Practice Free 350-401 Exam Online Questions
Which two namespaces does the LISP network architecture and protocol use? (Choose two.)
- A . TLOC
- B . RLOC
- C . DNS
- D . VTEP
- E . EID
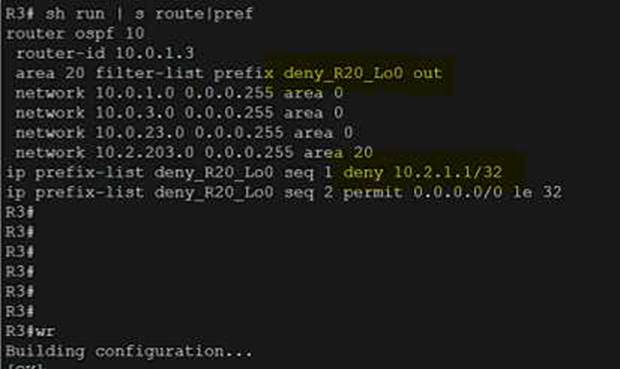
Refer to the exhibit.
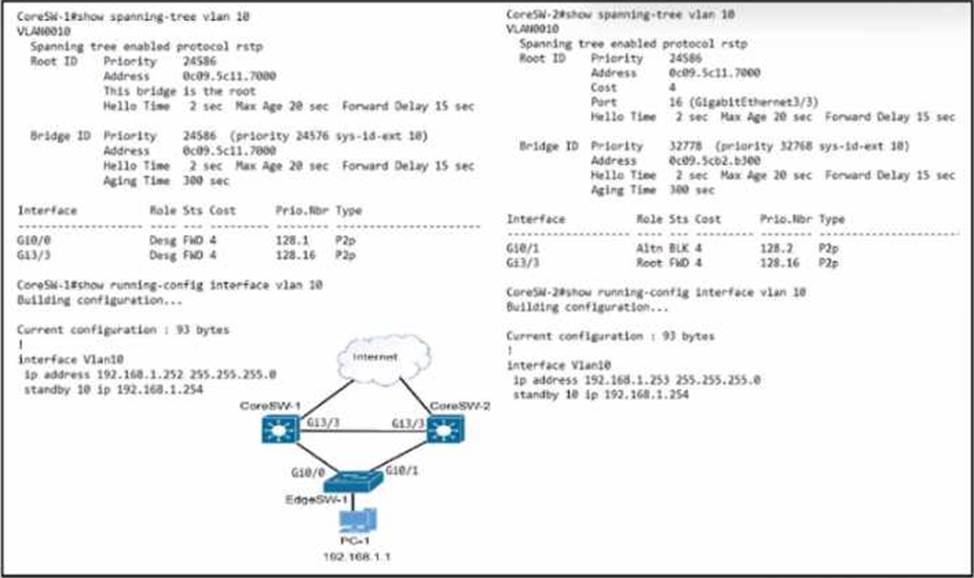
Which configuration causes the traffic from PC-1 to the internet to use the link between CoreSW-1 and CoreSW-2 when both switches are up?
A)
![]()
B)
![]()
C)
![]()
D)
![]()
- A . Option A
- B . Option B
- C . Option C
- D . Option D
Which NGFW mode block flows crossing the firewall?
- A . Passive
- B . Tap
- C . Inline tap
- D . Inline
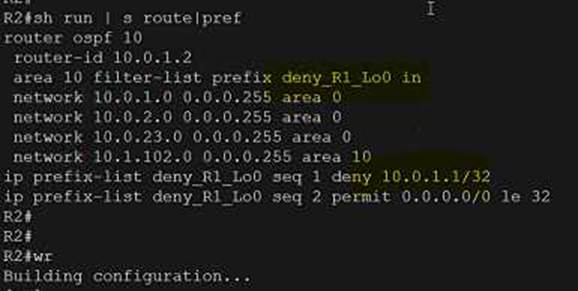
Refer to the exhibit.
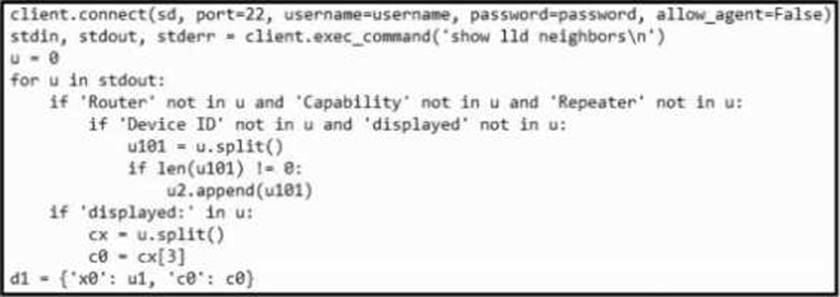
What is achieved by this Python script?
- A . It displays the output from show lldp neighbors into a standard output.
- B . It reads the neighbor count from show lldp neighbors into a dictionary list.
- C . It displays the Layer 3 neighbors from show lldp neighbors on the terminal screen.
- D . It reads the output from show lldp neighbors into an array object.
DRAG DROP
An engineer must create a script to append and modify device entries in a JSON-formatted file.
The script must work as follows:
Until interrupted from the keyboard, the script reads in the hostname of a device, its management IP address, operating system type, and CLI remote access protocol.
After being interrupted, the script displays the entered entries and adds them to the JSON-formatted file, replacing existing entries whose hostname matches.
The contents of the JSON-formatted file are as follows

Drag and drop the statements onto the blanks within the code to complete the script. Not all options are used.
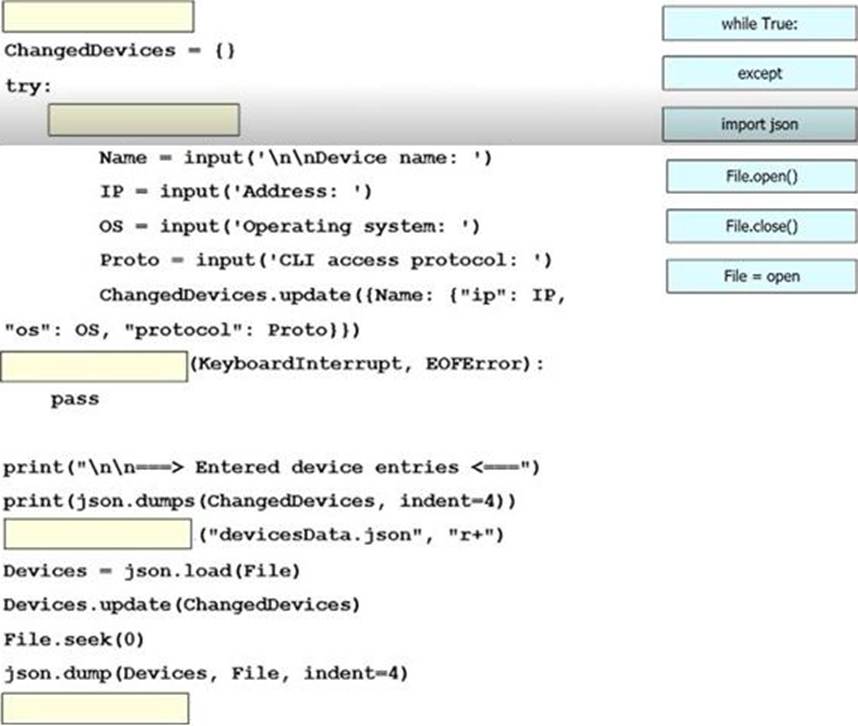
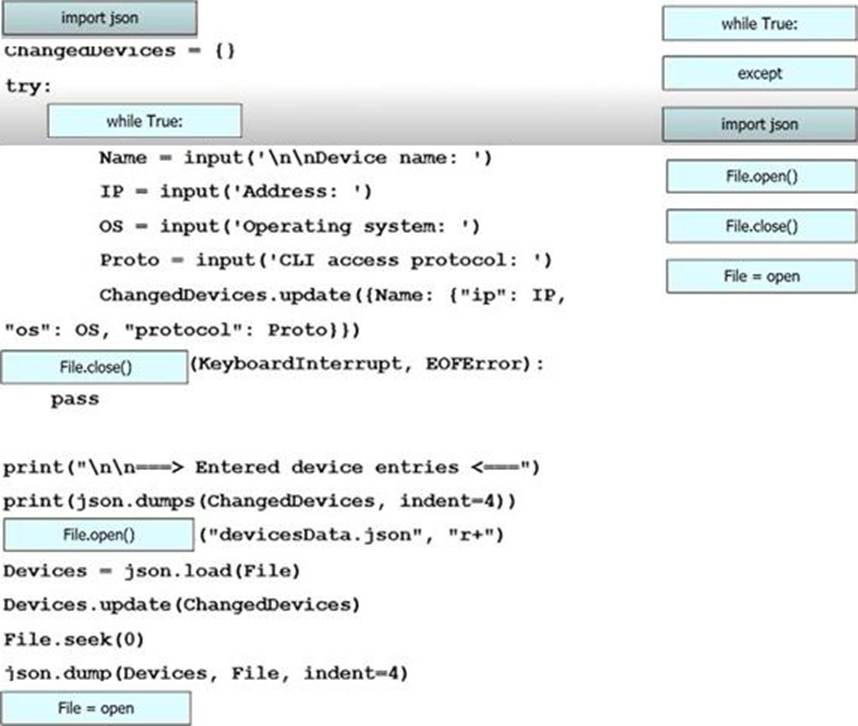
Explanation:
top down – while true, file.open(), except, file = open, file.close()
What is one characteristic of Cisco SD-Access networks?
- A . Devices are assigned to virtual networks based on their VLAN membership.
- B . Scalable group tags are used for macrosegmentatlon.
- C . Virtual networks are used for microsegmentation.
- D . All traffic is Layer 3 within the fabric.
Which two mechanisms are used with OAuth 2.0 for enhanced validation? (Choose two.)
- A . custom headers
- B . authentication
- C . authorization
- D . request management
- E . accounting
What is the recommended minimum SNR for data applications on wireless networks?
- A . 15
- B . 20
- C . 25
- D . 10
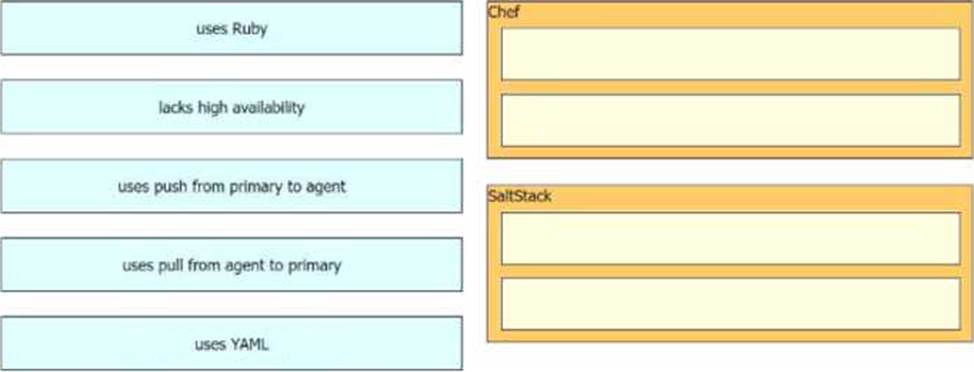
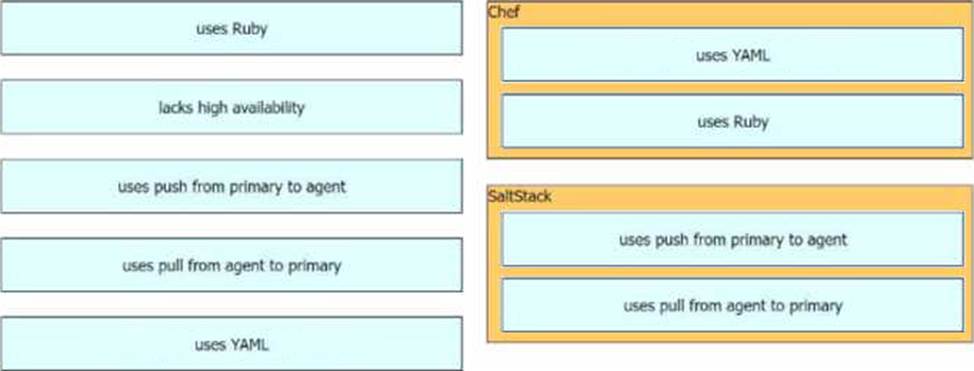
DRAG DROP
Drag and drop the automation characteristics from the left onto the appropriate tools on the right.
Not all options are used.