Practice Free 350-401 Exam Online Questions
What is a Type 1 hypervisor?
- A . runs directly on a physical server and depends on a previously installed operating system
- B . runs directly on a physical server and includes its own operating system
- C . runs on a virtual server and depends on an already installed operating system
- D . run on a virtual server and includes its own operating system.
A client device roams between wireless LAN controllers that are mobility peers, Both controllers have dynamic interface on the same client VLAN which type of roam is described?
- A . intra-VLAN
- B . inter-controller
- C . intra-controller
- D . inter-subnet
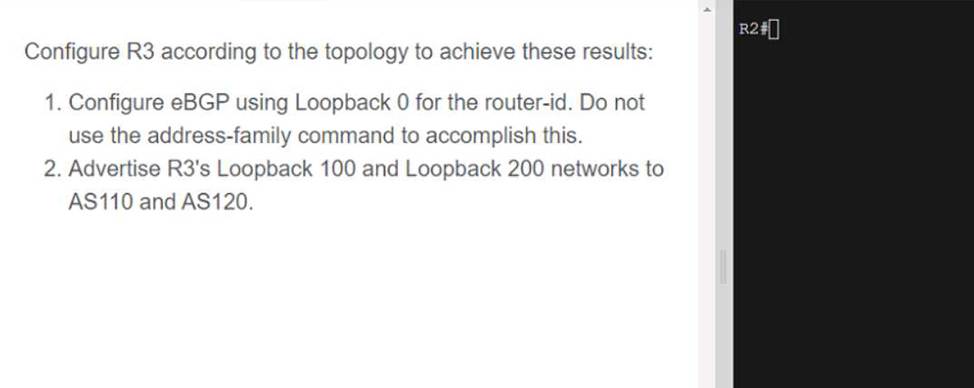
Refer to the exhibit.
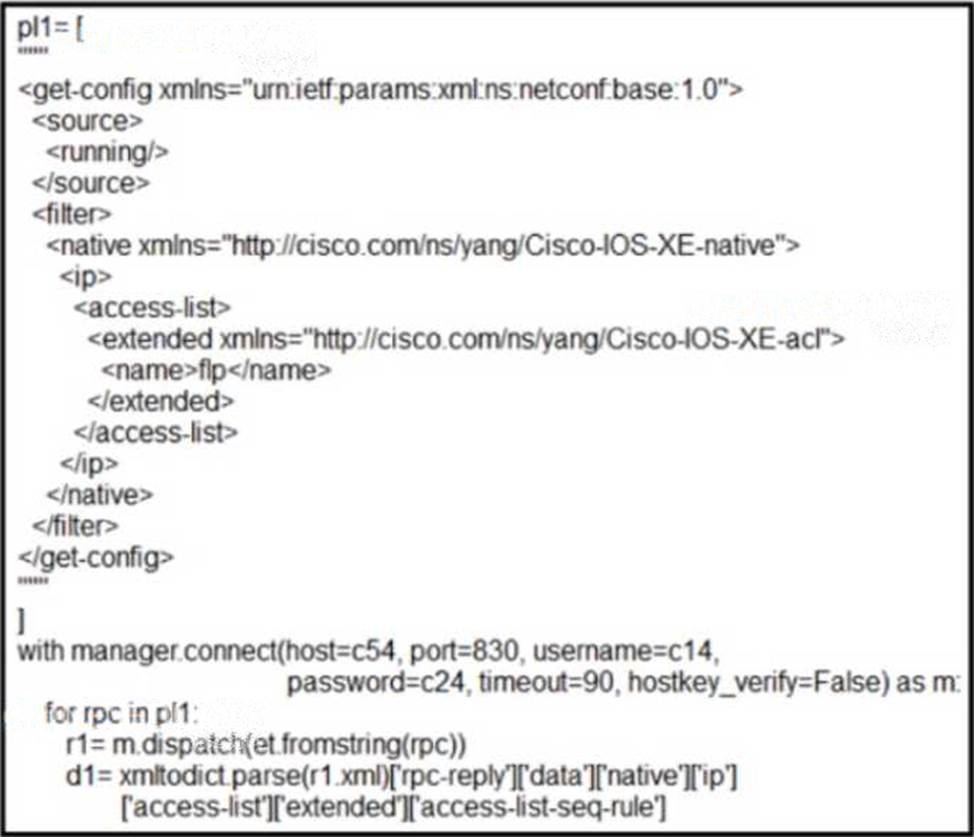
What is achieved by this Python script?
- A . It configures access list statements
- B . It reads access list statements into a dictionary list
- C . It displays access list statements on a terminal screen.
- D . It converts access list statements to a human-readable format.
Which HTTP status code is the correct response for a request with an incorrect password applied to a REST API session?
- A . HTTP Status Code 200
- B . HTTP Status Code 302
- C . HTTP Status Code 401
- D . HTTP Status Code: 504
What is one main REST security design principle?
- A . separation of privilege
- B . password hashing
- C . confidential algorithms
- D . OAuth
What is a characteristic of Layer 3 roaming?
- A . Clients must obtain a new IP address when they roam between APs.
- B . It provides seamless roaming between APs that are connected to different Layer 3 networks and different mobility groups.
- C . It is only supported on controllers that run SSO.
- D . It provides seamless client roaming between APs in different Layer 3 networks but within the same mobility group.
A wireless network engineer must configure a WPA2+WPA3 policy with the Personal security type.
Which action meets this requirement?
- A . Configure the GCMP256 encryption cipher.
- B . Configure the CCMP128 encryption cipher.
- C . Configure the GCMP128 encryption cipher.
- D . Configure the CCMP256 encryption cipher.
What is the purpose of a data modeling language?
- A . to establish a framework to process data by using an object-oriented programming approach
- B . to specify the rules for transcoding between text and binary data encodings
- C . to standardize the procedures that are executed when parsing sent and received data
- D . to describe the structure and meaning of exchanged data
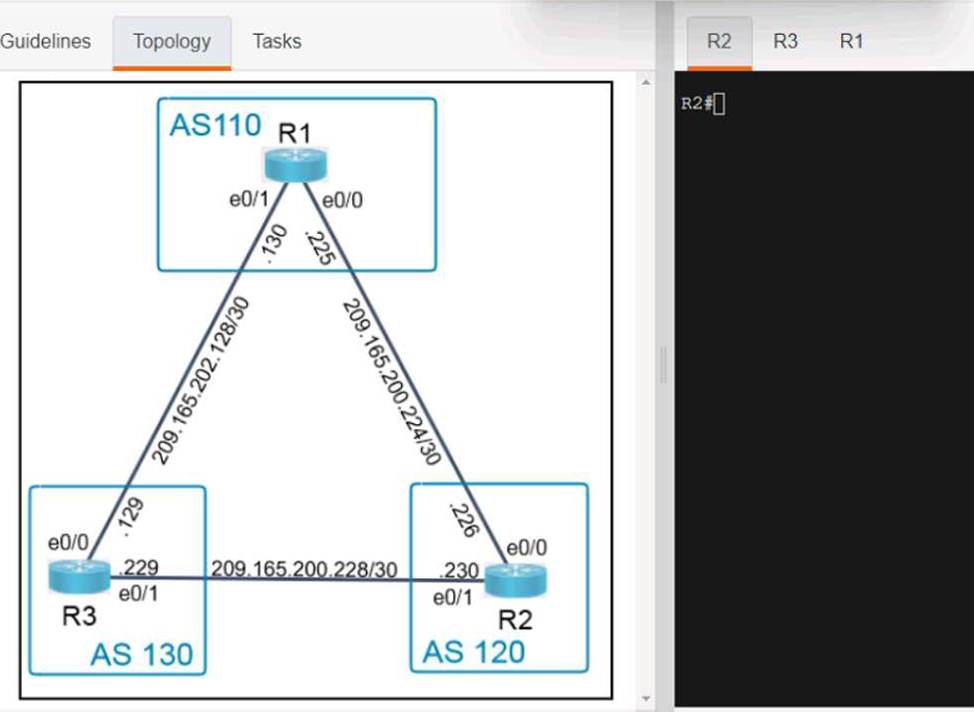
Refer to the exhibit.
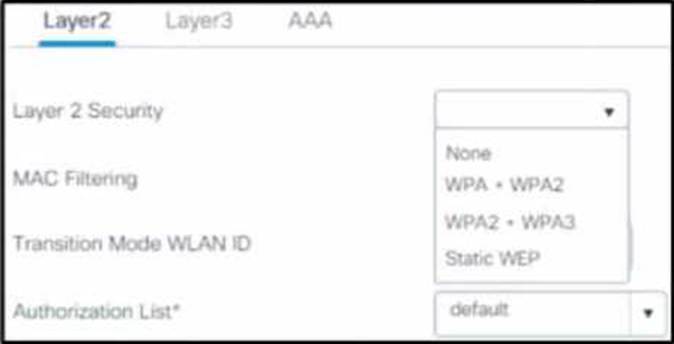
A client requests a new SSID that will use web-based authentication and external RADIUS servers.
Which Layer 2 security mode must be selected?
- A . Static WEP
- B . WPA2 + WPA3
- C . None
- D . WPA + WPA2