Practice Free JN0-650 Exam Online Questions
Which two statements correctly describe how EX Series switches use captive portal for Layer 2 authentication? (Choose two.)
- A . The captive portal is used as a fallback mechanism for clients that fail 802.1X or MAC RADIUS authentication.
- B . The captive portal authentication allowlist works for devices that do not have HTTP capabilities.
- C . The captive portal is configured on Layer 3 interfaces and does not participate in Layer 2 authentication on EX Series switches.
- D . The captive portal is the default Layer 2 authentication method that is applied before other methods such as 802.1X or MAC RADIUS.
Exhibit
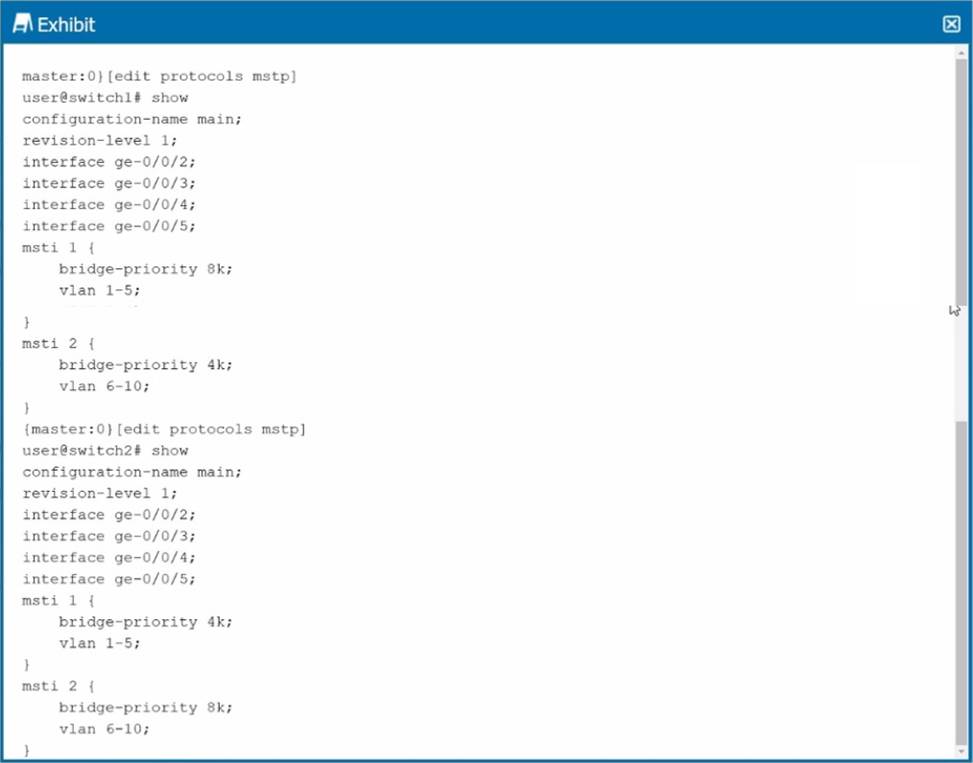
You are asked to configure VLAN load balancing on your network using MSTP. Referring to the exhibit, which two statements are correct? (Choose two.)
- A . Switch1 will be the root bridge for msti 1.
- B . Switch1 will be the root bridge for msti 2.
- C . Switch 1 will not assume the role of root bridge for both mstil and msti2 if Switch2 goes down.
- D . Switch1 will assume the role of root bridge for both mstil and msti2 if Switch2 goes down.
You configured MVRP in your Layer 2 network and you are adding two new interfaces to your distribution switch. You are asked to ensure that if a rogue device that uses MVRP is connected to these interfaces, that the MVRP PDUs are ignored.
In this scenario, what should you configure to accomplish this task?
- A . Configure the two new interfaces under MVRP using the forbidden registration mode.
- B . Configure the join-timer to 500 ms.
- C . Configure the no-dynamic-vlan feature under MVRP.
- D . Configure the two new interfaces as point-to-point
You must implement EVPN signaling on an EX Series device that is configured with both underlay and overlay networks.
Which network protocol accomplishes this task?
- A . OSPF underlay network
- B . IS-IS underlay network
- C . EBGP overlay network
- D . MPLS overlay network
Click the Exhibit button.
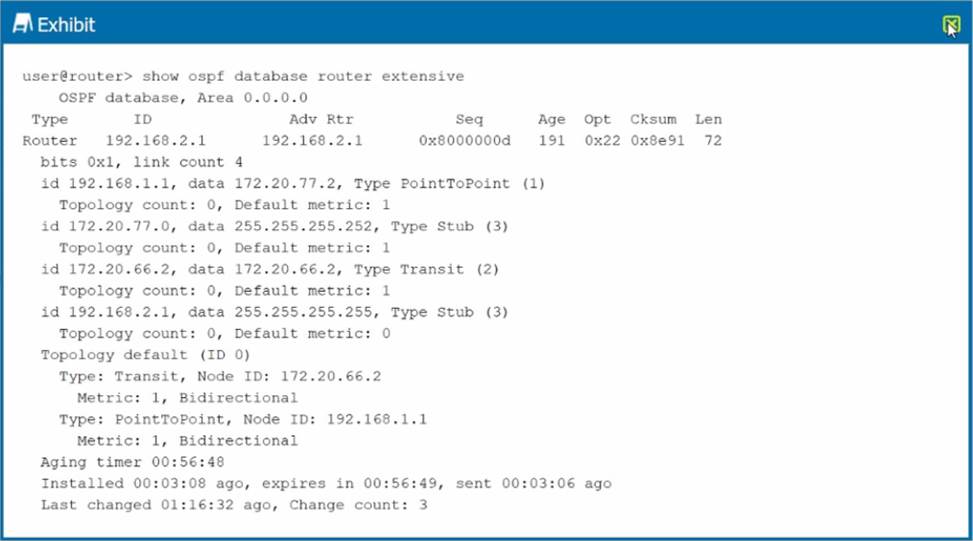
What is the OSPF router type shown in the exhibit for router 192.168.2.1?
- A . both an ABR and an ASBR
- B . neither an ABR nor an ASBR
- C . an ABR
- D . an ASBR
Exhibit
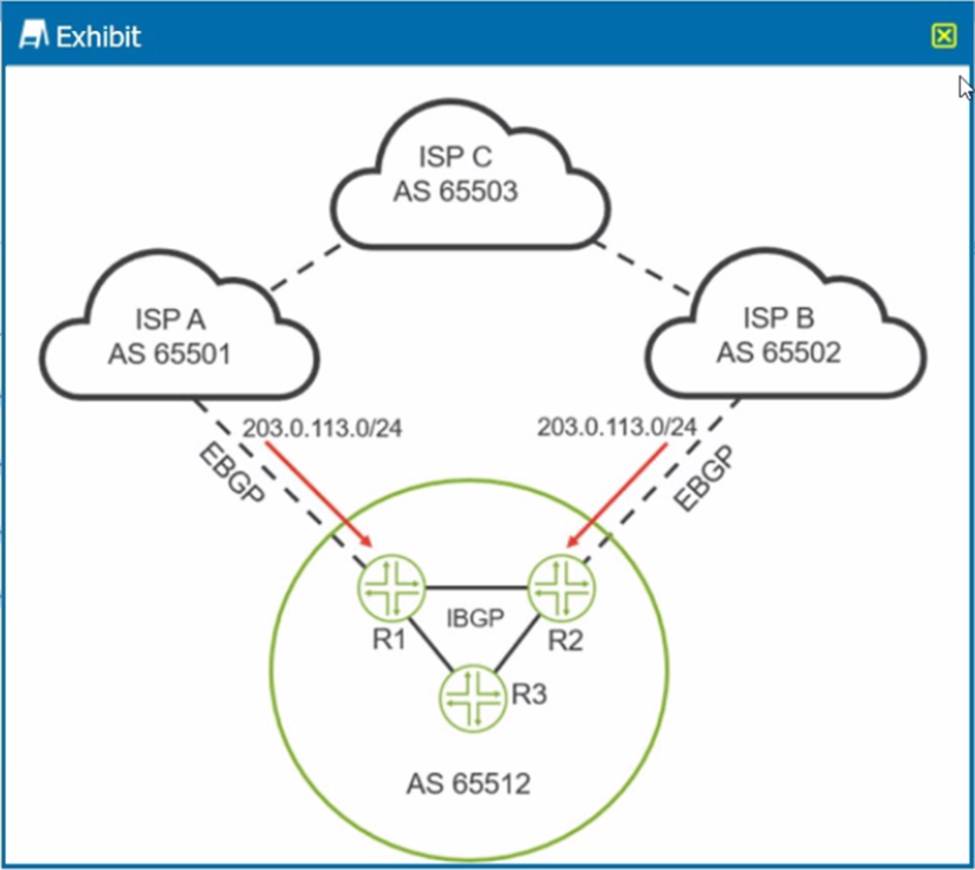
You are receiving the 203 0.113.0/24 route from both upstream ISPs You are asked to ensure that ISP A is the preferred ISP for traffic being sent to the 203.0.113.0/24 network from devices in AS 65512.
Referring to the exhibit, which two statements will accomplish this behavior? (Choose two.)
- A . You should assign a local preference that is lower than 100 for the route learned from ISP A.
- B . You should assign a local preference that is higher than 100 for the route learned from ISP A.
- C . You should assign a local preference that is lower than 100 for the route learned from ISP B.
- D . You should assign a local preference that is higher than 100 for the route learned from ISP B.
Click the Exhibit button.
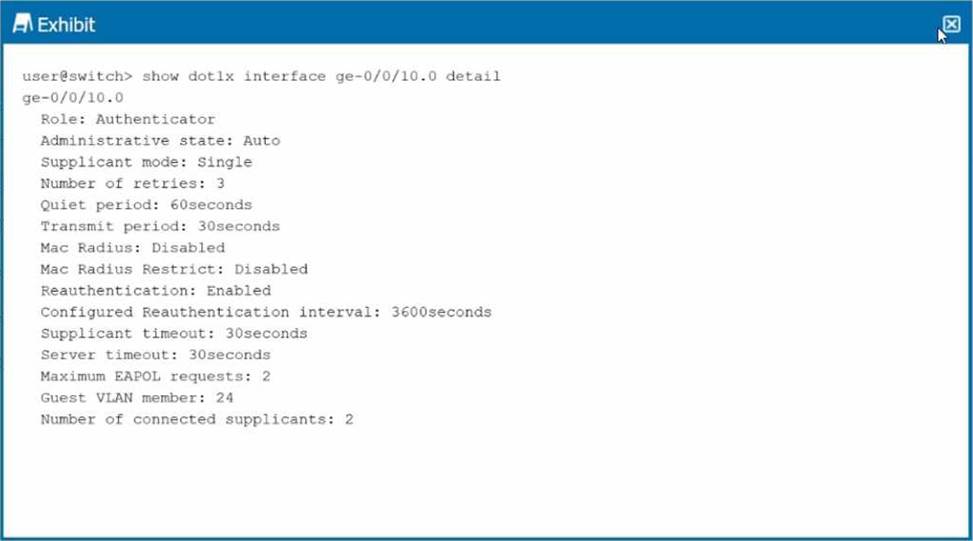
You want to limit port access to only one device at a time.
Referring to the exhibit, which configuration change will accomplish this task?
- A . Change the supplicant mode to single-Secure.
- B . Change the maximum EAPOL request to 1.
- C . Change the supplicant mode to multiple.
- D . Enable MAC RADIUS restrict
Click the Exhibit button.
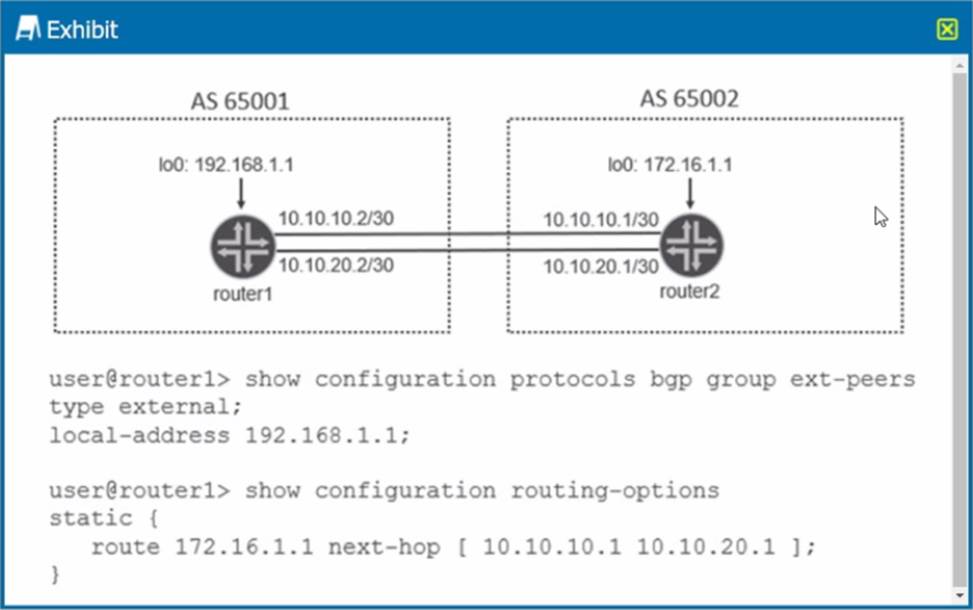
Referring to the exhibit, what is required for the BGP peering to establish?
- A . Configure neighbor 172.16.1.1 multihop under the ext-peers hierarchy.
- B . Configure neighbor 10.10.20.1 multihop under the ext-peers hierarchy.
- C . Configure neighbor 10.10.10.1 multihop under the ext-peers hierarchy.
- D . Configure neighbor 172.16.1.1 multipath under the ext-peers hierarchy.
Click the Exhibit button.
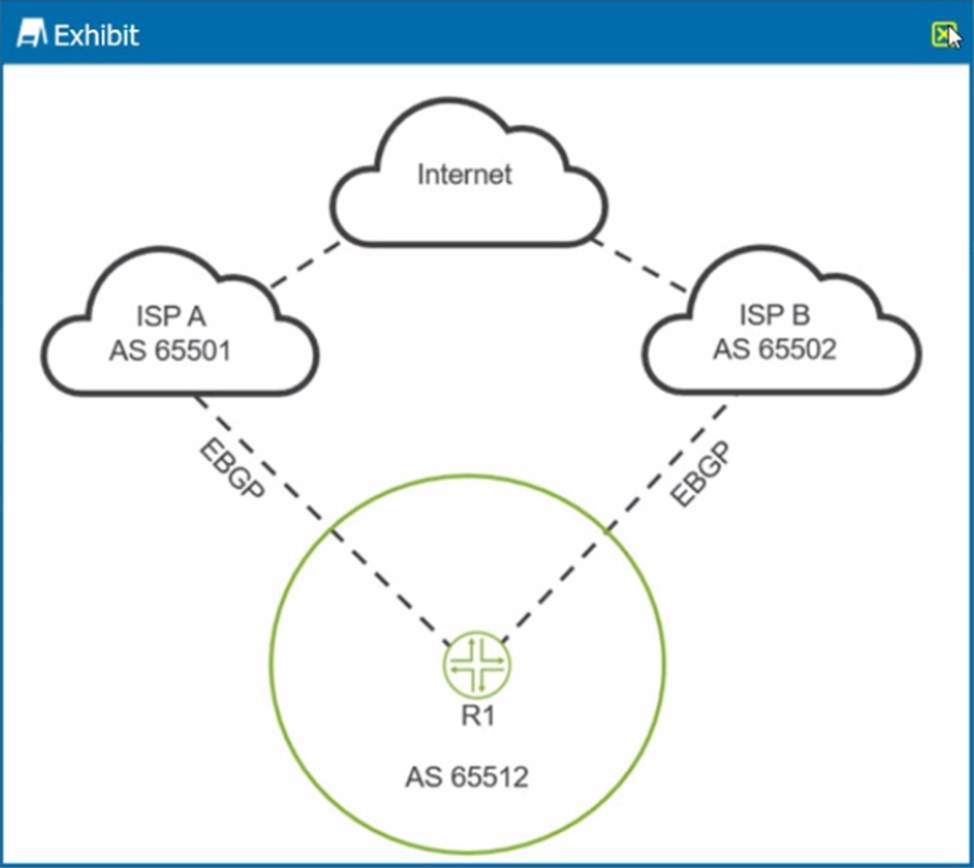
You are receiving the same BGP Internet routes on R1 from both upstream ISPs. You are asked to load-balance traffic destined to the Internet across both ISPs.
Referring to the exhibit, which BGP solution should you use?
- A . Use the multipath multiple-as feature on R1.
- B . Use the damping feature on R1.
- C . Use the multihop feature on R1.
- D . Use the prefix limit feature on R1.
You are asked to establish authentication for users connecting to the corporate network You must ensure that only corporate devices that are identified by MAC addresses are allowed to authenticate and connect. Authentication must be handled by a centralized database.
Which authentication method would you implement in this scenario?
- A . captive portal
- B . single-secure supplicant mode
- C . single supplicant mode
- D . MAC RADIUS
