Practice Free 300-430 Exam Online Questions
A customer requires wireless traffic from the branch to be routed through the firewall at corporate headquarters. A RADIUS server is in each branch location.
Which Cisco FlexConnect configuration must be used?
- A . central authentication and local switching
- B . central authentication and central switching
- C . local authentication and local switching
- D . local authentication and central switching
An engineer must provide a graphical report with summary grouped data of the total number of wireless clients on the network.
Which Cisco Prime Infrastructure report provides the required data?
- A . Client Traffic Stream Metrics
- B . Client Summary
- C . Posture Status Count
- D . Mobility Client Summary
An enterprise has recently deployed a voice and video solution available to all employees using AireOS controllers. The employees must use this service over their laptops, but users report poor service when connected to the wireless network. The programs that consume bandwidth must be identified and restricted.
Which configuration on the WLAN aids in recognizing the traffic?
- A . NetFlow Monitor
- B . AVC Profile
- C . QoS Profile
- D . Application Visibility
Refer to the exhibit.
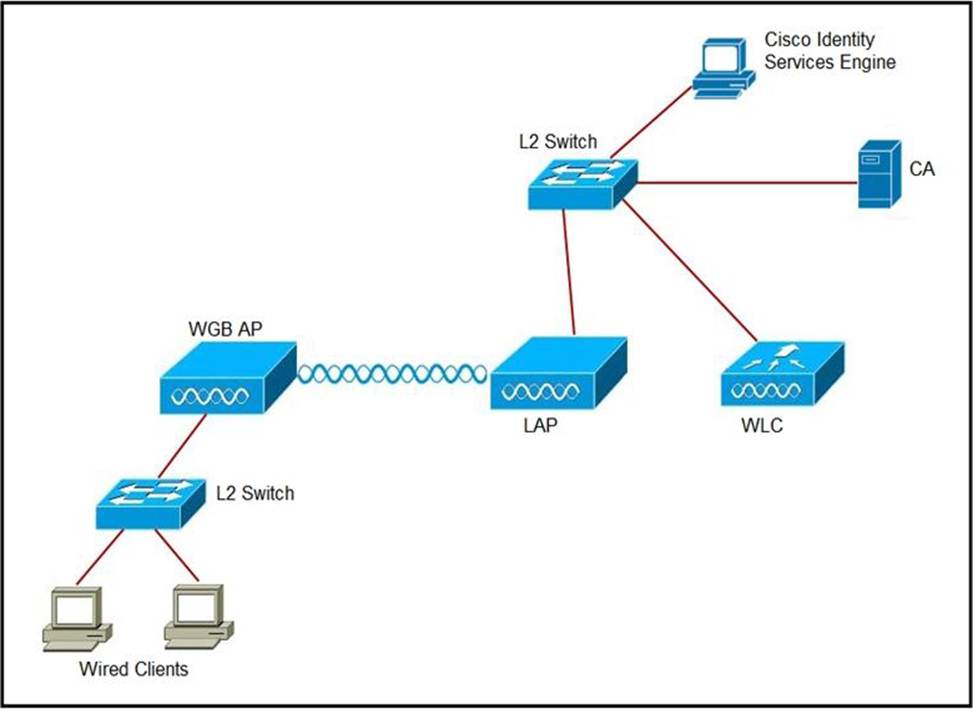
An engineer must connect a fork lift via a WGB to a wireless network and must authenticate the WGB certificate against the RADIUS server.
Which three steps are required for this configuration? (Choose three.)
- A . Configure the certificate, WLAN, and radio interface on WGB.
- B . Configure the certificate on the WLC.
- C . Configure WLAN to authenticate using ISE.
- D . Configure the access point with the root certificate from ISE.
- E . Configure WGB as a network device in ISE.
- F . Configure a policy on ISE to allow devices to connect that validate the certificate.
Refer to the exhibit.
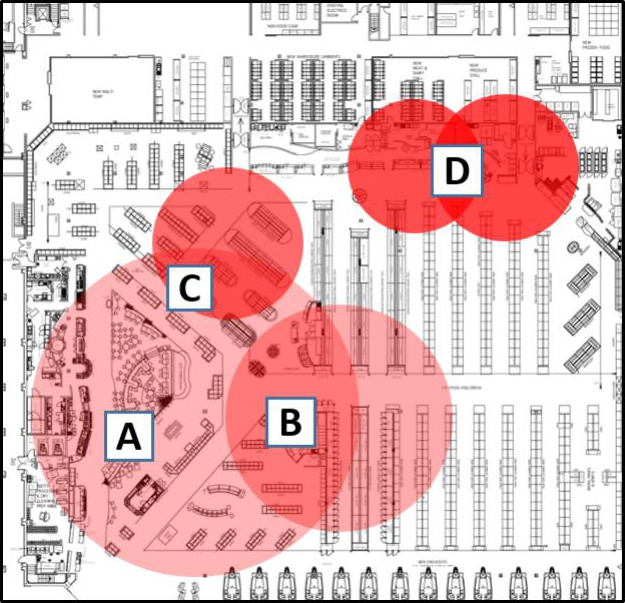
Which area indicates the greatest impact on the wireless network when viewing the Cisco CleanAir Zone of Impact map of interferers?
- A . A
- B . B
- C . C
- D . D
D
Explanation:
Reference: https://www.cisco.com/c/en/us/support/docs/wireless/5500-series-wireless-controllers/112139-cleanair-uwn-guide-00.html
WPA2 Enterprise with 802.1X is being used for clients to authenticate to a wireless network through a Cisco ISE server. For security reasons, thenetwork engineer wants to ensure that only PEAP authentication is used. The engineer sent instructions to clients on how to configure the supplicants, but the ISE logs still show users authenticating using EAP-FAST.
Which action ensures that access to the network is restricted for these users unless the correct authentication mechanism is configured?
- A . Enable AAA override on the SSID, gather the usernames of these users, and disable the RADIUS accounts until the devices are correctly configured.
- B . Enable AAA override on the SSID and configure an ACL on the WLC that allows access to users with IP addresses from a specific subnet.
- C . Enable AAA override on the SSID and configure an access policy in Cisco ISE that denies access to the list of MACs that have used EAP-FAST.
- D . Enable AAA override on the SSID and configure an access policy in Cisco ISE that allows access only when the EAP authentication method is PEAP.
An engineer configures a WLC and 20 Cisco OEAPs. The engineer must configure a remote LAN that uses WPA2 Enterprise security.
How should the LAN be configured?
- A . on the anchor WLC via the GUI
- B . on the OEAP via the GUI
- C . on the OEAP via the CLI
- D . on the WLC via the CLI
Refer to the exhibit.
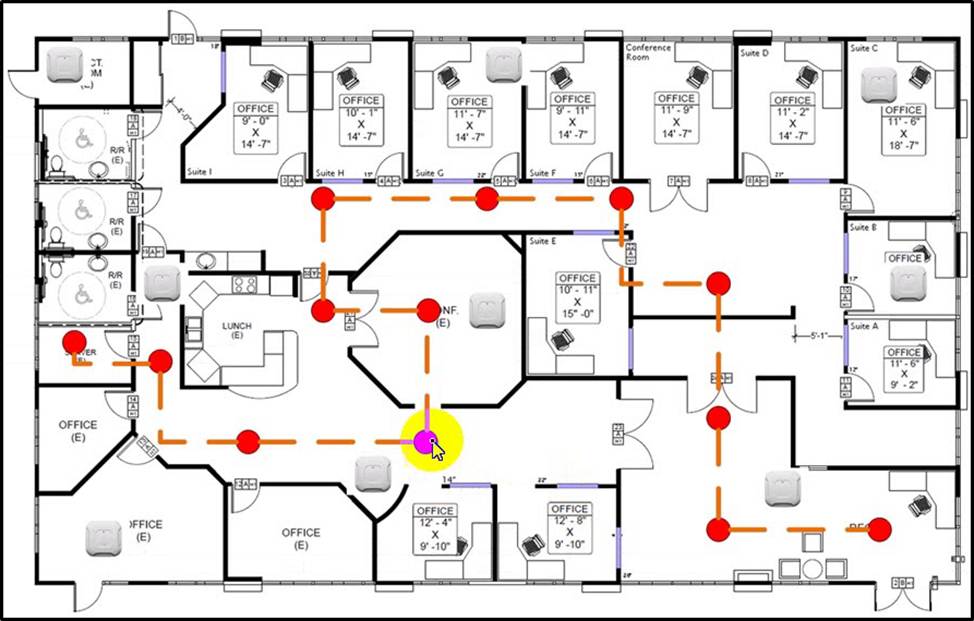
An engineer needs to configure location services in an office. The requirement is to use FastLocate and achieve higher locations refresh rates.
Which location-based technique should be implemented?
- A . probe-based
- B . location patterning
- C . data packet-based
- D . angulation
A user is trying to connect to a wireless network that is configured for WPA2-Enterprise security using a corporate laptop. The CA certificate for the authentication server has been installed on the Trusted Root Certification Authorities store on the laptop. The user has been prompted to enter the credentials multiple times, but the authentication has not succeeded.
What is causing the issue?
- A . There is an IEEE invalid 802.1X authentication policy on the authentication server.
- B . The user Active Directory account is locked out after several failed attempts.
- C . There is an invalid 802.1X authentication policy on the authenticator.
- D . The laptop has not received a valid IP address from the wireless controller.
An engineer is configuring a BYOD deploymernt strategy and prefers a single SSID model.
Which technology is required to accomplish this configuration?
- A . mobility service engine
- B . wireless control system
- C . identify service engine
- D . Prime Infrastructure
