Practice Free 300-430 Exam Online Questions
A customer has 10 Cisco 3700 Series APs in autonomous mode installed at a warehouse facility. A new VoWLAN service is being deployed to support Cisco WLAN phones. All wired QoS is configured. The customer requires that all VoWLAN signaling and RTP traffic be prioritized between the wired and wireless networks.
Which configuration is required?
- A . Apply a Cisco AVC profile for RTP and signaling on all the APs.
- B . Switch on Fastlane on all the APs.
- C . Set EDCA on all the APs to optimize voice and video.
- D . Enable AWID priority mapping on all the APs
A wireless engineer must configure access control on a WLC using a TACACS+ server for a company that is implementing centralized authentication on network devices.
Which role value must be configured under the shell profile on the TACACS+ server for a user with read-only permissions?
- A . ADMIN
- B . MANAGEMENT
- C . MONITOR
- D . READ
A network is set up to support wired and wireless clients. Both types must authenticate using 802.1X before connecting to the network. Different types of client authentication must be separated on a Cisco ISE deployment.
Which two configuration items achieve this task? (Choose two.)
- A . device profiles
- B . policy sets
- C . separate networks
- D . policy groups
- E . policy results
Refer to the exhibit.
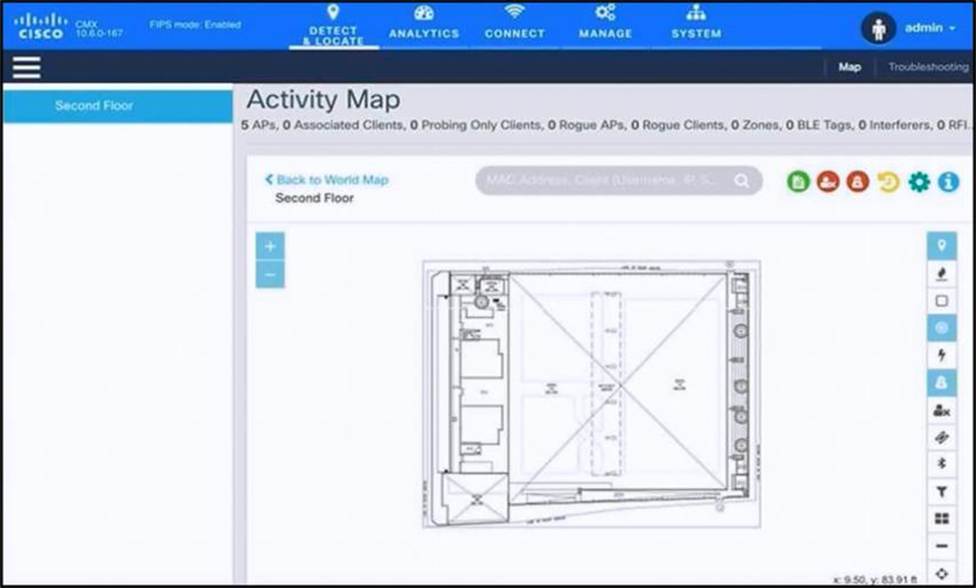
An engineer has deployed the Cisco CMX solution to track and detect the number of users who visit the office each day. The CMX dashboard is not showing any data.
Which action resolves this issue?
- A . Configure Single Sign-On authentication.
- B . Add the WLCs to CMX.
- C . Copy the exported Maps from CMX server to PI using SCP.
- D . Install an evaluation license to CMX server.
A customer is deploying local web authentication.
Which software application must be implemented on Cisco ISE to utilize as a directory service?
- A . Solaris Directory Service
- B . LDAP
- C . SAML
- D . Novell eDirectory
An engineer must implement rogue containment for an SSID.
What is the maximum number of APs that should be used for containment?
- A . 1
- B . 2
- C . 3
- D . 4
C
Explanation:
Reference: https://www.cisco.com/c/en/us/td/docs/wireless/technology/roguedetection_deploy/Rogue_Detection.html
A network administrator managing a Cisco Catalyst 9800-80 WLC must place all iOS connected devices to the guest SSID on VLAN 101. The rest of the clients must connect on VLAN 102 distribute load across subnets. To achieve this configuration, the administrator configures a local policy on the WLC.
Which two configurations are required? (Choose two.)
- A . Assign a policy map under global security policy settings.
- B . Add local profiling policy under global security policy settings.
- C . Create a service template.
- D . Allow HTTP and DHCP profiling under policy map.
- E . Enable device classification on global wireless settings.
All APs are receiving multicast traffic, instead of only the APs that need it.
What is the cause of this problem?
- A . The multicast group includes all APs
- B . The wrong multicast address was used
- C . The multicast group is assigned the wrong VLAN
- D . Multicast IGMP snooping is not enabled
An IT department receives a report of a stolen laptop and has information on the MAC address of the laptop.
Which two settings must be set on the wireless infrastructure to determine its location? (Choose two.)
- A . Location History for Clients must be enabled on the MSE.
- B . Client location tracking must be enabled on the MSE.
- C . Location History for Visitors must be enabled on the MSE.
- D . Location History for Rogue APs & Rogue Clients must be enabled on the MSE.
- E . Tracking optimization must be enabled on the WLC.
What is configured to use more than one port on the OEAP to extend the wired network?
- A . remote LAN ACL
- B . AAA override
- C . client load balancing
- D . remote LAN
