Practice Free 350-401 Exam Online Questions
Refer to the exhibit.
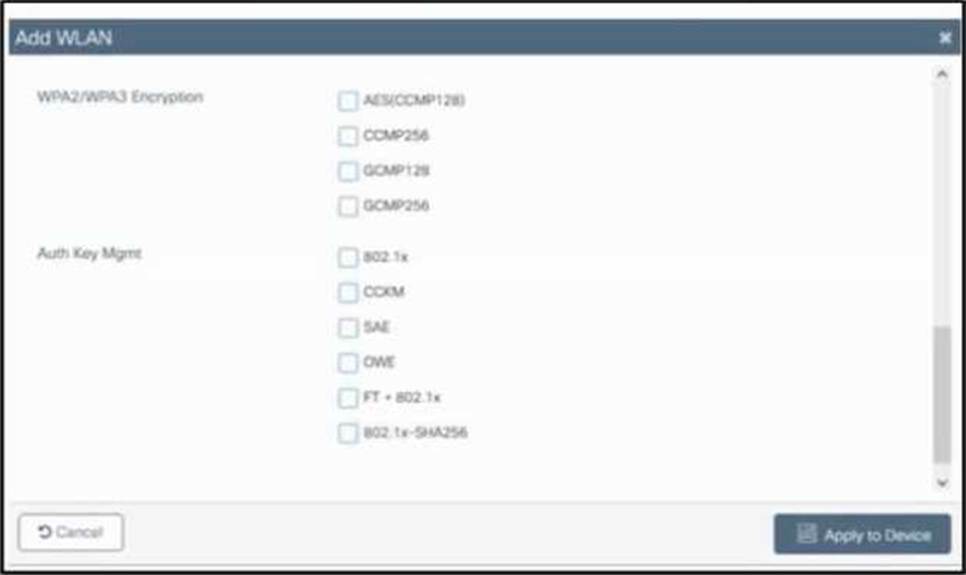
A customer asks an engineer to create a new secure WLAN to support only WPA3. Users must connect using a passphrase.
Which encryption and key management configuration is required?
- A . CCMP256 encryption with CCKM key management
- B . GCMP128 encryption with OWE key management
- C . CCMP128 encryption with SAE key management
- D . GCMP256 encryption with 802.1x key management
What is the function of the statement "import actions" in this script?
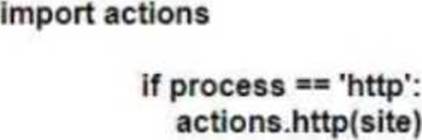
- A . It imports the functions that are not available natively in Python
- B . It imports the functions of a third-party module
- C . It imports a Python module
- D . It imports an external reference
Which tag defines the properties to be applied to each specific WLAN?
- A . RF tag
- B . policy tag
- C . AP tag
- D . site tag
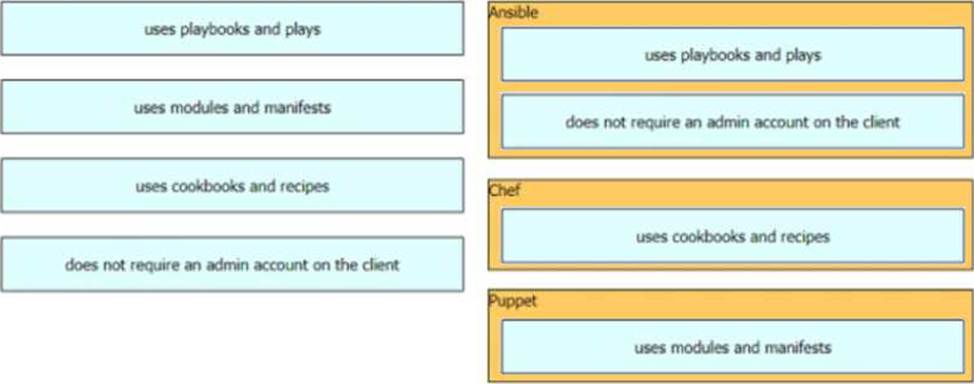
DRAG DROP
Drag and drop the automation characteristics from the left to the corresponding tools on the right.
To support new clients in the environment, an engineer must enable Fast Transition on the corporate WLAN.
Which command must be applied on a Cisco Catalyst 9800 Series WLC?
- A . security ft adaptive
- B . security wpa akm dotlx
- C . security wpa akm psk
- D . security wpa akm ft psk
An engineer is configuring local web authentication on a WLAN. The engineer chooses the Authentication radio button under the Layer 3 Security options for Web Policy.
Which device presents the web authentication for the WLAN?
- A . ISE server
- B . local WLC
- C . RADIUS server
- D . anchor WLC
When should the MAC authentication bypass feature be used on a switch port?
- A . when authentication is required, but the attached host does not support 802.1X
- B . when the attached host supports 802.1X and must authenticate itself based on its MAC address instead of user credentials
- C . when authentication should be bypassed for select hosts based on their MAC address
- D . when the attached host supports limited 802.1X
What is the VXLAN network identifier used to identify?
- A . network tunnel interface
- B . IP subnet
- C . virtual tunnel endpoint
- D . broadcast domain
