice question
The problematic device is Router 2, which has an incorrect configuration for the IPSec tunnel. The IPSec tunnel is a secure connection between the on-premises datacenter and the cloud provider, which allows the traffic to flow between the two networks. The IPSec tunnel requires both endpoints to have matching parameters, such as the IP addresses, the pre-shared key (PSK), the encryption and authentication algorithms, and the security associations (SAs).
According to the network diagram and the configuration files, Router 2 has a different PSK and a different address space than Router 1. Router 2 has a PSK of “1234567890”, while Router 1 has a PSK of “0987654321”. Router 2 has an address space of 10.0.0.0/8, while Router 1 has an address space of 192.168.0.0/16. These mismatches prevent the IPSec tunnel from establishing and encrypting the traffic between the two networks.
The other devices do not have any obvious errors in their configuration. The DNS provider has two CNAME records that point to the application servers in the cloud provider, with different weights to balance the load. The firewall rules allow the traffic from and to the application servers on port 80 and port 443, as well as the traffic from and to the VPN server on port 500 and port 4500. The orchestration server has a script that installs and configures the application servers in the cloud provider, using the DHCP server to assign IP addresses.
Part 2:
The correct options to provide adequate configuration for hybrid cloud architecture are:
Update the PSK in Router 2.
Change the address space on Router 2.
These options will fix the IPSec tunnel configuration and allow the traffic to flow between the on-premises datacenter and the cloud provider. The PSK should match the one on Router 1, which is “0987654321”. The address space should also match the one on Router 1, which is 192.168.0.0/16.
B. Update the PSK (Pre-shared key in Router2)
E. Change the Address Space on Router2
